Phishing Email Alerts
Catch of the Day: Solar Power Phish
Chef’s Special: Geek Squad Renewal Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Solar Power Phish
Technically speaking, this is a bit more of a SPAM exploit than a phish, but enough personal information is gathered that it could be either, or both SPAM and phishing. The exploit starts out with this email.
The email originates from the domain ghbob.com and is used in both the email sender address and the link address. Anthony does not live with us at this address.
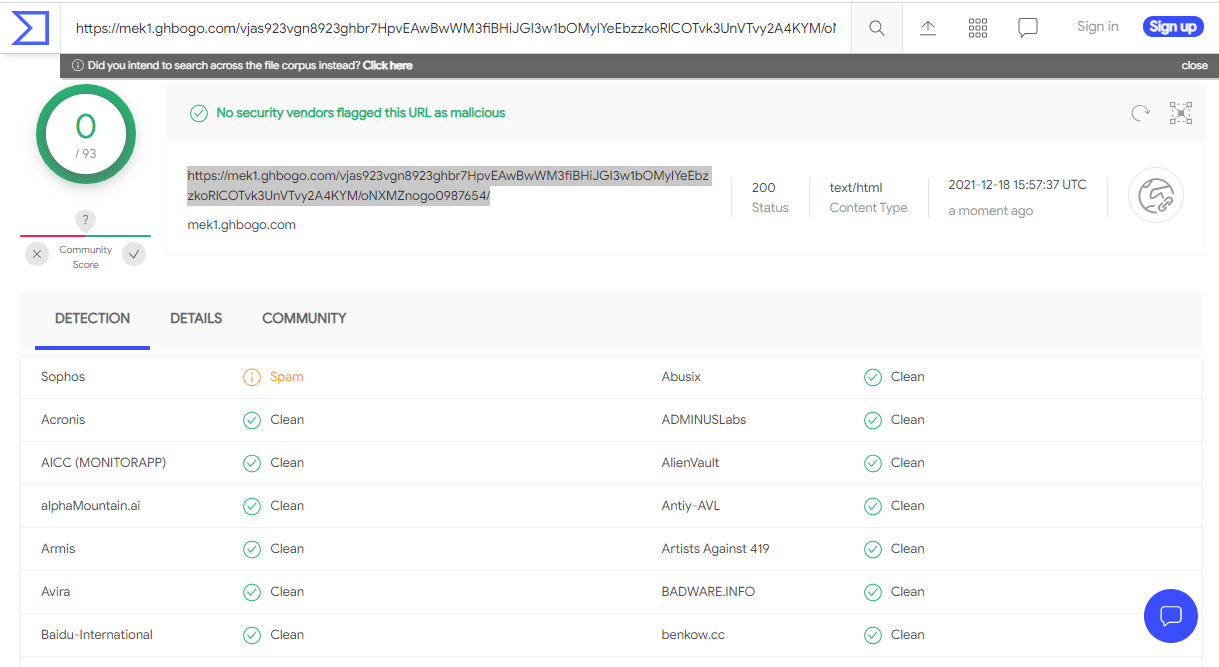
Virus total indicates that this is an known address for spamming. This is the address provided my the SUBMIT button.
