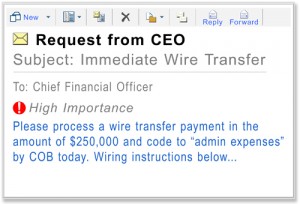
 Since 2013, cyber-criminal gangs working from the Middle East, Africa, and eastern Europe have scammed businesses out of $1.2 billion dollars worldwide, with over 700 US businesses reporting $747 million in losses to this exploit. In 2015 alone there has been a 270% increase in losses to this scam. On August 28th, the FBI warned business owners and manager to be on guard ...
Since 2013, cyber-criminal gangs working from the Middle East, Africa, and eastern Europe have scammed businesses out of $1.2 billion dollars worldwide, with over 700 US businesses reporting $747 million in losses to this exploit. In 2015 alone there has been a 270% increase in losses to this scam. On August 28th, the FBI warned business owners and manager to be on guard ...
SEP





