![]() Is there a way to maintain privacy online, and defeat tracking without resorting to extreme measures? We have written articles recently about the most private browsers, but using them requires changing habits and abandoning web browsers that you are already familiar with.
Is there a way to maintain privacy online, and defeat tracking without resorting to extreme measures? We have written articles recently about the most private browsers, but using them requires changing habits and abandoning web browsers that you are already familiar with.
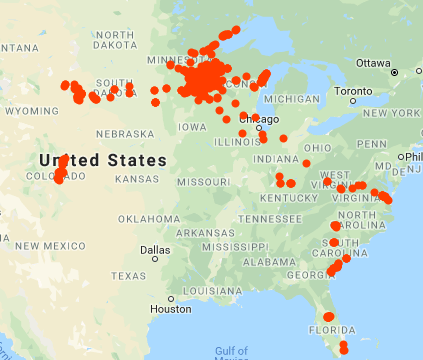
I came across this graphic on Pinterest, and thought it was worth sharing. It shows some pretty ...
Continue Reading →FEB