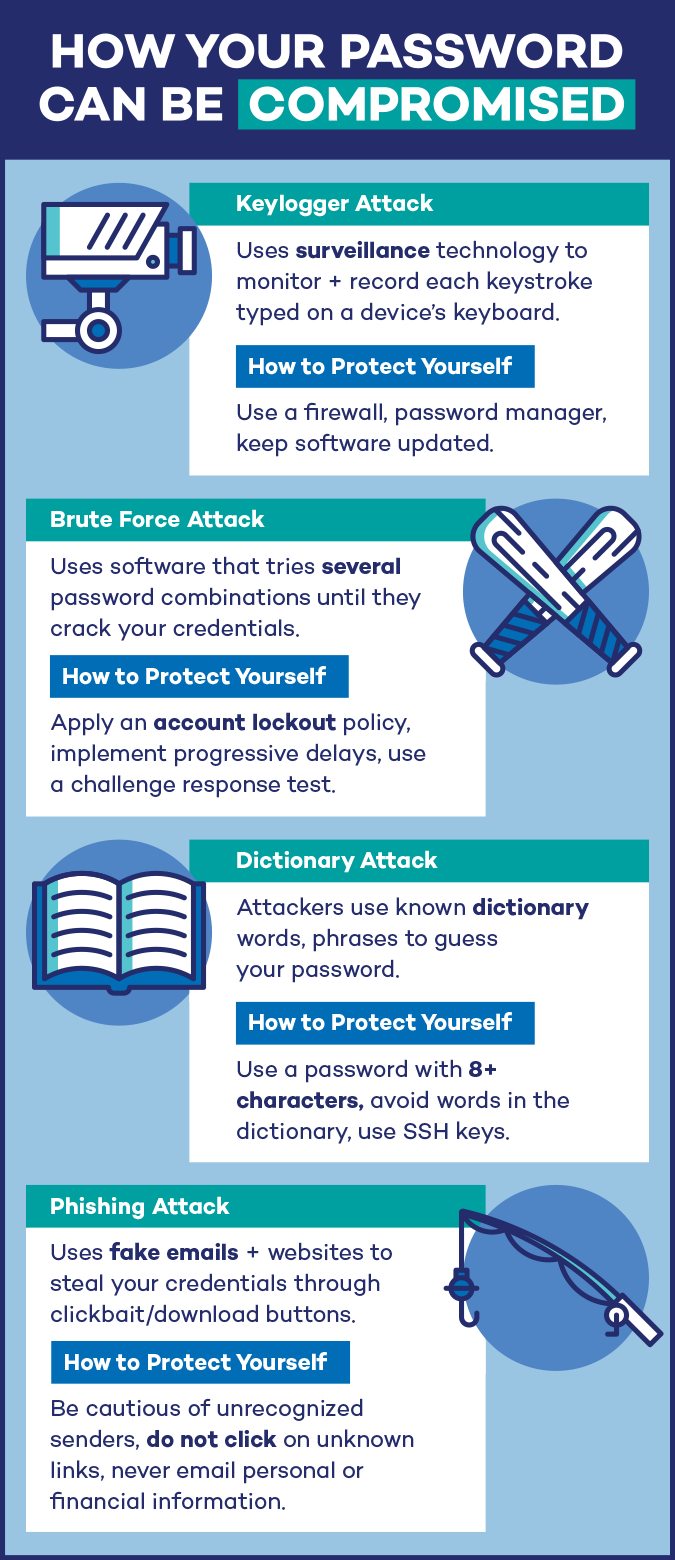
In our last post we looked at the frighteningly short amount of time that it takes to crack a typical password. Today we will look at all the different password cracking methods that a clever attacker can use to compromise your password, and how to defend against these attacks.
Password cracking
There are several types of automated password attacks that can be combined to make the process quicker, or to configure for a certain type of password attack.
- Dictionary attack – This is the quickest method and can easily solve more than half the passwords on the list. It works by checking known popular passwords and words found in a dictionary. You can protect yourself from this by avoiding popular passwords or dictionary words as your password.
- Brute-force attack – This method tries every possible combination of upper case and lower case letters, numbers, and symbols, and is very thorough. This takes more time, but it can solve the entire 281.5 trillion possible 8 character password combinations in 24 hours or less, depending on the equipment. The best defense against this is to create passwords that are longer than 12 characters.
- Hybrid attack – Hybrid attacks combine some characteristics of both brute-force and dictionary attacks with human predictability. Hybrid attacks looks for variations of popular passwords that might use some character substitution. Predictability exploits the things that people tend to do, like capitalizing the first character, and using the number 1 and the exclamation mark at the end of their passwords. These factors are added into the password cracking algorithm. I have read stories about hybrid attacks that can solve long passwords of 12 or more characters in a matter of hours. The best defense is to avoid making your long password by combining two or more dictionary words. At this point a 20-character randomly generated password would be your best defense. We will tell you how to do this in the next post.
- Password spraying – Brute-force attacks sends hundreds or thousands of tries against a single password protected account. Password spraying sends a single attempt against hundreds or thousands of systems, and then starts over again with a new password. Typically used in on-line attacks, see below.
- Off-line attacks – This happens when a password file or database has been exported from a web server or domain controller, and the passwords can be cracked automatically in bulk at the attackers leisure. Your best defense is to use passwords longer than 12 characters, that take decades or centuries to crack.
- On-line attacks – In this attack password cracking is attempted directly against the web site login screen using automated tools, and possibly password spraying. With password spraying, and attacker with try the same user and password combination on hundreds of accounts or websites, and then start the process over with a new user and password combination. This overcomes security strategies such as rate limiting, or locking out an account after a certain number of incorrect attempts within a certain time frame. This is used against WordPress websites, email accounts from Gmail, Outlook.com, or Yahoo, as well as popular online services such as Twitter and Facebook. Again, your best defense is to use passwords longer than 12 characters.
Our next post will reveal other methods that can be used by an attacker to compromise your password.
A special thanks to Panda Security for inspiring the content of this series and providing us with the infographics used in this series.
ShareJUN




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com