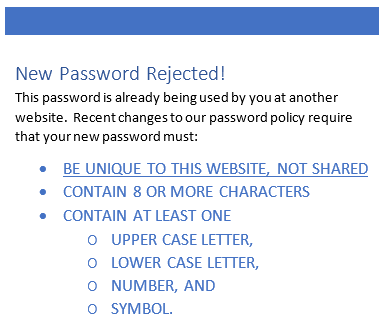
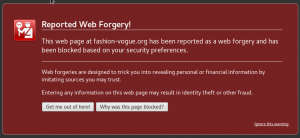
I have said it before, and I will repeat it now: passwords by themselves are no longer a useful form of security. The only option that makes passwords secure is two-factor authentication. Today we embark on a two week investigation into passwords, why they are so easy to break, how your password might be compromised, and how to create a password system that is less vulnerable to exploitation.
Why are passwords so easy to crack? Some of the answers we have ...
Continue Reading →JUN