Phishing Email Alerts
Catch of the Day: QuickBooks Phish
Chef’s Special: Account Verification Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
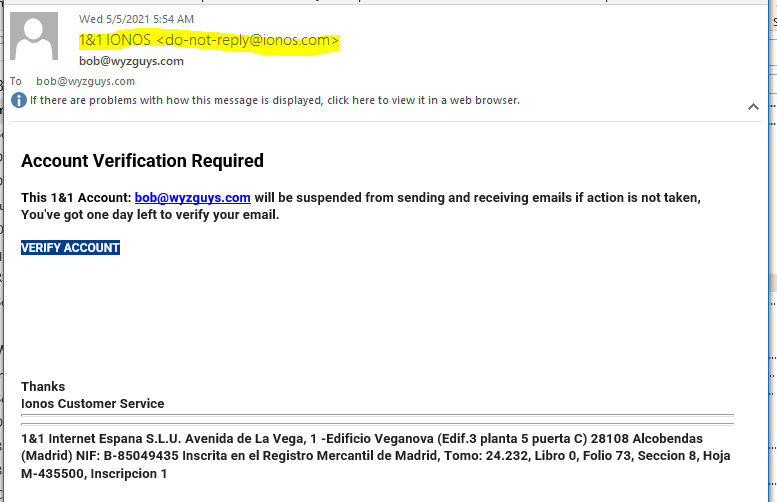
IONOS Account Verification Phish
This email has a nicely spoofed sender email address, and looks like a legitimate IONOS email. Checking the email headers showed that the email originated from an IONOS account, which is bad news. Possibly more than spoofing, this may be an email account hijacking of an actual IONOS account. Here are the mail headers:
Return-Path: <do-not-reply@ionos.com>
Received: from mout-xforward.perfora.net ([82.165.159.134]) by mx.perfora.net
(mxeueus004 [74.208.5.3]) with ESMTPS (Nemesis) id 1MEF45-1loO1m21LR-00AHC2
for <bob@wyzguys.com>; Wed, 05 May 2021 12:53:31 +0200
