Happy New Year!
A new year brings new phish.
Phishing Email Alerts
Catch of the Day: Mailjet Phish
Chef’s Special: Facebook Messenger Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
MailJet Phish
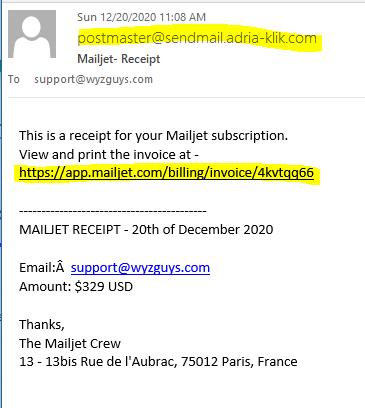
I received this email from MailJet. The sender email address is from the domain sendmail.adria-klik.com. This domain belongs to a Croatian online supermarket. Potentially their Sendmail server has been compromised, and is sending these phishing messages.
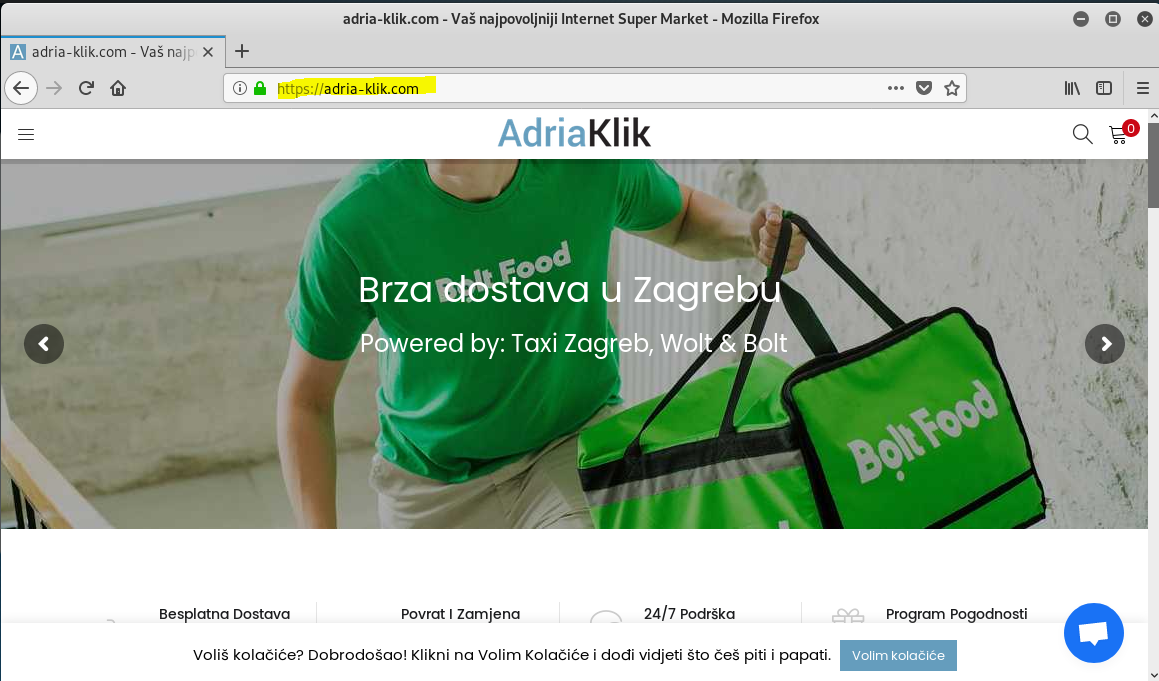
Adria-Klick.com online is a Croatian grocery website. Croatian – Voliš kolačiće? Dobrodošao! Klikni na Volim Kolačiće i dođi vidjeti što češ piti i papati. English – Do you like cookies? Welcome! Click on I love cookies and come see what you will drink and drink.
