Phishing Email Alerts
Catch of the Day: Domain Name Registration Phish
Chef’s Special: Intuit Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
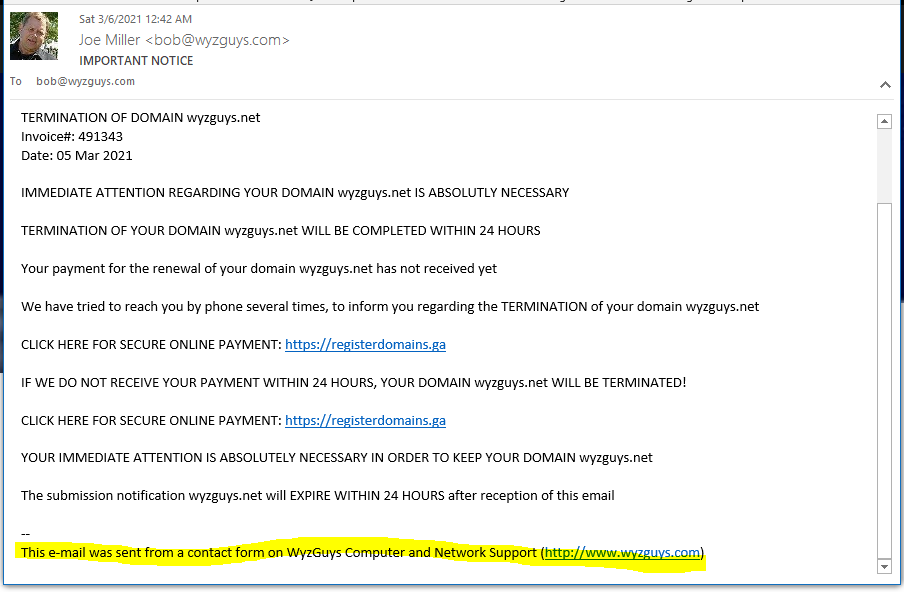
Domain Registration Scam Follow-up Phish
I posted this scam on March 5, but had to include the follow-up email I received on March 6. It is below. Again, the email was sent from my own website’s contact form, so totally not legit.
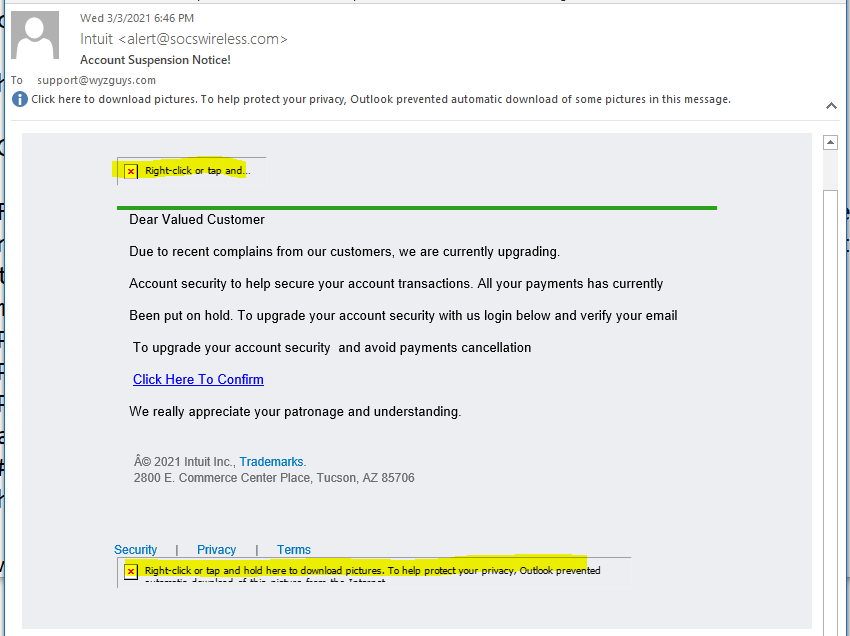
Intuit Phish
This phish didn’t get very far, by the time I researched it, the landing page had been taken down, and the image links were disabled. Nothing to see here, but I included it because Tax Season is upon us, and phish like this will be commonplace. If you want to log into to Intuit or some other tax preparation site, use a safe bookmark you have already saved, or just go to the web site directly. NO CLICKING ON EMAIL LINKS!
