A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.
Made a Fortune in BitCoin? Be careful who you tell.
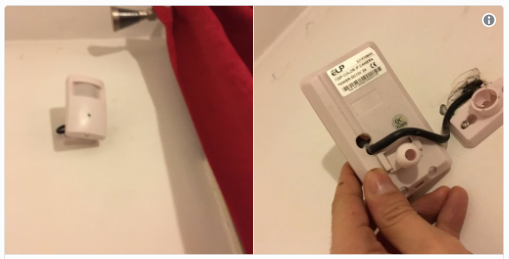
From Naked Security – Crypto Coins Robbed at Gunpoint.
Good old fashioned stick-ups still a possibility.
Watch out – fake support scams are alive and well this Christmas
Fake support scams – where the crooks help you “remove” malware you don’t have – are still a real ...
Continue Reading →DEC