 Most of the small business clients I work with do not have a huge budget for a cybersecurity program, and something like a managed security service program (MSSP) is beyond their reach. They have money for a firewall, and endpoint security, but that is about it. Sound like your business? Then read on.
Most of the small business clients I work with do not have a huge budget for a cybersecurity program, and something like a managed security service program (MSSP) is beyond their reach. They have money for a firewall, and endpoint security, but that is about it. Sound like your business? Then read on.
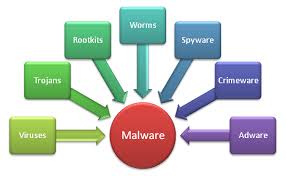
There are eight simple, free or low-cost things that small business IT professionals or IT support providers can do to eliminate nearly all malware from the computer networks they protect.
- Replace RDP with VPN – You should block port 3389 on your firewall for Remote Desktop Protocol and limit RDP sessions to those inside your network perimeter. Set up and use a Virtual Private Network when connecting to a computer from outside your firewall. Attackers search for open RDP ports to exploit for gaining access to a network remotely.
- Content Filtering – Paying a little extra for content filtering, either at the firewall, or better yet through a web proxy such as OpenDNS or Cisco Umbrella can prevent your employees from clicking through on a malicious link from a phishing email or having their browser redirected to a malicious web page. You can also block websites by content or subject matter as well.
- Geo-blocking – If your small business does not do business in Russia, China, India, or other countries where cybercrime is a major industry, then perhaps blocking access to these countries entirely, at your firewall or web proxy is another good way to keep your employees safe and out of trouble.
- Block exploitable file types – Make changes to your firewall and email filter to block these commonly exploited file types: .ADE, .ADP, .BAT, ..CAB, CHM, .CMD, .COM, .CPL, .DLL, .DMG, .EXE, .HTA, .INS, .ISP, .JAR, .JS, .JSE, .LIB, .LNK, .MDE, .MSC, .MSI, .MSP, .MST, .NSH .PIF, .SCR, .SCT, .SHB, .SYS, .VB, .VBE, .VBS, .VXD, .WSC, .WSF, .WSH.
- Registry Changes to Block Scripts – VBScript and JavaScript is often used in exploits and can be hidden in plain site or as part of a ZIP attachment. Microsoft recommends running this script to make the necessary changes to block scripts from running.
- Close MS Office vulnerabilities – Microsoft Office has been exploited through the use of Macros, Object Linking and Embedding (OLE), and Dynamic Data Exchange (DDE) flaws. Macros can be disabled inside of Office. OLE and DDE can be restricted following the instructions at the links below.
- Restrict PowerShell – PowerShell has been used in a number of recent exploits because PowerShell is a trusted application in the Windows environment. Turning up Windows AppLocker and restricting PowerShell to select administrator accounts only is a good solution.
- Endpoint Antimalware – Selecting and using an endpoint antimalware product can be an important decision. Look for products that go beyond traditional virus and malware blocking, and have some heuristics and IPS capabilities as well. And keep the local machine softare firewall turned up as well.
By completing these few projects, an IT administrator can block a very high percentage of malware types and exploits from getting into the network, with a few hours time and almost no additional costs. Give them a try on your network.
More information:
- Google – File Types Blocked in Gmail.
- TechNet – restrict the Ability to Run Scripts
- Microsoft – Blocking Macros in Office
- Microsoft – OLE embedded malware
- Disable DDE
- Bypassing PowerShell
- Disabling PowerShell
- Content filtering tools
JUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com