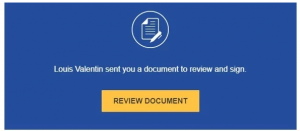
 You or your CFO receive an email offering business capital at attractive interest rates. The company that sent you the offer has provided an application for the loan using the legitimate document presentation platform, DocuSign. Everything looks legit, and it is. No fake web pages or near-miss web addresses. But this is the latest in “no malware” phishing scams.
You or your CFO receive an email offering business capital at attractive interest rates. The company that sent you the offer has provided an application for the loan using the legitimate document presentation platform, DocuSign. Everything looks legit, and it is. No fake web pages or near-miss web addresses. But this is the latest in “no malware” phishing scams.
Filling out the form will give ...
Continue Reading →FEB