 Catch of the Day – Donald Trump and Mike Pence phishing emails. Beware these official-looking “government” emails.
Catch of the Day – Donald Trump and Mike Pence phishing emails. Beware these official-looking “government” emails.
Chef’s Special – LogMeIn credential harvesting phish.
Phishing Email Alerts
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox.
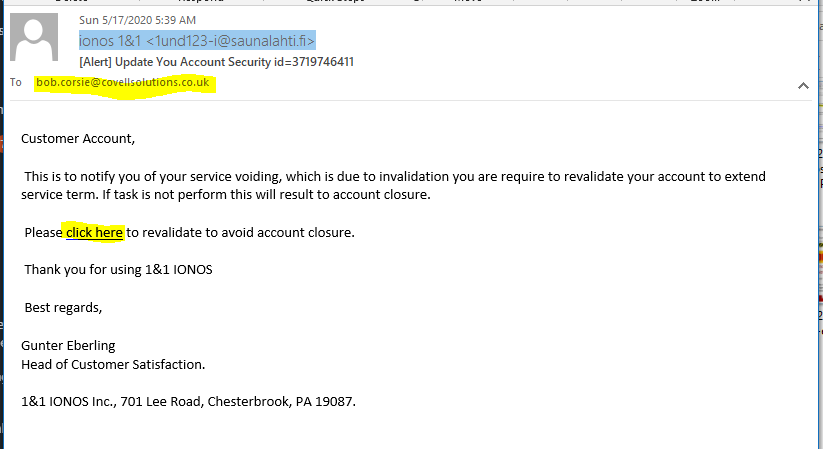
IONOS Update Your Account Security Phish
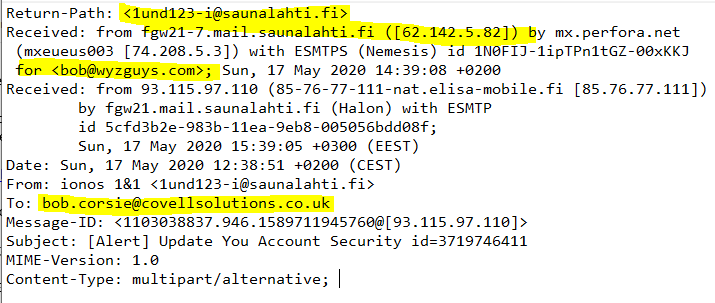
He is another phishing email designed to look like it was sent from my web hosting company, IONOS, formerly 1&1. The source email address is the first obvious clue this is a phish. The address 1und123-i<AT>saunalahti.fi does a fair job of spoofing a 1und1 address, but the email domain is for a Finnish sauna company
The destination email is to bob.corsie<AT>covellsolutions.co.uk. How this even ended up in my email box is a bit mysterious.
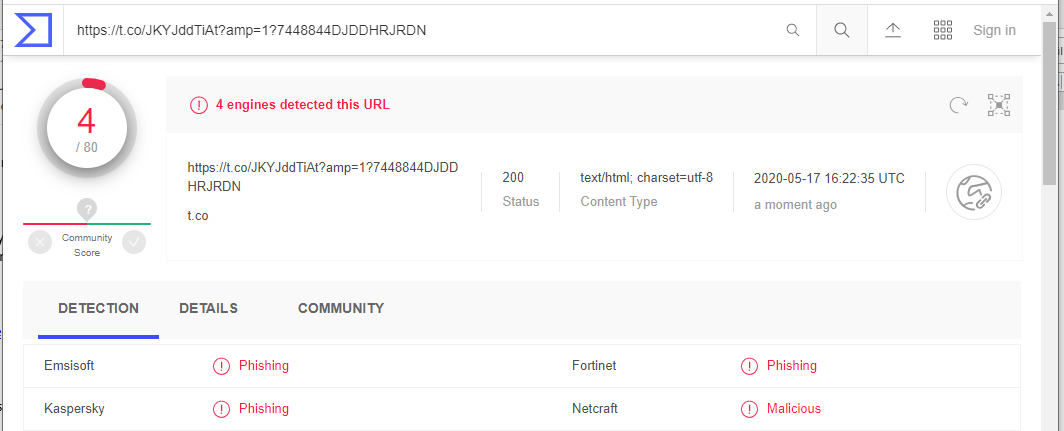
The email link resolved to: https://t.co/JKYJddTiAt?amp=1?7448844DJDDHRJRDN. A VirusTotal scan revealed this destination as a phishing site.
