Phishing Email Alerts
Catch of the Day: Another IONOS Phish
Chef’s Special: Excel XLL Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Another IONOS Phish
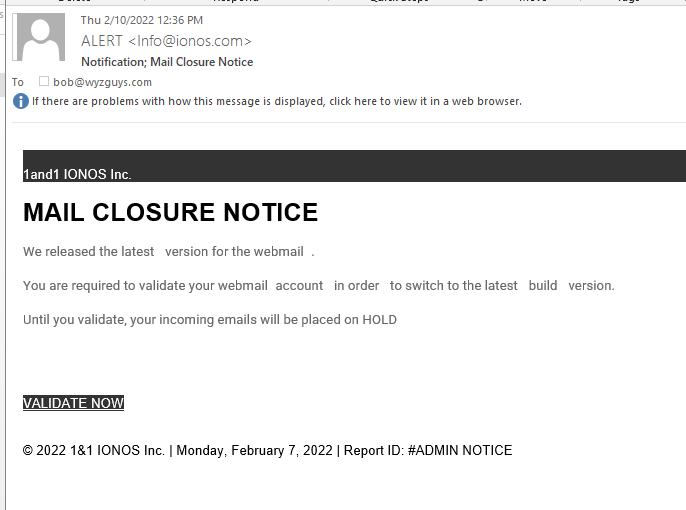
Here is another credential stealing phish with a MAIL CLOSURE NOTICE threatening to put my emails “on hold” whatever that means.
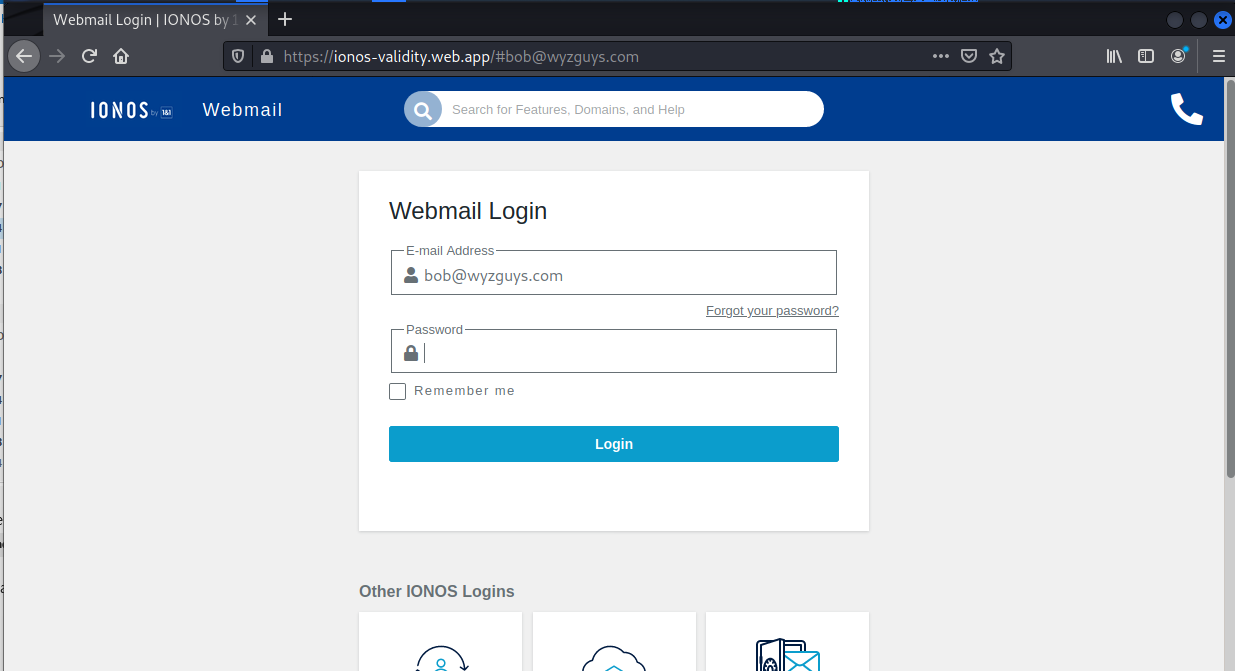
The Validate Now button resolves to http://bit.do/fTsj2#bob@wyzguys.com then is redirected to https://ionos-validity.web.app/#bob@wyzguys.com. Here is the landing page.
When entering my fake password, this page gave me an incorrect password error.
