 Phishing Email Alerts
Phishing Email Alerts
Catch of the Day: Ionos Email Credentials Phish
Chef’s Special: Zoom Meeting Phishing Attacks
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Ionos Email Credentials Phish
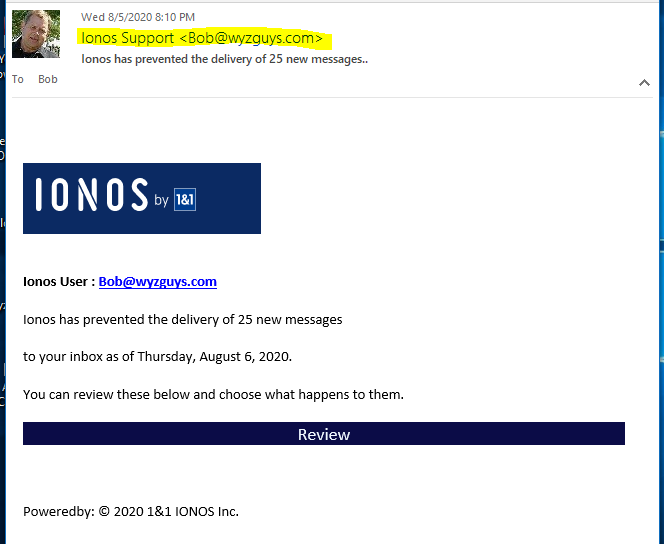
I continue to receive spearphishing emails from me (as the sender) and to me (as the recipient. A quick look at the email message headers shows the email came from a Telus SMTP server directly to the Perfora SMTP servers that my email host uses. Simple email address spoofing was used.
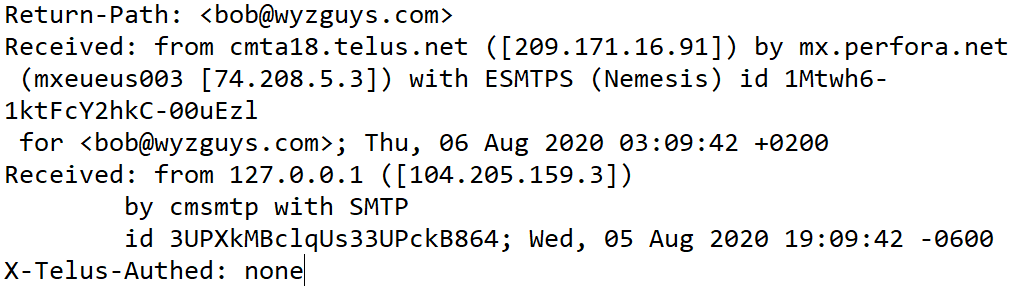
Here’s the beginning of the message header, with the IP addesses of the mail servers used in the exchange.
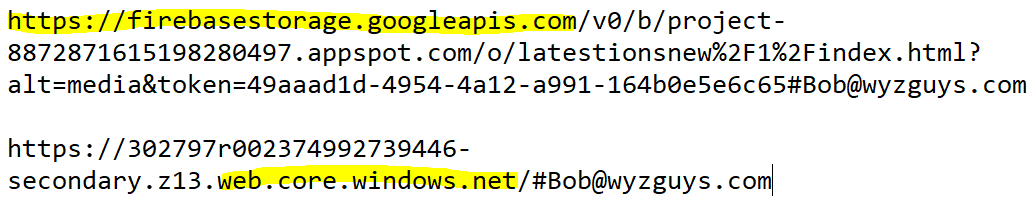
The Review link bounced me through a couple URLs, which are shown below. Both these URLs appear to be using legitimate, well recognized servers from googleapis.com and winodws.net.
According to ICANN whois, googleapis.com is registered to MarkMonitor Inc. So is windows.net. According to Wikipedia: “MarkMonitor Inc. is an American software company founded in 1999. It develops software intended to protect corporate brands from Internet counterfeiting, fraud, piracy, and cybersquatting. It also develops and publishes reports on the prevalence of brand abuse on the Internet.” So the attacker is using a trusted company and a pair of well-known brands to hide behind. Seems to me that Mark Monitor might be failing its mission in this case.
The google address is where the Review button resolved, and from there I was redirected to the windows URL.