https://mek1.ghbogo.com/vjas923vgn8923ghbr7HpvEAwBwWM3fiBHiJGI3w1bOMylYeEbzzkoRlCOTvk3UnVTvy2A4KYM/oNXMZnogo0987654/
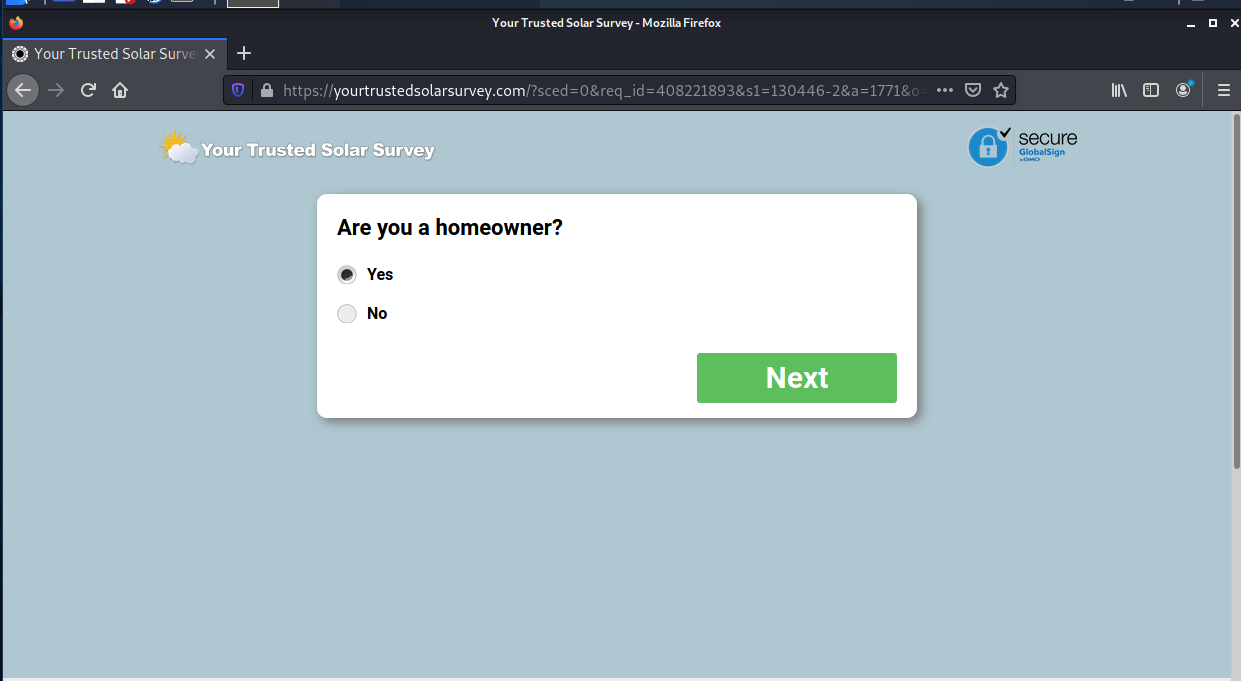
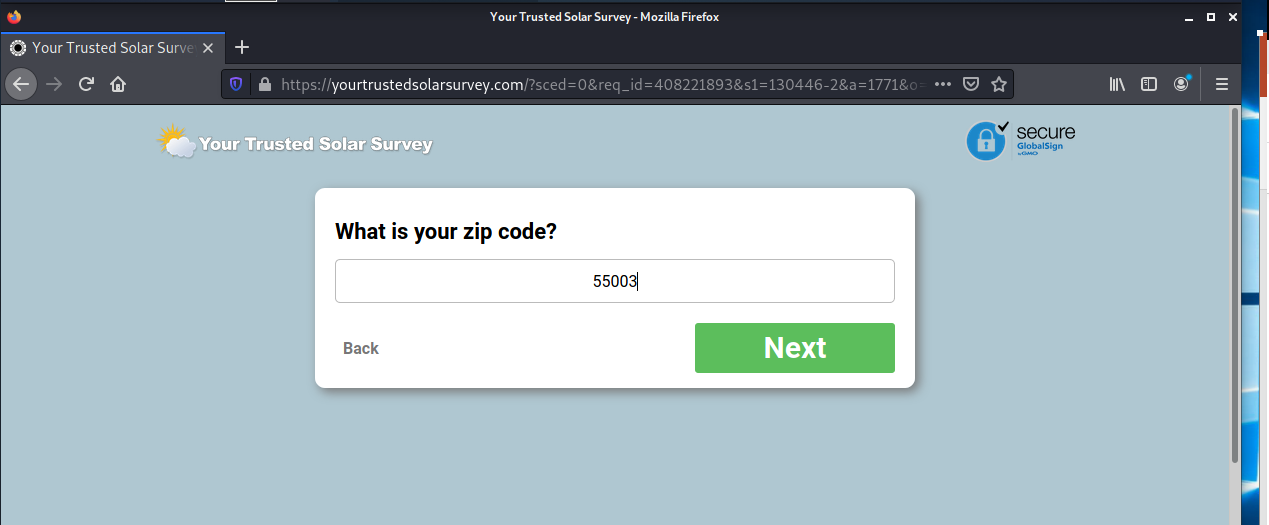
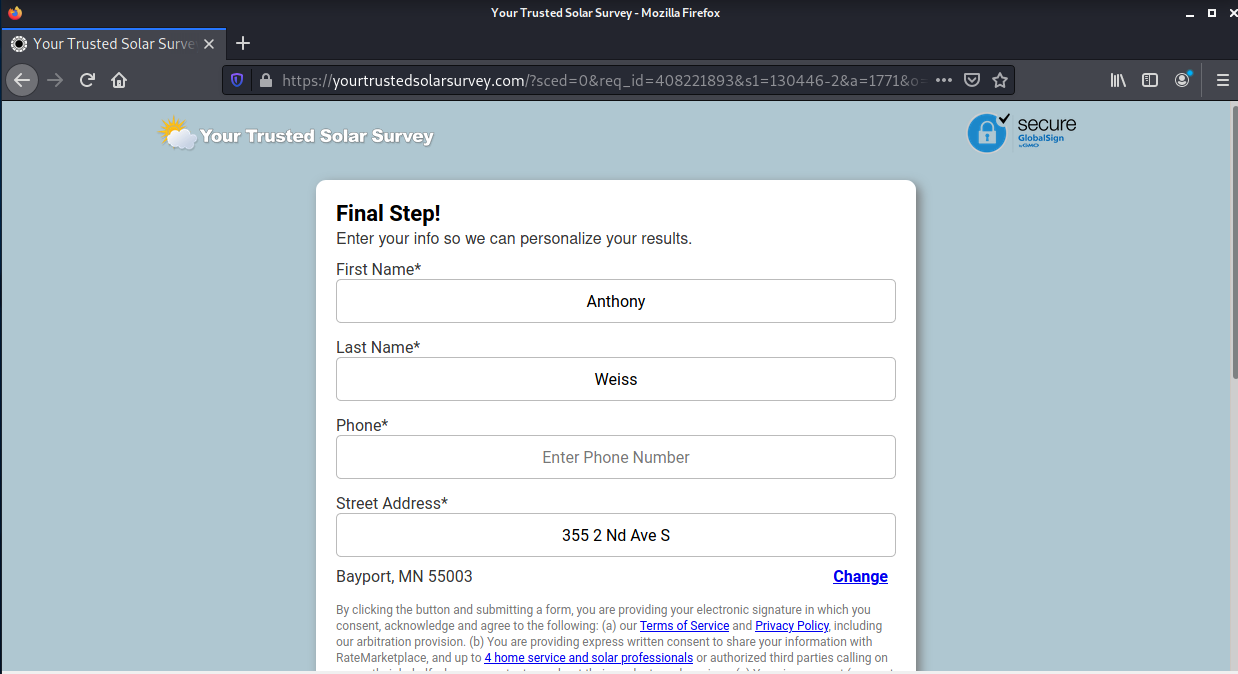
The submit button resolves to the mek1.ghbogo.com