 Phishing Email Alerts
Phishing Email Alerts
Catch of the Day: Contact Form Survey Scam Phish
Chef’s Special: Consent Phishing
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox.
I’ve been reporting about phishing, and performing my weekly autopsies for sixteen weeks. Not sure if this is significant, but the volume of phishing emails hitting my inbox has dropped. Makes me wonder if the other side has decided to stop sending me new ammunition.
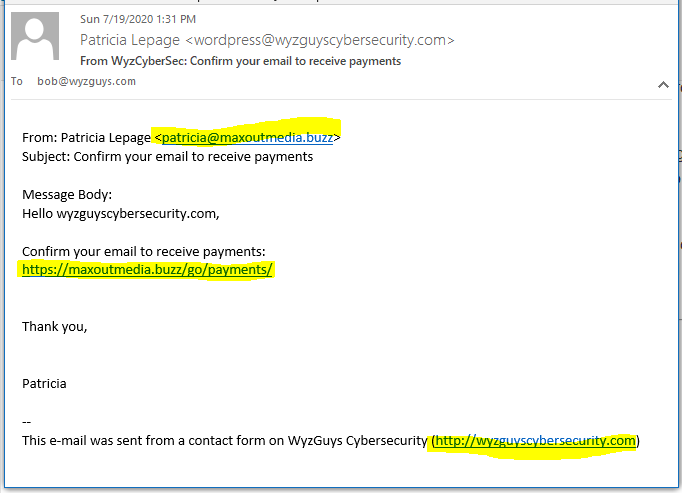
Contact Form Survey Scam Phish
I got another piece of contact form spam from my own website again. For the record, I could eliminate this spam completely by adding a CAPTCHA