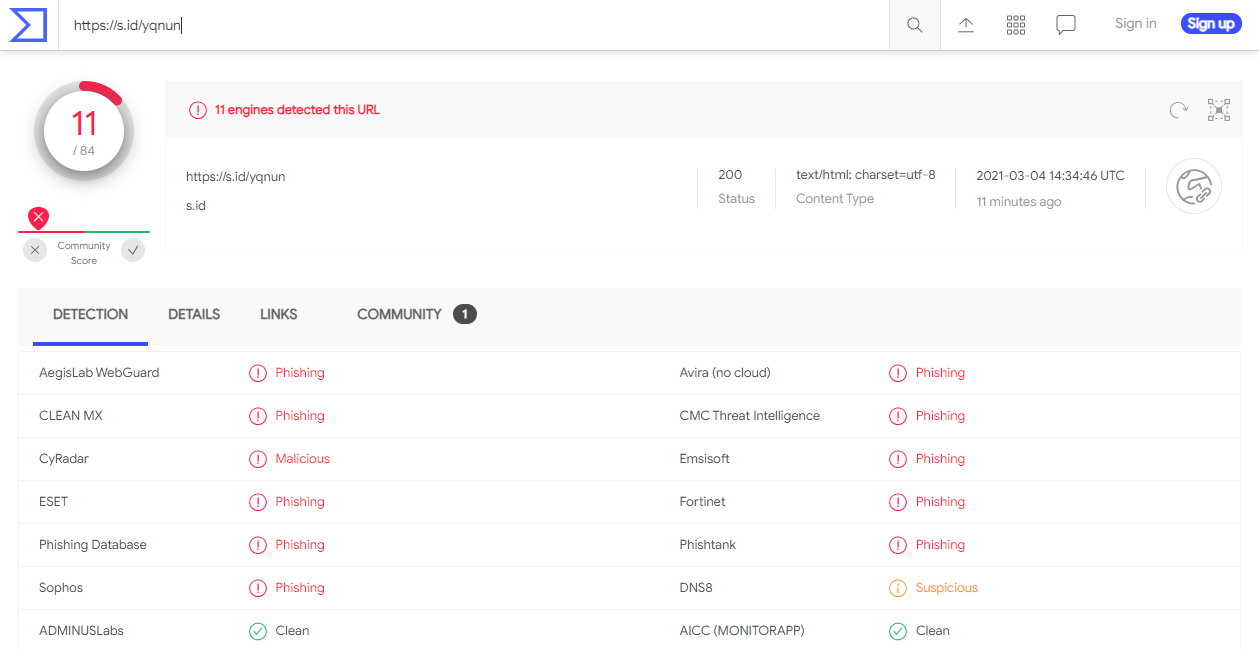
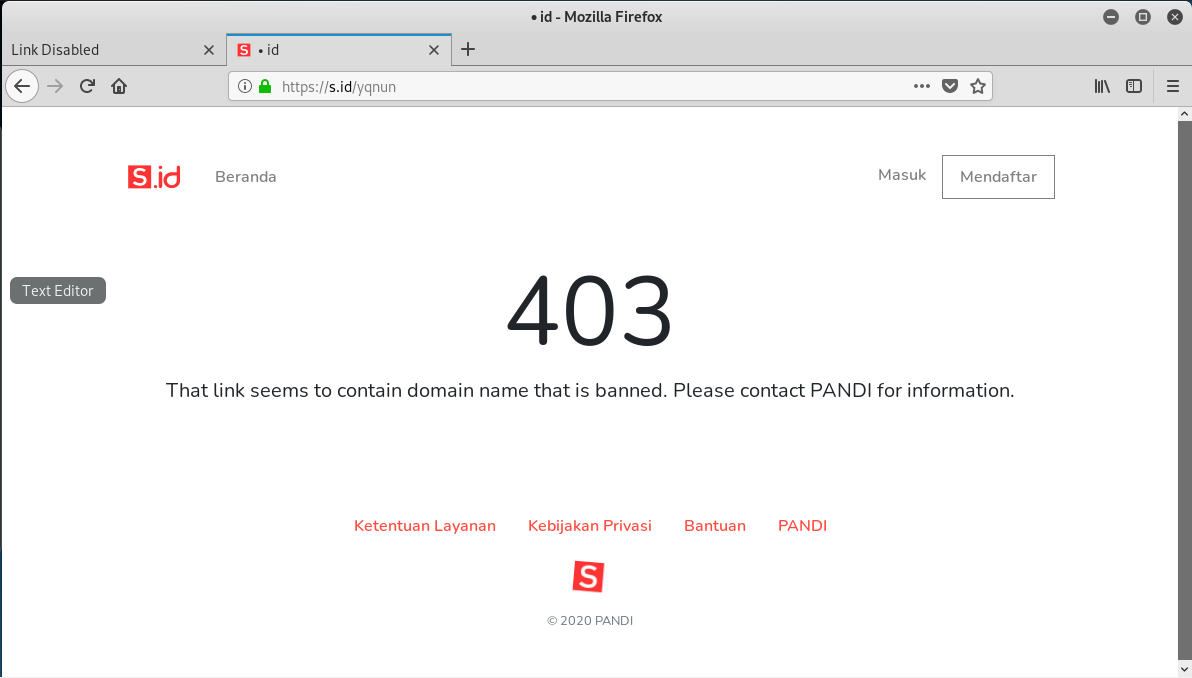
The link resolves to https://s.id/yqnun, but the page has been taken down. Virustotal had flagged is as a phishing URL.
Fake Invoice Phish
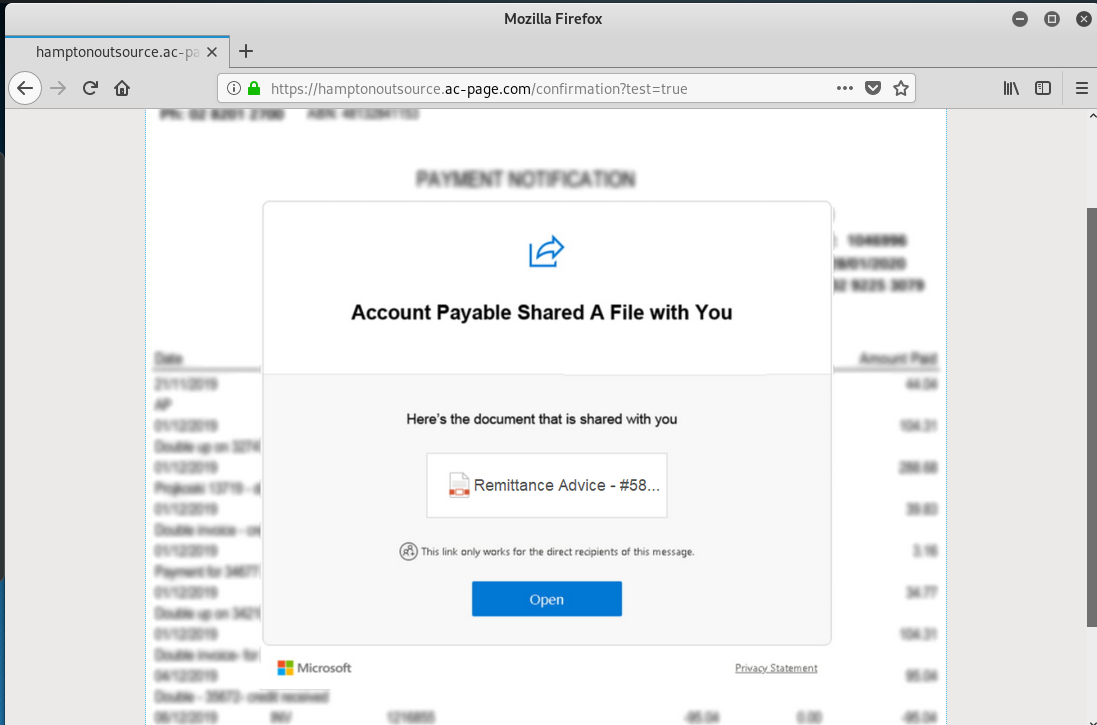
