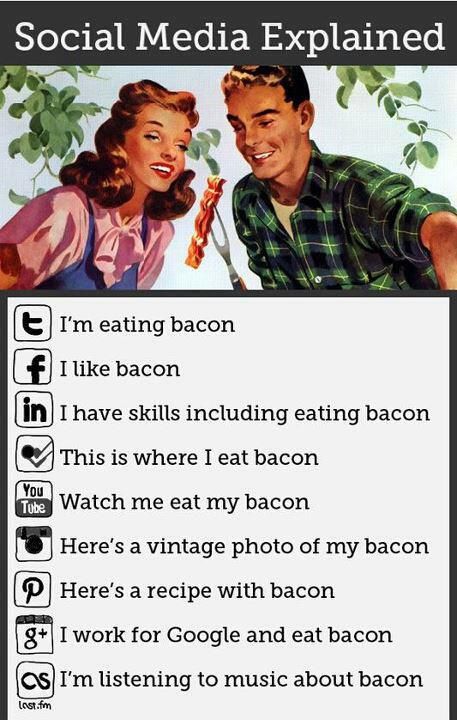
 Many social network sites make it too easy to overshare personal information. An innocent post to Twitter or Facebook, or pictures uploaded to SnapChat or Instagram can help a criminal target you. Online posts that identify your location, your travel and vacation plans, your employer, your home, and your personal possessions can be used by criminals to plan an crime. Kidnapping ...
Many social network sites make it too easy to overshare personal information. An innocent post to Twitter or Facebook, or pictures uploaded to SnapChat or Instagram can help a criminal target you. Online posts that identify your location, your travel and vacation plans, your employer, your home, and your personal possessions can be used by criminals to plan an crime. Kidnapping ...
MAR

 2017 is promising to be another difficult year for cyber-defenders who are protecting company and government networks from attack. Here are what I think will be the top attack vectors this year.
2017 is promising to be another difficult year for cyber-defenders who are protecting company and government networks from attack. Here are what I think will be the top attack vectors this year. US-CERT just released more information about the Grizzly Steppe cybercrime group who has been fingered for hacking the DNC and US voter registration databases. The short report, titled
US-CERT just released more information about the Grizzly Steppe cybercrime group who has been fingered for hacking the DNC and US voter registration databases. The short report, titled 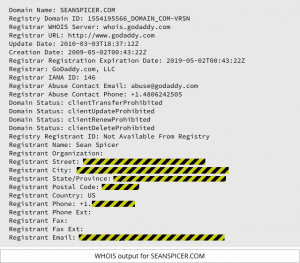 I will start out by admitting that I hate Domain Privacy. But I just read a story in
I will start out by admitting that I hate Domain Privacy. But I just read a story in  Remember late last year when the Russian Cyber Army was supposedly hacking the Vermont electrical grid?
Remember late last year when the Russian Cyber Army was supposedly hacking the Vermont electrical grid?
 I read an interesting article on Naked Security the other day about how Hamas had used Facebook and social engineering tactics to trick Israeli soldiers into installing surveillance malware. The malware allowed Hamas to track the soldiers using the phone’s GPS, and to turn on the microphone and video to actually listen in and and watch their targets. Hamas undoubtedly picked up the ...
I read an interesting article on Naked Security the other day about how Hamas had used Facebook and social engineering tactics to trick Israeli soldiers into installing surveillance malware. The malware allowed Hamas to track the soldiers using the phone’s GPS, and to turn on the microphone and video to actually listen in and and watch their targets. Hamas undoubtedly picked up the ...