Received: from ionos.com ([77.68.73.99]) by mrelay.perfora.net (mreueus003
[74.208.5.2]) with ESMTPA (Nemesis) id 0LwsL0-1lTFmE3nom-016M2c for
<bob@wyzguys.com>; Wed, 05 May 2021 12:53:31 +0200
From: 1&1 IONOS <do-not-reply@ionos.com>
To: bob@wyzguys.com
Subject: bob@wyzguys.com
Date: 5 May 2021 10:53:30 +0000
Message-ID: <20210505105330.CD3B3E576F6E5322@ionos.com>
MIME-Version: 1.0
Content-Type: text/html
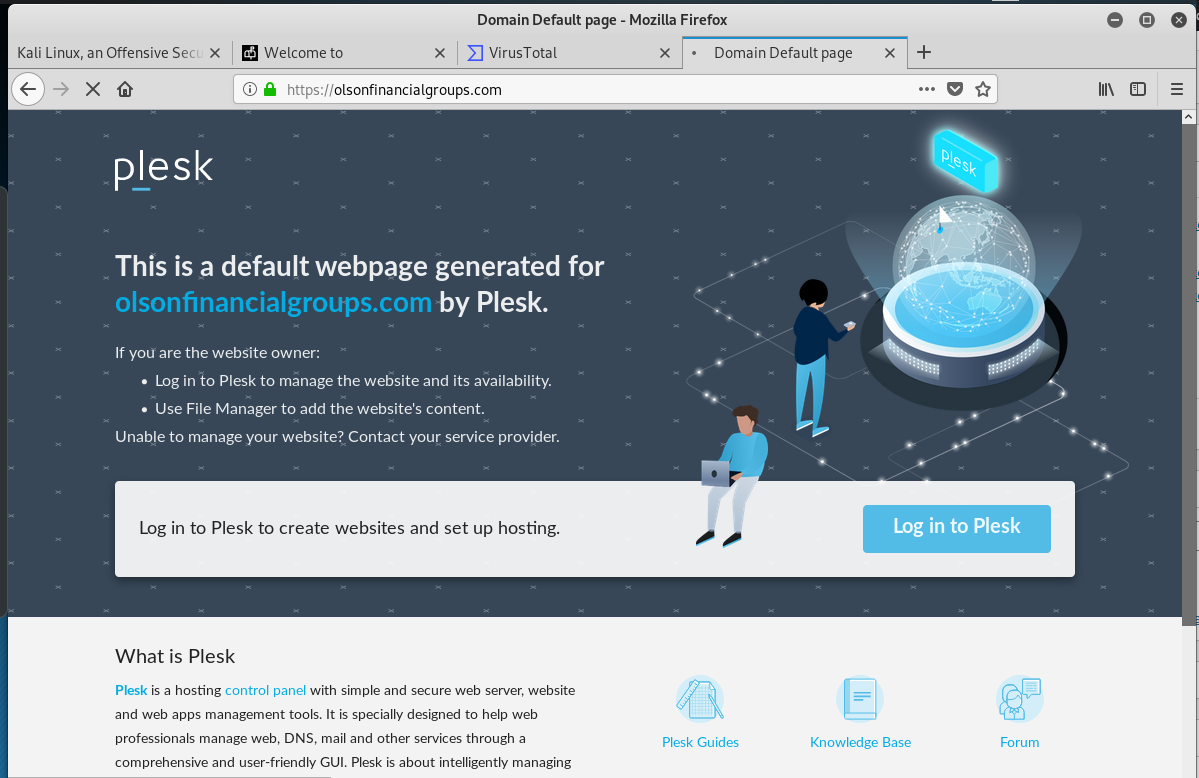
The Verify Account button resolved to https://olsonfinancialgroups.com/2d4b9c49f2c54fb13dc3862767f1d573/45bb4a72961b58e8/?email=bob@wyzguys.com. This appears to be a hijacked domain that has not been developed into a website yet.
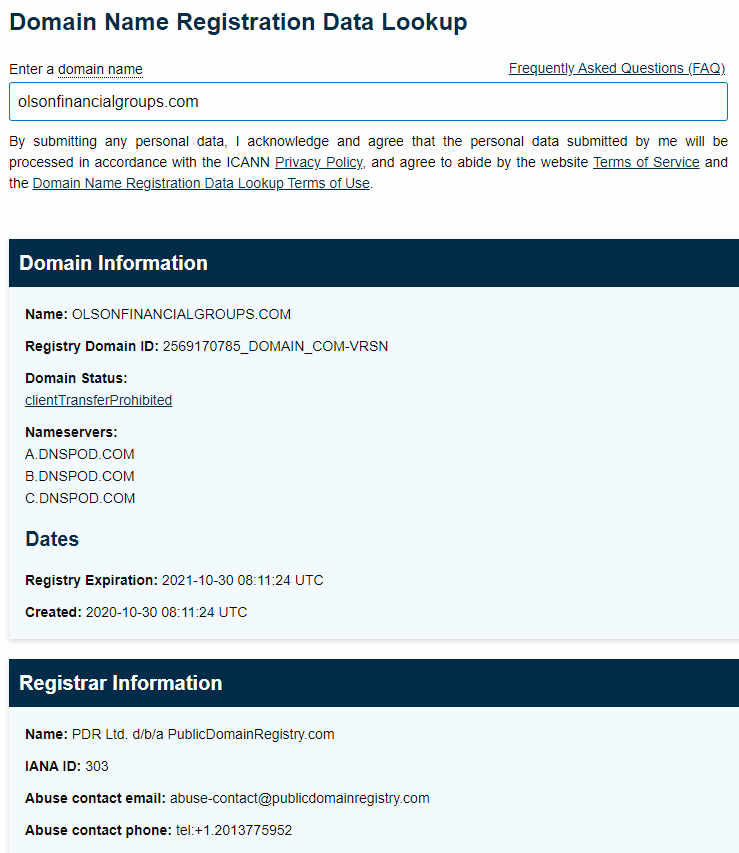
And here is the WHOIS data about this domain
The first landing page is a simple credential stealing web form.