to the web form, (and so could you),but then I would cut my phishing harvest in half. Contact form spam is very popular with crooks and scammers because your own website sends the contact form contents on your own email address, which is highly trusted by your email application.
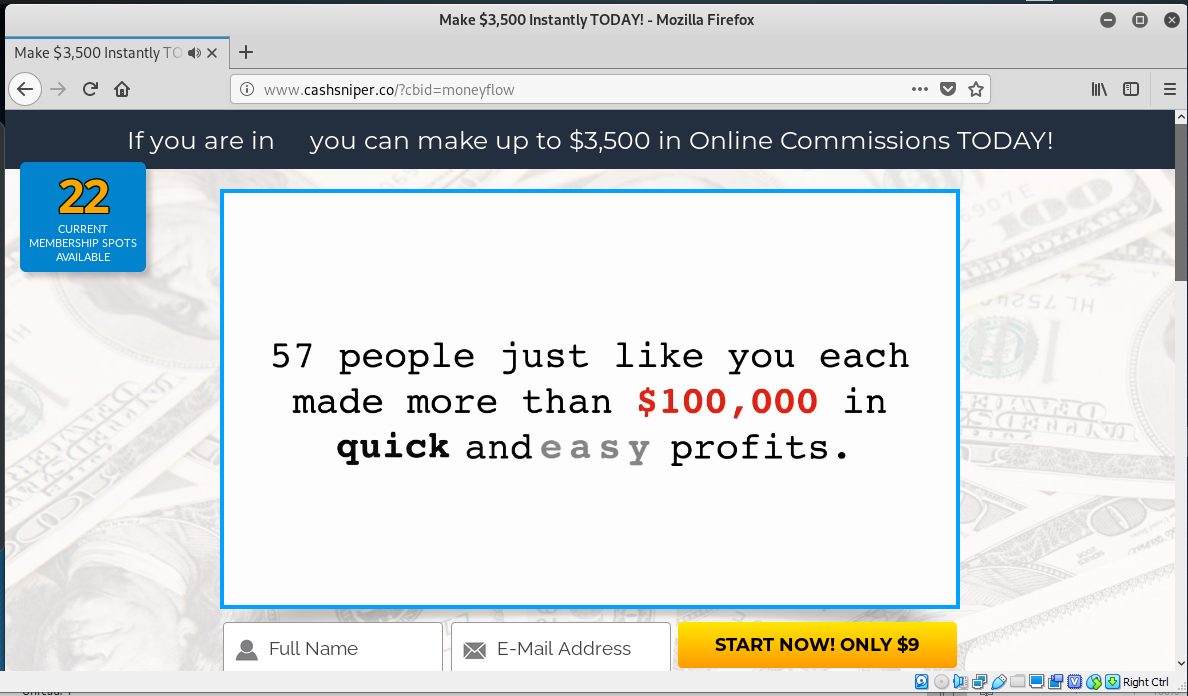
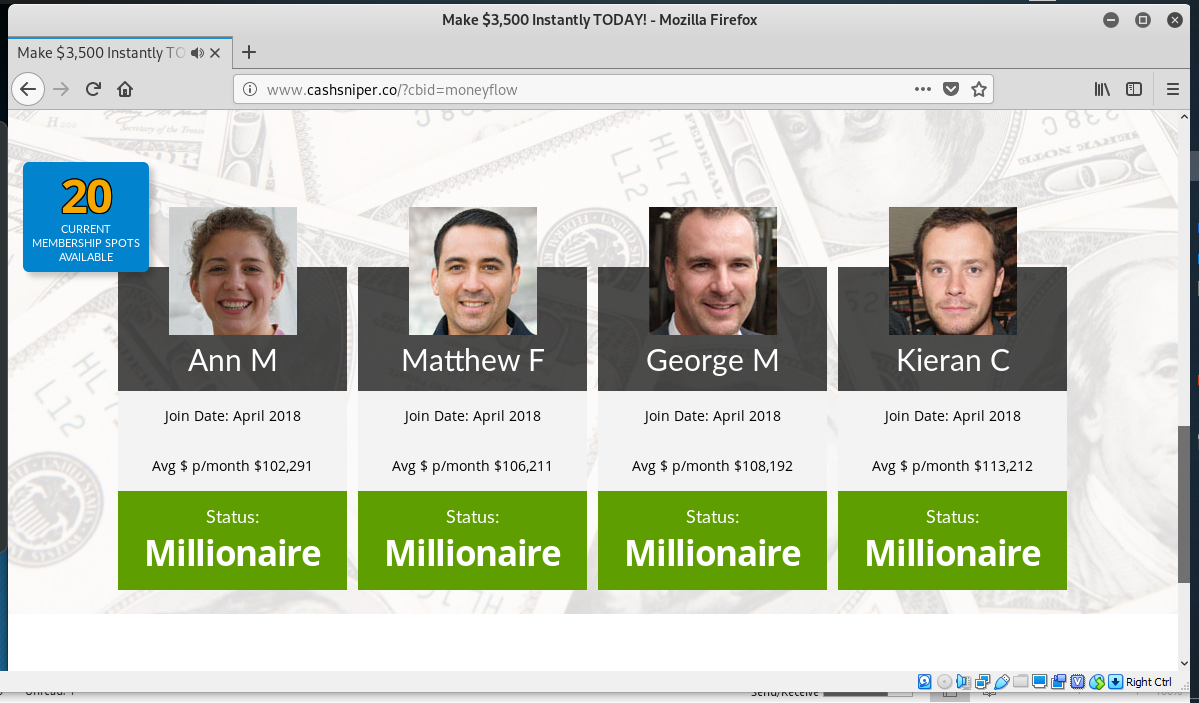
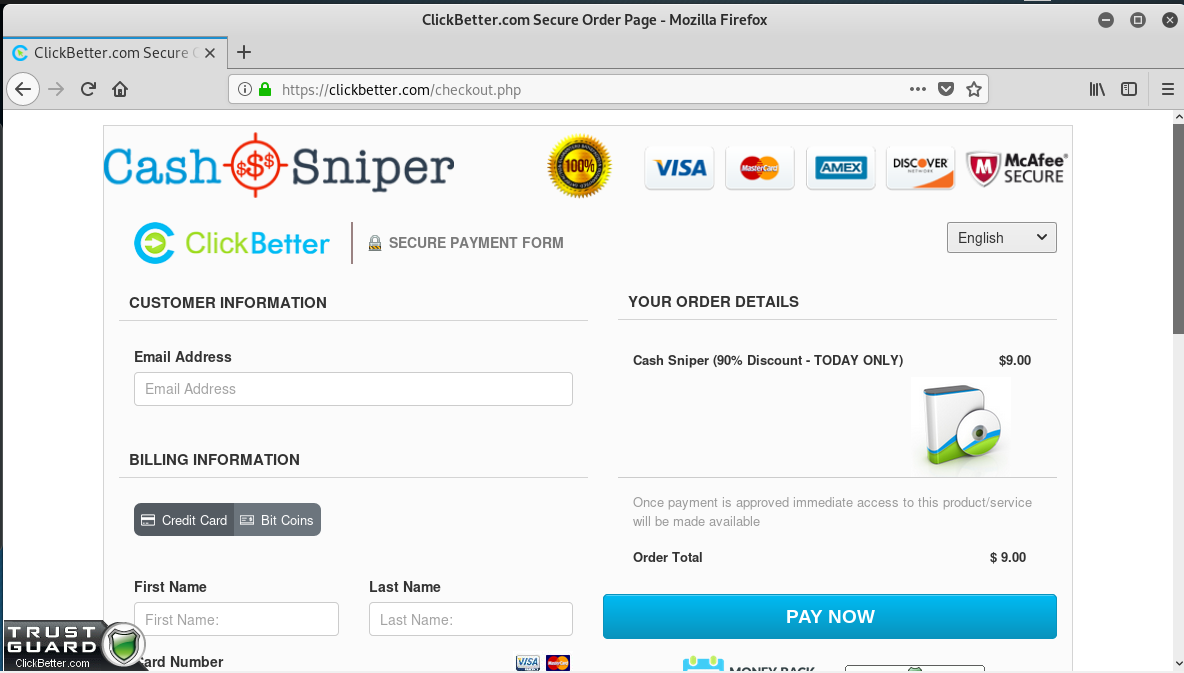
Back to the mission at hand. The email asks me to Confirm your email to receive payments. Hey – who doesn’t like to receive payments! Clicking on the link redirected me to a different URL that I was unable to capture, before landing on top3paidsurveys.com/1000s/.
