JAN
JAN
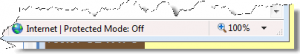
An alert client of mine called me in to “fix” a problem with their browser. IE7 was indicating in the status bar at the bottom of the window that Protected Mode was off. (see illustration)
 Going to the Tools menu, I opened Internet Options and clicked the Security tab. Protected mode was showing as enabled!! What gives??
Going to the Tools menu, I opened Internet Options and clicked the Security tab. Protected mode was showing as enabled!! What gives??
Beware of Valentine’s Day greetings in your e-mail, and DO NOT click throough on any links. As reported in IT World, a new malicious bot is being distributed disquised as a Valentine’s greeting.
Continue Reading →Multiple security vendors, including MX Logic Inc. , Trend Micro Inc. and Panda Security, have issued alerts about new Valentine’s Day-themed spam campaigns that try to dupe users into installing ...
President Obama is getting to keep his Blackberry, sort of…. As a technologist, I did refuse to vote for a Presidential candidate who could not even do his own e-mail. Frankly, I am tired of the fact that technological kindergarteners, illiterates, and phobics make technology policy in the country, and the fact that Obama “gets” tech and uses it was a big plus for me. Not quite enough to have gotten my vote, but the ...
Continue Reading →I read a number of computer security related blogs and email newsletters, and a couple of items came across my desk (ok, through my inbox) today that I thought worth passing on. For those of you who wonder why people write malware, here are a couple of articles worth a read. (I won’t call this stuff a “viruses” anymore. These are high quality malicious software programs – i.e. “malware,” written by professional software designers.)
Continue Reading →
JAN
Throughout most of 2008 it seemed that virus and spayware infections were decreasing, and I assumed that meant that the Anti-Virus and Anti-Spyware software comapnies had a handle on dectection and prevention. But in the last 2 months, it appears that the forces of darkness are back with better than ever mal-ware products that are taking over machines of my clients.
Most of this seems to be delivered via e-mail, usually in the form of ...
I have been harping long and loud recently about the purpose of malware writing. It’s about the money. No one is writing viuses for notoriety, fun, and fleeting fame anymore. It’s about the money – it’s phishing, it’s spam, it’s botnets, it’s identity theft and credit card and banking fraud.
But there may be some relief. It appears that phishing, at least, has hit the wall of diminishing returns. ...
It has been my contention for some time now that the only company able to take on Microsoft for world-wide dominion of the information technology space would be Google. There is evidence from the Internet traffic monitoring service Net Applications that there are other contneders nibbling away at the Kingdom of Redmond. Here is a quote from an aticle by John Murrell at SiliconValley.com.
Continue Reading →Last month, Microsoft’s Internet Explorer was used by 68.15 percent ...
One of my collegues sent a link to a BBC article about the Sinowal Trojan horse , which is also known as Torpig and Mebroot. This trojan installs itself on victims’ computers when they simply visit certain web sites, and collects banking and credit card information and reports back to the what appear to be eastern European and Russian criminal gangs, such as the Russin Business Network. Links to the article are here.
Your best form of protection ...
Continue Reading →