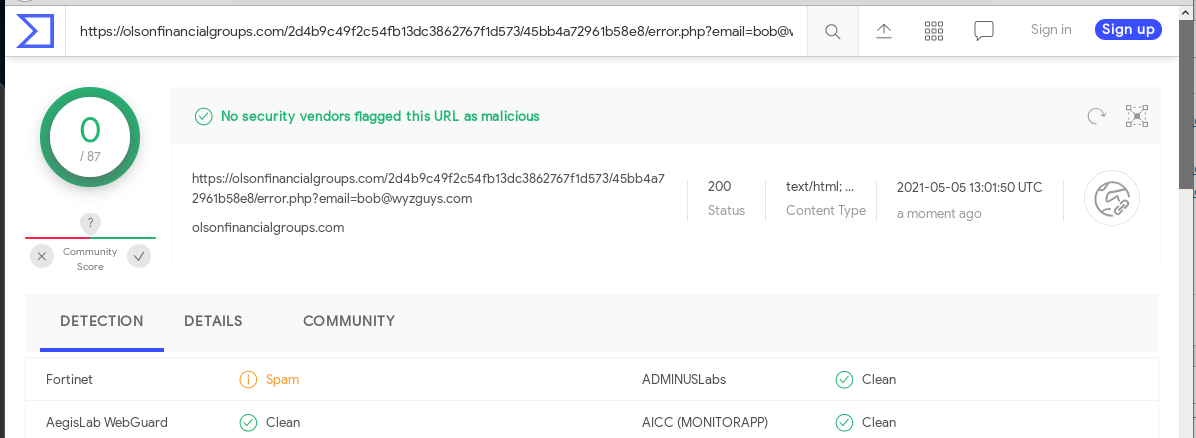
A quick look at VirusTotal showed only Fortinet had flagged this URL.
This example illustrates the importance of going beyond the email sender when verifying an email. The sender address looks real, but the URL on the button was definitely not legitimate.
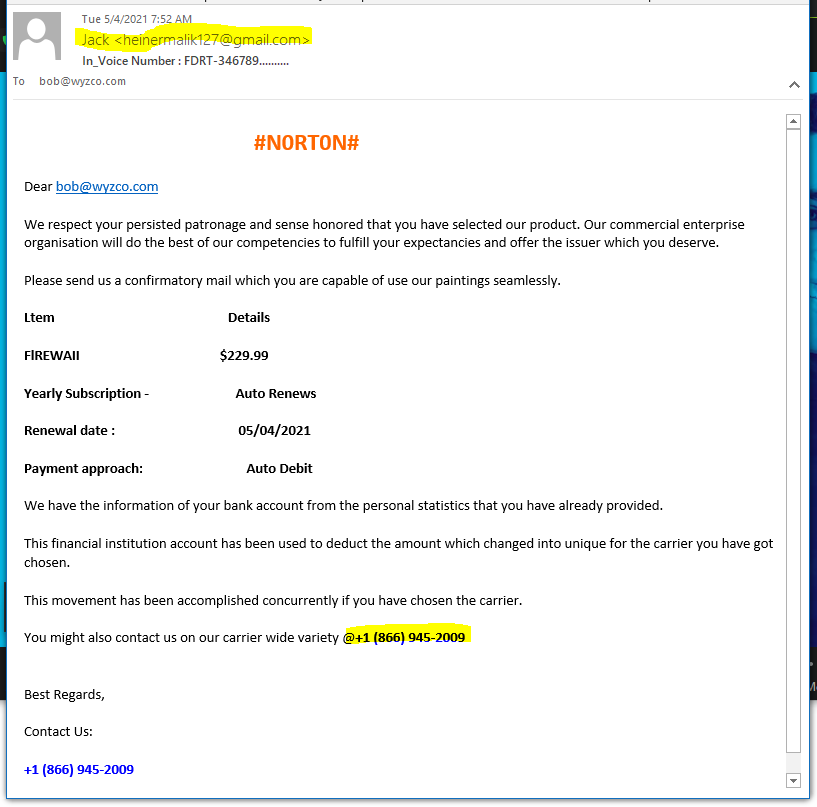
Another Norton Renewal Phish
Again, just disregard emails like this one. Calling the toll-free number will just get you connected with a con artist.