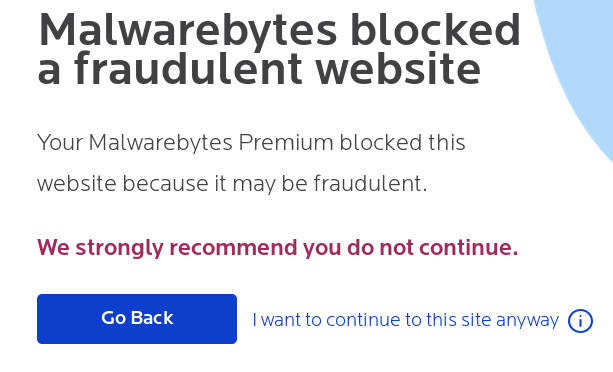
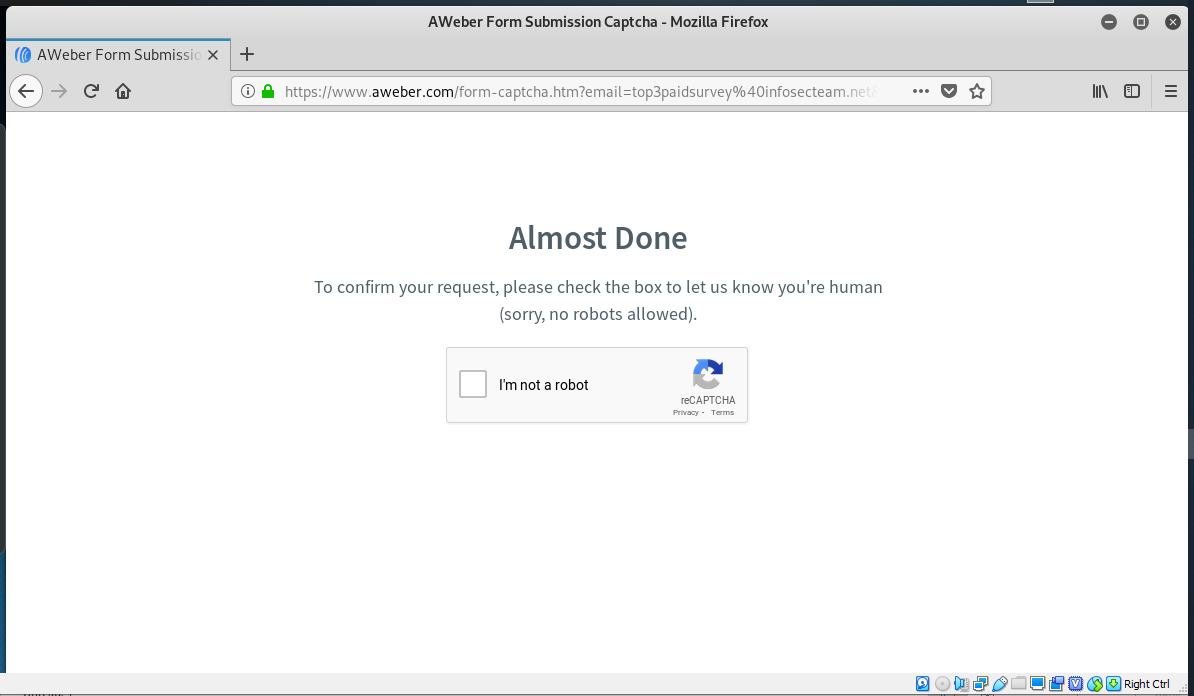
I quickly created a throw-away testing email account for to enter in the email field, but Malwarebytes had other plans, and would not let me move through this scam. I turned off Malwarebytes and clicked through, dealt with a tiresome CAPTCHA page and finally got the the pay dirt. I could become an Internet Millionaire sending out bogus surveys.
Stay Safe Online. Just Say NO to Scams.
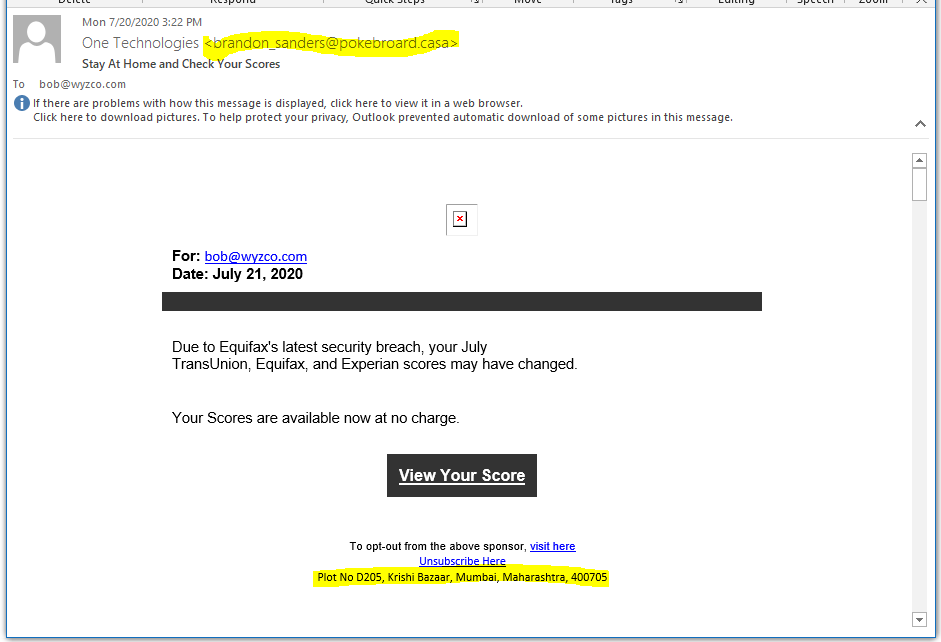
Free Credit Score Phish
Must be scam week. Here’s an interesting phish that turned out to be an affiliate marketing exploit for NationalCreditReport.com. Affiliate marketing is another “riches of the Internet” that promises big money returns to the affiliates for helping to market “legitimate” businesses. Unfortunately many of these businesses are super scammy.
