Phishing Email Alerts
Catch of the Day: Amazon Gift Card Phish
Chef’s Special: Geek Squad Invoice Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Amazon Gift Card Phish
I’ve been seeing a lot of this one lately, and all of them were sent from the email accounts of people I know.
The email appears to be coming from his Outlook.com account, and a review of the email headers confirms that the email was send by an Outlook.com mail server. Whether it is really from his email account is hard to determine. It may be his email was hijacked. Or it may be that his email addressed is being spoofed on a different Outlook.com account.
He is reporting that many of his contacts are getting this same email, which would seem to indicate that his contact list has been compromised somehow.
In researching this situation I found this 2019 query on Microsoft Answers.
Scam
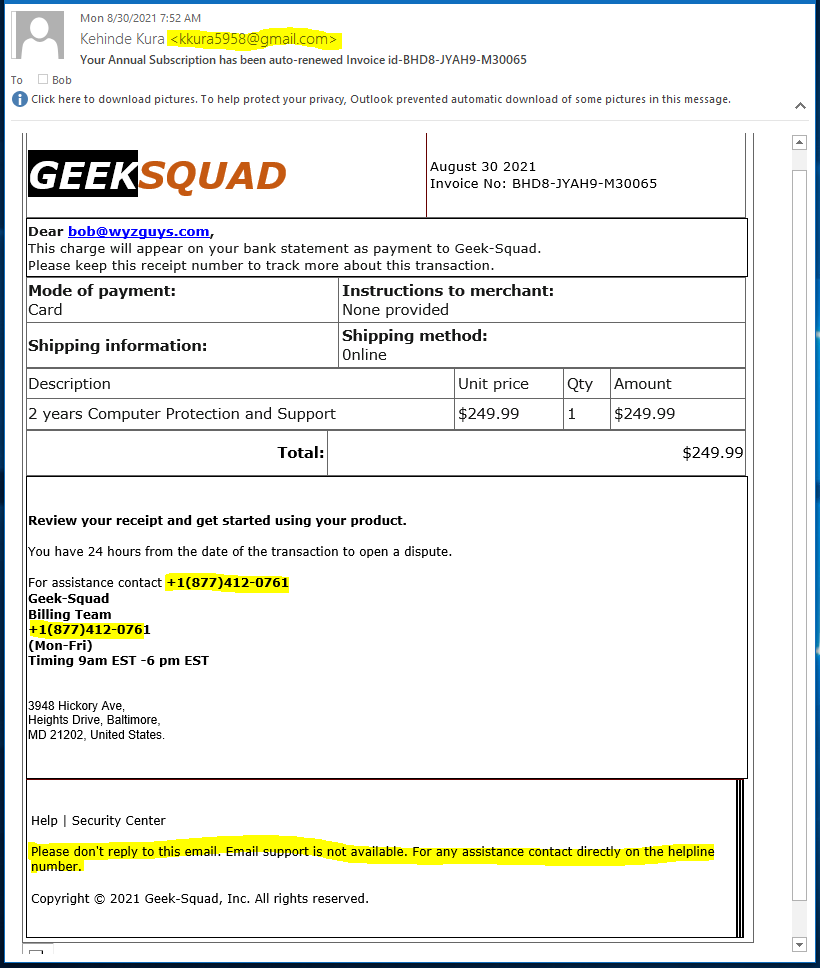
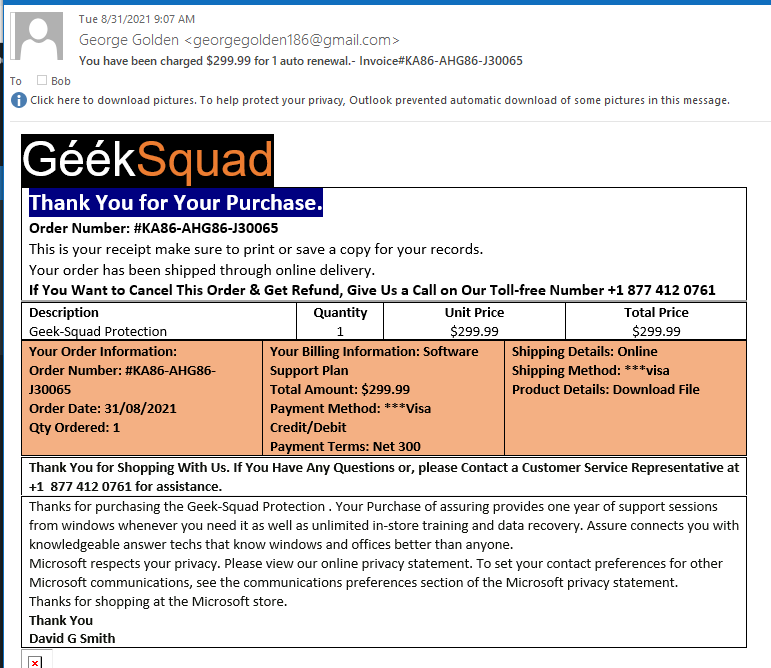
Geek Squad Invoice Phish