which is redirected to https://yourtrustedsolarsurvey.com/?sced=0&req_id=408221893&s1=130446-2&a=1771&o=3593&cpid=30086&s2=7498855&s3=&s4=&s5=&first_name=Anthony&last_name=Weiss&address=355+2+Nd+Ave+S&email=bob%40wyzguys.com&zipcode=55003&credit=Poor&phone_primary=&np=1#first-frame
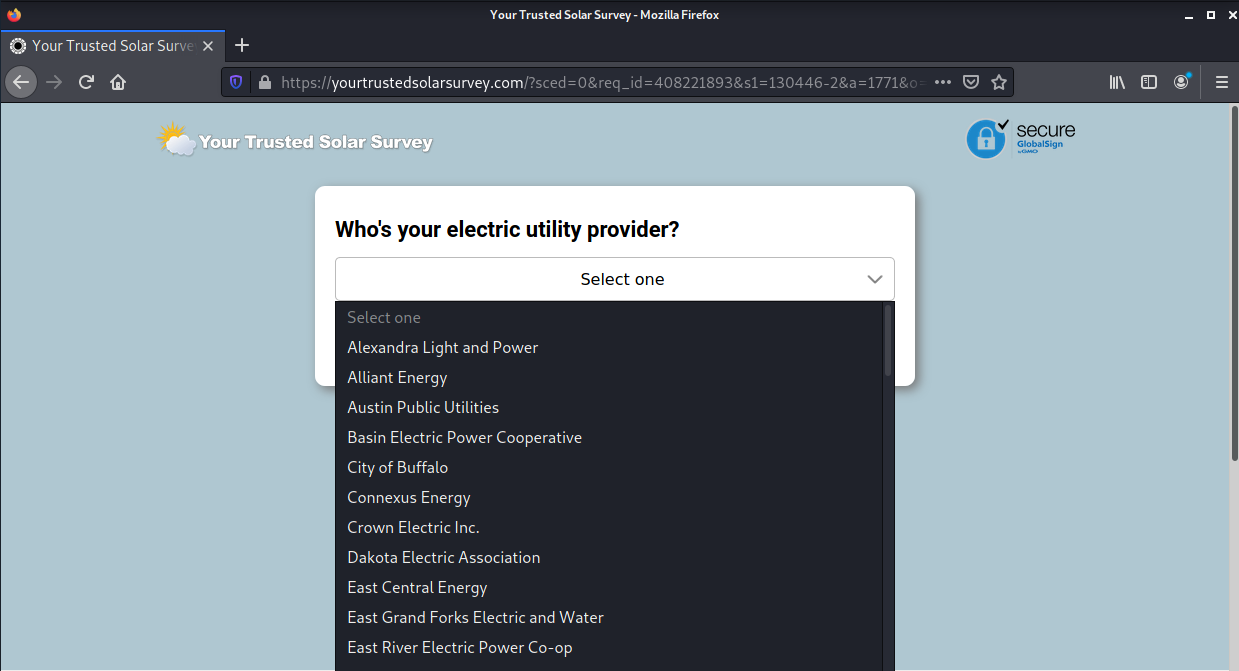
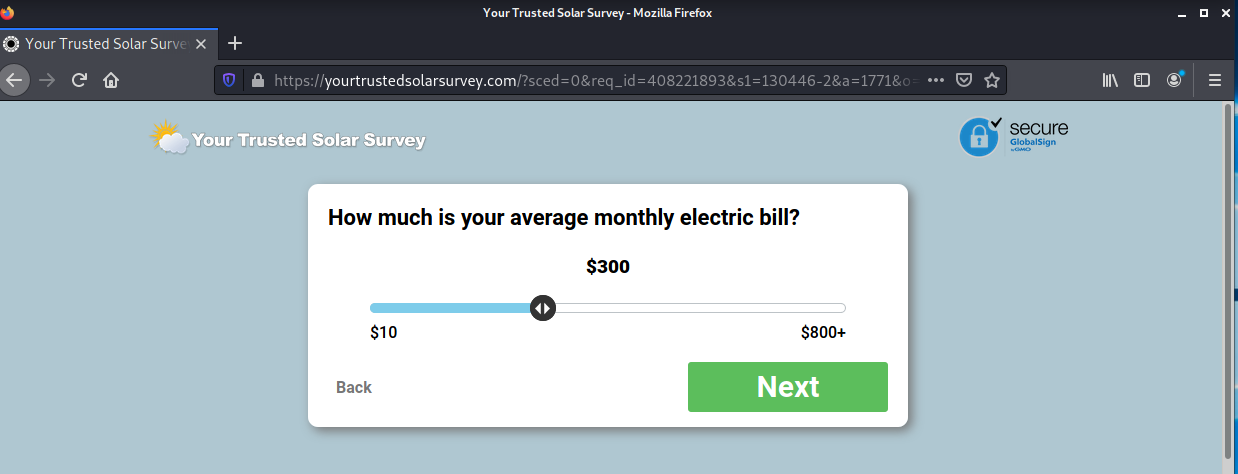
Note the change in the domain name used for the landing pages. yourtrustedsolarsurvey.com. The landing page is the first in a long series of survey questions that turn out to be about home solar energy systems.
