From Pinterest
Continue Reading →JUL
 The Apple OSX platform has long held the cache of being invulnerable to attack. Cyber-criminals have be crafting more exploits to target Macs, iPhones, and iPads, especially since 2012. The reason for this, as explored in a recent article on SiliconBeat, is that Apple users tend to have more disposable income. If you willingly pay more to have “the best” or ...
The Apple OSX platform has long held the cache of being invulnerable to attack. Cyber-criminals have be crafting more exploits to target Macs, iPhones, and iPads, especially since 2012. The reason for this, as explored in a recent article on SiliconBeat, is that Apple users tend to have more disposable income. If you willingly pay more to have “the best” or ...
 Research shows that over 90% of network breaches happen when an employee falls prey to a phishing email, clicking on the offered link or opening a file attachment, becoming infected with a remote access Trojan, and creating an entry point for the attacker. If only we could get people to stop falling for phishing emails!
Research shows that over 90% of network breaches happen when an employee falls prey to a phishing email, clicking on the offered link or opening a file attachment, becoming infected with a remote access Trojan, and creating an entry point for the attacker. If only we could get people to stop falling for phishing emails!
This is really not such a hard thing to do. ...
Continue Reading →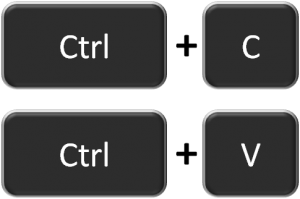 Using copy and paste to save text from websites is something all of us commonly do. Nothing could be simpler, right? Highlight your text, then <ctrl> c, and <ctrl> v. It turns out that this can be dangerous.
Using copy and paste to save text from websites is something all of us commonly do. Nothing could be simpler, right? Highlight your text, then <ctrl> c, and <ctrl> v. It turns out that this can be dangerous.
A new article on Naked Security tells how it is now possible to use copy and paste to inject malware code from a web site ...
Continue Reading →Thanks to QZ.com (The insults in other languages that sound the strangest in English) for these nuggets. Inspired by cjmerc39’s Reddit post.
 On Wednesday we discussed the many, many ways your smartphone is vulnerable to attack. Today we will look at solutions. Smart mobile devices need to be secured just as you would a laptop or desktop computer The small size and easy portability of smartphones and tablets make them easier to steal or lose. Some of our recommendations:
On Wednesday we discussed the many, many ways your smartphone is vulnerable to attack. Today we will look at solutions. Smart mobile devices need to be secured just as you would a laptop or desktop computer The small size and easy portability of smartphones and tablets make them easier to steal or lose. Some of our recommendations:
 Mobile smart devices have all the capabilities of a laptop or computer. What this means from a cybersecurity perspective is that they are every bit as vulnerable as a laptop or desktop computer. The fact that they are small makes them easy for a thief to slip in a pocket or backpack and carry away, along with your personal information, contacts, pictures, geo-location history, and a raft of critical and revealing ...
Mobile smart devices have all the capabilities of a laptop or computer. What this means from a cybersecurity perspective is that they are every bit as vulnerable as a laptop or desktop computer. The fact that they are small makes them easy for a thief to slip in a pocket or backpack and carry away, along with your personal information, contacts, pictures, geo-location history, and a raft of critical and revealing ...
 Microsoft has made Windows 10 one of the most highly personalized and cloud integrated operating systems ever, and this may introduce new security risks into using your computer. They do this by keeping track of what you do, where you go an the Internet, and what you are typing. This is how features such as Cortana get to know your preferences, and begin to make suggestions. Microsoft says this information is ...
Microsoft has made Windows 10 one of the most highly personalized and cloud integrated operating systems ever, and this may introduce new security risks into using your computer. They do this by keeping track of what you do, where you go an the Internet, and what you are typing. This is how features such as Cortana get to know your preferences, and begin to make suggestions. Microsoft says this information is ...