Phishing Email Alerts
Catch of the Day: Job Recruitment Scam Phish – a deep look into an Internet online job scam.
Chef’s Special: Fake Invoice Trio
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Job Recruitment Scam Phish
Wow! A cool work from home job that pays $28 per hour! Please – never believe these kind of offers. This is either an advance fee fraud (pay a fee as part of the hiring process) or they are setting up an elaborate beard to cover a money mule (money laundering) operation. Just keep reading.
I decided to give the Xooran.com web site a look – not even developed yet! Lazy scammers for sure.
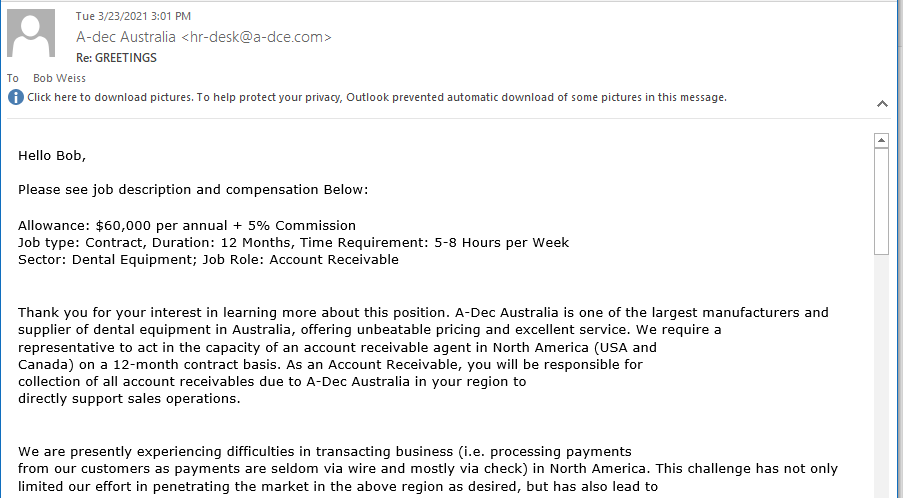
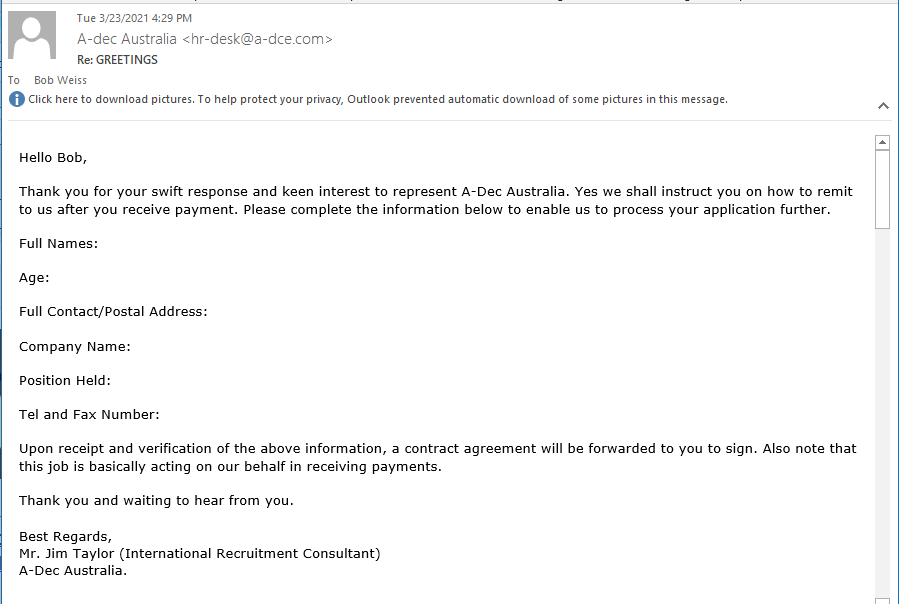
So I replied to the original email and got a speedy reply. This time the email domain was a-dce.com. This is a very near match to a legitimate domain of the actual dental supply company. Part of the email response and the actual A-dec website follow.
The email header showed the email was Received: from us2-ob4-6.mailhostbox.com ([208.91.199.215]) and a quick check in an IP locator website showed the email was send from Austin Texas (not Australia)
Not exactly trying to keep my identity or profession a secret.
