Phishing Email Alerts
Catch of the Day: OneDrive Phishing
Chef’s Special: SanLam Finance Spam
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
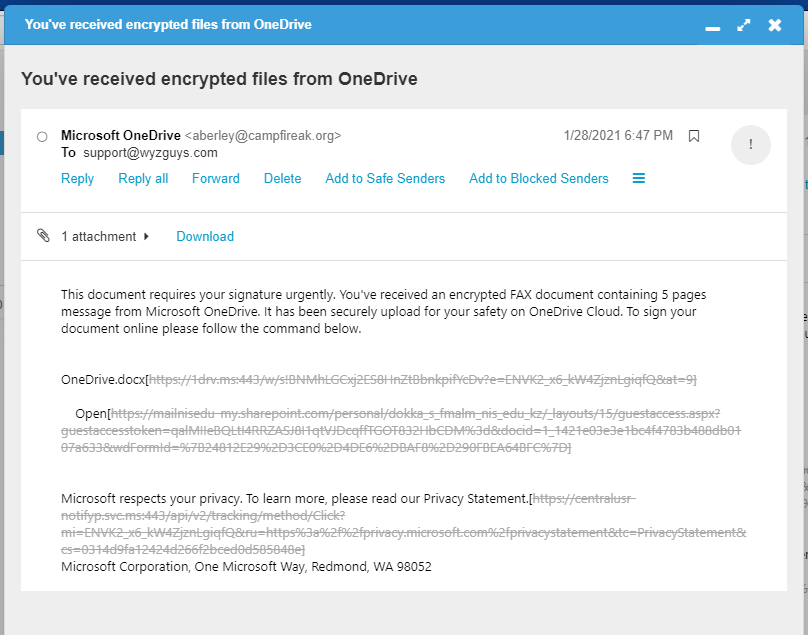
OneDrive Phishing
Either my email filtering services have improved (possible) or the professional phishers have removed me from their email list (possible), but I am not getting the quantity of phishing emails that I used to get in my inbox. This one I dragged out of the SPAM filter provided by my host. Links were all disabled by the spam filter, so I have to look at the source code to get what I show here. This still gives you a good idea of how this exploit looks, with an eye to avoiding it yourself.
This is the source code including the mail header.
Return-Path: <aberley@campfireak.org>
Received: from [74.208.5.3] ([74.208.5.3]) by mx.perfora.net (mxeueus003
[74.208.5.3]) with ESMTP (Nemesis) id 1N9cwj-1m1PVM2nLh-015db3 for
<bobweiss@wyzguys.com>; Fri, 29 Jan 2021 00:47:46 +0100
Received: from campfireak.org ([70.113.225.10]) by mx.perfora.net (mxeueus003
[74.208.5.3]) with ESMTP (Nemesis) id 1M9F4F-1l1A9O2ktT-006Lxn for
<support@wyzguys.com>; Fri, 29 Jan 2021 00:47:45 +0100
From: Microsoft OneDrive<aberley@campfireak.org>
To: support@wyzguys.com
Subject: You’ve received encrypted files from OneDrive
Date: 29 Jan 2021 07:47:45 +0800
Message-ID: <20210129074745.CD11FCDB0BD5728C@campfireak.org>
<span dir=3D”ltr”>This documen=
t requires your signature urgently. You've received an encrypted FAX d=
ocument containing 5 pages message from Microsoft OneDrive. It has been sec=
urely upload for your safety on OneDrive Cloud. To sign your document onlin=
e please follow the command below.</span></td>
” href=3D”https://mailnisedu-my=
=2Esharepoint.com/personal/dokka_s_fmalm_nis_edu_kz/_layouts/15/guestaccess=
=2Easpx?guestaccesstoken=3DqalMIIeBQLtI4RRZASJ8I1qtVJDcqffTGOT832HbCDM%3d&d=
ocid=3D1_1421e03e3e1bc4f4783b488db0107a633&wdFormId=3D%7B24812E29%2D3CE0%2D=
4DE6%2DBAF8%2D290FBEA64BFC%7D”
Microsoft respects your privacy. To learn more, please read our=
<a data-auth=3D”NotApplicable” href=3D”https://centralusr-notifyp.svc.ms:4=
43/api/v2/tracking/method/Click?mi=3DENVK2_x6_kW4ZjznLgiqfQ&ru=3Dhttps%3a%2=
f%2fprivacy.microsoft.com%2fprivacystatement&tc=3DPrivacyStatement&cs=3D031=
4d9fa12424d266f2bced0d585848e”
The links did not work for me, so I moved on to the HMTL attachment. This is what I found.
