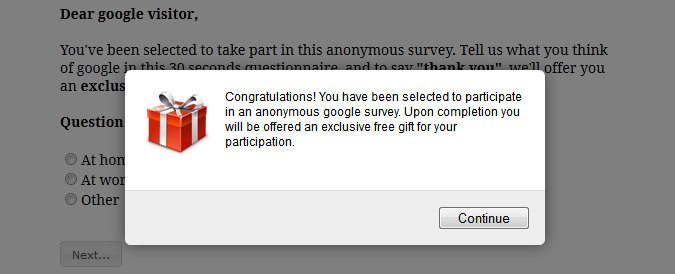
You know those surveys, games, and “like and copy” messages that your Facebook “friends” share with you? Would you be surprised to learn that many of these “fun with friends” activities are just cover for a new form of phishing exploit? In the last few years phishing attacks have evolved from a primarily email-based attack into attacks using other vectors including surveys, games, gifts and prizes, and social networks.
JAN