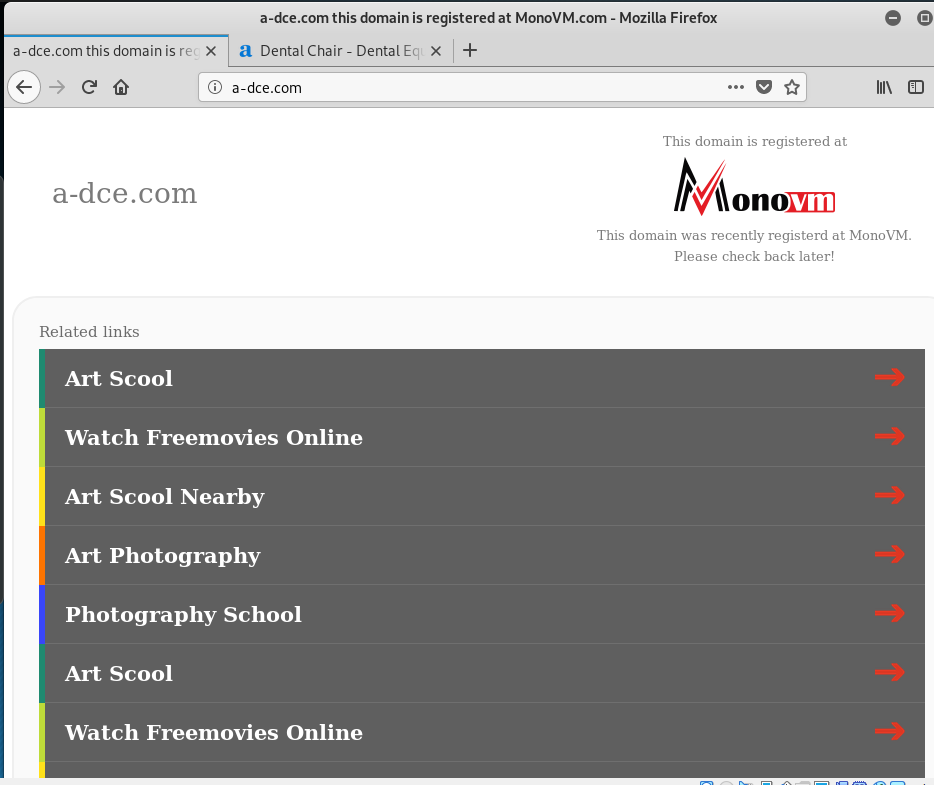
I checked out the website at the fake a-dce.com domain and found a holding page.
There is an actual dental supply company as named in the reply email. Just at a different domain name. This is a fairly sophisticated scam as they are using a real company that is Google searchable. It appears the job would be with a legitimate employer.
This email moves us to the next stage. Just a little PII (personally identifying information) and I will receive the “Contract.” Looks like I have a promising career in money laundering just a few emails away. I am not sure how much farther I want to proceed, but the information they are asking for is in my email signature already, so they have that information. “Just part of the process.”
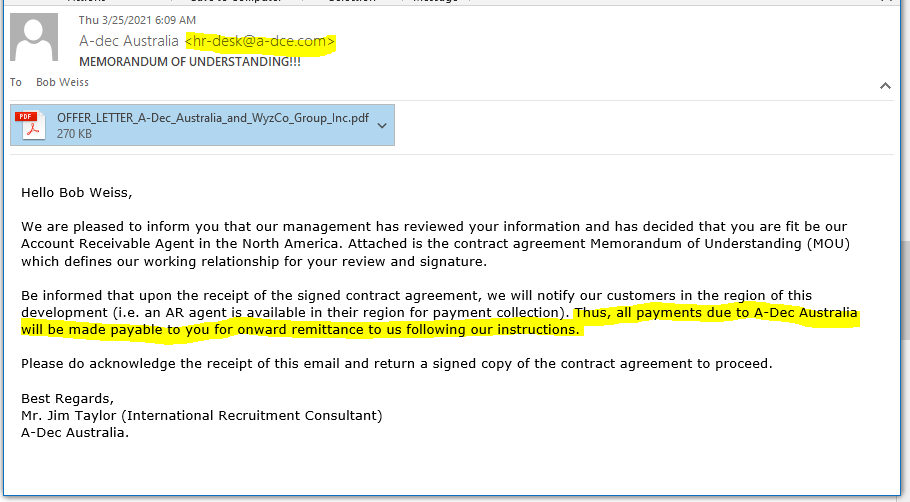
I wanted to see what was next, so I replied again, and received the following email and employment contract. This email exchange so far has been with Jim Taylor at a typo-squatting email address of A-dec Australia <hr-desk@a-dce.com>. The legitimate domain of the dental supply company is a-dec. Notice that the e and c have been inverted in the fake email address.
