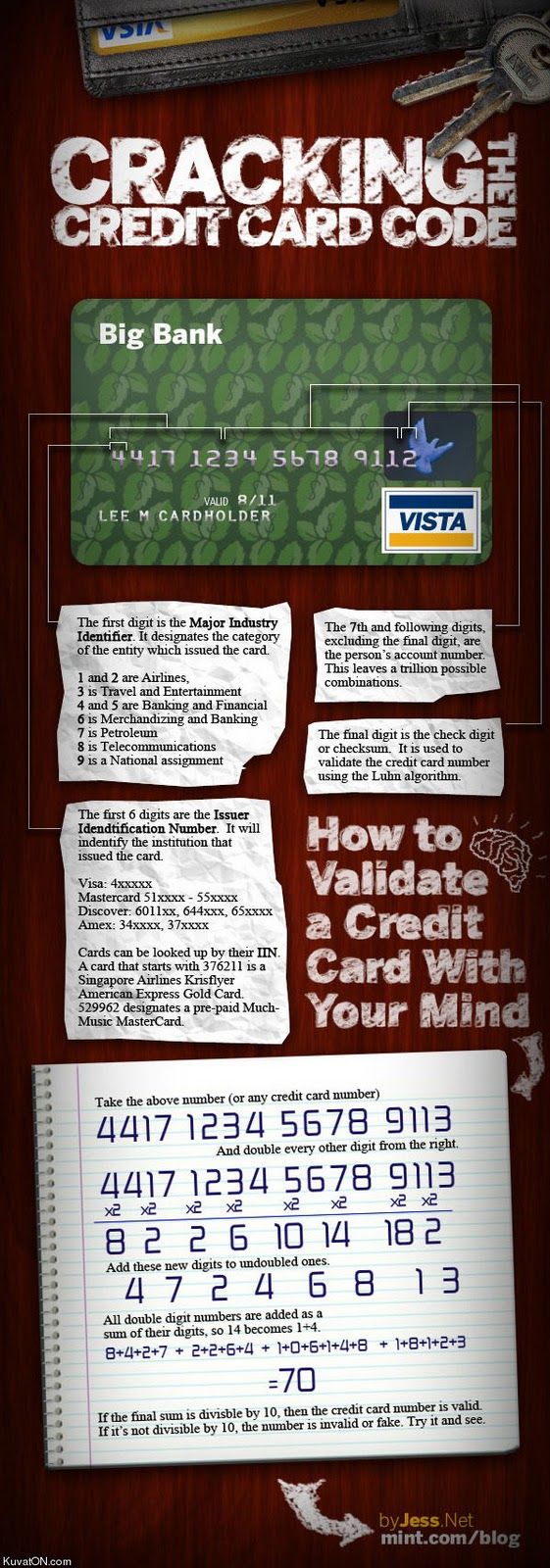
Thanks to mint.com for the following infographic. Credit card numbers are like social security numbers, different parts of the number tell a story. A credit card number, to be valid, has to conform to something called the Luhn algorithm. Basically, after doing some crazy math, the result needs to be divisible by 10.
Continue Reading →FEB


 If you are in high school (or junior high) or college, attracted to technology, and looking for a career with a future, then you should give serious consideration to the field of Cybersecurity. A recent press release from
If you are in high school (or junior high) or college, attracted to technology, and looking for a career with a future, then you should give serious consideration to the field of Cybersecurity. A recent press release from  Last week we took an in depth look at social engineering, and looked a phone and email examples in depth.
Last week we took an in depth look at social engineering, and looked a phone and email examples in depth.
 Here’s a provocative statement: If you could just prevent your staff for clicking on links or opening attachments in phishing emails, 95% of your cybersecurity problems would be prevented.
Here’s a provocative statement: If you could just prevent your staff for clicking on links or opening attachments in phishing emails, 95% of your cybersecurity problems would be prevented.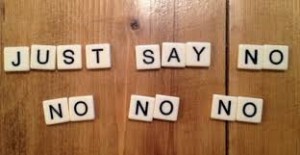 Your phone rings. The caller identifies themselves as someone from a “tech support” company. Your computer has problems, he says, and he called to help you fix them. You agree to pay some sort of fee. You help them set up remote access to your computer. And now you have been hacked and helped them do it.
Your phone rings. The caller identifies themselves as someone from a “tech support” company. Your computer has problems, he says, and he called to help you fix them. You agree to pay some sort of fee. You help them set up remote access to your computer. And now you have been hacked and helped them do it. This should really be called “anti-social” engineering. A good definition is “social engineering is a non-technical method of intrusion hackers use that relies heavily on human interaction and often involves tricking people into breaking normal security procedures. It is one of the greatest threats that organizations today encounter.”
This should really be called “anti-social” engineering. A good definition is “social engineering is a non-technical method of intrusion hackers use that relies heavily on human interaction and often involves tricking people into breaking normal security procedures. It is one of the greatest threats that organizations today encounter.”