 Another out of cycle post, this one directed to anyone who is running balloting operations for the upcoming elections. I make jokes all the time about our next president being elected by the Russian Cyber Army, the Chinese Peoples Liberation Army Unit 61398, the ISIS Cyber Caliphate, or the Syrian Electronic Army. But this is a potential reality, and US-CERT has released a publication advising local election officials and those that support the information technology systems and networks that support it.
Another out of cycle post, this one directed to anyone who is running balloting operations for the upcoming elections. I make jokes all the time about our next president being elected by the Russian Cyber Army, the Chinese Peoples Liberation Army Unit 61398, the ISIS Cyber Caliphate, or the Syrian Electronic Army. But this is a potential reality, and US-CERT has released a publication advising local election officials and those that support the information technology systems and networks that support it.
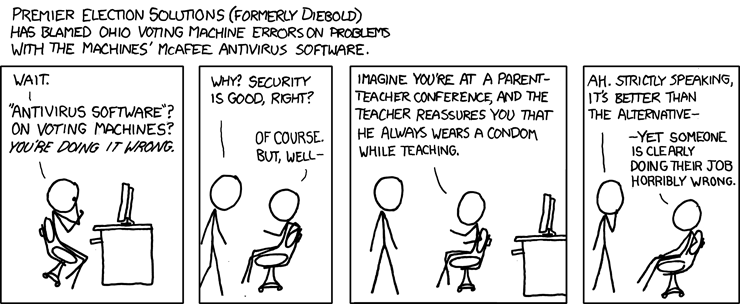
It turns out, not surprisingly, that electronic voting systems, and voter registration databases, are subject to the same sorts of attacks that have been plaguing other businesses. The warn to be on guard for phishing emails, ransomware, server vulnerabilities to exploits such as SQL injection, cross-site scripting.
Solutions include having good working (tested) backups, application white-listing, patching and updating, controlling administrative privileges, and setting up firewalls to block traffic coming from or going to overseas IP addresses. They also advise inviting a penetration tester in to try and uncover exploitable vulnerabilities that may exist.
If you are working with systems that will be used in the coming election, please take a moment to read their article.
SEP




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com