Basically, this looks like a OneDrive credential harvesting exploit. The import consideration is that this exploit captures your Microsoft ID, which may be used for your Office365 subscription, Outlook.com and Exchange Online based email account, and even your computer login, so this would be a significant lost of security.
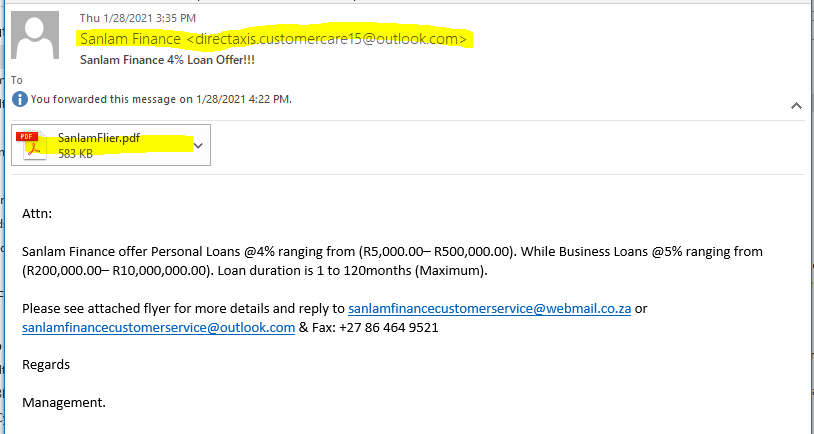
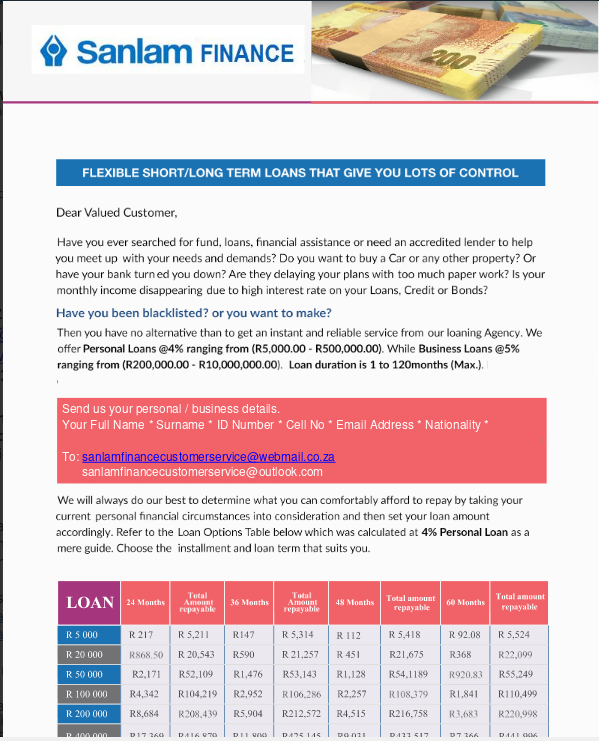
Sanlam Finance – Phish or Spam
This email looked phishy, but turned out too be spammy.
I tested the PDF attachment at VirusTotal, and it was not flagged as malicious. Not proof of safety, but a good indication that this is simply a money lending scheme, undoubtedly at ridiculously high interest rates. No links to dodgy web pages. So this is more likely a Spam exploit than a Phish.
