 I don’t like to get political in this web log, but since the mainstream parties have given us what is possibly the worst two choices in Presidential candidates since the Revolution, may I suggest voting Libertarian? You can check out their platform from the link.
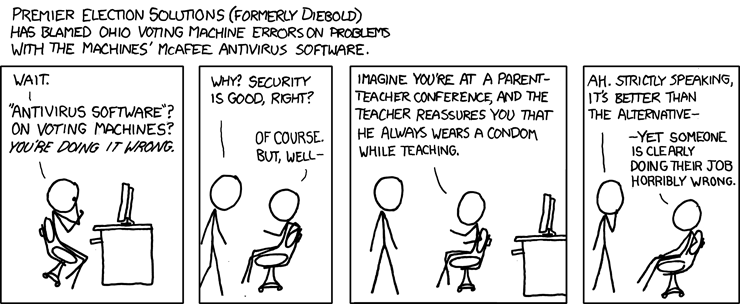
I don’t like to get political in this web log, but since the mainstream parties have given us what is possibly the worst two choices in Presidential candidates since the Revolution, may I suggest voting Libertarian? You can check out their platform from the link.Tuesday we get to vote for president again. Worried about the security of electronic voting machines? You are not alone, but you would not find any political or election officials in your group. They think everything is fine! The fact that your next president may be elected by the Russian Cyber Army is OK, I guess. So that means Trump.
Here’s a little humor to make the nightmare seems more acceptable.
 Continue Reading →
Continue Reading →
NOV
 On of the more hopeful presentations from the Cyber Security Summit was presented by Tony Sager from the Center for Internet Security. Titled “Making Best Practices Common Practices: The CIS Controls,” Tony provided us with a road map for implementing secure practices in our networks.
On of the more hopeful presentations from the Cyber Security Summit was presented by Tony Sager from the Center for Internet Security. Titled “Making Best Practices Common Practices: The CIS Controls,” Tony provided us with a road map for implementing secure practices in our networks.
There are 20 CIS controls. Tony said that implementing the first 5 (20%) would reduce your risk by 80%. ...
Continue Reading →NOV
 On Monday we looked at the some of the primary attack vectors used by cyber-criminals. Here are the rest of the attack vectors that Kevin Thompson from FireEye shared at the Cyber Security Summit. Many of these are significant twists on old exploits, or more sophisticated exploits.
On Monday we looked at the some of the primary attack vectors used by cyber-criminals. Here are the rest of the attack vectors that Kevin Thompson from FireEye shared at the Cyber Security Summit. Many of these are significant twists on old exploits, or more sophisticated exploits.
- Attacks using legitimate services.
- Social networks – make friends or connections, gather information.
- Cloud storage services to host malware downloads. Link looks legitimate, its from Google Docs or ...
NOV
 Hey, when I spend several hundred dollars and two days of my time to attend a cybersecurity conference, a guy like me hopes he can milk a few blog articles out of it. Here is the third (so far.)
Hey, when I spend several hundred dollars and two days of my time to attend a cybersecurity conference, a guy like me hopes he can milk a few blog articles out of it. Here is the third (so far.)
Most of these nuggets came from a keynote titled “2016 Cyber Attacks By The Numbers” presented by Kevin Thompson, a former CIA analyst and now a threat analysis for the cybersecurity firm FireEye. Very eye-opening.
Primary Attack Vectors
- Spearphishing ...
OCT
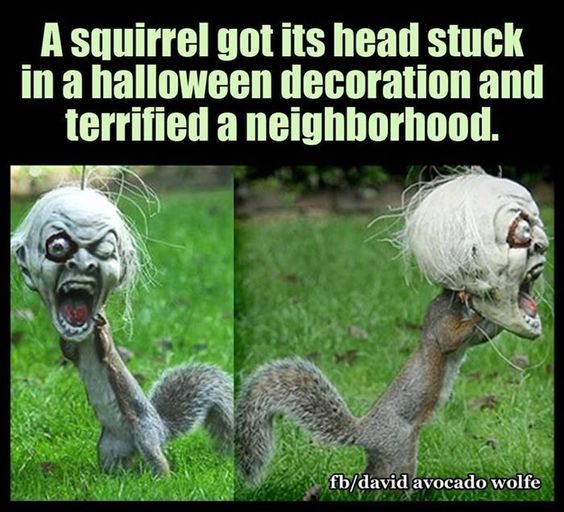
From Pinterest – actually pretty freaky!

 In the last several days, we have seen big distributed denial of service (DDoS) attacks against DynDNS, an Internet services company that provides domain name services (DNS) to many companies including Twitter and PayPal. DNS is how web sites are found on the web, you enter a web address in your browser, and DNS finds the website you are looking for. When attacked in ...
In the last several days, we have seen big distributed denial of service (DDoS) attacks against DynDNS, an Internet services company that provides domain name services (DNS) to many companies including Twitter and PayPal. DNS is how web sites are found on the web, you enter a web address in your browser, and DNS finds the website you are looking for. When attacked in ...