I skipped a few pages but there were additional questions about the amount of sun on my roof and my credit score. Then we finally finished the survey.
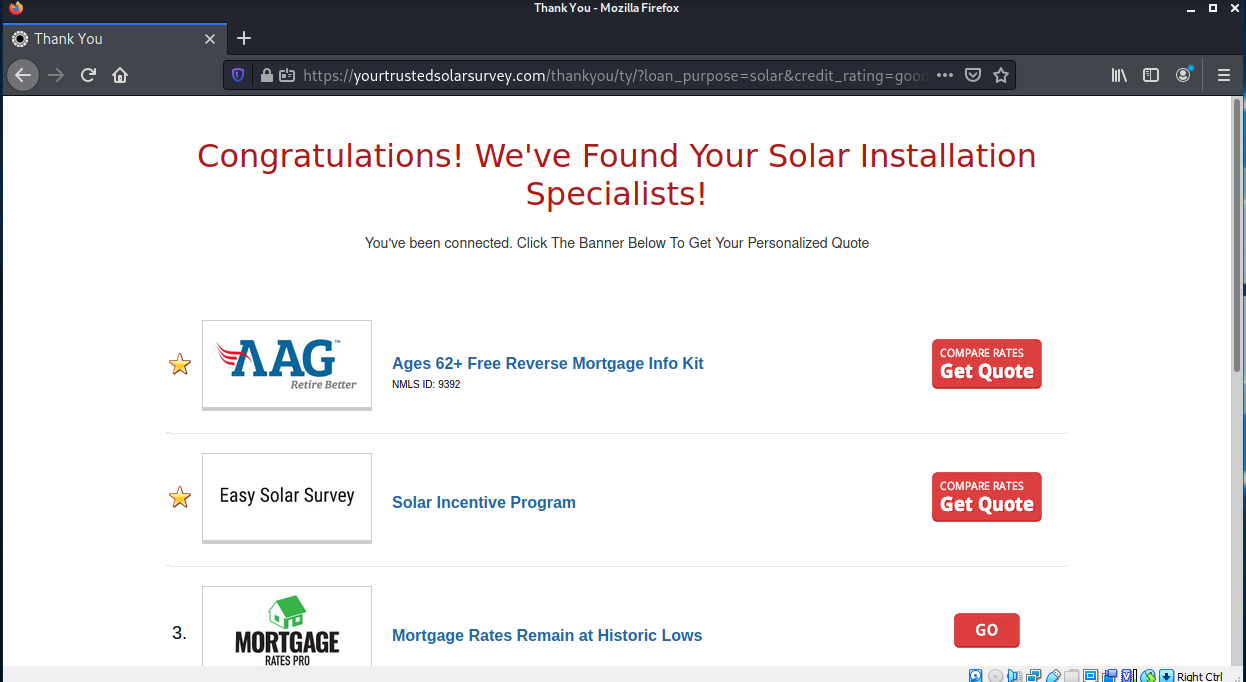
And then we are presented with our “report.”
Any first contacts from the information I provided will go to an email I use for investigation purposes. I expect to be bombarded with SPAM. Stay tuned for follow up reporting on this exploit.
