The security thing we love to hate.
JUL
 Phishing Email Alerts
Phishing Email AlertsCatch of the Day: Wells Fargo Identity Theft Phish – A trifecta – bank account, personal information, and a credit card. On the Dark Web this is called a Fullz.
Chef’s Special: Phishing attacks impersonate QuickBooks invoices ahead of July 15 tax deadline
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources ...
Continue Reading → A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.The Wordfence Threat Intelligence Team just published details of an attack harvesting database credentials, targeting over 1 million WordPress sites. For 24 hours, attacks from this campaign accounted for 75% of all exploit attempts on plugins and themes across all of WordPress.
Both the free and paid versions ...
Continue Reading → A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.Does all this COVID-19 related ruling by Executive Order give you the Constitutional willies? Well, the Legislative Branch is doing its best to keep pace in the race to see which branch of the government can violate our rights the most. The government can keep on surveilling your online ...
Continue Reading → If you use Google for anything (and who doesn’t), it is a good idea to periodically check your your Google account security settings. If you have an Android phone, then there is a Gmail account attached to the phone, whether you use it or not. This account is tied to the GPS location history generated by your phone. It is also attached to Google Calendar, Google Contacts, Google Photos, any ...
If you use Google for anything (and who doesn’t), it is a good idea to periodically check your your Google account security settings. If you have an Android phone, then there is a Gmail account attached to the phone, whether you use it or not. This account is tied to the GPS location history generated by your phone. It is also attached to Google Calendar, Google Contacts, Google Photos, any ...
 I have been predicting the death of the password for several years now, but all of us are still using them, even if they are easily stolen, cracked, or bypassed. A password by itself is not all that secure anymore. But there are several simple steps you can take to make them more secure.
I have been predicting the death of the password for several years now, but all of us are still using them, even if they are easily stolen, cracked, or bypassed. A password by itself is not all that secure anymore. But there are several simple steps you can take to make them more secure.
Do not:
 A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.People Are Searching for Answers
After a night of confusion and uncertainty in which no results were reported for the Iowa Democratic caucus, people are searching for answers. As a cybersecurity journalist, I probably consider the hacking possibilities more than most, but it was hard not to wonder. Adding to the ...
 There is only one person that you can rely on to keep you protected in your online life – and that person is YOU! Because the bad actors on the network target people more frequently than machines, this means that we more likely to be the first point of contact in an exploit. We are ultimately responsible for keeping our online life ...
There is only one person that you can rely on to keep you protected in your online life – and that person is YOU! Because the bad actors on the network target people more frequently than machines, this means that we more likely to be the first point of contact in an exploit. We are ultimately responsible for keeping our online life ...
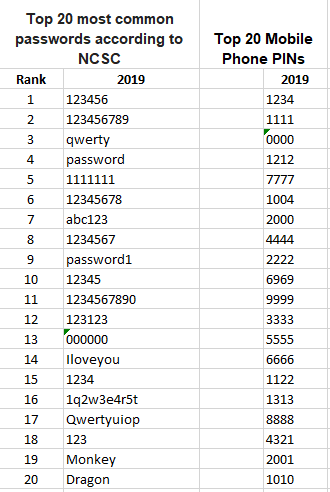 If you are using one of these passwords or PINs to “secure” your computer, smartphone, or online accounts you are in danger of having your digital life cracked and compromised. The passwords have been cracked, are on sale on the Dark Web, and will be the FIRST passwords tried by an attacker. If you are using one of these, please change it ...
If you are using one of these passwords or PINs to “secure” your computer, smartphone, or online accounts you are in danger of having your digital life cracked and compromised. The passwords have been cracked, are on sale on the Dark Web, and will be the FIRST passwords tried by an attacker. If you are using one of these, please change it ...
 Someone has stolen your user ID and password from a website where you have an account. Are you at risk? What are they going to do with it?
Someone has stolen your user ID and password from a website where you have an account. Are you at risk? What are they going to do with it?
Unfortunately, even with the best security, passwords are stolen all the time from websites and cloud service providers. There are over 15 billion stolen credentials. Usually the passwords are solved using off-line brute force password cracking methods, and then packaged up and sold ...
Continue Reading →