A quick look at the email headers showed that the destination address had been spoofed and the email was actually sent to my email address.
I opened a Linux virtual machine and clicked the link. The click here link redirected to a landing page at https://eresteredir987003.blogspot.com/6IDHDHDKS. This bounced once more to a Russian DNS address at http://u726573vi0.ha004.t.justns.ru/. At this point my journey ended, as the phishing landing page was no longer to be found. The following image was from Firefox on the Linux VM. End of the road for this scam, which has evidently already been taken down.
Amazon has placed your orders on hold phishing email
From Facebook, so I don’t know where the link goes, but certainly not to Amazon. Emails like this are always bogus. Never click on a link without verifying the destination. When in doubt, just log on to your Amazon account the way you usually do!
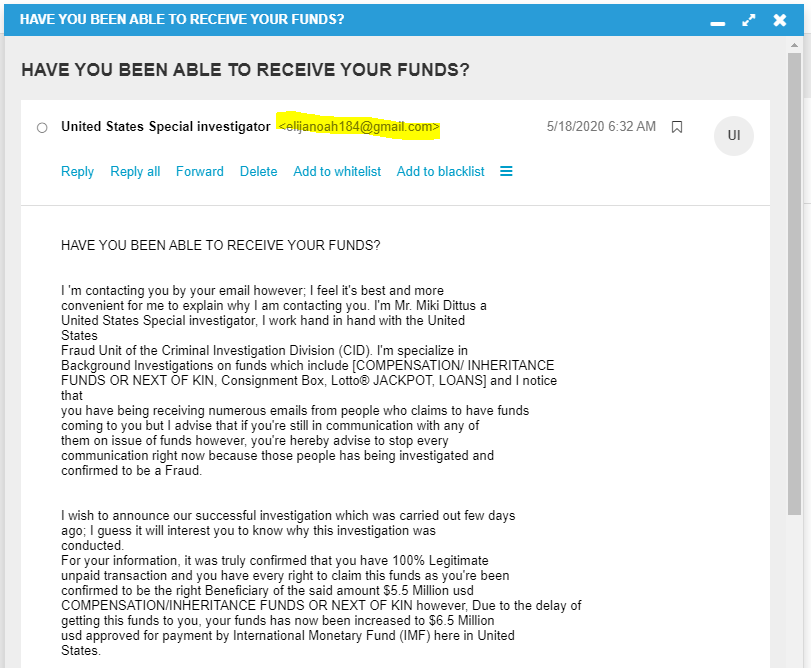
Another Example of the Advance Fee Phishing Email
Supposedly I inherited $65 million dollars. I am positive that a federal investigator” would not be using gmail to communicate.
The full text of the email follows.
