 Most corporate password policies are a waste off time and do not add anything extra to providing secure authentication. Many of these policies were put in place to meet the standards of various compliance bodies (PCI-DSS, HIPAA, etc.) But basically these policies are not keeping up with the state of the art in password cracking, as we discussed last November in our post on password cracking.
Most corporate password policies are a waste off time and do not add anything extra to providing secure authentication. Many of these policies were put in place to meet the standards of various compliance bodies (PCI-DSS, HIPAA, etc.) But basically these policies are not keeping up with the state of the art in password cracking, as we discussed last November in our post on password cracking.
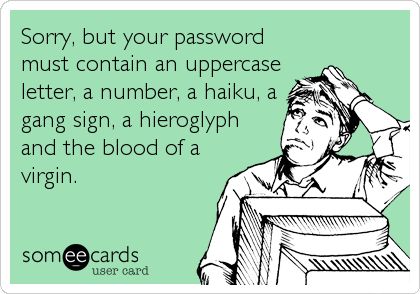
Let’s look at a common password policy standard and find out what is wrong with it.
- Length – Most password policies recommend a minimum length of only 8 characters. As we discussed last month, rainbow tables for all password possibilities of ten characters or less are available on the Dark Web, so password minimums need to be at least 11 characters. NIST is currently recommending a minimum of 14.
- Complexity – A password full of upper and lower case letters, numbers, and symbols is no more resistant to automated password cracking than a simpler password of the same length, for the reason stated above.
- Duration – Many password policies require changing the password every 90 days, and in high security facilities this may be as short as 45 or even 30 days. Here again, if the password length is 10 or less, your shiny new password already has a solution available on the Dark Web. Frequent password changes have been shown to lead to users selecting easier passwords, which defeats the purpose of having a policy.
On Wednesday we will close the loop and discuss several alternatives to the current set of password policies that would provide better security for user authentication.
More information:
- WyzGuys on password cracking
- WyzGuys on NIST’s password policy recommendations
- WyzGuys on password changing
- Bruce Schneier on password changing
- Naked Security on password strength
- Wikipedia – Pass the Hash
DEC




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com