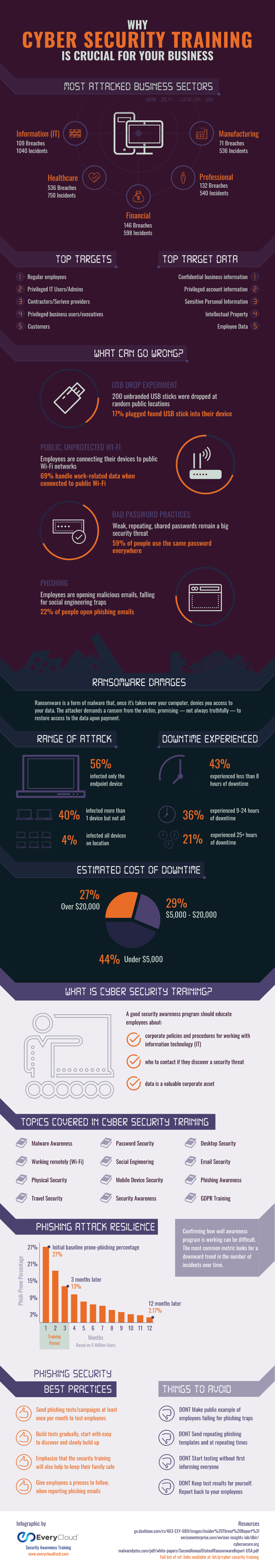
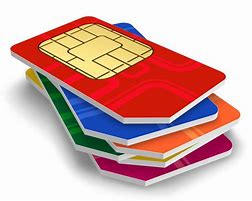
 In the middle of the day your cell phone mysteriously goes dead. Later on, when you call the cell phone carrier, you find out that someone else pretending to be you has visited a store and claimed to have lost your phone. Customer service agents moved your mobile number to a new SIM card on a new phone, and using your phone and other personal information gathered earlier through phishing scams ...
In the middle of the day your cell phone mysteriously goes dead. Later on, when you call the cell phone carrier, you find out that someone else pretending to be you has visited a store and claimed to have lost your phone. Customer service agents moved your mobile number to a new SIM card on a new phone, and using your phone and other personal information gathered earlier through phishing scams ...
SEP