Phishing Email Alerts
Catch of the Day: Outlook Web App Phish
Chef’s Special: Fake Copyright Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Outlook Web App Phish
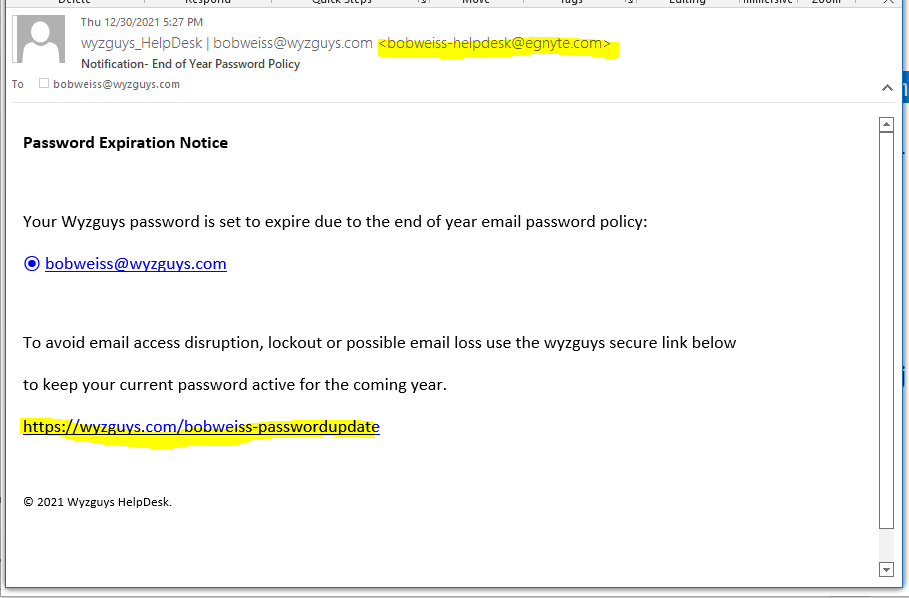
This is a simple credential stealing exploit aimed at Outlook Web App, MS Azure, or Office365 users. The quality of the trade dress is pretty good. Below is the email that starts it all.