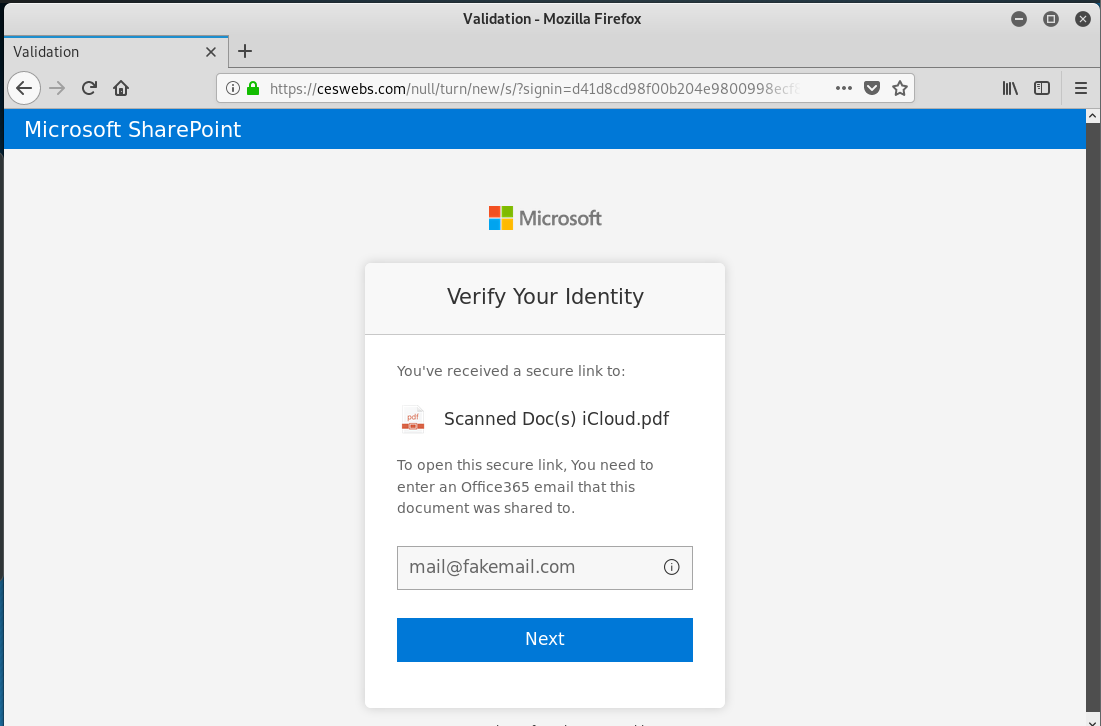
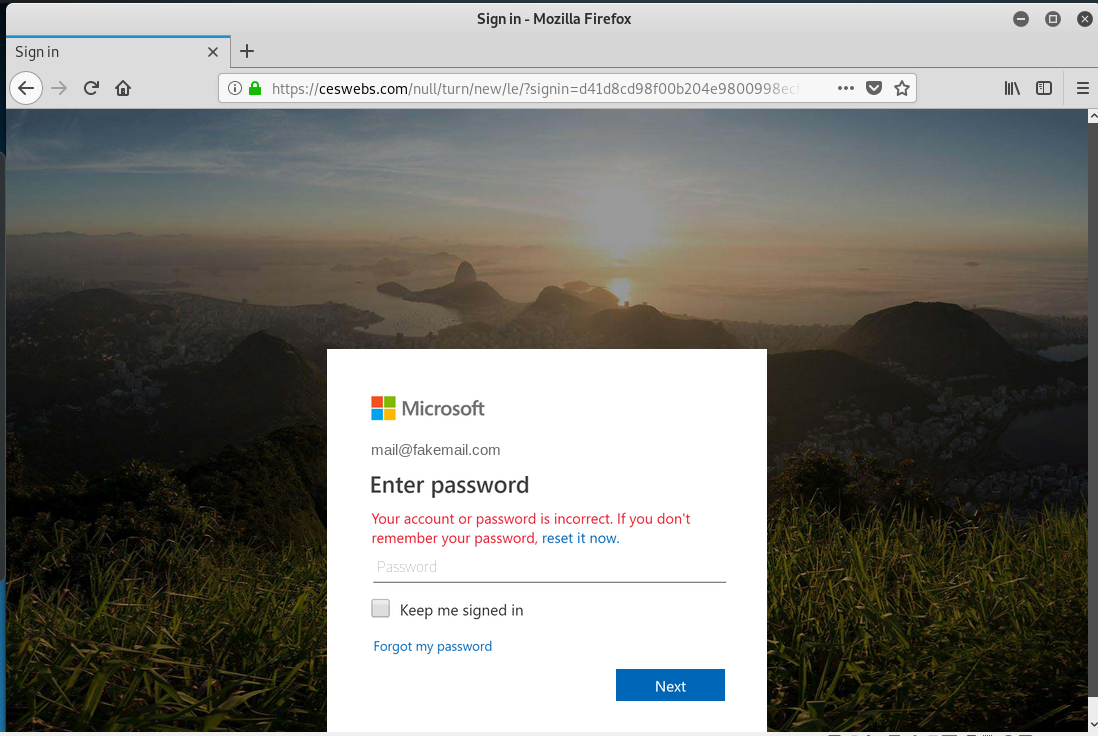
Initially, as I began this investigation, I thought this was going to deliver a malicious download with the PDF file, but it turned into an elaborate set of landing pages designed to ultimately