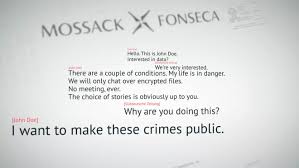
 We have written before about the importance of properly securing your WordPress website. According to a recent post on the WordFence blog, the Mossack Fonseca breach, commonly known as the “Panama Papers,” was apparently made possible by an unpatched WordPress plugin, and also a mail program that stored user credentials in plaintext..
We have written before about the importance of properly securing your WordPress website. According to a recent post on the WordFence blog, the Mossack Fonseca breach, commonly known as the “Panama Papers,” was apparently made possible by an unpatched WordPress plugin, and also a mail program that stored user credentials in plaintext..
This again reiterates the importance of keeping your WordPress version up to date (version 4.5 as of 4-16-2016), ...
Continue Reading →APR

 I read a couple of thought provoking articles recently on the subject of data security, and more directly, on how data destruction can serve to permanently “secure” the data that is destroyed. One article appeared in the
I read a couple of thought provoking articles recently on the subject of data security, and more directly, on how data destruction can serve to permanently “secure” the data that is destroyed. One article appeared in the  We have been recommending the Google Chromebook to our clients for use as a dedicated online banking system. The reason we like this platform even more than a Linux LiveCD boot disk is that because the Chrome operating system simply supports the operation of the notebook itself, and the Chrome browser. That’s it. There is not a way to install any programs to ...
We have been recommending the Google Chromebook to our clients for use as a dedicated online banking system. The reason we like this platform even more than a Linux LiveCD boot disk is that because the Chrome operating system simply supports the operation of the notebook itself, and the Chrome browser. That’s it. There is not a way to install any programs to ...

 Tired of cyber-creeps kicking sand in your face at the virtual beach? Microsoft wants to pump you up!!. Businesses using the Enterprise version of Windows 10 will have the option of using
Tired of cyber-creeps kicking sand in your face at the virtual beach? Microsoft wants to pump you up!!. Businesses using the Enterprise version of Windows 10 will have the option of using