United States Special investigator
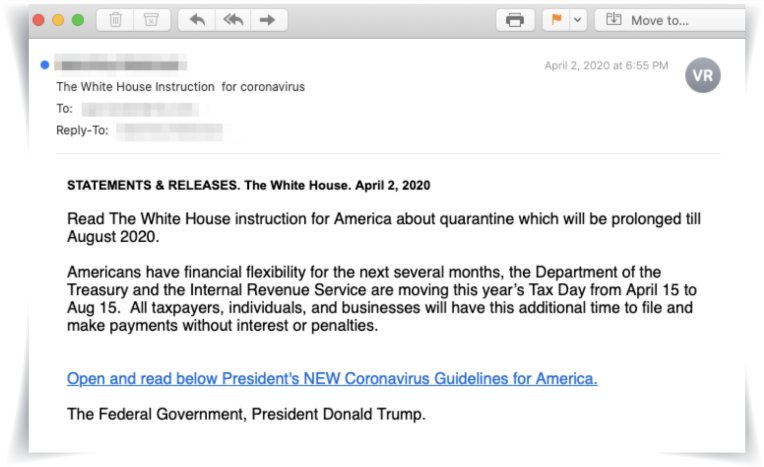
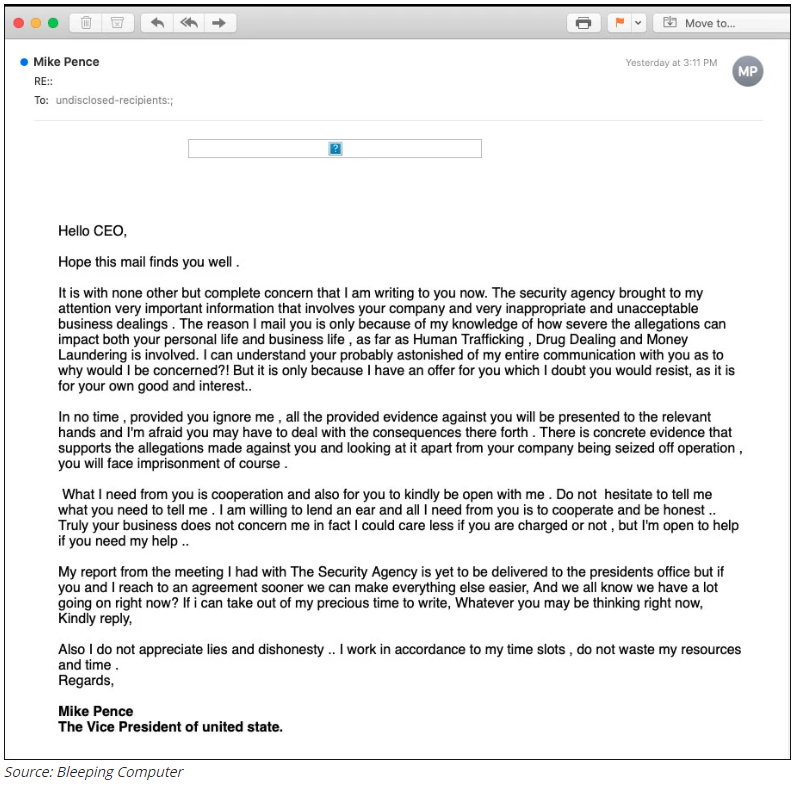
Emails from President Trump and VP Mike Pence are Fake Phish
Be on the lookout for fake emails regarding COVID-19 news from the President, Vice President, and frankly any government organization including the CDC, DHS, and other likely acronyms.
Watch out for the Coming Tsunami of Mortgage Rescue Phishing Scams
(From KnowBe4) At this point in time, with 10 years of phishing attack analysis under our belt, we can predict with a high reliability level what will be showing up in the near future. We see two scams that will be extremely popular during the rest of 2020. We will cover the first one in this blog post, the other one in a few days. With so many individuals out of work, furloughed, and having trouble keeping up with mortgage payments, I predict we’re going to see a resurgence of this scam. Read more…
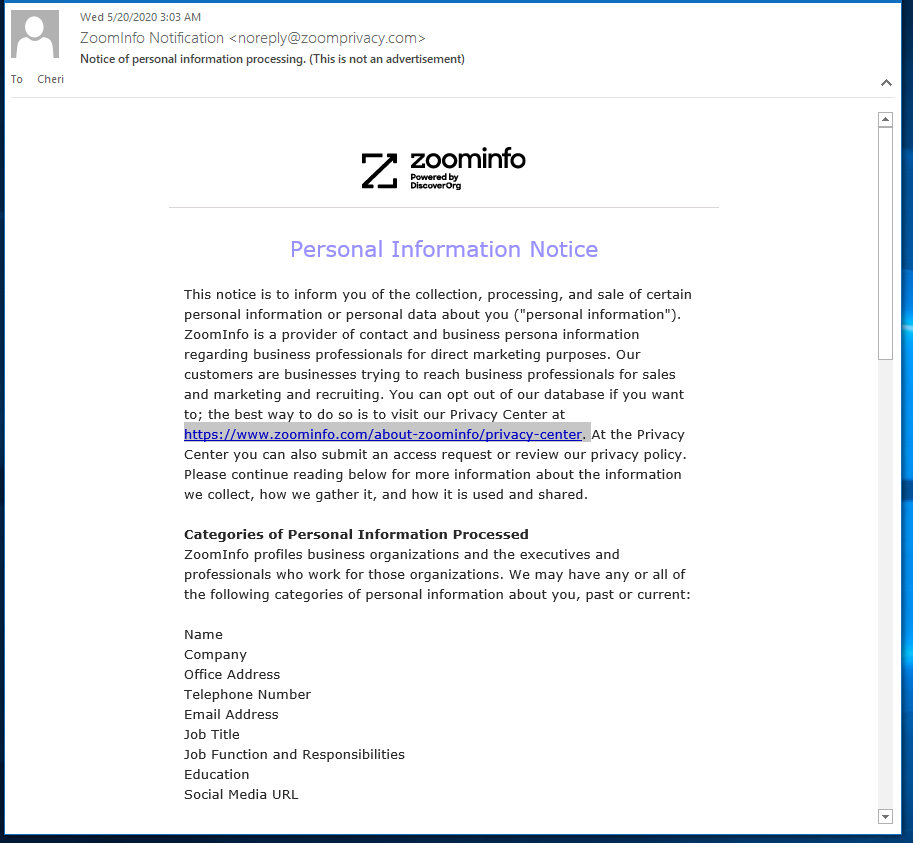
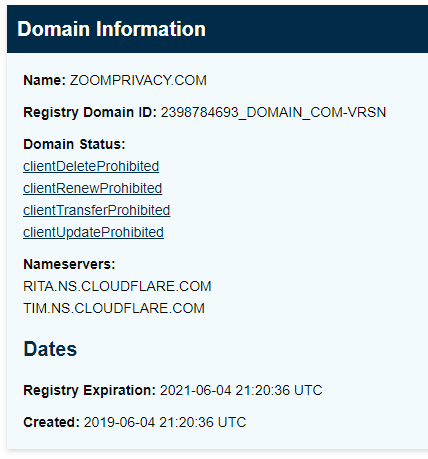
Suspicious Email from ZoomInfo?
Is this from Zoom? Or is ZoomInfo a different web site and business entity? This one raised my shields because of three issues. The first is the email domain zoomprivacy<dot>com. This domain is similar to the company’s principal domain zoom.us, but it has the potential to be registered by a scammer. According to ICAAN WHOIS this domain registration is less than a year old.
