 Phishing Email Alerts
Phishing Email Alerts
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox.
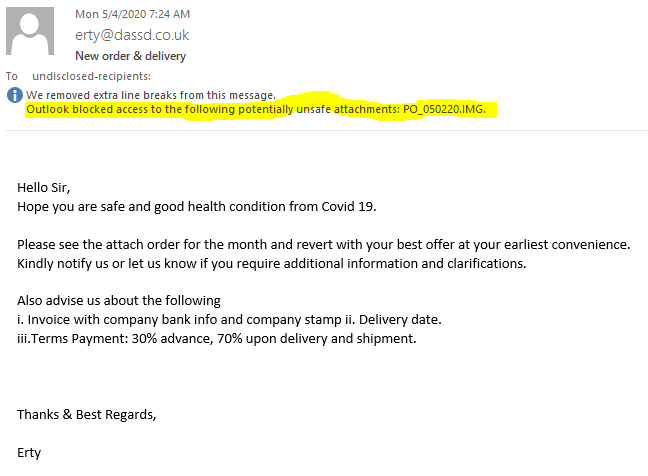
Fake Purchase Order Phish
Nobody is buying anything unless you open the attachment. Then you are buying a heap of trouble. Outlook blocked the attachment, which is your clue this email is bogus. And why I like using Outlook.
The attachment is an image file, with embedded malware. Opening the attachment would infect your computer.
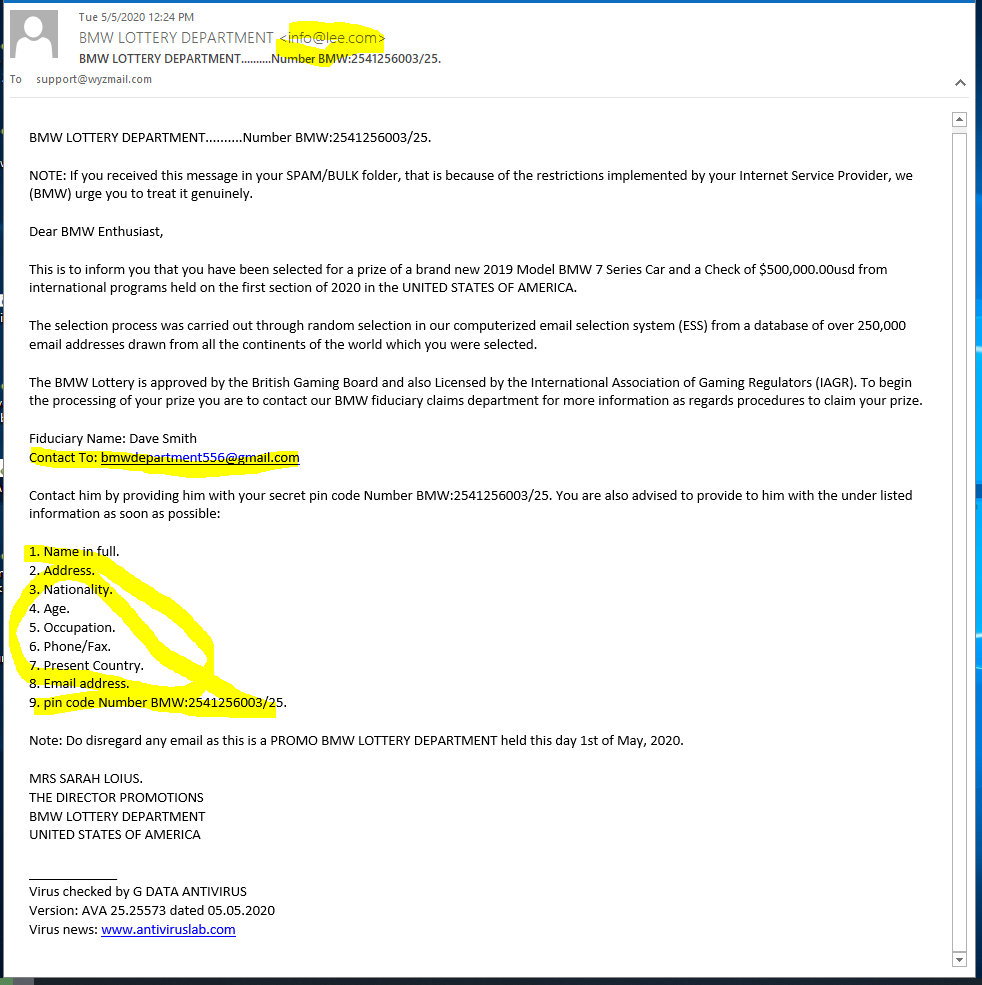
I Won a BMW Lottery! Not!!
