 Phishing Email Alerts
Phishing Email Alerts
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox.
Fake Hosting Account Support Phish
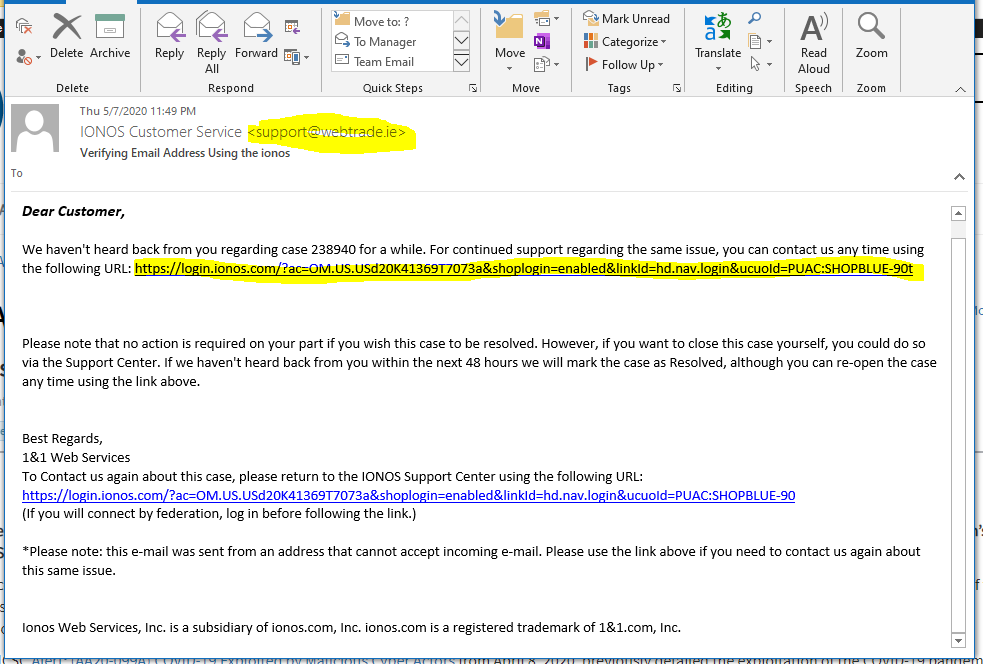
This is a longer look at a phishing email, with a look at the fake login landing page, and the home page of the compromised site hosting the landing page. First, the email. Notice the webtrade<dot>ie sender address. The link resolves to http://resten<dot>net/1and1/
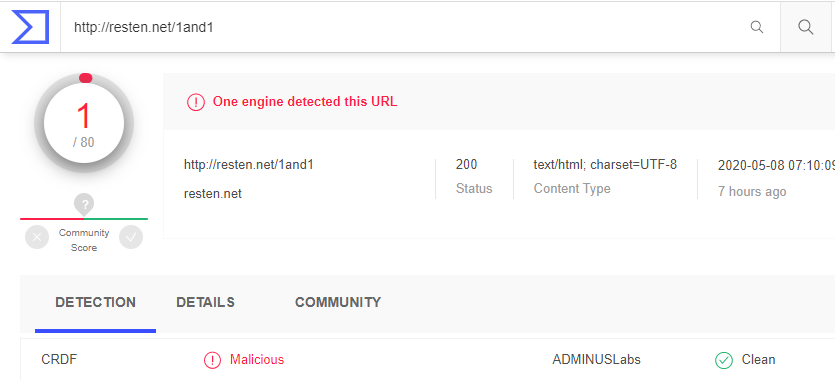
Running this destination through Virustotal shows this site is malicious.