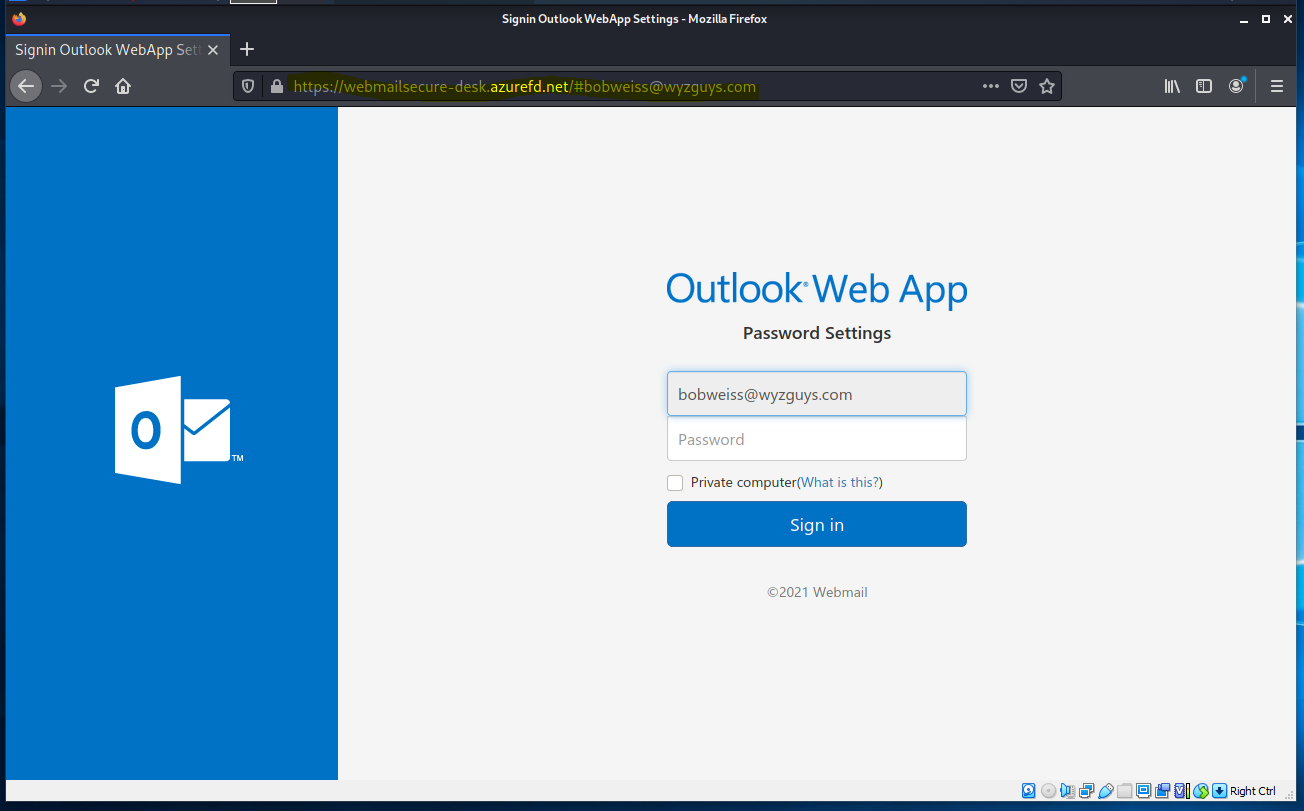
The bobweiss-passwordupdate link resolves to https://webmailsecure-desk.azurefd.net/#bobweiss@wyzguys.com which reveals this landing page
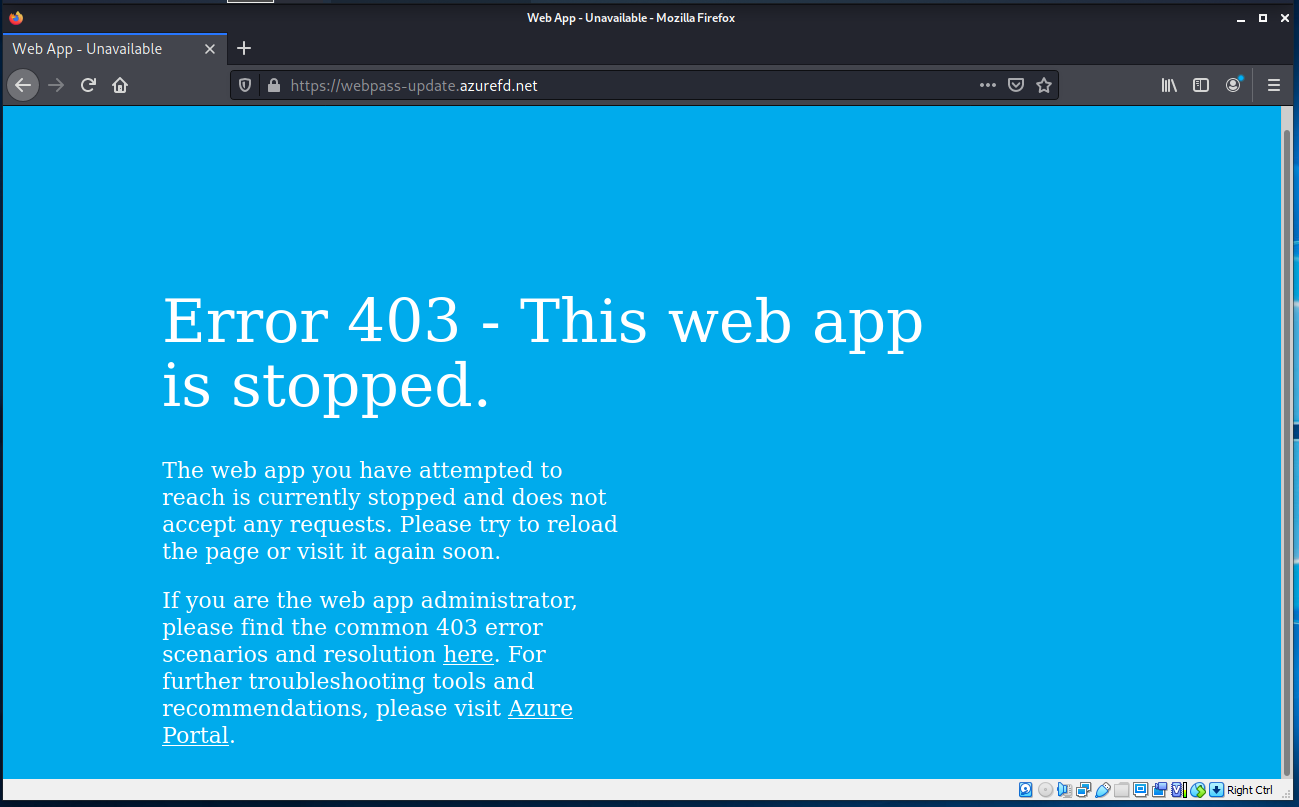
Entering a password and clicking Sign in sends the entered credentials to the phishers. This action also sends you to this error page.