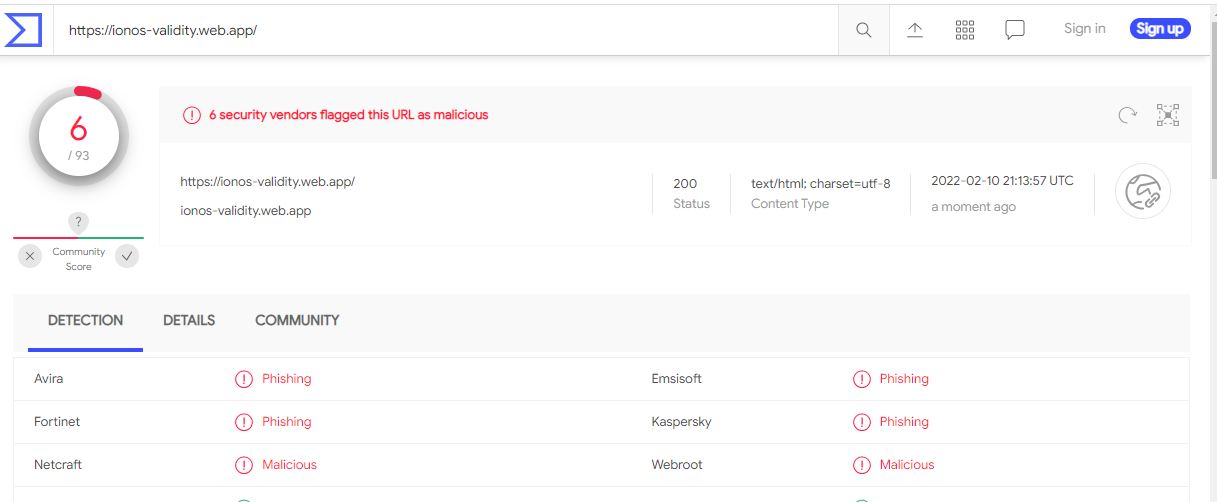
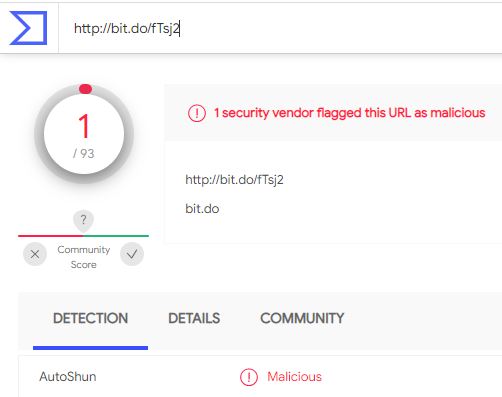
VirusTotal flagged both of the URLs used in this exploit.
Use of Excel .XLL Add-Ins Soars Nearly 600% to Infect Systems in Phishing Attacks
Cybercriminals are taking to more advanced functionality than traditional VBA scripting to both execute complex malicious actions via Excel and to obfuscate their true intention – phishing attacks.
If I had a nickel for every time I heard about a malware attack that used macros embedded in an Office document, I’d have quite a few nickels by now. It’s an age- old tactic that, to this day, remains an effective means to execute malicious code.
But new data from HP Wolf Security’s Threat Insights Report Q4 2021, just released this month, shows a newer tactic very quickly growing in popularity in the form of an Excel Add-In. These add-ins allow individuals to create custom functions using the Excel JavaScript API that can be used – in most cases – across Excel on Windows, Mac, and within a web browser, making this potentially very dangerous.
According to Wolf Security, they’ve seen this technique used in malware we’ve covered here in our blog, including Dridex, IcedID, BazaLoader, Agent Tesla, Raccoon Stealer, Formbook and Bitrat. And in Q4 of last year (the timeframe covered by their latest report), the presence of XLL files increased 588% over Q3.
Emails sent to potential victims include a malicious XLL file as the attachment. Clicking it launches Excel and prompts the user to install and activate the add-in.
Blog post with links: https://blog.knowbe4.com/use-of-excel-.xll-add-ins-soars-nearly-600-to-infect-systems-in-phishing-attacks
- [RELATED NEWS] MSFT Finally (!) blocking some macros by default:
https://techcommunity.microsoft.com/t5/microsoft-365-blog/helping-users-stay-safe-blocking-internet-macros-by-default-in/ba-p/3071805
FEB





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com