The email has a single link to another near-miss domain zoominfo<dot>com. But this link resolves to ANOTHER near-miss domain https://www.zoominfo<dot>com/about-zoominfo/privacy-center. The type of information being collected is an identity thief’s wet-dream. There is a lot of other information that I have not included, but this email DOES look very official and possibly legitimate. But the use of three near-miss domains, and the fact that my efforts to actual go to these web pages was met with problems. A quick Google search revealed that ZoomInfo has nothing to do with the conferencing app Zoom. One question answered.
But this is definitely a personal information vacuum cleaner (marketing company), and collects information about us all from scraping websites, and compiling databases with this content. This is beginning to look less like a phish, and more like an “invitation” to open a profile on ZoomInfo so I can more completely “share” my information. Thanks, but no thanks. But I may take a moment to go in and remove any data about myself that I can.
Beware of emails with “horrible charts” about Covid-19
These charts aren’t “horrible” because of their coronavirus data – they’re horrible because they could let criminals conquer your computer. Read more…
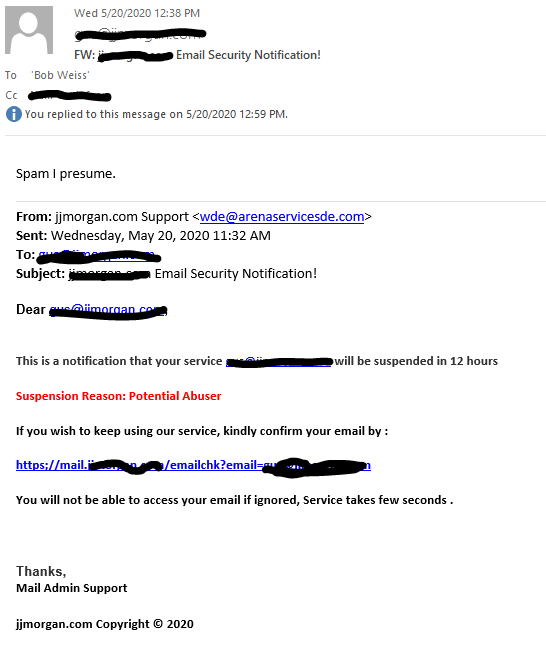
Fake Email Security Notification
This email was contributed by a client and I have redacted his information from the image. He correctly concluded this was “spam I presume.” The sender email looked dodgy.