Another fake contract renewal invoice, this time seemingly from the Geek Squad. Clues on this one are the sender’s email address, which should have a Geek Squad domain, but doesn’t, and the toll free billing team number.
And this one a few days later
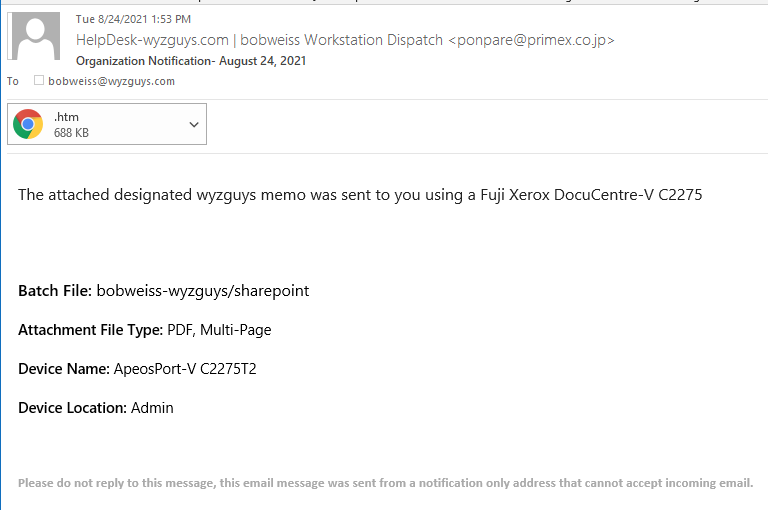
Outlook Web App Scanner Phish
This is designed to look like you received a scanned document. But the sender is from a Japanese domain, and is suspicious. All of the action is in the HTM (think web page) attachment.
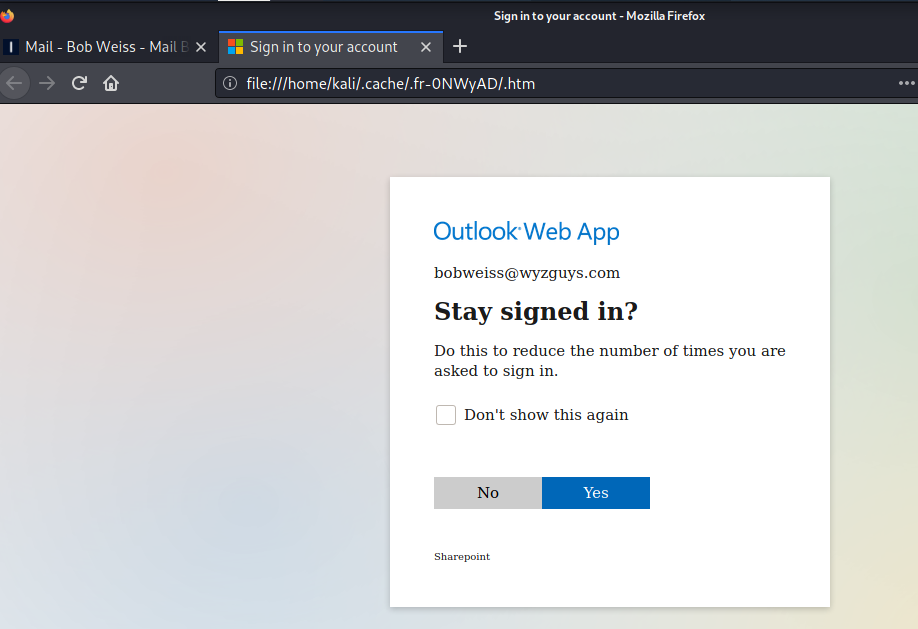
Opening the attachment (in Kali Linux) showed me this initial landing page. Looks like an Outlook Web App message box. When I clicked on YES, I got the next page
This is a password dialog, attempting to hijack your Office365 credentials
Beware of these sorts of messages. If you don’t know the sender, DO NOT open the attachment. Even if you know the sender, giving them a quick call (not email reply) to confirm that they sent it and wjhat is it about will keep you from becoming a victim for these sorts of scams.
