 If you visited certain websites with your iPhone (or Android or Windows device**) over the last two years, it is possible that your iPhone downloaded and installed malware that allowed attackers to intercept and record everything you did and everywhere you went with your iPhone. This includes real-time location information, all your emails and messaging (including encrypted versions such as WhatsApp, Telegram and iMessage), web browsing history, phone calls and call history, saved passwords in the Keychain, contacts, calendars, photos, and videos.
If you visited certain websites with your iPhone (or Android or Windows device**) over the last two years, it is possible that your iPhone downloaded and installed malware that allowed attackers to intercept and record everything you did and everywhere you went with your iPhone. This includes real-time location information, all your emails and messaging (including encrypted versions such as WhatsApp, Telegram and iMessage), web browsing history, phone calls and call history, saved passwords in the Keychain, contacts, calendars, photos, and videos.
This was discovered recently by Google Project Zero. It appears to be an example of a “watering hole” style attack. A watering hole attack usually compromises a website used by people who work in a specific business sector or company, or share a political affiliation or common social interest. It is a more targeted attack focused on a specific group of people. The websites used in this attack were created to attract a specific group of users with a shared special interest. The entire website might have been a fake, or the attackers may have compromised an existing legitimate site. In either case, any visitors connecting to the infected sites with an iPhone would have been infected themselves, and their iPhones completely compromised. Investigators and researchers think that the targeted group may have a common political affiliation or social interest, and the attackers were most likely a nation-state organization.
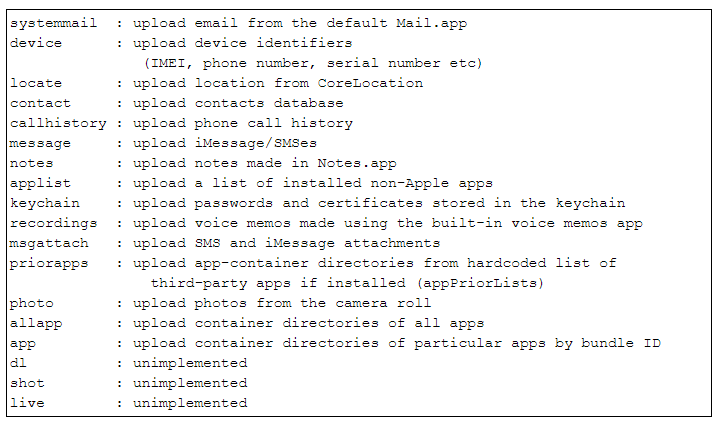
Here’s a list of commands that the attackers could execute on a compromised iPhone.
Evidently, if you rebooted your phone at any point in the last two years, the malware was disabled, and you would have had to revisit the website to get reinfected. And if you have updated to iOS version 12.1.4 (February 2019 release) your phone has been updated to remove this infection and prevent it from recurring. To check what version you’re using, go to Settings > General > Software Update. This will tell you what version of iOS you’re using and if a newer version is available.
**New information available at the beginning of September indicates that this exploit also targeted Android phones and Windows devices as well. If you are using a watering hole attack, as these attackers were after a specific group of people, not specific devices.
ShareSEP




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com