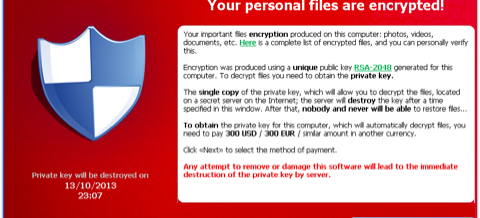
I have been writing about the latest threat, CryptoLocker, and promised I would report what ever Carbonite replied to my inquiry about whether CryptoLocker could encrypt online backups. Here is what they said:
Continue Reading →Computers infected with the CryptoLocker virus would indeed be at risk to having their online Carbonite backups also encrypted. In fact we see this on a daily basis unfortunately. Carbonite recognizes when a file previously backed up changes and automatically seeds it for backup. Assuming the client software ...
NOV