And here is the PDF document,
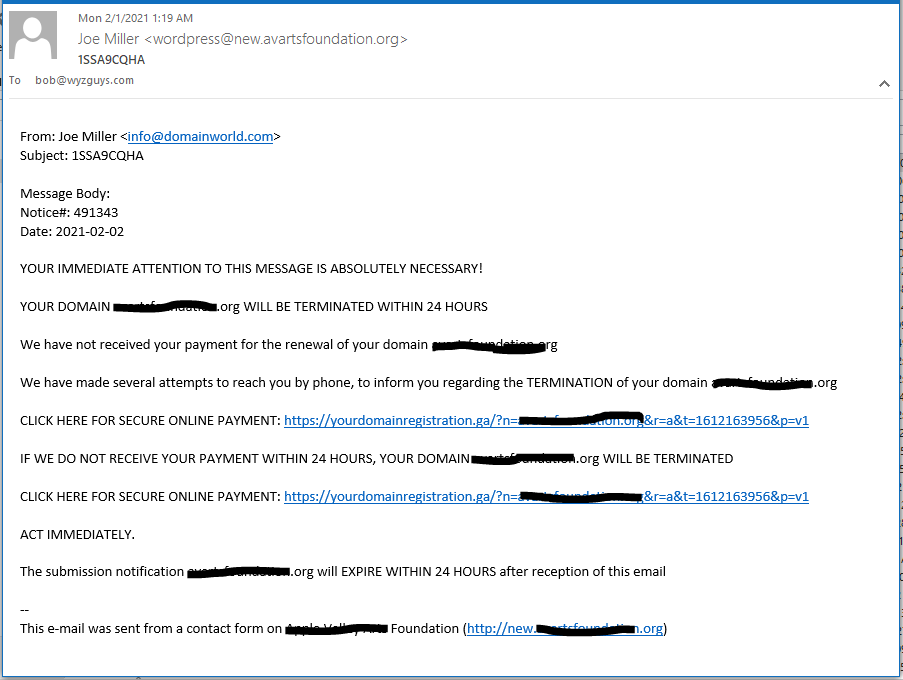
Domain Renewal Scam Form Phish
This exploit sends the phishing email by using the contact form from the victim’s own website. The email claims that your domain name registration is about to expire. The links resolve to a landing page where you can “renew” your domain name registration. Unfortunately your domain will NOT be renewed, and you will be out-of-pocket for the amount of the plan you select.
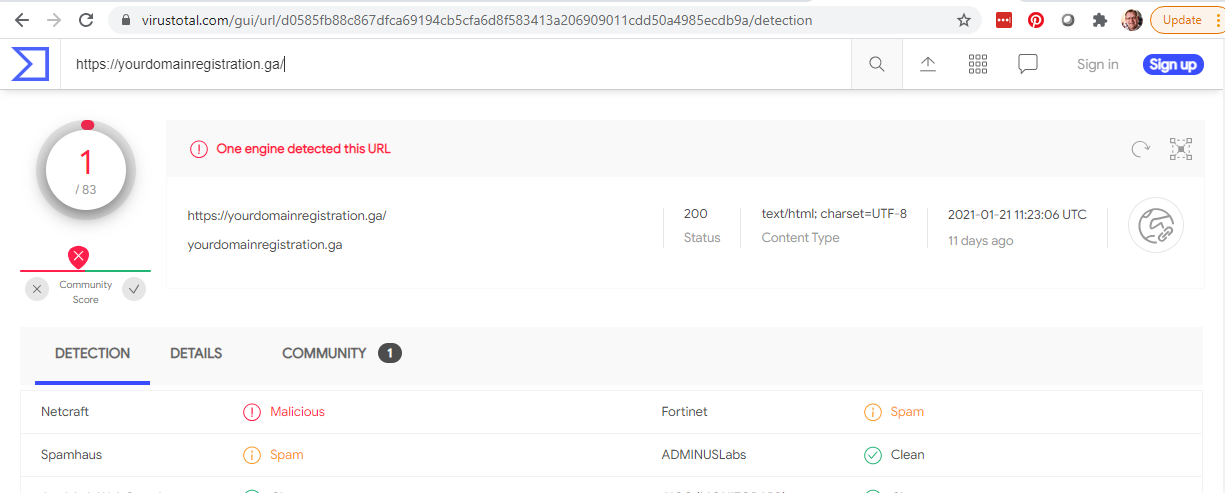
The link domain ga is the top-level-domain assigned to the African country of Gabon, Your domain name registrar is unlikely to be headquartered there. https://yourdomainregistration.ga/?n=yourfoundation.org&r=a&t=1612163956&p=v1
Virustotal reported this site.
Emotet malware taken down by global law enforcement effort
The infamous botnet has been disrupted thanks to an international effort across the US, Canada, and several European nations.
Emotet typically found its way to computers through infected files sent via email. In these cases, the email messages came with malicious Microsoft Word documents either attached to the message or available for download via a link. After opening such a document, the recipient is asked to enable macros so that the malicious code in the file could activate and install Emotet on the computer.
Share
FEB








About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com