capture your Microsoft Account credentials. Kudos on the realistic looking MS account login page.
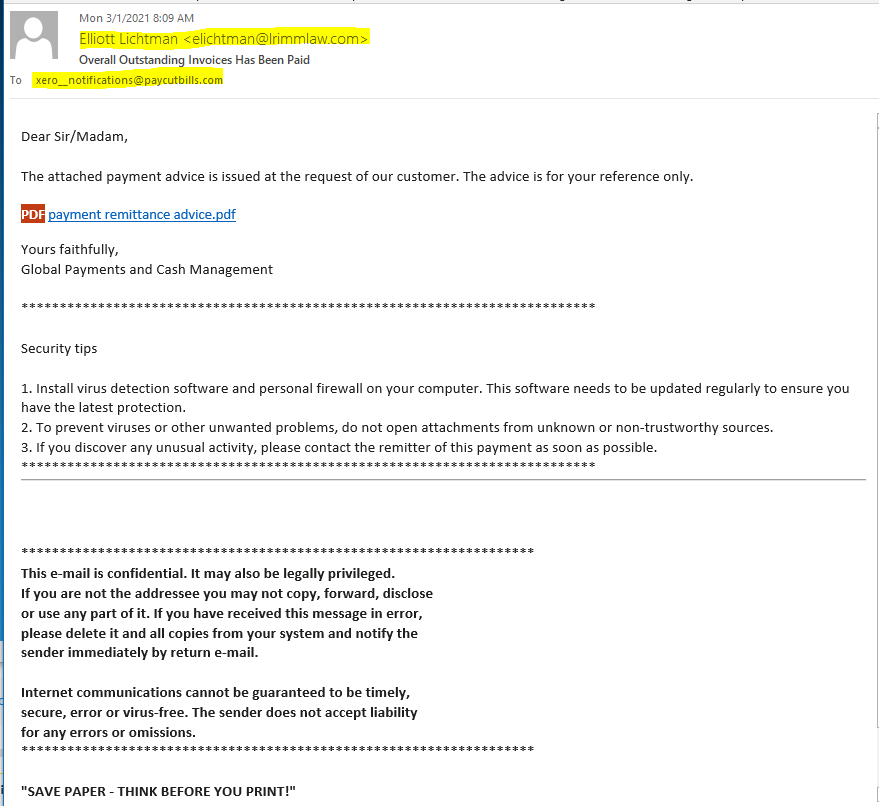
In reviewing the email headers, the sending account from Elliot Lichtman appears to be a legitimate email account on Microsoft365, and I can only assume this email account has been hijacked
The Payment Remittance Advice link resolved to https://hamptonoutsource.ac-page.com/confirmation?test=true. The Open button resolved to: https://ceswebs.com/null/turn/new. Clicking on the button started the process.
