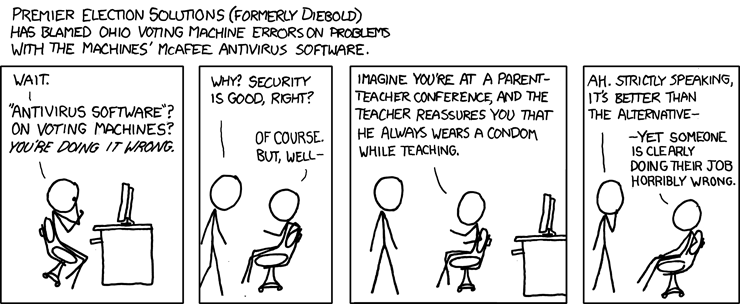
Tuesday we get to vote for president again. Worried about the security of electronic voting machines? You are not alone, but you would not find any political or election officials in your group. They think everything is fine! The fact that your next president may be elected by the Russian Cyber Army is OK, I guess. So that means Trump.
Here’s a little humor to make the nightmare seems more acceptable.
 Continue Reading →
Continue Reading →
NOV

 On of the more hopeful presentations from the Cyber Security Summit was presented by Tony Sager from the Center for Internet Security. Titled “Making Best Practices Common Practices: The CIS Controls,” Tony provided us with a road map for implementing secure practices in our networks.
On of the more hopeful presentations from the Cyber Security Summit was presented by Tony Sager from the Center for Internet Security. Titled “Making Best Practices Common Practices: The CIS Controls,” Tony provided us with a road map for implementing secure practices in our networks. On Monday we looked at the some of the primary attack vectors used by cyber-criminals. Here are the rest of the attack vectors that Kevin Thompson from FireEye shared at the Cyber Security Summit. Many of these are significant twists on old exploits, or more sophisticated exploits.
On Monday we looked at the some of the primary attack vectors used by cyber-criminals. Here are the rest of the attack vectors that Kevin Thompson from FireEye shared at the Cyber Security Summit. Many of these are significant twists on old exploits, or more sophisticated exploits.
 In the last several days, we have seen big distributed denial of service (DDoS) attacks against DynDNS, an Internet services company that provides domain name services (DNS) to many companies including Twitter and PayPal. DNS is how web sites are found on the web, you enter a web address in your browser, and DNS finds the website you are looking for. When attacked in ...
In the last several days, we have seen big distributed denial of service (DDoS) attacks against DynDNS, an Internet services company that provides domain name services (DNS) to many companies including Twitter and PayPal. DNS is how web sites are found on the web, you enter a web address in your browser, and DNS finds the website you are looking for. When attacked in ...
 NIST has created a self assessment tool for companies and organization who are working through the
NIST has created a self assessment tool for companies and organization who are working through the