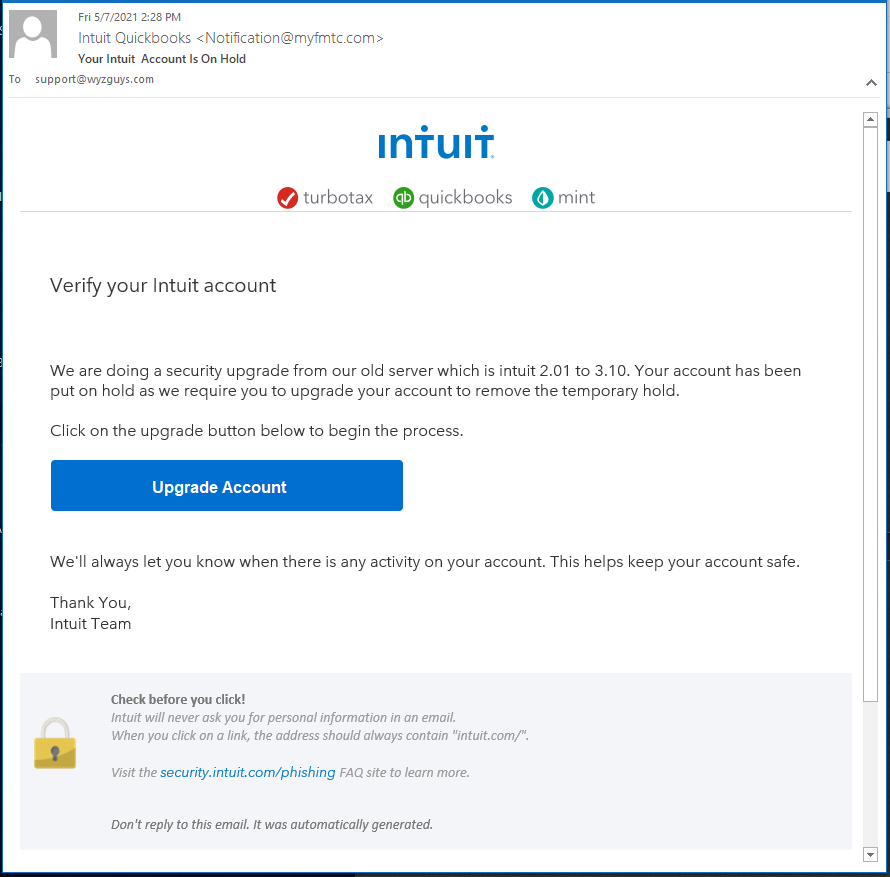
QuickBooks Phish
Here is a QuickBooks/Intuit phish. There are a couple of nice flourishes. First, the sender email, while not exactly frim Intuit, looks like it might be one of those commonplace marketing or support special-purpose domains. Second, there is a PHISHING WARNING at the bottom of the email. Nice touch!