The email:
And here is the first landing page
And the second
The third
And the final page with an error message
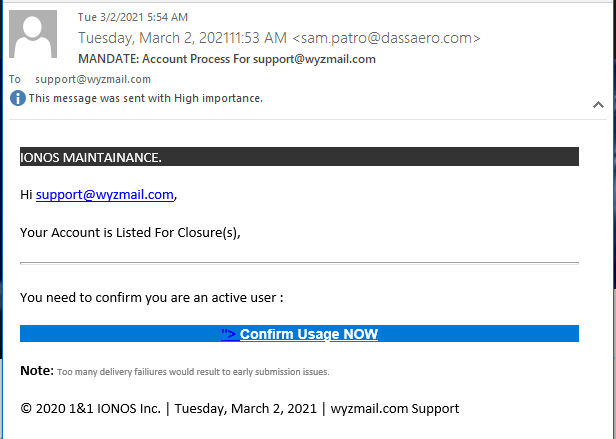
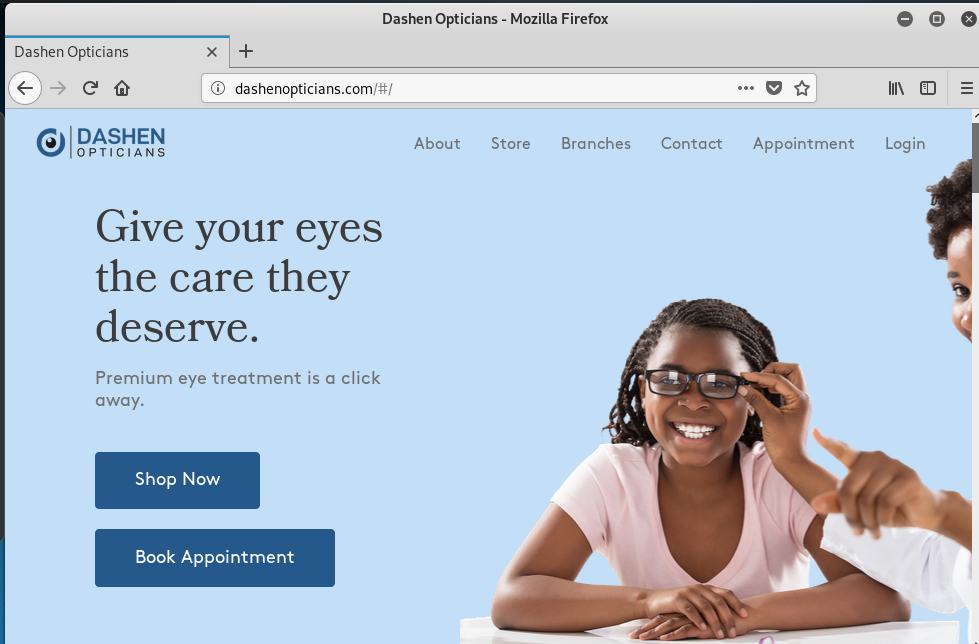
IONOS Maintenance Phish
Here is another credential stealer masquerading as an account maintenance email. The sender’s email address is an obvious clue. Confirm Usage Now link resolves to http://_55_.dashenopticians.com///#aHR0cHM6Ly9nYWdhbWlsYW5vLmNvbS5ici9pbWcvc291cmNlLz80MDg5MzY5OTg4NTI3MDA5JmVtYWlsPXN1cHBvcnRAd3l6bWFpbC5jb20= which was redirected to https://gagamilano.com.br/img/source/?4089369988527009&email=support@wyzmail.com. Virustotal identified the second link as a phishing link
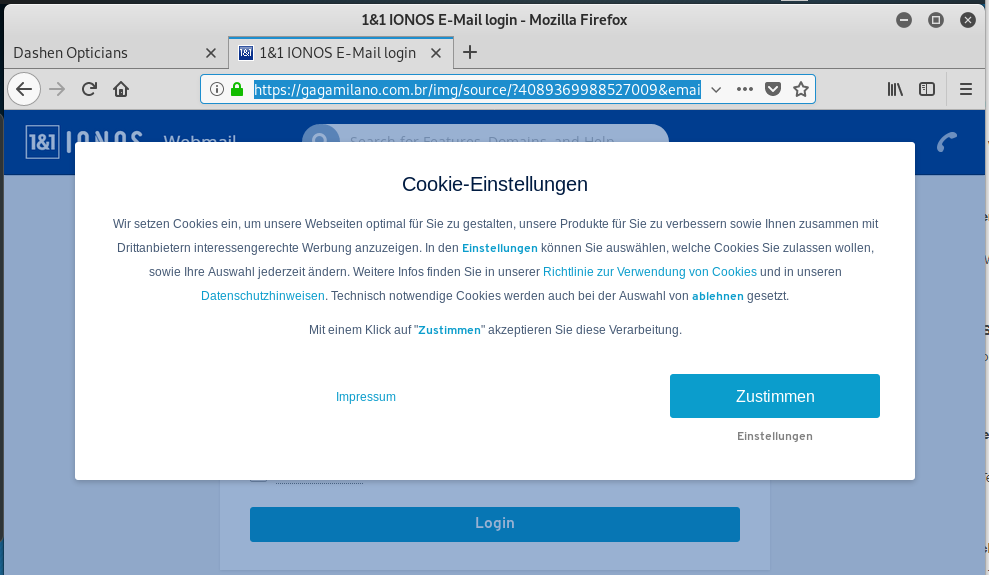