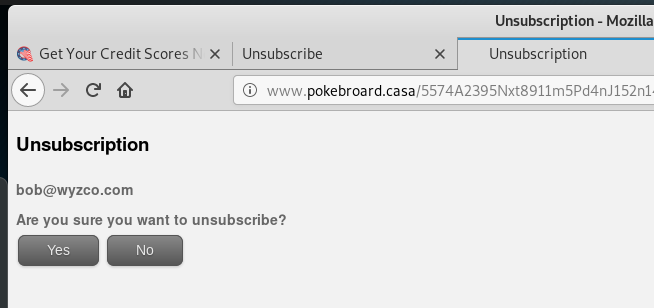
FIrst, Brandon Sanders email domain is the same domain pokebroard.casa that the View Score, Opt-Out, and Unsubscribe links use, which is uncommon. But of course these links all redirected elsewhere. I’ll get to that in a minute.
At the bottom of the email there is an address in Mumbai, India. Plot No D205, Krishi Bazaar, Mumbai, Maharashtra, 400705. I ran it through Google Maps and got this information. Evidently the Pokebroard Company is located in a vegetable stand in a street bazaar.
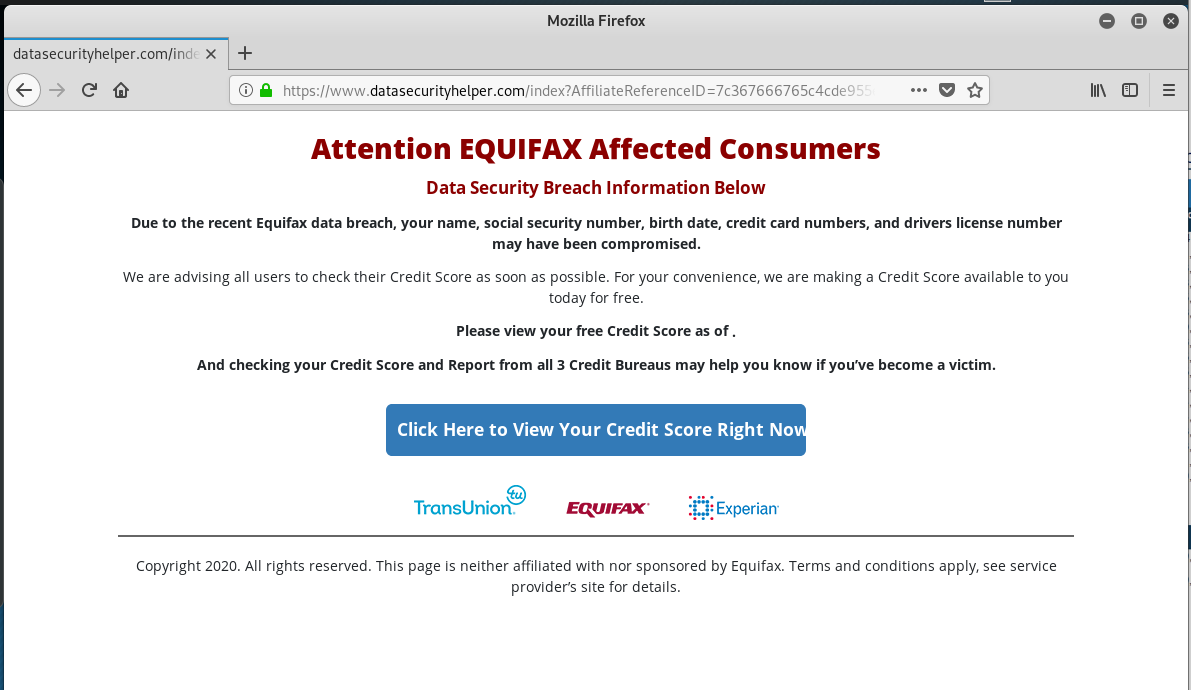
Back to the link redirects. The View Your Score link went to a long URL that I have truncated for simplicity http://www.pokebroard.casa/summoners-juxtapose/8dc6bO23… This was redirected to a URL where the sender “Brandon” affiliate link was counted as an advertising return (me!). https://www.datasecurityhelper.com/index?AffiliateReferenceID=7c367666765c4cde955ef52fecd79de6&affiliate_id=142. This was the landing page. So I clicked to view my credit score right now.