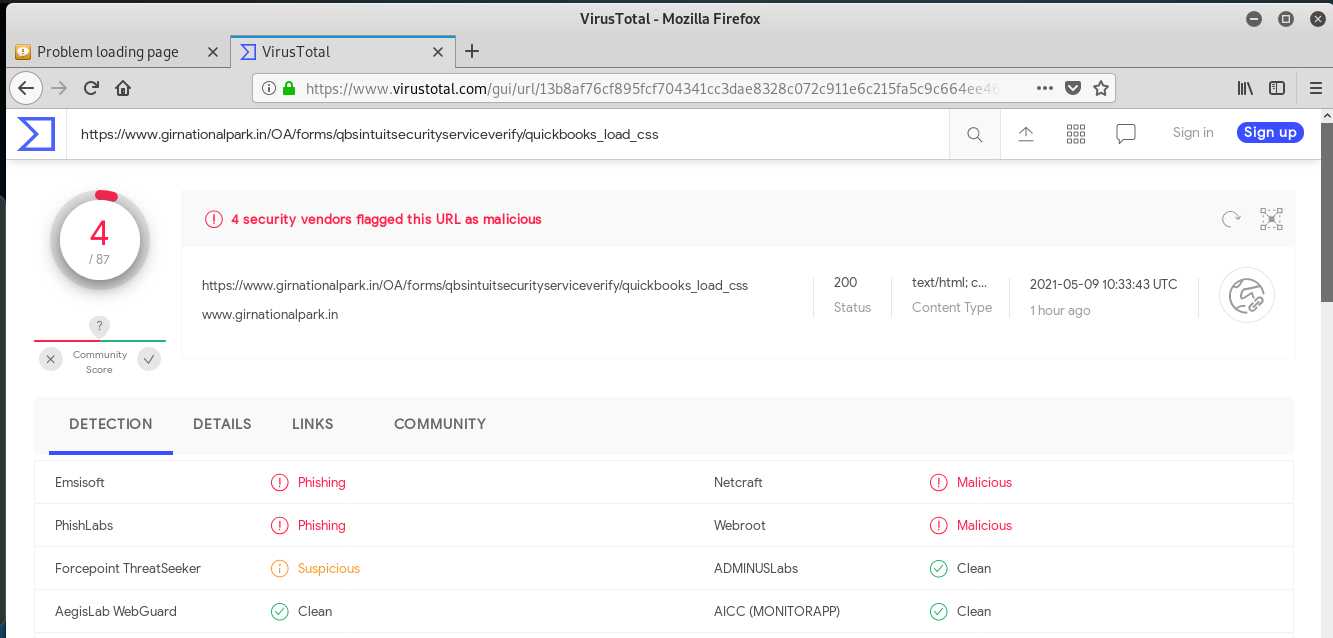
The Upgrade Account button link resolves to https://s.id/AmKxa which is redirected to https://www.girnationalpark.in/OA/forms/qbsintuitsecurityserviceverify/quickbooks_load_css. This is a website for an Indian national park. At the time of my