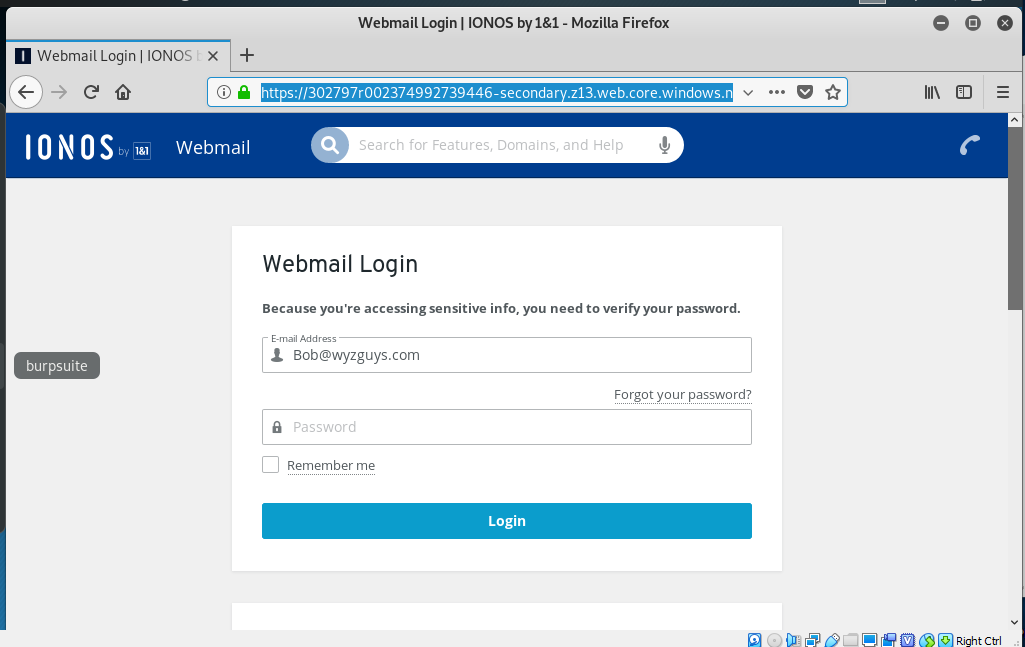
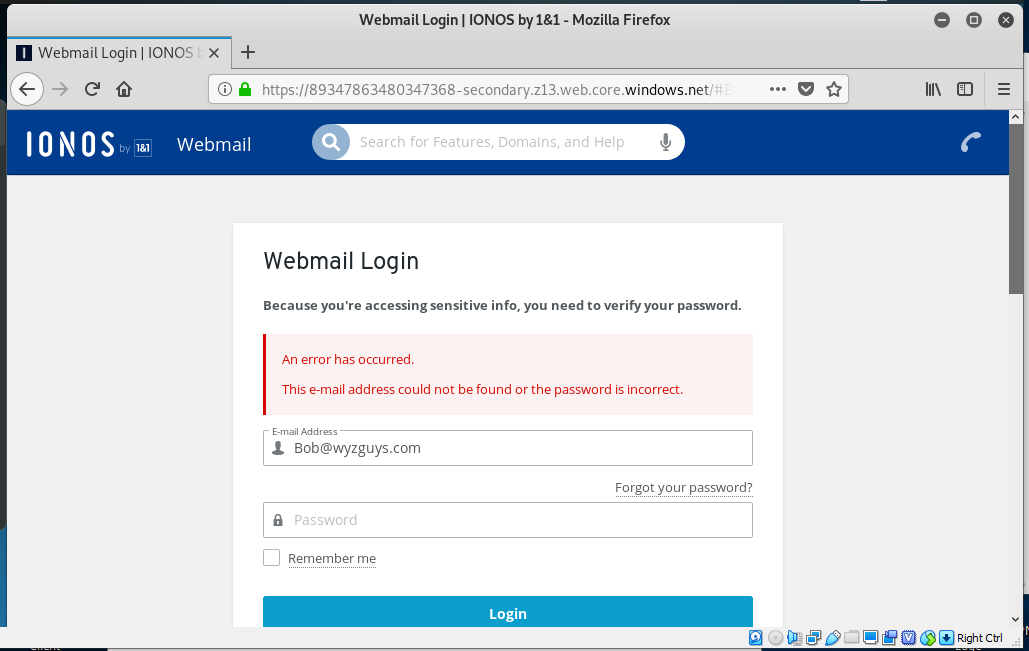
Here is the first landing page, which shows us a simple email account credential stealing web form. Entering the fake password spawned the error message.
I ran both URLs through VirusTotal, and Sophos identified the first as Suspicious and the second URL was identifies as Suspicious by Sophos and Malicious by Dr. Web.
Using cloud-based, short-term rental servers from well known hosts and cloud services companies is an additional way these attackers are making their exploits appear more legitimate. URLs like this not only are designed to trick humans, they are also designed to fool the AI in automated email and web filtering defenses.
These exploits have a short shelf life, sometimes only a day or two. I have reported this to MarkMonitor today (8-6-2020 as I write this). By the time this is published on 8-14, it will be unlikely the trail will still exist at all.
Balboa Capital Spam
It seems like the amount of phishing emails I receive has really dropped. Maybe “they” have figured out that I am “outing” them and their nefarious ploys. Or maybe its just vacation time.