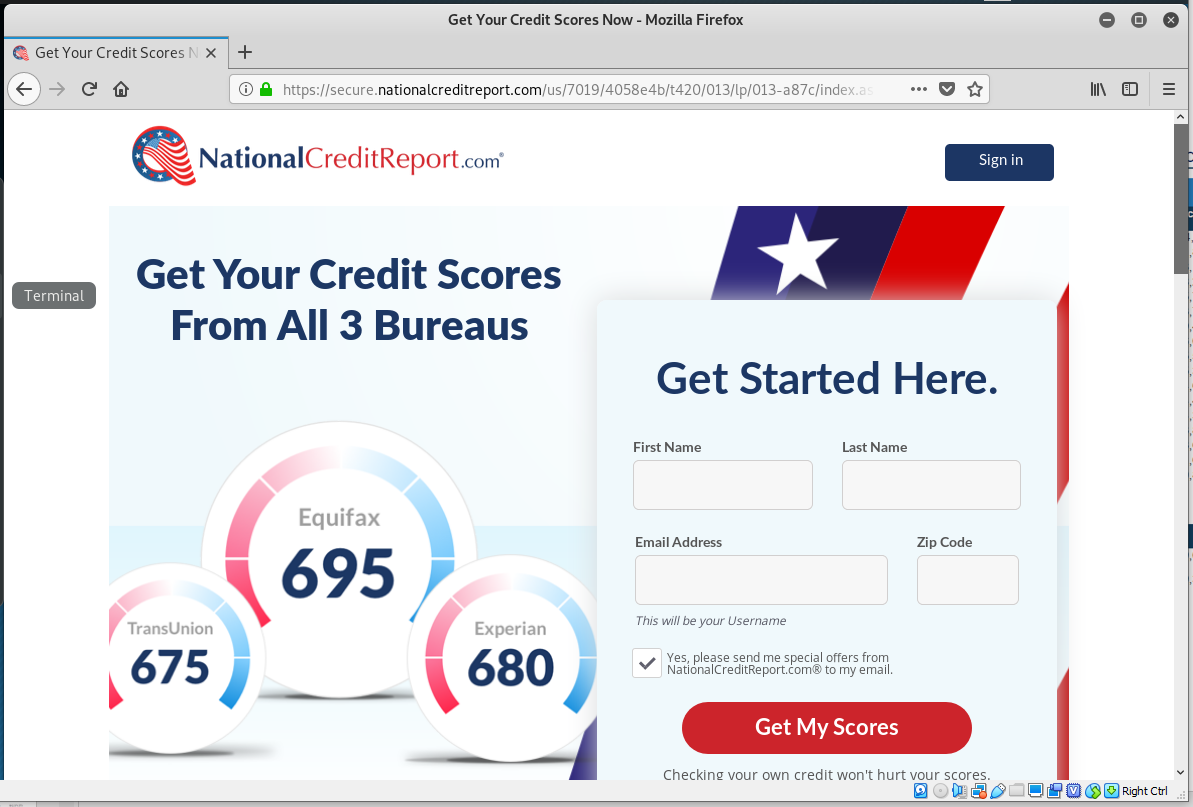
This link took me to another URL, which again I have shortened. https://secure.nationalcreditreport.com/us/7019/4058e4b/t420/013/lp/013-a87c/index.aspx?sid=AFFCPA008125Z&id=3998&ord=1&append=1&edata=471211&edata2=142%2c142&edata3=418996&edata4=07_45076247_53a6562b-b53d-4d56-a3a3- This is the website for NationalCreditReport.com.
I entered some fictitious data into the form to see where I would go. This next page looks like a PII data harvesting operation.
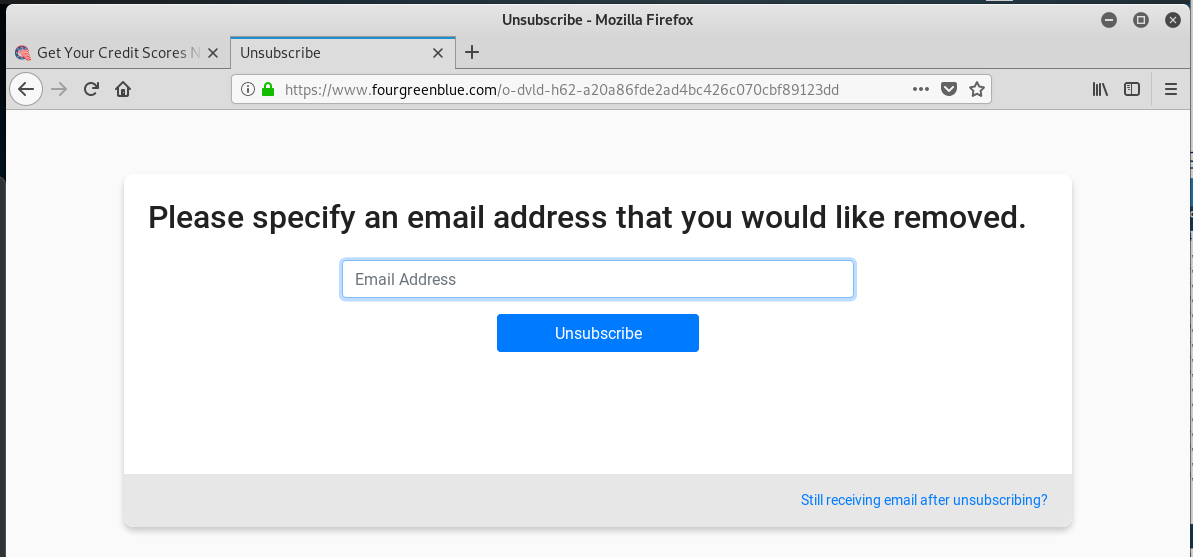
The Opt-out link http://www.pokebroard.casa/advocated-sensitivity/6484U2395iLo8611c5do3Co152J14jFsFf68.GsEGsi9BdcooKobe7Sq10nGi6K2i0lb and the Unsubscribe link http://www.pokebroard.casa/5574A2395Nxt8911m5Pd4nJ152n14OFsFf68.GsEGsi9cdcooKobe6Wyp1w06V@13ib/summoners-juxtapose went to two different pages that wanted my email address.