Best Buy / Geek Squad Renewal Phish
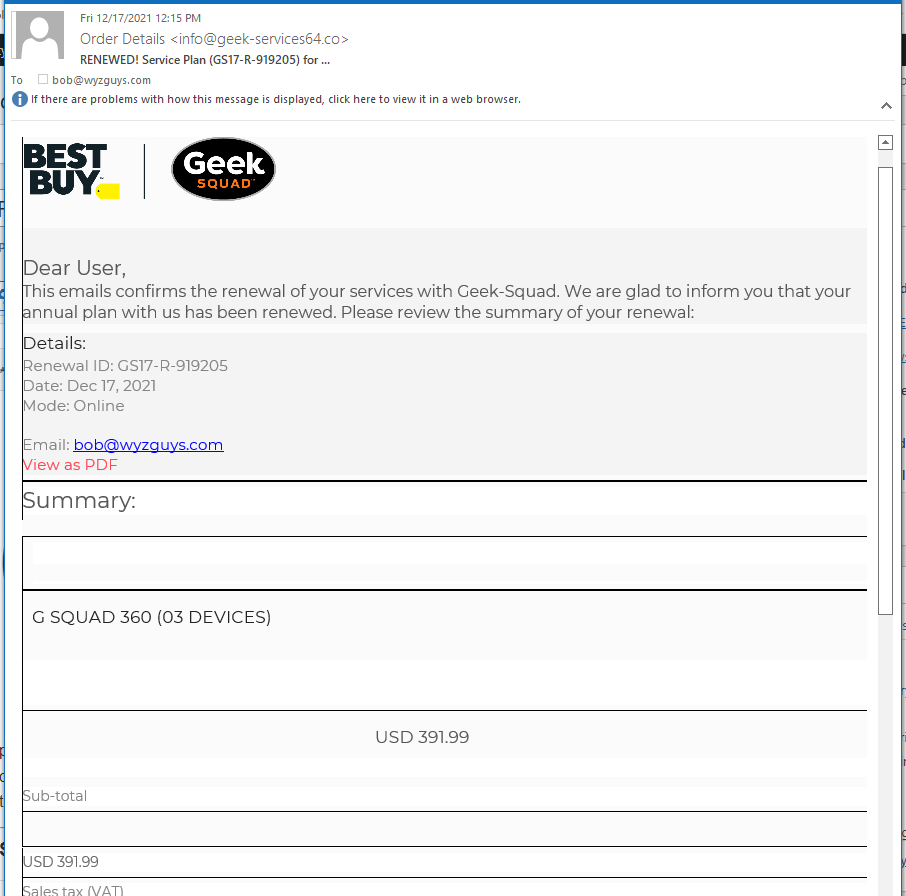
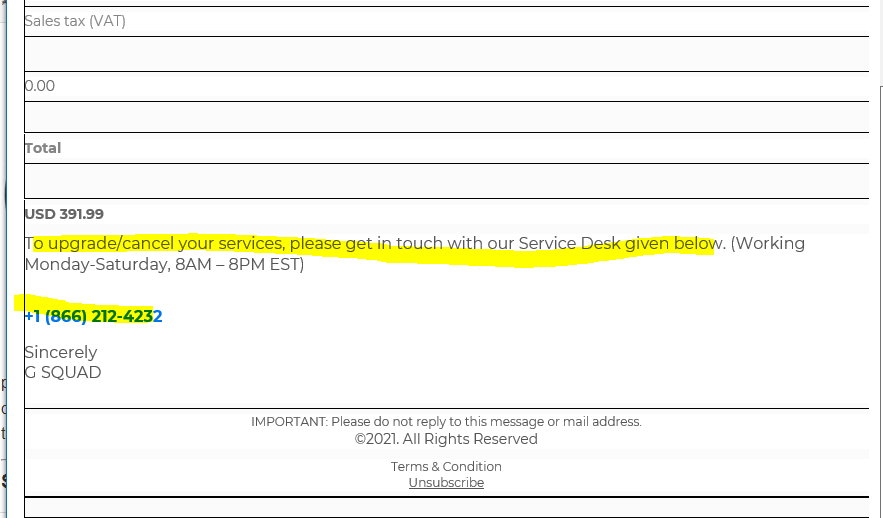
No you did not have an annual support plan with the Geek Squad (unless you did.) This email is phony, and the $391.99 charge will not appear on any credit card statements. The goal here is to get you to call the Support number at the bottom of the invoice.
In this social engineering scam, the support agent will “need you credit card number” to refund the spurious charges. Perhaps they will ask for and collect other personally identifiable information.
If you feel compelled to check, look for new charges on your bank card or credit card accounts. There will be no new activity, and this should allay your concerns. And remember, your credit cards are protected against fraudulent use from the first dollar.
Here’s the latest email. The top
And the bottom. Note the toll free support number. DO NOT call these people.
Share
DEC







About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com