 Here is a frightening twist on your typical domain name spoofing. Attackers have found ways to reuse legitimate sub-domains of well know business entities such as Microsoft and other companies to seed phishing email links with authentic sub-domains.
Here is a frightening twist on your typical domain name spoofing. Attackers have found ways to reuse legitimate sub-domains of well know business entities such as Microsoft and other companies to seed phishing email links with authentic sub-domains.
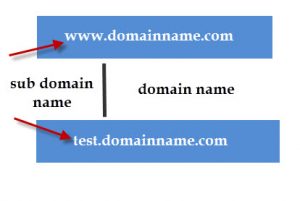
What is a sub-domain?
Anyone person or business that has a registered domain name can create any sub-domain they would like on the main domain that they hold. For example, I hold the domain name wyzguys.com. I can log into my hosting account and create sub-domain names that would look like sales.wyzguys.com, specialoffer.wyzguys.com, and so forth. When I create a sub-domain, it appears as a prefix followed by a period and then main domain name. It is possible to create a sub-domain on another sub-domain, such as computer.sales.wyzguys.com. Sub-domains can be created without additional cost to the domain holder.
Sub-domain creation has to go through the domain name registrar that is hosting their domain name, and this administrative account with the registrar is usually has a strong, well-protected password that often is couple with two-factor authentication. So sub-domain hijacking does not usually happen with hijacking a registrar admin account. It is easier than that.
Companies often create special use sub-domains for marketing campaigns, support queues, product pages, and so forth. A familiar example from Microsoft would be outlook.office365.com.
Sometimes these sub-domains are used for a limited time, and then abandoned. In a perfectly secure world, the person or organization responsible for creating the sub-domain would delete it. But this often doesn’t happen. Sub-domains used in marketing campaigns often point to another registered domain name, using a DNS record called a CNAME, that is also used temporarily. The special purpose domains are allowed to expire, usually.
If I am an attacker, I can search for active and abandoned sub-domains of a major company using DNS search techniques. Once I have a list, I can find abandoned sub-domains simply by trying the address in a web browser or using quicker search tools in Kali Linux. Unused sub-domains will return a 404 Not Found or similar error. If the error message is actually from an abandoned domain name redirect, I can register that domain name, and now I have a legitimate sub-domain on well known domain that I can use for phishing email links and other exploits. There is a great article on Sophos Naked Security that goes into detail on this exploit.
There are two take-aways from this article:
- Even if you are carefully checking links to be sure they are going to genuine domains, this exploit cuts right through your vigilance. The reality is that you may be getting phished even if the domain is legitimate. Now you need to rely on whether the email seems suspicious for other reasons, like the offer is too good to be true. Check these links out in VirusTotal, but understand that a clean report is not a guarantee of safety. But if the sub-domain is flagged for any reason, avoid it or use with extreme caution.
- If your business has one or more registered domain names, and you have active or old marketing campaigns that relied on sub-domains for destination landing pages, make sure you cancel the sub-domain when you are done with your campaign. Audit the sub-domains you have created on your registrar account, and delete any you no longer use.
And use extra care when clicking on links that contain sub-domains. They bring a new level of reality to phishing and website scams.
More Information:
-
Researcher finds 670 Microsoft subdomains vulnerable to takeover
- Why the Bruhaha over the Corp.com Domain?
The Corp.com domain is for sale, and depending on who ends up owning it, this could be catastrophic for companies that use Windows domains and Active Directory. It basically is Microsoft’s fault (of course), except it is not. The problem is that many admins who were setting up Active Direc…
ShareMAR




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com