I am sure at some point I would have been asked to pay a fee and actually see a credit score, and for some sort of credit report monitoring or protection services. You can get a lot of this information and services directly from the credit bureaus. at least these are companies that do not have offices in a vegetable market in India.
The very next day, the spam begins, unfortunately NOT on my throwaway address, but on the good address they used on the first email.
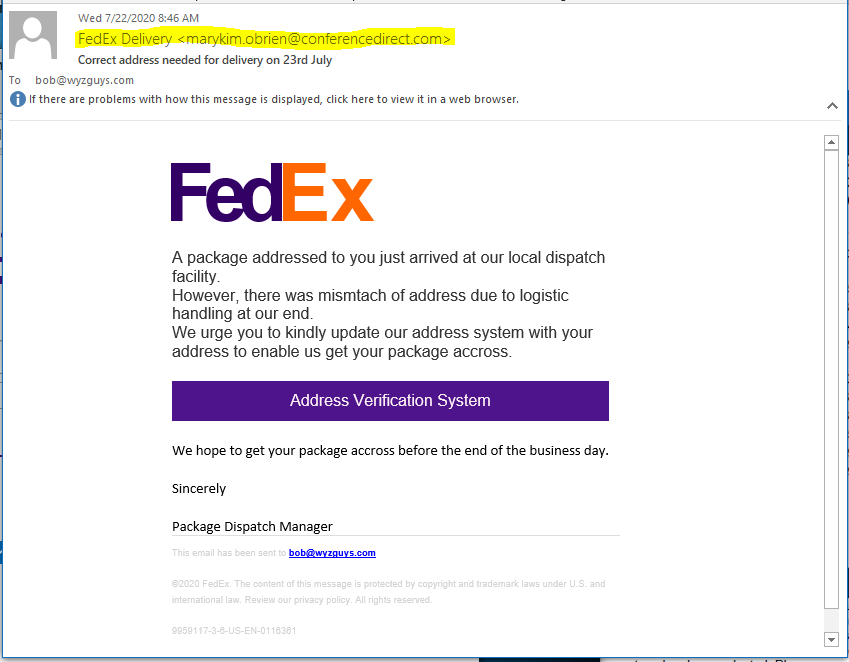
Fedex Delivery Problem Phish
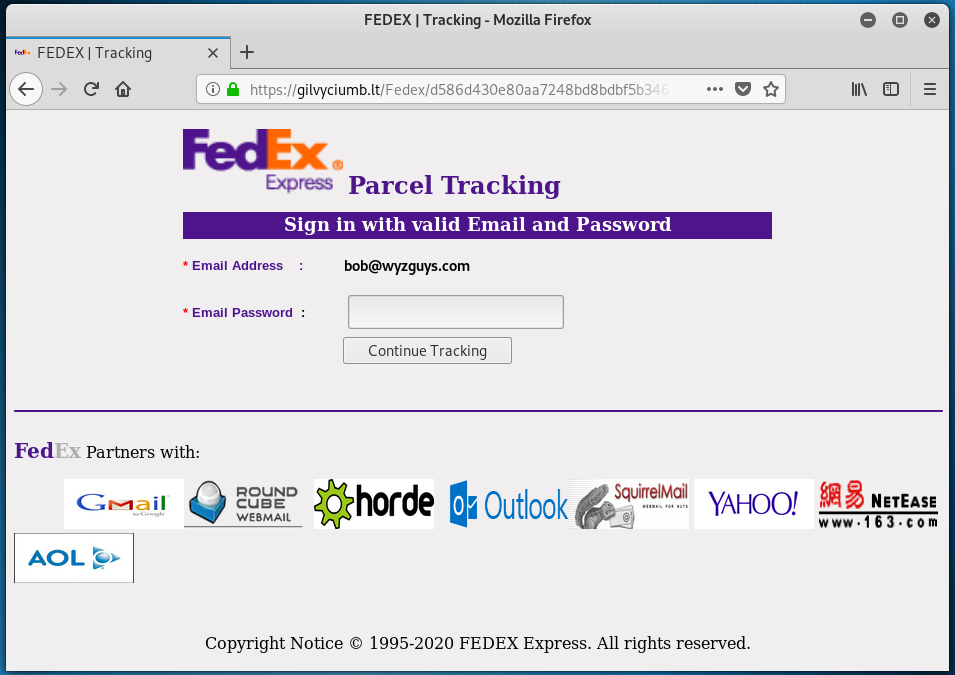
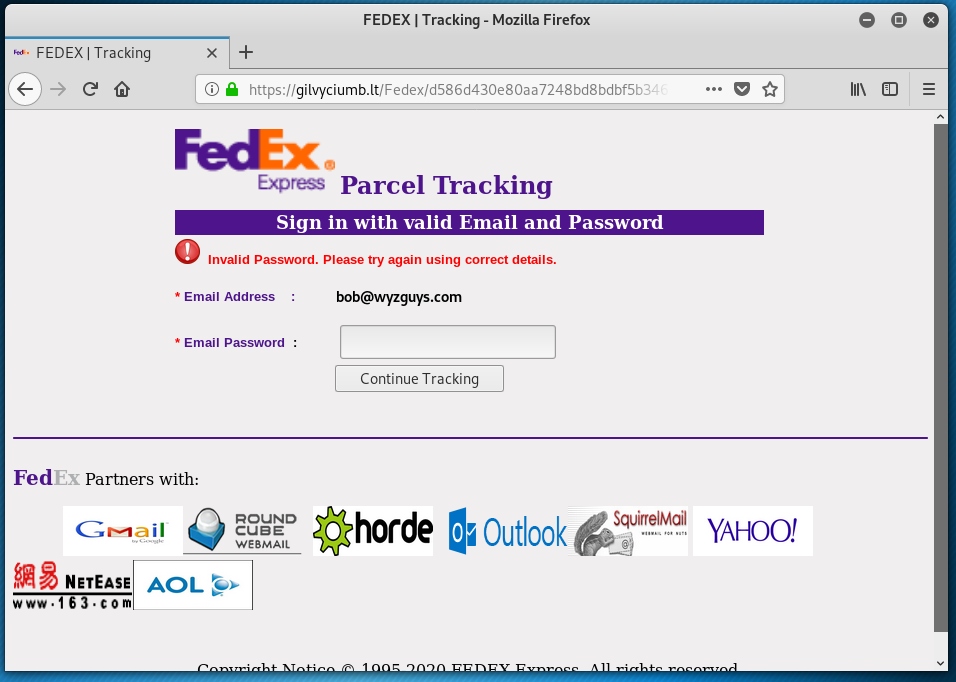
This is a lot of work for the cyber criminals to go through just to get your FedEx login credentials. The Phishing email button took a trip across three hijacked websites.
