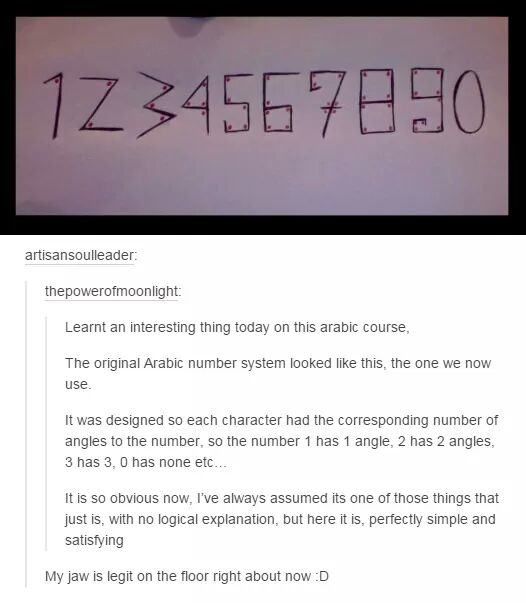
Found this on Pinterest again. Very interesting story about the origins of our numbers.
DEC
Found this on Pinterest again. Very interesting story about the origins of our numbers.
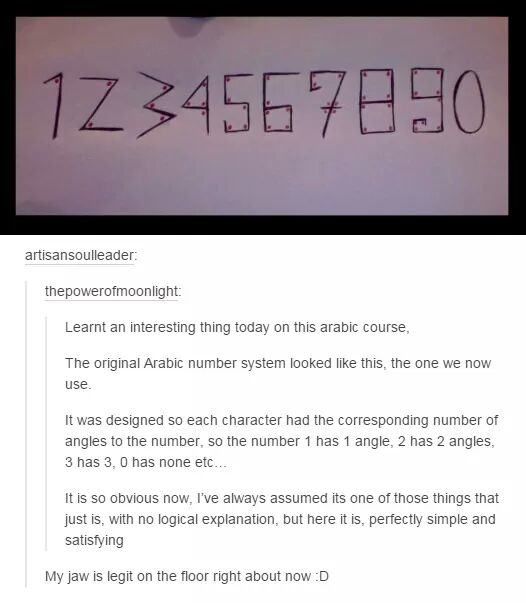
 SHA-1 or Secure Hashing Algorithm 1 was developed in 1993 by the National Security Agency (NSA). It has been used to provide both hashing functions and digital signatures that validate that a certain document, web site, or other resource is genuine, original, and unchanged.
SHA-1 or Secure Hashing Algorithm 1 was developed in 1993 by the National Security Agency (NSA). It has been used to provide both hashing functions and digital signatures that validate that a certain document, web site, or other resource is genuine, original, and unchanged.
SHA-1 is used in common services such as SSL (secure websites) and TLS (secure email). There has been discussion about the low security of SHA-1 going back to ...
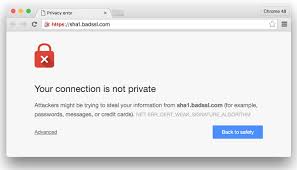
Continue Reading → On Monday we attacked the utility of current password policies and standards. Today we will offer up an array of improvements.
On Monday we attacked the utility of current password policies and standards. Today we will offer up an array of improvements.
To be truly effective from a security perspective, password policies need to be designed to withstand both online and offline password cracking methods. We discussed offline methods in our post last month, so we will not do more than recap them ...
Continue Reading → Most corporate password policies are a waste off time and do not add anything extra to providing secure authentication. Many of these policies were put in place to meet the standards of various compliance bodies (PCI-DSS, HIPAA, etc.) But basically these policies are not keeping up with the state of the art in password cracking, as we discussed last November in our post on ...
Most corporate password policies are a waste off time and do not add anything extra to providing secure authentication. Many of these policies were put in place to meet the standards of various compliance bodies (PCI-DSS, HIPAA, etc.) But basically these policies are not keeping up with the state of the art in password cracking, as we discussed last November in our post on ...
 If you have been the victim of a ransomware scam, or fake tech support scam, or other computer incident, intrusion, or breach, you may be wondering if you should report it to the police.
If you have been the victim of a ransomware scam, or fake tech support scam, or other computer incident, intrusion, or breach, you may be wondering if you should report it to the police.
If you report your crime to the police, it is unlikely that it is going to be solved and the perpetrator arrested. Many local police departments have a computer fraud officer or even a larger group, but there ...
Continue Reading → The site Adult Friend Finder, the “world’s largest sex and swingers site” recently exposed 412 million user credentials due to poor, or in some cases, non-existent password hashing practices. The biggest group losses were:
The site Adult Friend Finder, the “world’s largest sex and swingers site” recently exposed 412 million user credentials due to poor, or in some cases, non-existent password hashing practices. The biggest group losses were:
As we discussed last week, the reason that the Yahoo breach went unreported ...
Continue Reading → It was recently reported in Naked Security that a Seattle television news crew interviewed an Office Depot employee who alerted them to the practice of selling in-store repair scams to customers who came in looking for computer help. This whistle-blower told a story where employees where encouraged and even pressured to run the chain’s “PC Health Check” on evey ...
It was recently reported in Naked Security that a Seattle television news crew interviewed an Office Depot employee who alerted them to the practice of selling in-store repair scams to customers who came in looking for computer help. This whistle-blower told a story where employees where encouraged and even pressured to run the chain’s “PC Health Check” on evey ...
 From Pinterest. As we approach the holiday season, we ask ourselves the perennial question – Why did Walmart put 24 checkout aisles in the store if they are only going to open 5 of them?
From Pinterest. As we approach the holiday season, we ask ourselves the perennial question – Why did Walmart put 24 checkout aisles in the store if they are only going to open 5 of them?
They remodeled the Walmart in Stillwater (actually Oak Park Heights) maybe ten years ago, and tore out a bunch of merchandise space to put in two dozen ...
Continue Reading →We are taking the day off from our usual schedule to give thanks for many blessings, and to enjoy the day with friends and family.
Continue Reading →