Now that football season has started, there will be a lot of discussion about why great defenses don’t win football games. Defense is not enough in the realm of cybersecurity, either. I recently attended a webinar put on by The Open Web Application Security Project (OWASP) featuring Mike Benkovich (@mbenko) that discussed this concept as it applied to the DevSecOps (or SecDevOps) or the secure development of web applications. It is not enough to write code that works, it also must work securely, in order to protect your business and clients from Dark Web marauders.
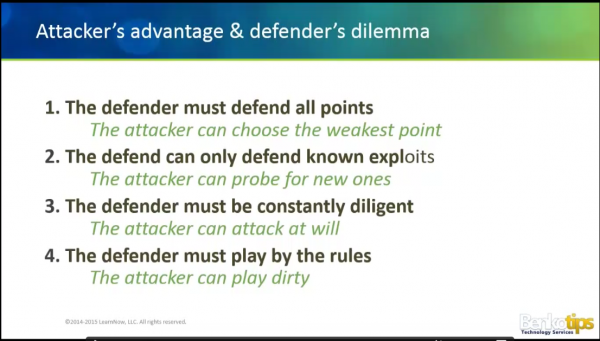
This applies to your business network as well. Defense will not be enough to keep the bad guys out. Why not? The image below, from Mike’s slide deck explains the problem.
- The defender must defend all points
- The attacker can choose the weakest point
- The defender can only defend known exploits
- The attacker can probe for new ones
- The defender must be constantly diligent
- The attacker can attack at will
- The defender must play by the rules
- The attacker can play dirty
I was watching a History Channel show about the Trojan War the other day. The Trojan War lasted ten years. The citadel of Troy was the best defensive design of its day, and withstood every attempt the Greek army made to breach the walls from the outside. In the end it was the first Trojan horse that defeated Troy. The Greeks left an apparent “gift” behind, and sailed away. Inside the gift was a small contingent of Greek soldiers who were able to open the gates to the city from the inside. The Greek armada returned and easily defeated the defenders, once inside the walls.
It is not an accident that the Trojan horse malware exploit is the most frequently used method to gain access to a well defended network. Trojan horses work. Trojan horses most commonly arrive in phishing or spearphishing emails as malicious links or attachments. There are email filtering solutions to help weed out these attacks before they reach your inbox or the inboxes of your employees. In a Windows server environment, some of these exploits can be prevented through group policy. But it only takes one clever email and one trusting employee to open a doorway into your network.
So what to do? Going back to ancient Troy, what would have happened if the gift horse had been given a proper inspection before it was rolled into the city? Failing that, what would have happened it there were a group of guards present when the Greeks emerged from their horse? If the Greeks had been prevented from opening the city gates in the first place?
This is where modern cybersecurity is leading us. In addition to defending against outside intruders, networks must be monitored constantly for insider intrusions, marked by unusual traffic between systems on the same network, or unexpected communications from a device on the network to some other device outside the network. These rogue devices can be quickly identified and removed from the network, and stop your breach in its tracks.
So part of a good defense these days is making the assumption that you will be breached at some point, preparing for the inevitable attack, and remaining vigilant about the inside of your network, too.
ShareSEP




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com