The link resolved to https://pabeneentd.16-b.it, and displayed the following landing page.
This is a pretty standard credential harvesting operation, and entering your password would allow the attacker to hijack your email account, with usually devastating consequences.
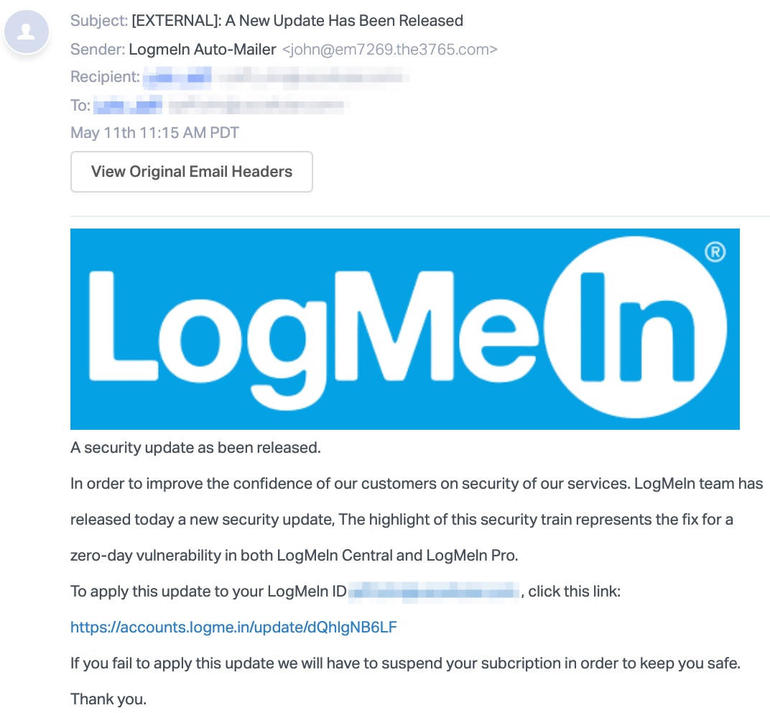
New phishing campaign impersonates LogMeIn to steal user credentials
From TechRepublic:
Spotting this new phishing attack for first time in May, Abnormal Security noted that the recent impersonations of LogMeIn and other remote collaboration tools such as Zoom are likely due to the shift in remote work. In this particular attack, the phishing email claims to be from LogMeIn with a notice informing the recipient of a fix to a zero day vulnerability found in LogMeIn Central and LogMeIn Pro. As such, this campaign is also taking advantage of the security concerns raised about these remote access platforms.
To apply this alleged security update, the user is told to click on a link in the email. A stern warning asserts that if the update is not applied, then the user’s account will have to be suspended for security reasons. Clicking on the link brings the recipient to a fake login page that appears similar to the actual LogMeIn page. The page also contains branding for password manager LastPass, which is the parent company for LogMeIn.
Of course, any credentials entered at the phony login page are captured by the criminals behind this attack. And since LogMeIn uses a single sign-on with LastPass, the attackers may be trying to gain access to the user’s password manager, potentially opening the door to all of the person’s stored passwords.
How can you best avoid these types of scams? Ken Liao, vice president of Cybersecurity Strategy at Abnormal, offers a concise recommendation.
“Many of the recent attacks have masqueraded as updates–even more specifically–security updates,” Liao said. “As always, users should default to updating applications via the application itself and not via links in emails to prevent not only credential loss but the potential introduction of malware onto their machines.”
MAY









About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com