The highlighted statement in the email is concerning, as all invoice collections payments will be made to me directly, and presumably run through my business checking account. This is not normal. This is money laundering. The “payments” will not be from legitimate dentists, but will come from other illegal sources. At the very least, there are corporate tax consequences to deal with. If the plan goes sideways, the police would be arresting me, and “Jim Taylor” will be nowhere to be found.
The attached Offer Letter is the shortest employment contract I have ever seen. Normally, employment contracts are many pages of legal terms and conditions. I will have to terminate this investigation at this point. Last thing I want to do is contractually participate in a criminal activity.
Here is the WHOIS record for a-dce.com. The nameserver information is interesting. These may be nameservers run by a “bulletproof” criminal hosting operation. Or not. The hosting company MonoVM appears to be located in Russia. Very definitely interesting. The registration occurred in January 2021, which is too recent to be the domain of a long-standing dental supply company.
Many people have lost jobs during the Pandemic and are desperately looking for work. Criminal gangs like this one take advantage of that desperation. $60K a year and 5% commission sounds too good to be true. And it it. Do yourself a favor and stay away from scams like this one.
Fake Invoice Trio
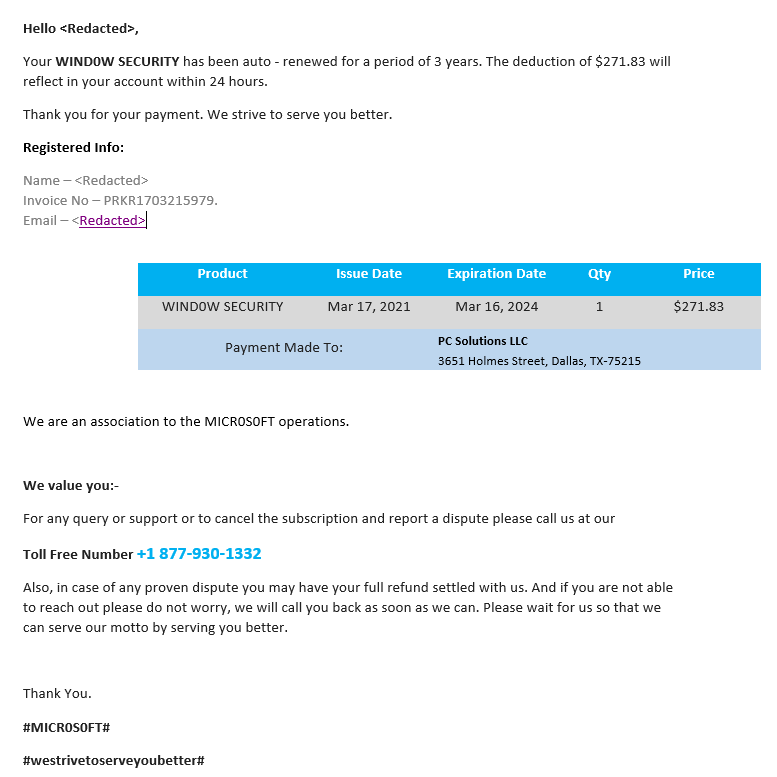
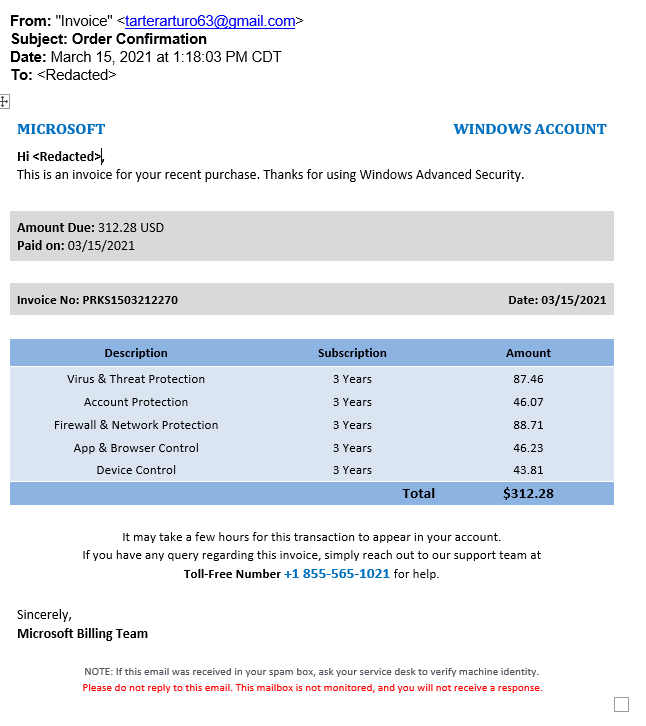
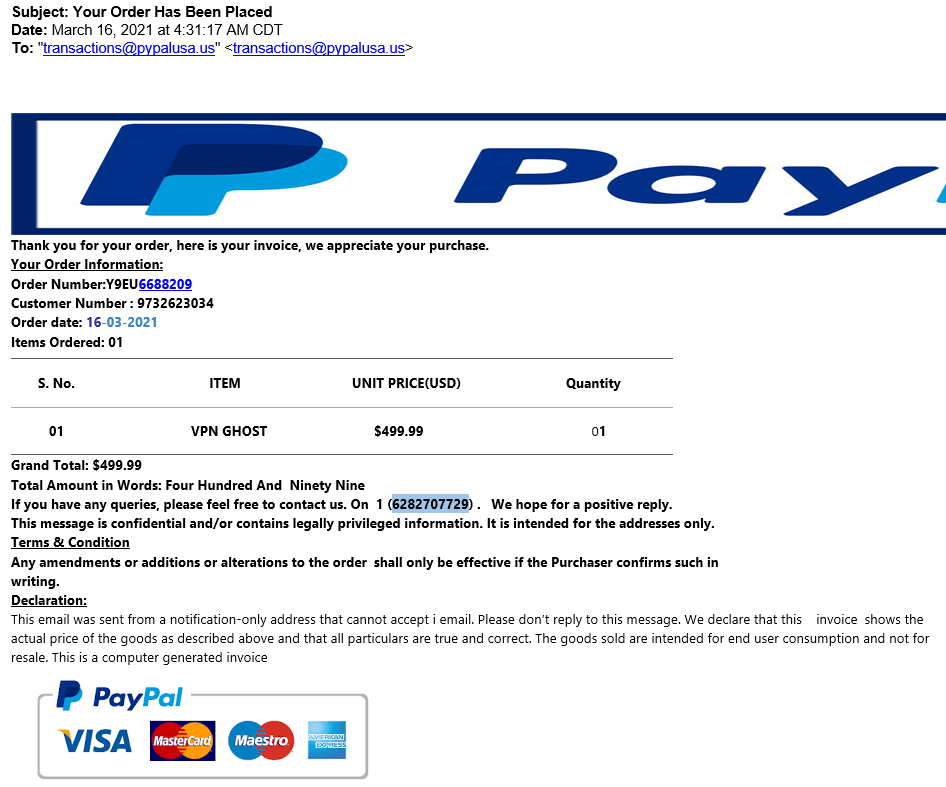
A client of mine sent these phish to me. They are designed to get the target to pick up the phone, call the number, and dispute the charges. A clever social engineer in a call center will be there to help separate the victims from their money.
When you get unsolicited invoices the best response is to check your credit card and bank accounts for unauthorized transaction, and if found, open your dispute with the credit card company or bank. NEVER call the provided toll-free number or click on any links.
Also – notice the use of the 0 (zero) in plave of the O in Micr0soft and 0ffice
Share
MAR








About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com