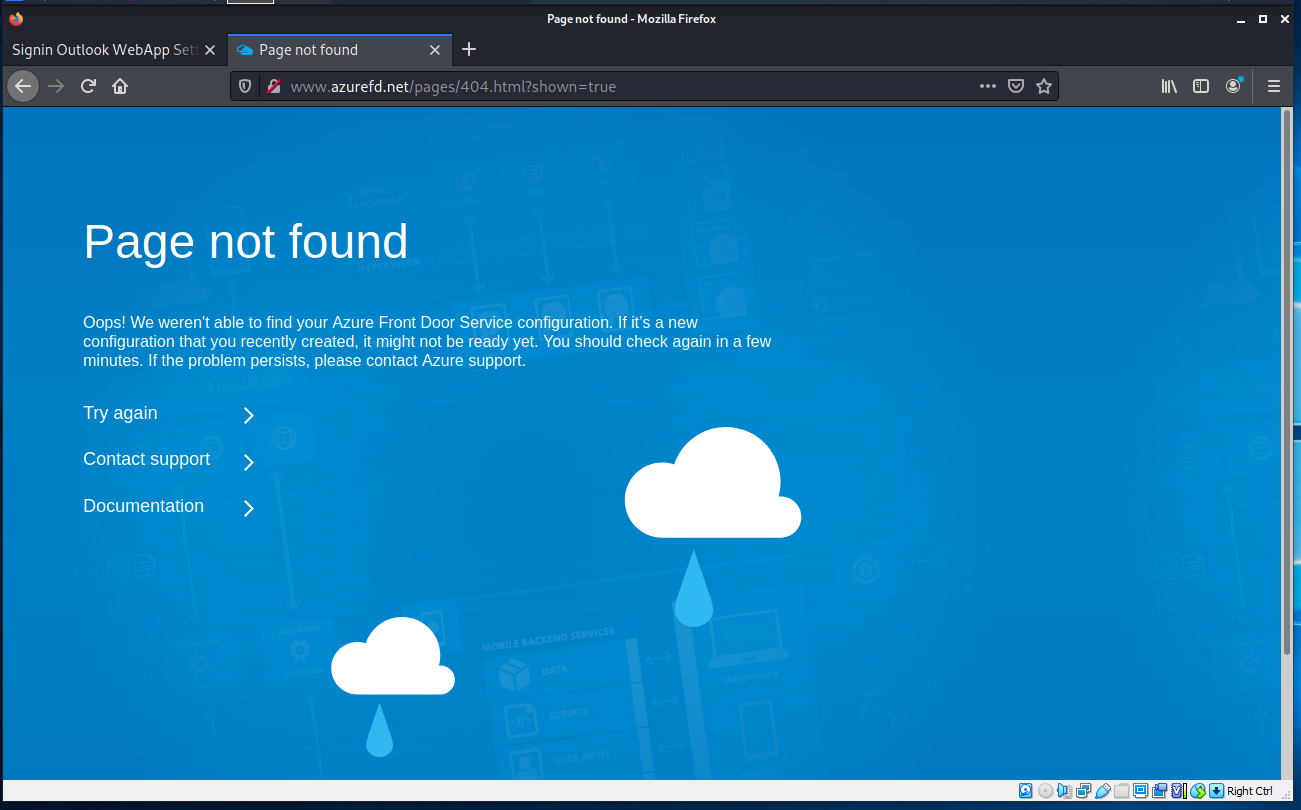
This exploit appears to be built out on an Azure space at azurefd.net. This service is called Azure Front Door. This is the error page I got when I tried to check it out.
Followers of my web blog would recognize this as a phishing email from the start. Make a New Year’s Resolution not to be fooled by exploits like this one in 2022.