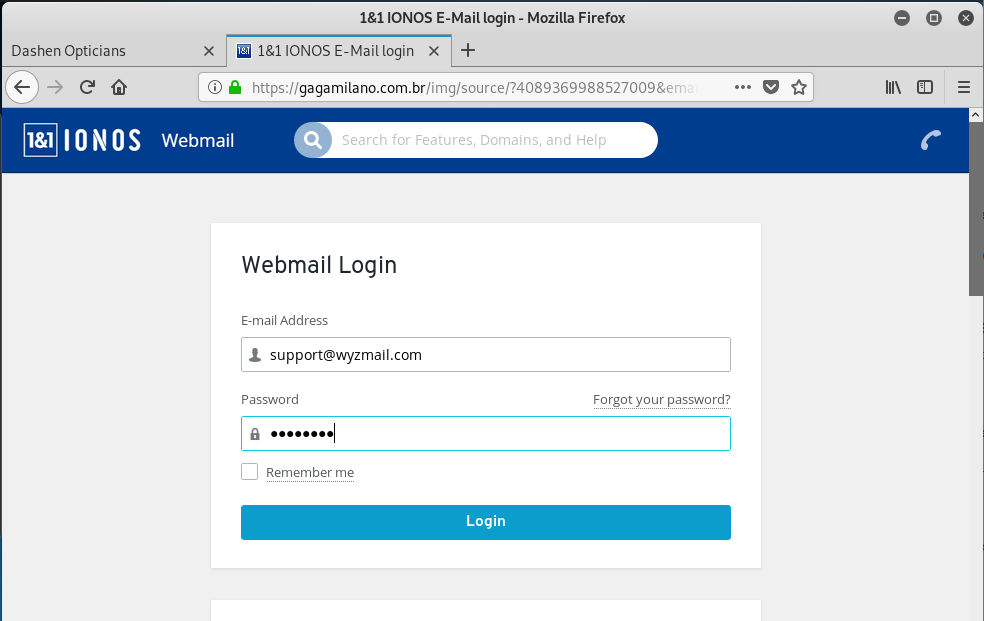
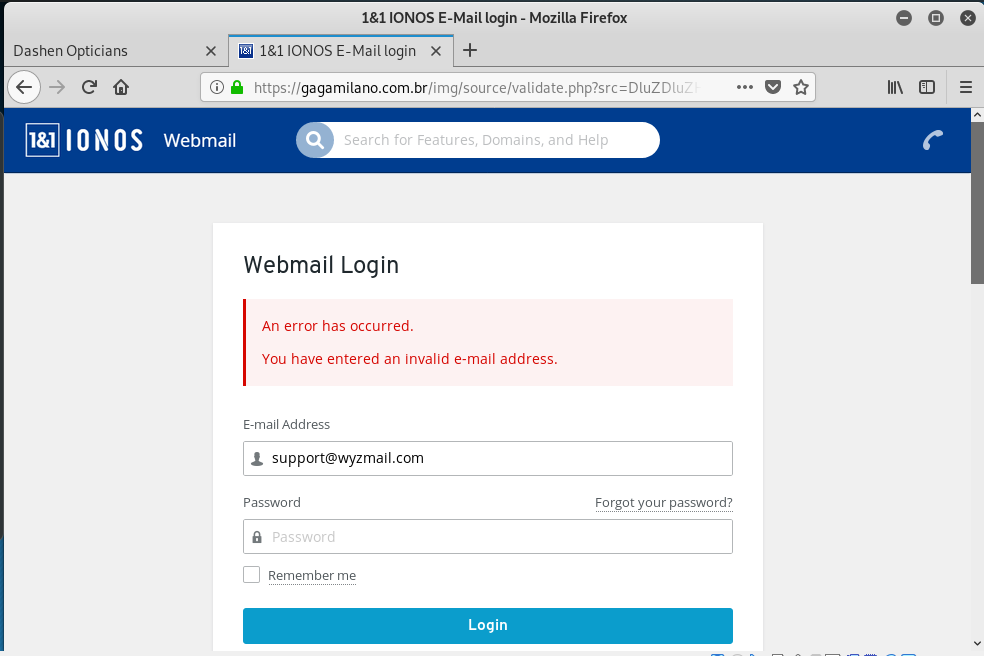
There are two hijacked websites being used in this exploit: The first for Dashen Opticians and the second for Gaga Milano, a Brazilian e-commerce site. See the email, landing pages, and hijacked sites below.
The first landing page displayed a cookie notice in German.
The second landing page steals the victims credentials
The third page displays an “error message.”
The first hijacked website provides a redirect to the second site:
And the second page, where the landing pages were located.
Nigerian Advance Fee Fraud