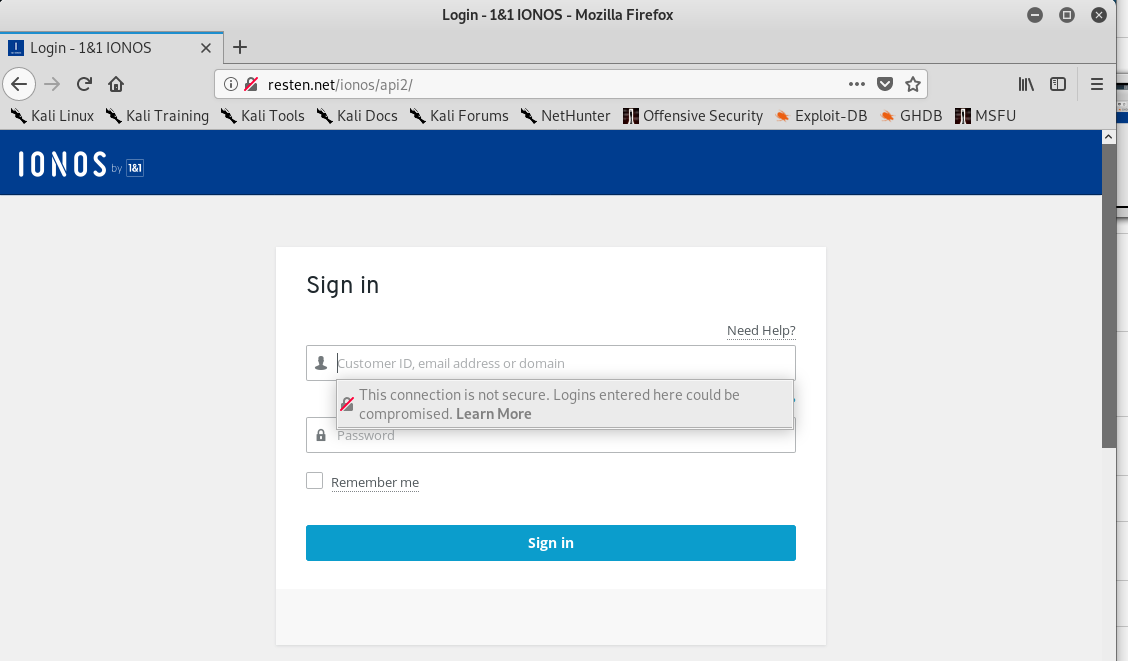
Opening Kali Linux in a virtual machine, we click through to the landing page, which is a reasonable facsimile of an IONOS login page. When I attempted to enter fake credentials, this warning box popped up.
After entering the “credentials” I was transported to a genuine IONOS page, as you can see from the address bar.
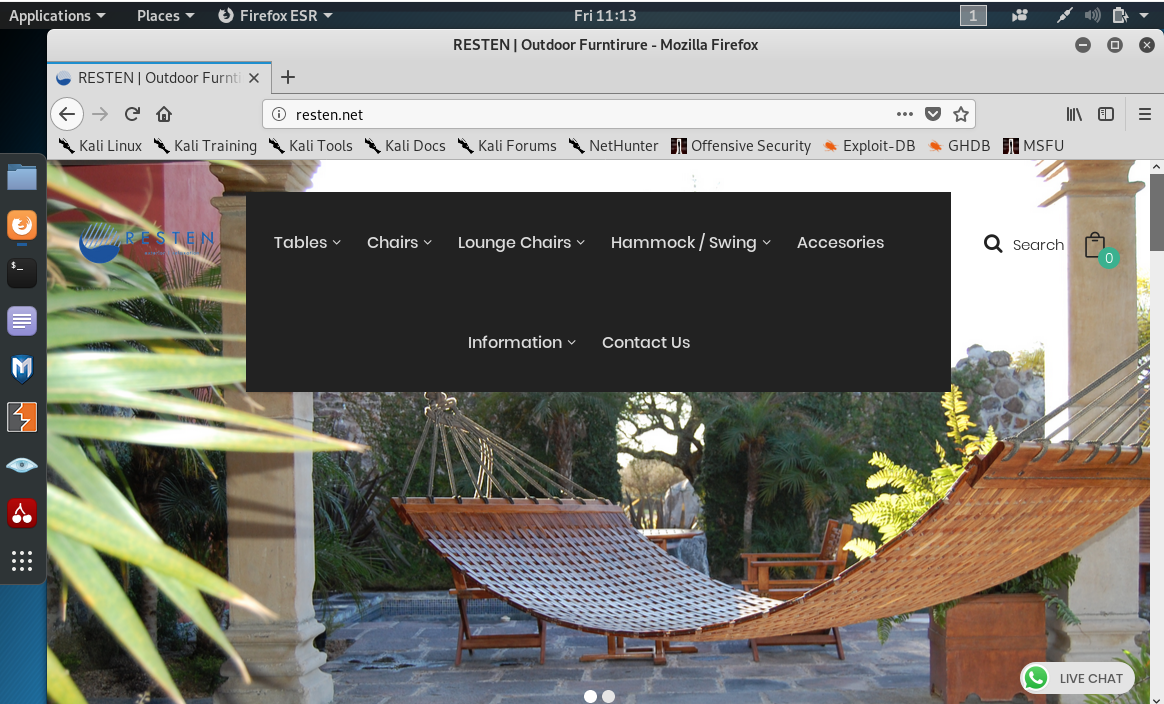
And this is the home page of the unfortunate victim of a web site hijacking that is being used by the attacker in this scam. As we can see, this is an outdoor furniture company website running on WordPress.