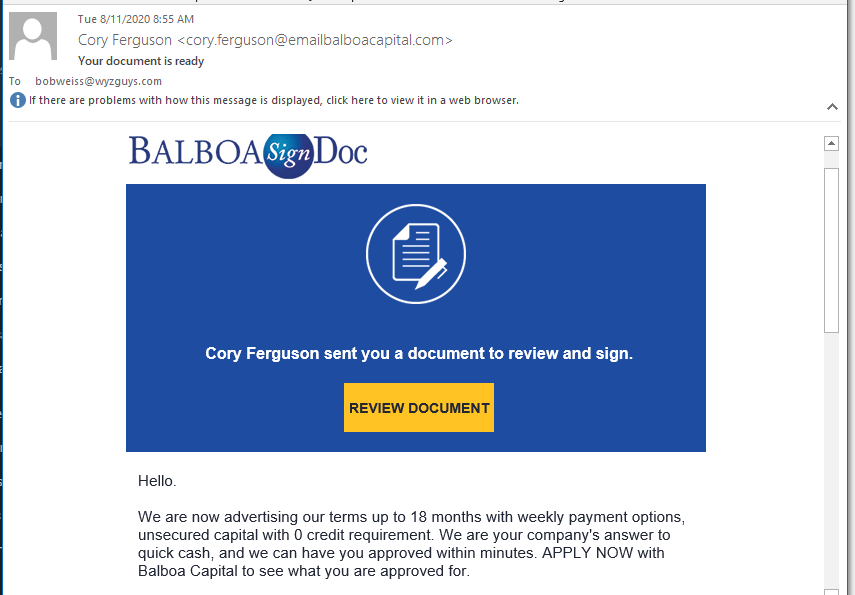
I am including this one because the email came as a document signing type email. These do look official, and if you weren’t paying attention, you might just click on the button. The button link goes to a solutions1.balboacapital.com web page.
This just appears to be a semi-legitimate way to acquire more debt, probably at fairly high interest rates.. Not malicious, just tedious.
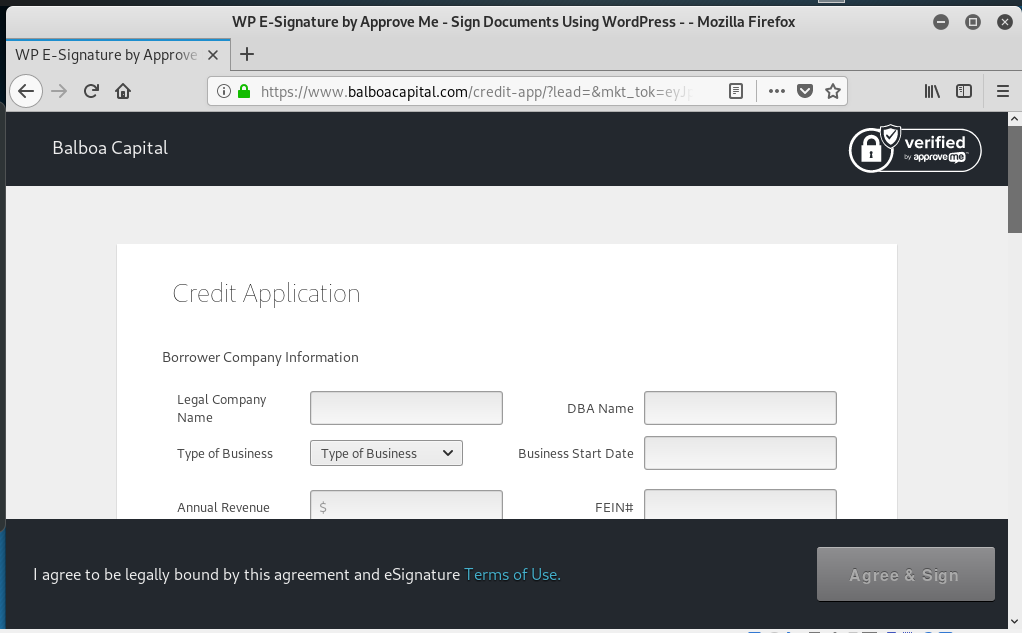
Here’s the web page. Not sure how comfortable I am sharing my credit history with these guys.
Explosion of Zoom Meeting Phishing Attacks Targeting O365 and Outlook
Researchers at INKY have observed an explosion of Zoom-themed phishing attacks over the Spring and Summer of 2020. Most of the attacks are aimed at stealing credentials to services like Outlook and Office 365 by directing users to spoofed login pages. Read more…
Google and Amazon most impersonated brands in phishing attacks
WhatsApp, Facebook, and Microsoft rounded out the top five as the most spoofed brands last quarter, says Check Point Research.
AA20-225A: Malicious Cyber Actor Spoofing COVID-19 Loan Relief Webpage via Phishing Emails
Original release date: August 12, 2020
Summary
The Cybersecurity and Infrastructure Security Agency (CISA) is currently tracking an unknown malicious cyber actor who is spoofing the Small Business Administration (SBA) COVID-19 loan relief webpage via phishing emails. These emails include a malicious link to the spoofed SBA website that the cyber actor is using for malicious re-directs and credential stealing. Read more…
Technical Details
CISA analysts observed an unknown malicious cyber actor sending a phishing email to various Federal Civilian Executive Branch and state, local, tribal, and territorial government recipients. The phishing email contains:
- A subject line, SBA Application – Review and Proceed
- A sender, marked as disastercustomerservice@sba[.]gov
- Text in the email body urging the recipient to click on a hyperlink to address:
hxxps://leanproconsulting[.]com.br/gov/covid19relief/sba.gov - The domain resolves to IP address:
162.214.104[.]246
Figure 1 is a screenshot of the webpage arrived at by clicking on the hyperlink.
AUG





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com