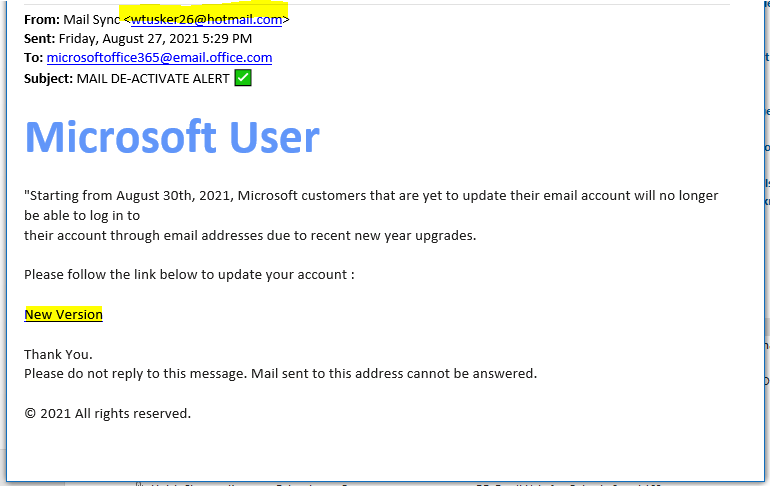
Microsoft Update Phish
A client of mine sent me this email, wondering if it was legitimate or not. It is not. Here’s the email.
The sender’s email address is the first clue. The New Version link resolves to
https://na01.safelinks.protection.outlook.com/?url=https%3A%2F%2Flinktr.ee%2Fhotmailewij&data=04%7C01%7C%7C8ccc3ed3718e4280328008d969ac40ab%7C84df9e7fe9f640afb435aaaaaaaaaaaa%7C1%7C0%7C637657010822988219%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000&sdata=avVEL0knHEzywC3TVmFgDrQ6duVkST7NwEYwzjBB%2BxM%3D&reserved=0
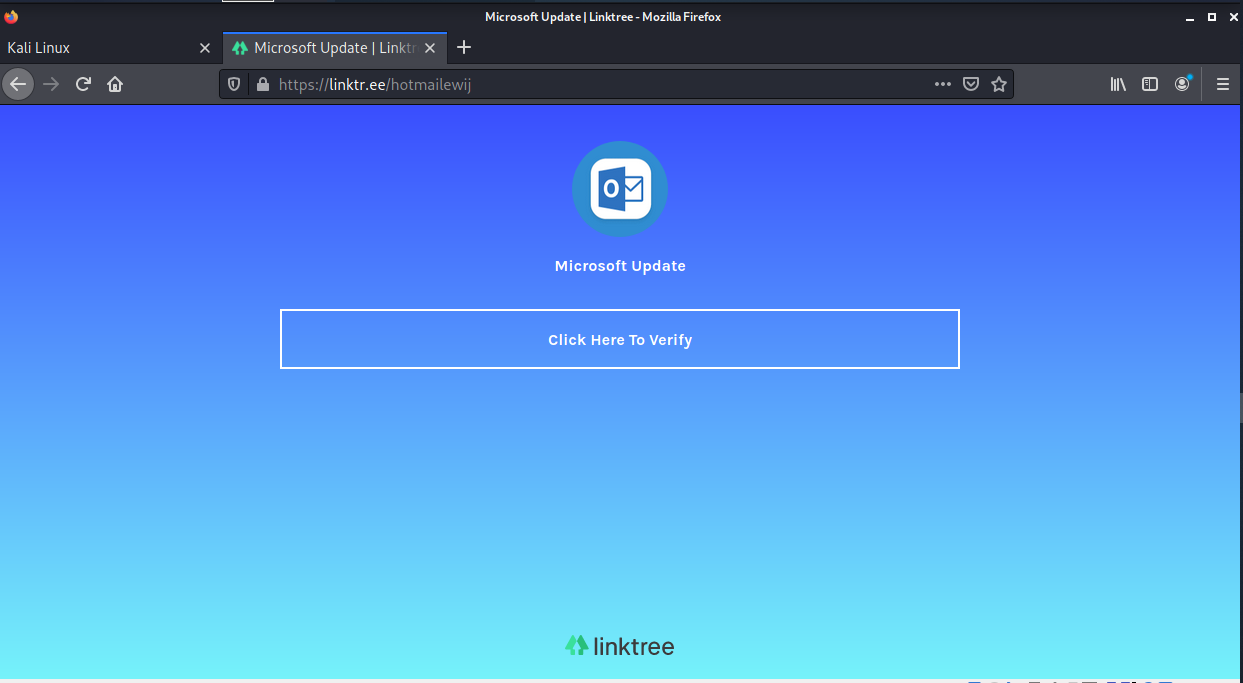
which redirects to https://linktr.ee/hotmailewij. Here is the landing page
Clicking on the Click Here to Verify took me to a second landing page on Weebly at https://hjbsdkj.weebly.com/ This is obviously an Outlook credential stealing exploit.
I put in some fake credentials to see what happened, next, but the game ended when I clicked on Next.
These sorts of attacks are very common these days, and you should treat any email asking you to renew, verify, or reactivate your account with deep suspicion. If you are wondering if it is real, close the email, and log into your online account the regular was, using the provider’s login URL, and NOT the link in the email.
Widespread credential phishing campaign abuses open redirector links
Microsoft has been actively tracking a widespread credential phishing campaign using open redirector links. Attackers combine these links with social engineering baits that impersonate well-known productivity tools and services to lure users into clicking. Doing so leads to a series of redirections—
