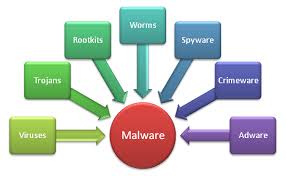
Is it a USB cable or a Trojan horse? We have come to consider Trojan horses to be malicious software these days, and part of the virtual world, But the original Trojan Horse was a very physical device. And so is this stunning USB style Trojan.
Is it a USB cable or a Trojan horse? We have come to consider Trojan horses to be malicious software these days, and part of the virtual world, But the original Trojan Horse was a very physical device. And so is this stunning USB style Trojan.
Called the O.MG Cable by its creator, Mike Grover, whose online handle is MG, this device ...
Continue Reading →MAR