The email headers showed the origin coming from an Office.com mail server (alpha677.startdedicated.com [85.25.130.76])
Mail headers:
Return-Path: <bounce+21a242.c70da-support=wyzguys.com@sendmail.adria-klik.com>
Received: from [74.208.5.21] ([74.208.5.21]) by mx.perfora.net (mxeueus005
[74.208.5.21]) with ESMTPS (Nemesis) id 1Mrgoy-1kL2z008ZQ-00ni00 for
<bobweiss@wyzguys.com>; Sun, 20 Dec 2020 18:09:38 +0100
Received: from m32-12.eu.mailgun.net ([141.193.32.12]) by mx.perfora.net
(mxeueus005 [74.208.5.21]) with ESMTPS (Nemesis) id 1M1ZI7-1ko1H706Wp-0039dP
for <support@wyzguys.com>; Sun, 20 Dec 2020 18:09:38 +0100
DKIM-Signature: a=rsa-sha256; v=1; c=relaxed/relaxed; d=sendmail.adria-klik.com;
q=dns/txt; s=krs; t=1608484177; h=Content-Type: Message-Id: Date:
Subject: To: From: MIME-Version: Sender;
X-Mailgun-Sending-Ip: 141.193.32.12
X-Mailgun-Sid: WyI3MTczNSIsICJzdXBwb3J0QHd5emd1eXMuY29tIiwgImM3MGRhIl0=
Received: from office.com (alpha677.startdedicated.com [85.25.130.76]) by
smtp-out-n03.prod.eu-central-1.postgun.com with SMTP id
5fdf8504e8c855a794a23c53 (version=TLS1,
cipher=TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA); Sun, 20 Dec 2020 17:08:20 GMT
Sender: postmaster@sendmail.adria-klik.com
MIME-Version: 1.0
From: Mailjet Support <postmaster@sendmail.adria-klik.com>
To: support@wyzguys.com
Subject: Mailjet- Receipt
Date: Sun, 20 Dec 2020 18:08:20 +0100 368692793
Message-Id: <5474196568cd75f5e9be6901e59a98f3.1.D7EA961150935F77@mailjet.com>
Content-Type: text/html
Envelope-To: <bobweiss@wyzguys.com>
X-Spam-Flag: NO
X-UI-Filterresults: notjunk:1;V03:K0:2d0sXFWoRUw=:i4fNNYRTXznfIE0qL822P5IDcd
The Links
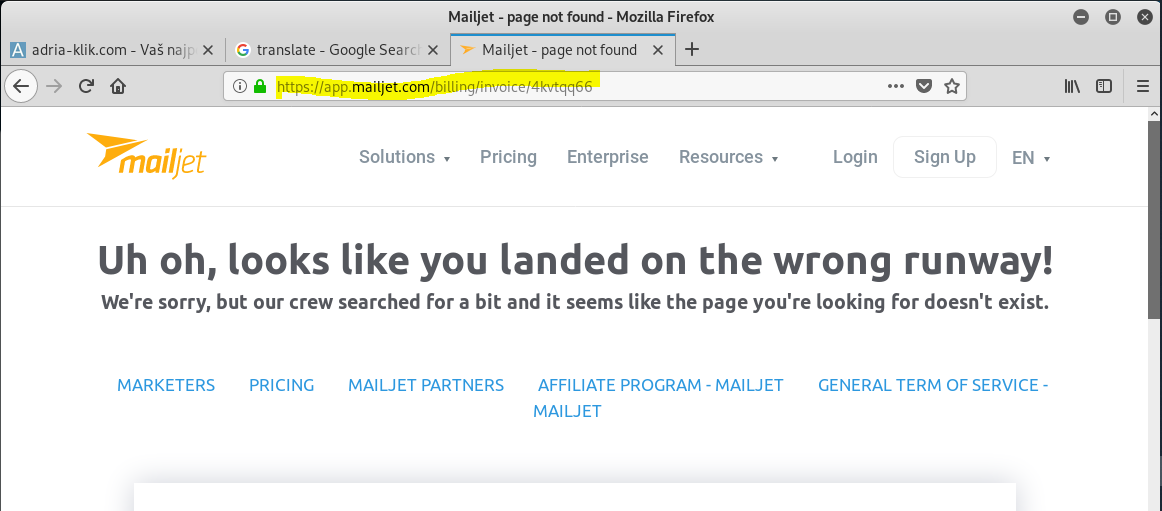
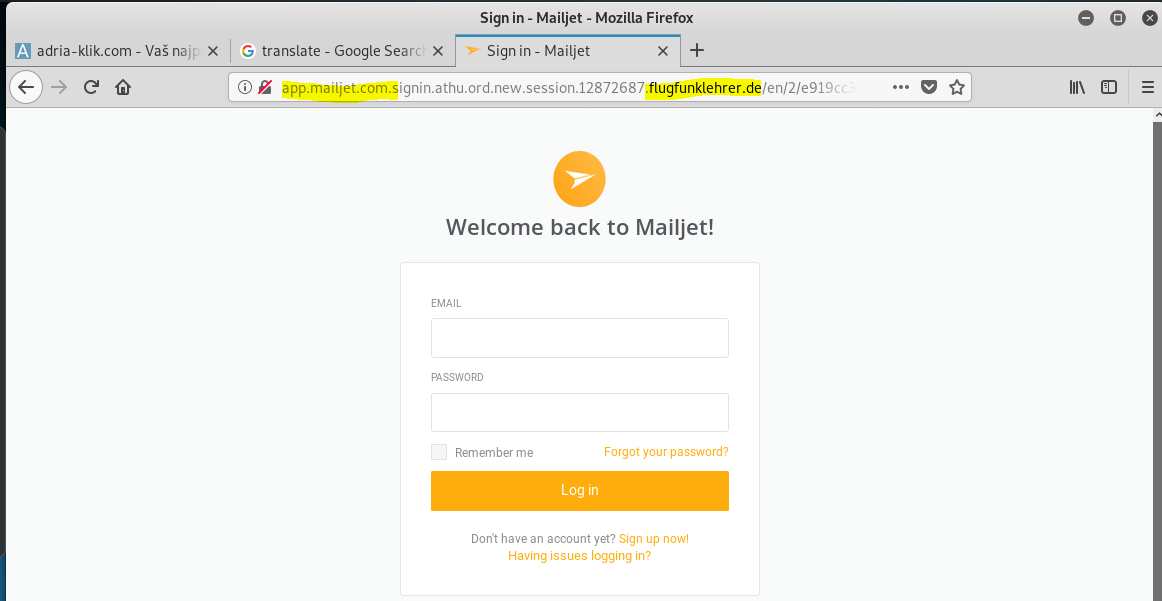
The displayed link https://app.mailjet.com/billing/invoice/4kvtqq66 – goes to 404 page, but actually resolves to: http://app.mailjet.com.signin.athu.ord.new.session.12872684.flugfunklehrer.de/c4ca4238a0b923820dcc509a6f75849b/5aecdccf52282419085f25d1cf101e47/e919cc3f36f13f94bba4b5770aa7a322/ffc5e01f578535fd6f95f889cb31939d
The URL looks legit until you work down through all the sub-domains to the actual primary domain flugfunklehrer.de which translates to radio instructor. The hijacked website is for a German flight school.