Instagram copyright infringement scams – don’t get sucked in!
We deconstructed a copyright phish so you don’t have to. Be warned: the crooks are getting better at these scams…
Phishing Attacks Remain the Top Type of Cybersecurity Breach This Year
Over half of organizations say they’ve experienced a cybersecurity breach caused by phishing in the last 12 months, dwarfing the second-place breach cause (malware) by almost 30%. The latest data from Dark Reading’s annual Strategic Security Survey shows phishing continues to be an organization’s biggest problem. With 53% of organizations citing phishing as being the cause of a security breach (up from 51% in 2020), organizations are keenly aware of the problem that exists when mixing users, social engineering, and phishing emails.
According to the survey:
- 58% say users being socially engineered via phishing or other scams is the most significant endpoint security concern
- 48% of respondents say that if their organization experiences a major data breach in the next 12 months, the most likely cause will be a negligent end user
So, users are definitely the weak link in the security chain in most orgs. And this requires some shoring up of security efforts around users, including security awareness training to turn the user from a security liability to an asset who aids in protecting the organization. According to the survey, of those organizations that experienced a cybersecurity breach in the last 12 months, 23% reported network disruptions and application unavailability, 17% say they experienced a major financial loss, and 15% reported fraud. Blog post with links:
https://blog.knowbe4.com/phishing-remains-top-form-of-cybersecurity-breach-in-2021
Recent Nigerian Phishing Scams Target U.S. Military Families With Needed “Services”
With loved ones potentially a half a world away, scammers prey on families with scams that offer to assist with communication, care packages, leave, and more.
We all know military families sacrifice a lot so their loved ones can serve literally anywhere on the globe. It’s also well-known that military folks aren’t exactly making CEO-level compensation either. So, it’s pretty disgusting to hear that scammers are targeting these folks to separate them from their hard-earned money. According to new detail from security vendor Lookout, a wave of new scams leveraging more than 50 very realistic websites are focused on tricking military families into paying for services that will never be provided.
The services being offered include:
- Communication Permits
- Application for Leave
- Care Packages
- Compensation Fund Applications (for those that have lost someone in the line of duty)
- Deployment Declination
- Marriage
- Housing Options
- Resignation
Victims are asked in many cases to pay exorbitant prices for these services – well beyond anything reasonable in the real world. This is beyond low. A list of the fake domains is provided by Lookout for reference.
Blog post with links:
https://blog.knowbe4.com/new-nigerian-phishing-scams-target-u.s.-military-families-with-needed-services
New Omicron-Themed Phishing Attack is Now Running Rampant
A mean-spirited phishing campaign is mocking victims after infecting their devices with Dridex malware, according to Lawrence Abrams at BleepingComputer.
“Over the past few weeks, one of the Dridex phishing email distributors is having fun toying with victims and researchers,” Abrams writes. “This was first seen when the threat actor began trolling security researchers by using their names combined with racist comments as malware file names and email addresses. More,,,
West Virginia Healthcare Breach Traced to Phishing
Monongalia Health System in West Virginia has disclosed a data breach that exposed sensitive patient and employee information.
“Monongalia Health System, Inc., and its affiliated hospitals, Monongalia County General Hospital Company and Stonewall Jackson Memorial Hospital Company (collectively, ‘Mon Health’), announced that it recently investigated and addressed an email phishing incident, and is now notifying individuals, including patients, providers, employees, and contractors, whose information may have been involved,” the company said in a press release. More…
5 Notable Obscure Phishing Scams
By Roger Grimes.
We know that customers who frequently educate and test their co-workers reduce cybersecurity risk lower than those that do not. The best security awareness training programs educate people in the most common social engineering attacks first and best. You should make sure your security awareness training program focuses on the most likely attacks.
At the same time, it can’t hurt to sprinkle in the less common types of social engineering attacks so that people get introduced to a wide range of methods and tricks. With that thinking, here are five interesting, but more obscure, phishing scams.” The blog post has examples, screenshots and links:
- Browser Notifications
- NFT Scam
- Spellcaster Scam (yes)
- Fake CNN Video
- PayPal Family and Friends
The blog post also has a super simple graphic you can use to send to your users, with a bare bones algorithm they can use to determine if something is phishy: https://blog.knowbe4.com/5-notable-obscure-phishing-scams
Share
JAN





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com