This is how a credential stealing phishing scam works. Had I given the attacker my real login credentials, they would be able to take over my website, too.
Phishing emails caught exploiting DocuSign and COVID-19
A new attack discovered by Abnormal Security aims to steal account credentials from people who use the online document signing platform. Follow link to read full story on Tech Republic
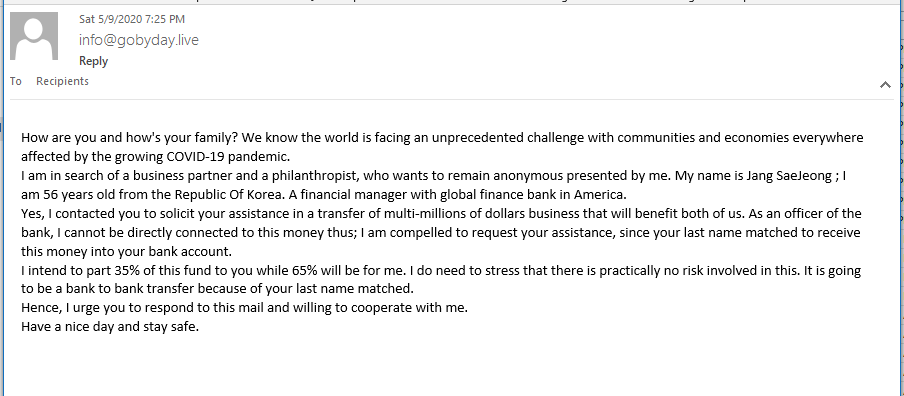
An Update to the Good Old Nigerian Prince Scam
This phish does not have much in the way of tricks, just a straight up advance-fee scam.
How Bad Guys Deceive High-Rank Executives to Give Them Access to Your Office 365 accounts: PerSwaysion
Researchers at Group-IB have discovered a sophisticated spearphishing campaign that’s targeted executives at more than 150 companies around the world since mid-2019. The researchers have named the campaign “PerSwaysion” because the attackers abused the Microsoft Sway presentation program. The attackers seem particularly adept at using social engineering against multiple employees as part of the same attack.
Beware the DHL delivery message email – it could be a package scam
From Sophos Naked Security Blog.
Incoming Package Notification!
This it to notify you that you have an incoming shipment registered in your email [REDACTED]. Please follow the URL below to track your shipment.
And that’s all there is to the email.
OK, so the exclamation point after the word “Notification” probably wouldn’t be there in a genuine notification – it’s a notification, after all, not a warning or an alert.
More importantly, however, hovering over the link wouldn’t show you a website name you’ve never heard of (this scam used a hacked webserver belonging to a construction company in Bahrain, as it happens).
If you click through just to see what this is all about, you’ll see a similarly simple web page:
As unexpectionable and as unscammy as the page itself looks, the address bar is a fortunate giveaway that this is a scam.
The URL (which we’ve masked out here) wasn’t on a lookalike or soundalike domain name, so it looked completely different to any website you might expect for a DHL server.
Also, there’s no padlock, because the URL started with http:// (insecure) rather than https:// (session encrypted).
Share
MAY








About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com