Finally, here is the landing page that is hidden on the hijacked website of the flight school. This is a basic credential stealing exploit.
What’s interesting is all the different moving parts – hijacked email accounts or email servers, one and possibly two highjacked web sites. Its a lot of work to go through just to collect a set of user credentials.
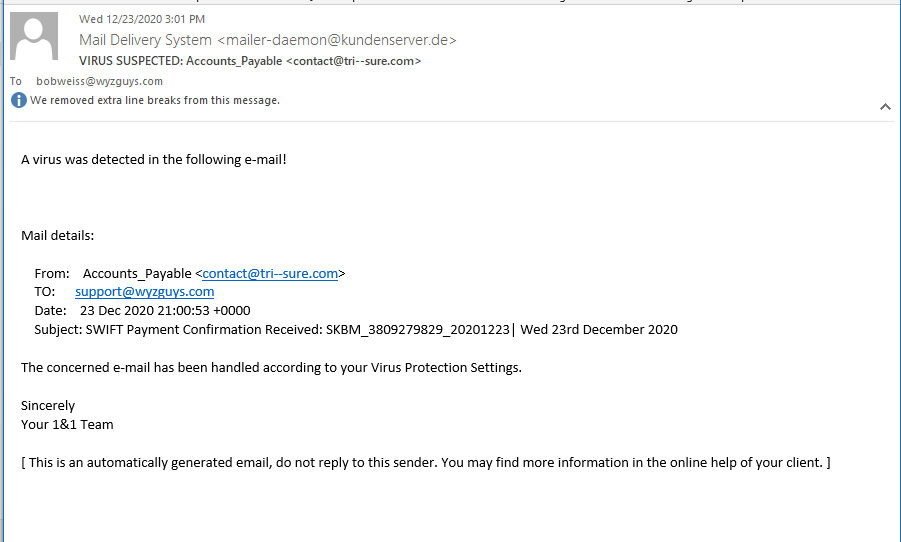
Virus Suspected Alert
This was an alert from my email host. It’s nice when your email service provider can catch a few for you, like this one. It is still possible to see the scammy parts of this message.
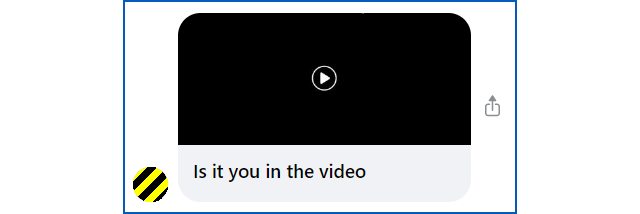
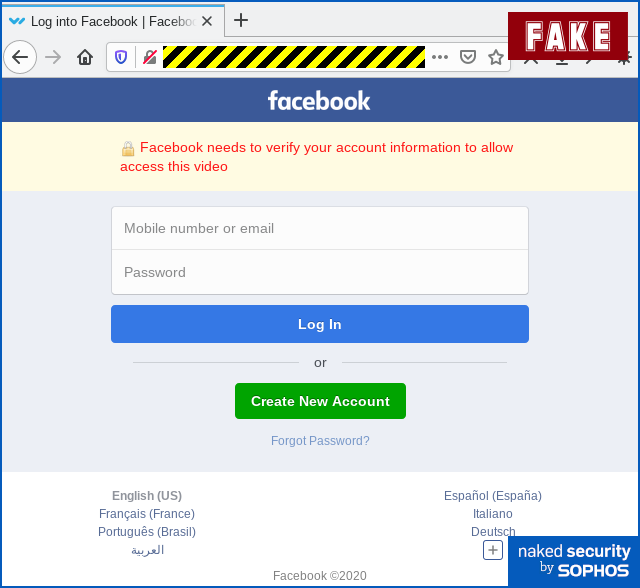
Facebook Messenger Phish
This example is from Sophos Naked Security blog. If you get a message like this from a friend, beware – it means their account was hijacked.
Clicking on the video will take you to a fake Facebook login page, and if you fill it out, your account will be hijacked too. To see the full exploit with a longer explanation, read the original article on Sophos Naked Security blog.
Share
JAN







About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com