 A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.
ILOVEYOU: The Love Bug virus is 20 years old – could it happen again?
The Love Bug virus is 20 years old. It was also known as ILOVEYOU because it spewed itself out in emails with those three words, jammed together as one, in the subject line. This was one of the first mass mailing worms I ...
Continue Reading →MAY

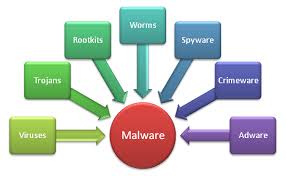


 We have been recommending Windows Defender as an acceptable anti-malware program. What we like about it is that it comes baked into the Windows 10 operating system, and gets its malware definitions updates with the other Windows security and feature updates that users are already receiving. And it is free. Plus it keeps your system a little less cluttered than adding a third party anti-malware product.
We have been recommending Windows Defender as an acceptable anti-malware program. What we like about it is that it comes baked into the Windows 10 operating system, and gets its malware definitions updates with the other Windows security and feature updates that users are already receiving. And it is free. Plus it keeps your system a little less cluttered than adding a third party anti-malware product.