research, the entire site was doen. Nevertheless, VirusTotal was able to identify the link as malicious.
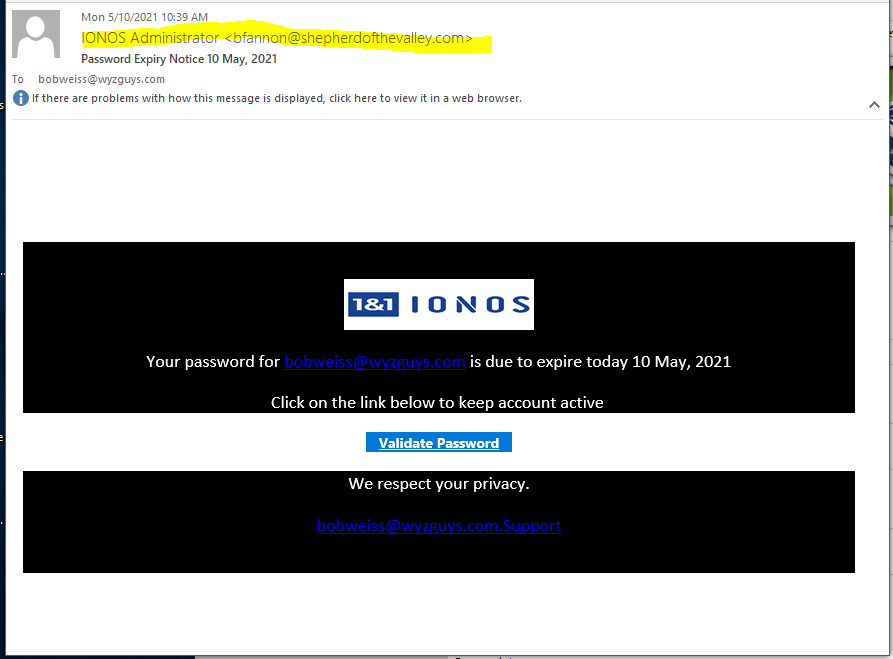
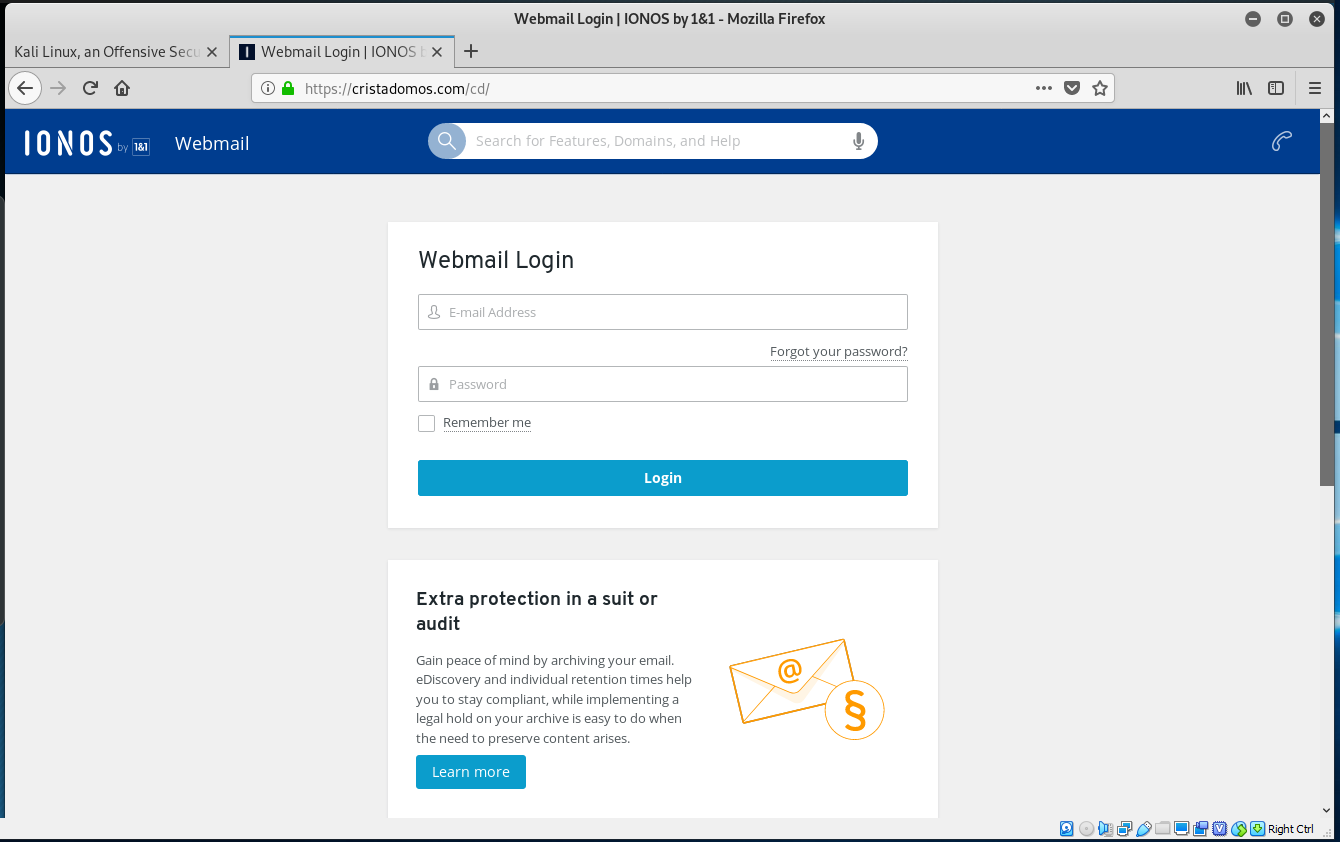
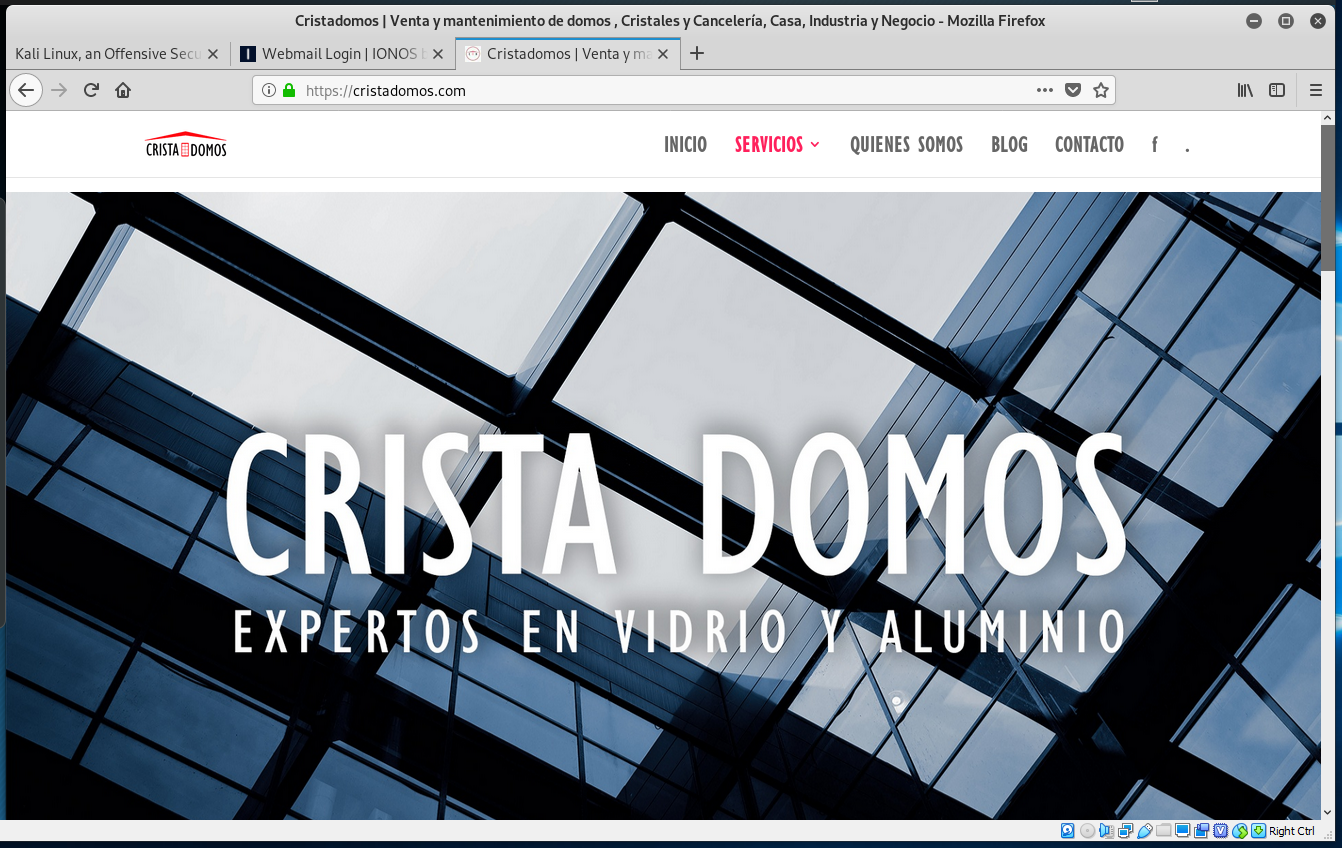
IONOS Password Phish
This crappy looking email showed up in my inbox today. Could you at least try to create something convincing? Button resolved to https://cristadomos.com/cd/, which is a legitimate by hijacked website. Email, landing page, and hijacked home page follow.
Share
MAY






About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com