 When you work in a cybersecurity organization that serves other business entities, every now and again you see something really unique. This one crossed my desk on March 28th. A client of ours received a letter by postal mail that threatened to shut them down with a distributed denial of service attack. They are probably trying to avoid the Computer Fraud and Abuse Act, but extortion by postal mail is a ...
When you work in a cybersecurity organization that serves other business entities, every now and again you see something really unique. This one crossed my desk on March 28th. A client of ours received a letter by postal mail that threatened to shut them down with a distributed denial of service attack. They are probably trying to avoid the Computer Fraud and Abuse Act, but extortion by postal mail is a ...
MAR


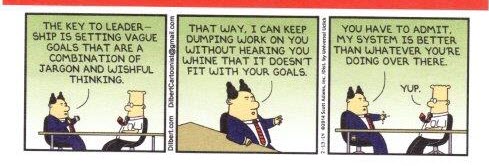

 Social networks are a tremendous source of personal information leakage. Actually, more like a waterfall. As we learned in the last post, attackers use social networks to perform reconnaissance against their chosen targets. Since few of us are going to delete all our social network accounts and move of the grid, we have to find a way to live ...
Social networks are a tremendous source of personal information leakage. Actually, more like a waterfall. As we learned in the last post, attackers use social networks to perform reconnaissance against their chosen targets. Since few of us are going to delete all our social network accounts and move of the grid, we have to find a way to live ...