I haven’t seen one of these in a while, but found this one while going through my SPAM filter. I use a spam filtering service from SpamDrain. Here is a link to an FBI article on the Nigerian “419” scam. My letter follows:
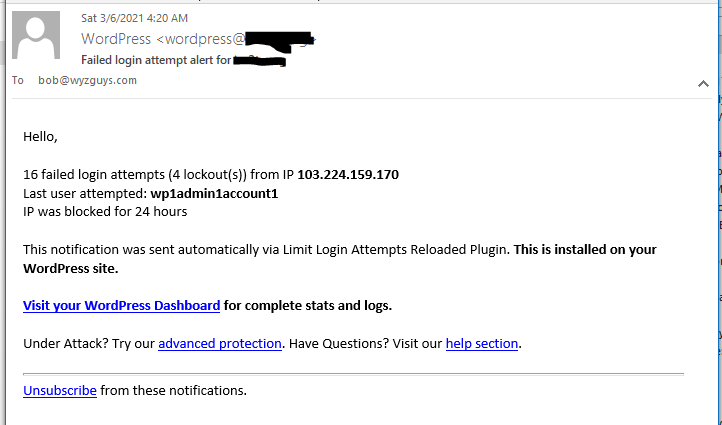
Wordfence Security Alert
Nearly all phishing exploits I have reviewed involved the use of hijacked websites used to host the phishing exploit landing pages. These hijacked sites are used to collected user credentials and other information from people who clicked on the embedded link in the phishing email.
Many of these hijacked sites WordPress sites, and none of them were using a WordPress security plug-in like Wordfence. I use Wordfence and highly recommend it. Here’s why:
Share
MAR







About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com