 I love hash, especially corned beef hash, with a little salt. Maybe a couple of poached or over-easy eggs perched on top. Wait! This is not a foodie blog! That’s not what I am writing about today. As it turns out, using a hash plus a salt is a great recipe for keeping passwords secure on a web server or an authentication database.
I love hash, especially corned beef hash, with a little salt. Maybe a couple of poached or over-easy eggs perched on top. Wait! This is not a foodie blog! That’s not what I am writing about today. As it turns out, using a hash plus a salt is a great recipe for keeping passwords secure on a web server or an authentication database.
If your password has been extracted from a web server breach somewhere, you may already be aware that many website store passwords in a way that makes them easy to crack. (And who hasn’t lost a password or two? Check www.haveibeenpwned.com to find out)
If you are operating a website, and collecting your web site’s user credentials, the responsibility to adequately secure your users’ information is yours. And if you think your site is too small to interest cyber-criminals, you would be wrong.
There are several ways to protect passwords. Which one is your website using? Don’t know? I may have some answers for you down the page a bit, so stick with me.
- Unencrypted or plaintext password stores can still be found occasionally. This is the worst way possible to store a password. If you are doing this, please stop.
- Encrypted passwords sound like a great idea until you realize that if you lose the encryption key, the entire encrypted database can be deciphered.
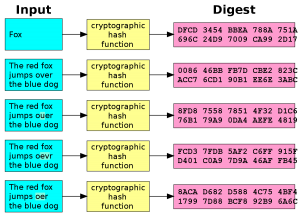 Hashing the password is a one-way form of encryption that cannot be reversed, even with knowledge of the encryption key. This is the way that most passwords are stored in web servers and online databases, and even network operating systems such as Microsoft Active Directory. The problem is that some sites use old methods of hashing such as MD5 or SHA-1. These older hashing algorithms use keys that are too short. SHA-256 is a good solution. But we could do better.
Hashing the password is a one-way form of encryption that cannot be reversed, even with knowledge of the encryption key. This is the way that most passwords are stored in web servers and online databases, and even network operating systems such as Microsoft Active Directory. The problem is that some sites use old methods of hashing such as MD5 or SHA-1. These older hashing algorithms use keys that are too short. SHA-256 is a good solution. But we could do better.- Salt is also called a “nonce” or a number used once. If I add a random number to the password and then hash it, it makes it much more difficult to crack the password, even using brute-force automated methods. It also prevents two users who are coincidentally using the same password for getting the same hash result. The salt prevents that.
- Stretching increases the complexity of the hash by hashing the password multiple times. These are call “iterations.” So if I take the password, hash it, add some salt, and hash it again, many times, maybe thousands of times, my hashed password result would be nearly impossible to solve, as the password cracker would have to know what hashing algorithm was used, what the salts were, and how many iterations were run. Or we could say they are pretty much out of luck. A popular hashing method that does all these things is called bcrypt.
So how do the popular website builder programs, often called a CMS or a Content Management System, stack up at protecting passwords? What kind of password hashing is built into them?
- MD5 – Even though MD5 is regarded as too old and insecure to be useful, over 25% of popular CMS programs still used it including WordPress, osCommerce, SuiteCRM, X3cms, SugarCRM, CMS Made simple, MantisBT, Simple Machines, miniBB, Phorum, MyBB, Observium, and Composr. WordPress users who are despairing that WP uses MD-5 natively can improve their security by installing a bcrypt plugin such as WP Modern Password Hashing or PHP Native password hash.
- SHA-1 – Over 10% of CMS system still use SHA-1, even though it has been deprecated. Some of the guilty are GetSimple CMS, Redmine, Collabtive, PunBB, Pligg, and Omeka.
- bcrypt – bcrypt is a well-regarded solution for properly hashing and securing passwords, and is used by Joomla, Zurmo, OrangeHRM, SilverStripe, Elgg, XOOPS, e107, NodeBB, Concrete5, phpBB, Vanilla Forums, Ushahidi, Lime Survey, Mahara, Mibew, vBulletin, OpenCart, PrestaShop, and Moodle.
If you are collecting user credentials in your website, take a moment to discover how password security is handled by your website. If you need to make changes or updates, do so. Your customers, clients, and staff, will appreciate it.
More information:
- Sophos Naked Security – Store Your Users’ Passwords Safely
- Sophos Naked Security – Pass the Salt!
- Department of Digital Systems at the University of Piraeus in Greece
JUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com