Here;s a typical Lottery Scam Phish. First is the sending email info<at>lee.com. This is unlikely to be the email domain of either BMW or a marketing company that is handling the lottery. The “fiduciary” Dave Smith is using a GMail account bmwdepartment556<at>gmail,com. This too is unlikely.
For some reason, a lottery that has enough information about me to send me an email seems to know nothing else about me, This is a straight information harvesting con. I would expect that the next phase would involve sending some sort of fee or bank account information. The email follows
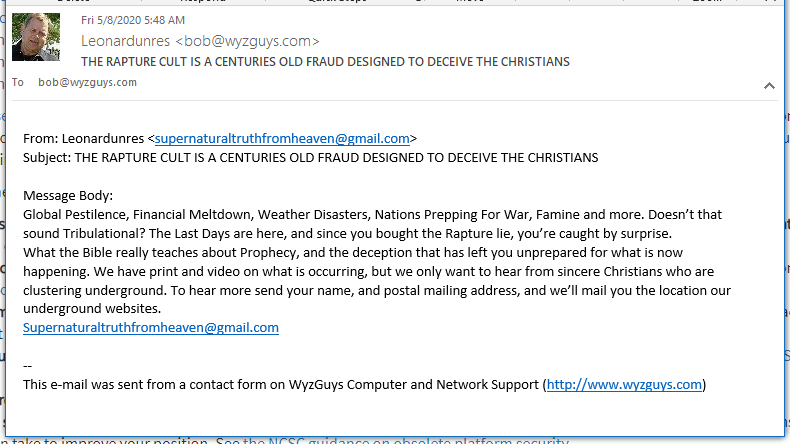
Rapture Fraud Targeting Christians and Religious Preppers
War, Famine, Pestilence, Death. Sounds like the Apocalypse to me too. But this is only the four thousandth time that the End of Days has been declared. I am not religious, or a prepper, so this group has their demographics screwed up, some many of us will see this. Do not fall for this phish or others like it.
Coronavirus-themed malware intensifies across the world
Such threats continued to spread in April and are likely to be the new norm, at least until the pandemic subsides, according to Bitdefender.
[Heads Up] ‘Florentine Banker Group’ Use Microsoft 365 Functionality to Scam Private Equity Firm out of 1.2 Million
A new investigation by Check Point’s Incident Response Team (CPIRT) demonstrates how brazen cybercriminals are and the lengths they will go to in order to see their scam succeed.
Cybercriminals were able to divert well over 1 million dollars in funds from a PE firm back in December, according to a newly released CPIRT report. This business email compromise (BEC) attack involved the targeting of specific firms, a ton of intel gathering, the use of malicious mailbox rules, lookalike domains, impersonation, and either intercepting or starting new wire transfers.
Here’s how the scam works:
- Target the CEO or CFO of a PE firm with malware designed to take over their machine
- Watch the email conversations, looking for opportunities to misdirect wire transfers
- Divert inbound emails related to pending wire transfer transactions to an attacker-used mailbox folder
- Setup a lookalike domain impersonating the PE firm
- Send emails using the lookalike domain impersonating those involved with the wire transfer to the PE firm, taking over the email thread without the PE firm realizing (think cut and paste, including those in the other firm, and using the new domain as the from address. All replies will now no longer involve the other PE firm.)
- Continue to reroute inbound emails from the other firm, isolating any legitimate communications from the other firm
- Commit wire fraud by providing new banking details to an existing (but pending) wire transfer
Additionally, the scammers also looked through countless emails between the compromised mailbox and their bank, identifying contacts at the bank to whom they sent new wire requests.
[Click Alert] So, What Is the Phish-Prone Percentage on Recent Coronavirus Phishing Tests?
I had some numbers run on the usage of our new, dedicated COVID-19 phishing templates to find out what the Phish-prone percentage was, since this is an unprecedented worldwide event. Since these templates were released—note, we warned against this for the first time Jan 31, 2020—here are the numbers. Read more….
COVID-19:
- Delivered: 2,183,318
- Failed: 192,042
- PPP: 8.80%
Share
MAY




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com