Star Wars Death Star Waffle Iron – $39.00
Starry Flight of Serenity Tee Shirt – $20.00
 I was surprised to discover proof that my business is a target of cyber-criminals. After installing some security and reporting tools on my websites, I was alerted to the almost constant state of attack that they were under. And all I am doing is writing a cybersecurity blog. And you, dear reader, what of your business? There is a good chance that you are too, but simply don’t know it ...
I was surprised to discover proof that my business is a target of cyber-criminals. After installing some security and reporting tools on my websites, I was alerted to the almost constant state of attack that they were under. And all I am doing is writing a cybersecurity blog. And you, dear reader, what of your business? There is a good chance that you are too, but simply don’t know it ...
DEC
 My Facebook friend Jeff Wegge asked: “Security question Bob. Is the hotspot on my mobile verizon phone any more secure than public Wi-Fi?”
My Facebook friend Jeff Wegge asked: “Security question Bob. Is the hotspot on my mobile verizon phone any more secure than public Wi-Fi?”
This is a most excellent question! Generally speaking, the mobile hotspot will be more secure for two reasons The first is that only you are likely to be using it, unless you explicitly shared the SSID (network name) and passphrase with someone else. The second reason ...
Continue Reading →DEC
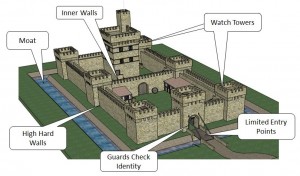 Classical computer and network security has relied on perimeter defense, in the form of firewalls, intrusion detection devices, and similar technologies for quite some time. This is usually coupled with some form of endpoint security, typically in the form of a security software package. We are finding that this no longer is working. The reasons are many, but the big one ...
Classical computer and network security has relied on perimeter defense, in the form of firewalls, intrusion detection devices, and similar technologies for quite some time. This is usually coupled with some form of endpoint security, typically in the form of a security software package. We are finding that this no longer is working. The reasons are many, but the big one ...
DEC
I was recently interviewed by Carolyn Heinze for ChannelPro Network magazine on the subject of ransomware. Ransomware is back (if it ever really left) and there are strategies you can use to defeat it. If you do nothing, there will be nothing for you but to pay up.
On October 21st at the Cyber Security Summit in Boston, comments by Joseph Bonavolonta, Assistant Special Agent in Charge ...
Continue Reading →NOV
Darwinism in Action
 Mashable reported to wide popularity in September that in 2015, more people have died taking selfies than in shark attacks. The score is Fatal Selfies 12 vs. Sharks 8. Either way not a huge risk, something tells me that lightning strikes score higher (according to NOAA – 26) than either of these. The reason this statistic is so popular is the same reason we find ...
Mashable reported to wide popularity in September that in 2015, more people have died taking selfies than in shark attacks. The score is Fatal Selfies 12 vs. Sharks 8. Either way not a huge risk, something tells me that lightning strikes score higher (according to NOAA – 26) than either of these. The reason this statistic is so popular is the same reason we find ...
NOV
 This week we have focused on the people part of the security puzzle. As we know, people are the weakest link and the easiest point of access. But beating this point into your employees will not help them be better at computer and network security, and just make them feel hopeless and badgered.
This week we have focused on the people part of the security puzzle. As we know, people are the weakest link and the easiest point of access. But beating this point into your employees will not help them be better at computer and network security, and just make them feel hopeless and badgered.
Getting employee buy-in requires a little bit of strategy mixed in with a lot of fun.
- Sharing the actual ...
NOV
 On Monday we discussed the effect that living in a code yellow world has on creating security fatigue. Peter Herzog, in his blog Dark Matters expanded on this theme recently, giving examples of how teaching your employees how to stay secure in an insecure world may be counter-intuitive to the way we usually accomplish this.
On Monday we discussed the effect that living in a code yellow world has on creating security fatigue. Peter Herzog, in his blog Dark Matters expanded on this theme recently, giving examples of how teaching your employees how to stay secure in an insecure world may be counter-intuitive to the way we usually accomplish this.
Here are his recommendations:
- Teach your employees to say “I don’t ...
NOV
It seems like we are being barraged with a never ending string of news stories about cybersecurity events, breaches, and lapses. Often these stories will provide helpful tips or advise us how to avoid or recover from these security incidents. This author, in our own humble way, is contributing to the constant ringing alarms about cybersecurity. Maybe it is getting to be too ...
Continue Reading →NOV
From Pinterest