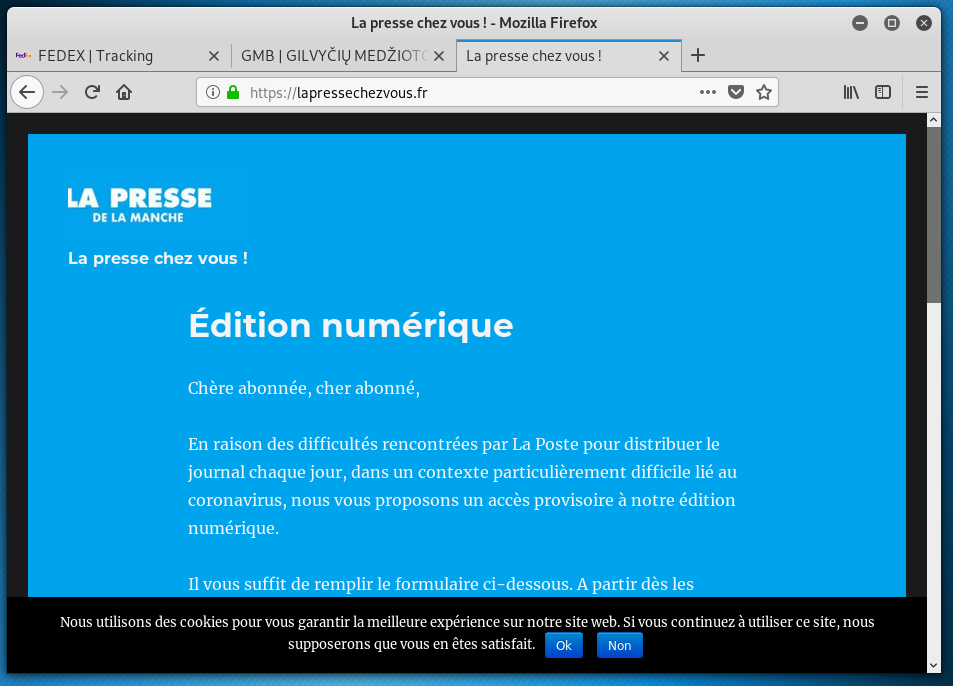
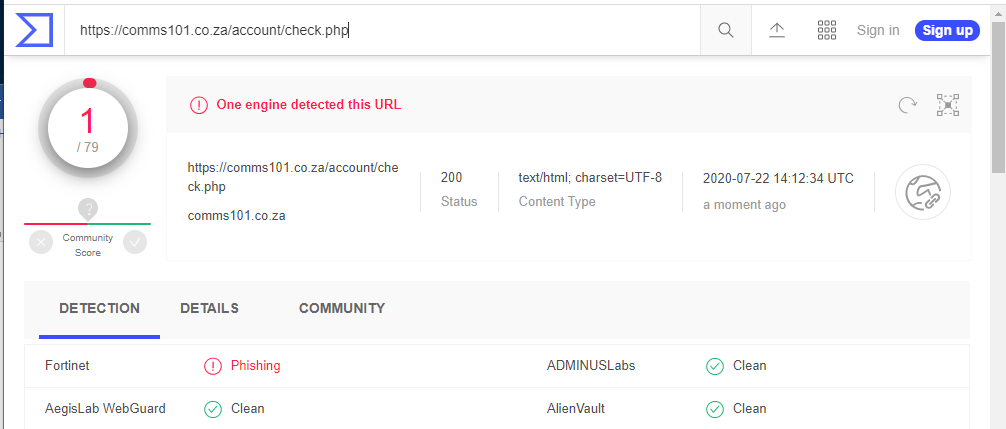
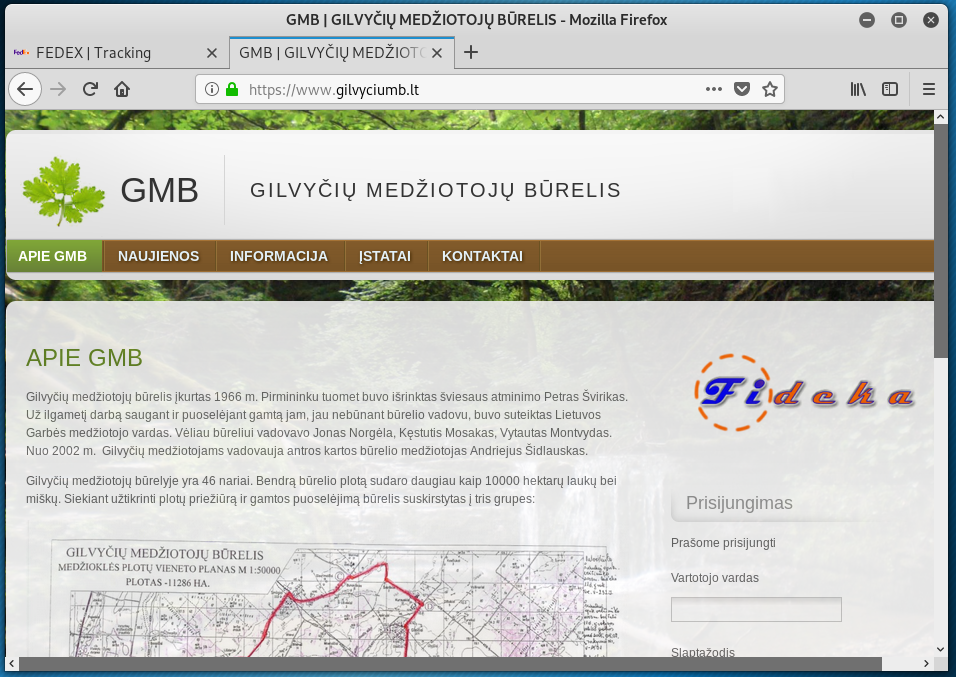
The first issue is of course the sender’s email address, which is NOT on a FedEx email domain. The Address Verification System button goes first to a hijacked French website, which is redirected to a South African website, and finally finds a landing page on a Lithuanian website. Only the second hop comms101.co.za tested positive for phishing on VirusTotal, the other two showed up clean. Here is the path.
https://lapressechezvous.fr/#Ym9iQHd5emd1eXMuY29t
redirect to https://comms101.co.za/account/check.php
redirect to https://gilvyciumb.lt/Fedex/bc82f92370e635760f07226d203c8784/tracking.php?websrc=59c275dc2e97dd3b896ed4ff2b82a8fd&dispatched=44&id=7554010382&email=bob@wyzguys.com#….(truncated)
Here are the home pages of the three hijacked websites used in this exploit. Again, it took a lot of work to set this up just to get a FedEx password.
Consent phishing: An application-based threat to keep an eye on
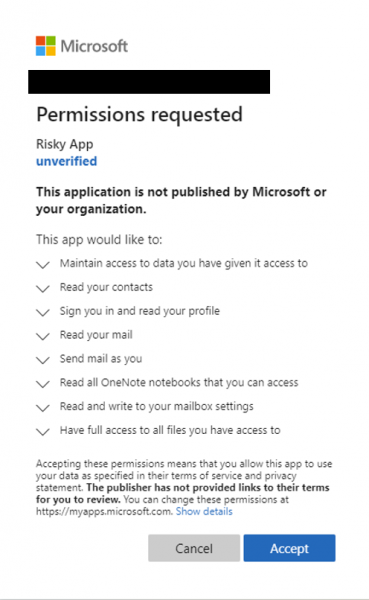 Today developers are building apps by integrating user and organizational data from cloud platforms to enhance and personalize their experiences. These cloud platforms are rich in data but in turn have attracted malicious actors seeking to gain unwarranted access to this data. One such attack is consent phishing, where attackers trick users into granting a malicious app access to sensitive data or other resources. Instead of trying to steal the user’s password, an attacker is seeking permission for an attacker-controlled app to access valuable data.
