 When you work in a cybersecurity organization that serves other business entities, every now and again you see something really unique. This one crossed my desk on March 28th. A client of ours received a letter by postal mail that threatened to shut them down with a distributed denial of service attack. They are probably trying to avoid the Computer Fraud and Abuse Act, but extortion by postal mail is a Federal crime too.
When you work in a cybersecurity organization that serves other business entities, every now and again you see something really unique. This one crossed my desk on March 28th. A client of ours received a letter by postal mail that threatened to shut them down with a distributed denial of service attack. They are probably trying to avoid the Computer Fraud and Abuse Act, but extortion by postal mail is a Federal crime too.
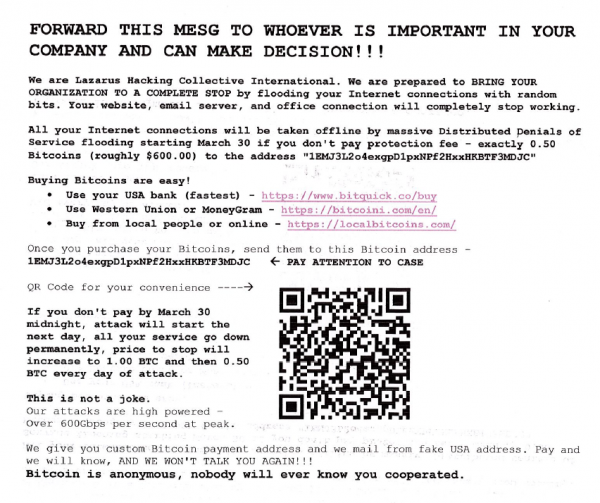
This was sent to a church. [Update: Another coworker brought me a second sample, also sent to a church. In both cases the letter appeared to come from a firm in the same town, but the actual street addresses were different. Real street addresses, but for homes.] The body of the letter follows in the image below.
This is a threat that could really happen, but is not usually leveled at an organization this small. This is what is called a Denial of Service attack or a Distributed Denial of Service Attack (DDoS), depending how many attacking systems are used.
A Google Search says the “Lazarus Hacking Collective International” is the same Lazarus Group that was identified as responsible for the Sony Hack and some Philippine Banking hacks. It is also possible that this scammer is riding on the coattails of a more famous group. I did not see anything about this specific threat, and you might expect there to be several reports of this one.
So there is a possibility that it is a lone attacker pretending to be the Lazarus group. Might just be a kid who went to Sunday School there.
If they were to pay the extortion amount, there is no proof that the attack won’t happen anyway. There is also no way to know if there is really a botnet waiting to attack, either. It may be that nothing will happen. If I received this letter, I would wait to see what happens. Comcast (or whoever is their ISP) would have to deal with a DDoS against their network connection. Their web hosting company would have to deal with any DDoS traffic to the web server. Not really a problem for the church that got the letter.
 It’s interesting that the background for the Lazarus logo is a fist over a floppy disk – like anyone uses floppies anymore.
It’s interesting that the background for the Lazarus logo is a fist over a floppy disk – like anyone uses floppies anymore.
It would be a good idea for the recipient to post it to the Internet Crime Complaint Center at www.ic3.gov. This will get it to the FBI. If there are more of these sorts of exploits, they can be aggregated and combined into one big case.
Although I was not able to find anything about this specific exploit, there were a couple of similar scams attributed the “Armada Collective” last year. Here are links to the Verge and Ars Technica articles.
Follow up note: 4/4/2017 – March 31 came and went and there was no DDoS attack. I am thinking this was someone’s rather elaborate April Fool’s joke since the attack was schedule to start on April 1.
ShareMAR




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com