In this campaign, we noticed that the emails seemed to follow a general pattern that displayed all the email content in a box with a large button that led to credential harvesting pages when clicked. The subject lines for the emails varied depending on the tool they impersonated. In general, we saw that the subject lines contained the recipient’s domain and a timestamp as shown in the examples below:
- [Recipient username] 1 New Notification
- Report Status for [Recipient Domain Name] at [Date and Time]
- Zoom Meeting for [Recipient Domain Name] at [Date and Time]
- Status for [Recipient Domain Name] at [Date and Time]
- Password Notification for [Recipient Domain Name] at [Date and Time]
- [Recipient username] eNotification
A Tricky New COVID-19 Phishing Caper
A new phishing campaign is exploiting the ongoing uncertainty about company policies related to COVID-19, according to Roger Kay at INKY. The campaign uses emails that purport to come from a company’s HR office informing employees that they’re required to fill out a COVID-19 vaccination status form.
Clicking on the link in the email will take the user to a Microsoft Outlook credential phishing page. “This campaign was able to bypass existing email security in a number of ways,” Kay says. “It sent the lures from legitimate but hijacked email accounts to evade standard security checks.
If the recipient clicked through, they were taken to a hijacked web page that impersonated a trusted brand. Because the phishers used a hijacked site, their exploit had not yet appeared on any threat intelligence feed. The sally was effectively a zero-day attack. More…
Share
SEP









About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com