Today developers are building apps by integrating user and organizational data from cloud platforms to enhance and personalize their experiences. These cloud platforms are rich in data but in turn have attracted malicious actors seeking to gain unwarranted access to this data. One such attack is consent phishing, where attackers trick users into granting a malicious app access to sensitive data or other resources. Instead of trying to steal the user’s password, an attacker is seeking permission for an attacker-controlled app to access valuable data.
While each attack tends to vary, the core steps usually look something like this:
- An attacker registers an app with an OAuth 2.0 provider, such as Azure Active Directory.
- The app is configured in a way that makes it seem trustworthy, like using the name of a popular product used in the same ecosystem.
- The attacker gets a link in front of users, which may be done through conventional email-based phishing, by compromising a non-malicious website, or other techniques.
- The user clicks the link and is shown an authentic consent prompt asking them to grant the malicious app permissions to data.
- If a user clicks accept, they will grant the app permissions to access sensitive data.
- The app gets an authorization code which it redeems for an access token, and potentially a refresh token.
- The access token is used to make API calls on behalf of the user.
If the user accepts, the attacker can gain access to their mail, forwarding rules, files, contacts, notes, profile and other sensitive data and resources. Read full article on Microsoft.com
Phishing Leads to Ransomware in 30% of Attacks
TechRepublic
Organizations and their employees can fall victim to a variety of cyber-attack methods, including phishing campaigns, viruses, spyware, and Trojans. But one particularly problematic and pervasive type of attack is ransomware. A report released recently by security provider Positive Technologies discusses the trends of ransomware attacks during the first quarter of 2020.
Share
JUL










About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com