 Is your computer technology Managed Service Provider (MSP) the weakest link in your supply chain security program? Are they the easiest point of entry for an attacker? Your contracted tech support provider holds keys to your computer network that are coveted by cyber-attackers. MSPs are commonly targeted by cyber-criminal groups and other bad actors because MSPs have unparalleled access to their clients’ networks. What kinds of security controls have they put in place on their own network? Are they as secure as they ought to be? Have you checked?
Is your computer technology Managed Service Provider (MSP) the weakest link in your supply chain security program? Are they the easiest point of entry for an attacker? Your contracted tech support provider holds keys to your computer network that are coveted by cyber-attackers. MSPs are commonly targeted by cyber-criminal groups and other bad actors because MSPs have unparalleled access to their clients’ networks. What kinds of security controls have they put in place on their own network? Are they as secure as they ought to be? Have you checked?
As a cybersecurity instructor, I am currently working with a large hospital systems cybersecurity department whose members are studying for the CISSP certification exam. This question came up in the practice questions: “What is the first step in working with a third party cybersecurity firm?” The correct answer was to have the security vendor submit to a vulnerability assessment. I found the answer surprising, but as I thought about it, it makes perfect sense.
For a period of over two years I worked with a large MSP. As a large contract IT shop they had a managed service platform that they had deployed to hundreds of client networks, comprised of thousands of devices.. This is commonly known as an RMM or Remote Monitoring and Management system. These tools work by installing a small program called and “agent” on the computer systems being managed by the MSP. The agent program keeps track of system status, and alerts the help desk staff if a computer or server is having difficulties of any kind. RMM systems also allow the help desk to remotely access the affected computer over the Internet, log in to an administrative account, troubleshoot and even repair the system. The RMM system and all the client computers are managed by a command and control server that provides a control dashboard for the help desk staff to use. If this sounds like a bot-net, that’s because it is a bot-net. But a bot-net to help the MSP support their clients. A “good” botnet. But what happens if a good bot-net is hijacked by a bad actor?
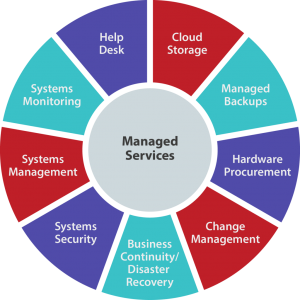
This MSP hired me to create a cybersecurity practice area that they could offer to their clients. This is currently a big expansion area for MSPs. This type of support business is called a Managed Security Services Provider of MSSP. As we rolled our the new product and service offerings, one of the first products was a UTM (universal threat management) and SEIM (security event and incident management) system from Alien Vault. This added another agent to protected systems, and looked for anomalous traffic and attacks, and reported back to the Security Operation Center (SOC) staff.
Vulnerability scanning and assessments were one of the other early service offerings that a client company could hire us to perform. Over my time at this MSP, I must have done close to a hundred of these scans. At no time did any on the clients I worked with ask us to submit to a third party cybersecurity review of any sort.
And that is my point with this article. Many businesses, maybe yours, have some sort of tech support service arrangement with an outside support company. Maybe your vendor has installed the RMM tools I discussed earlier. Do they ever have their own network scanned for vulnerabilities? Have you ever asked your MSP to share with you what sort of security they have deployed on their own network?
At a recent presentation I saw at the local (ISC)2 chapter meeting, the presenter, Josh Marpet of Red Lion was talking about ransomware attacks against MSPs. In a worst case scenario he told us about, an employee of the MSP fell for a phishing email, and released a crypto-ransomware attack on the MSP network. It quickly spread to the networks of all the customers with RMM agents on their computers. This attack also wiped out network attached back-up systems. This MSP and their clients were screwed.
When you hire an MSP or even a new-fangled MSSP, I am sure your expectation is that their own security is top-notch. While this should be the case, often it is not. The security systems they sell to you is a new profit center, and becomes part of their recurring revenue stream, and goes to the income side of the ledger. The money they spend securing their own network falls to the expense side of the ledger. Just as the shoemaker’s kids are barefoot, often the companies we trust to run our networks do not deploy the same solutions to their networks that they are selling to you.
Some of the common shortcomings of an MSP are:
- Using short, easy administrative passwords.
- Lack of two-factor authentication and password management.
- Passwords often stored on a shared Excel spreadsheet.
- Sharing the same administrative account between several help desk employees.
- Using the same credentials to access every customer network.
- Not providing cybersecurity awareness training to their own staff, especially administrative, human resource, senior management, and sales employees.
The MSP that I worked for did an overall excellent job at securing client information and access to client networks. Passwords were long, and supplemented with two-factor authentication. To access client networks via the RMM system required a client-unique 20 character password and 2FA. Passwords for clients were stored in an encrypted password management system that also used 2FA. The MSP itself was the first Alient Vault client, and they monitored their own network in the SOC. One of the tasks I was responsible for was running a quarterly automated vulnerability assessment against our own network and reporting the security state to company management. Another task was reading the SIEM reports about potential new vulnerabilities or possible attacks, and following up the SOC when the situation warranted it. We provided cybersecurity awareness training on a semi-annual basis to the technical, administrative and sales staff. The company ran a Barracuda Spam Firewall that protected employee inboxes from most phishing emails. We ran phishing simulations against our own employees to train them to detect ones that might get through.
But not one of our clients ever once.asked me to provide a recently vulnerability assessment to or describe the security controls we had in lace to protect ourselves and our clients. I bet you haven’t either. Maybe you should.
More information:
ShareAPR




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com