 Phishing Email Alerts
Phishing Email Alerts
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox.
Warning! Fake Zoom “HR meeting” emails phish for your password
You are not being fired or laid off! Scammers have turned to employment worries as their latest lure for Zoom phishing scams.
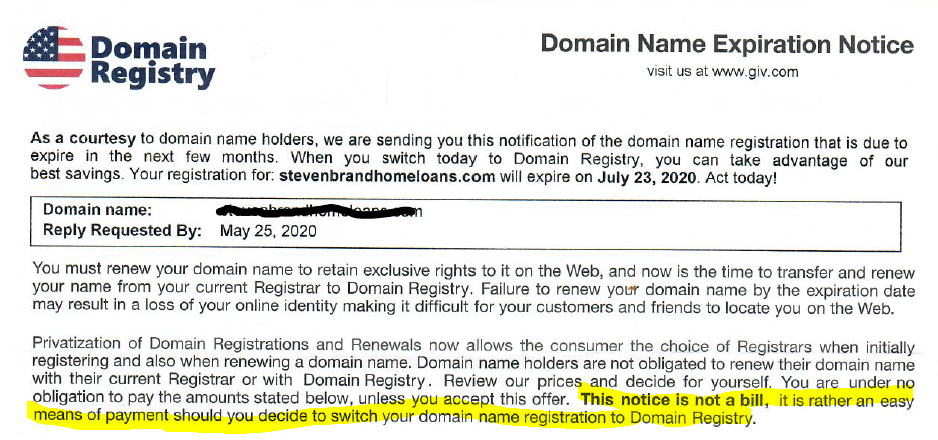
Domain Name Registration Scam
Unfortunately, these solicitations are NOT illegal. This si simply a kind reminder of the annual renewal for your domain name. If you accept their offer, your domain name registration will be transferred from GoDaddy or whoever, to Domain Registry in this case. Usually your email accounts and website stop functioning when those are left behind with the original registrar. It can take up to a week to a month to figure out what happened and transfer you domain back and get your website and email working again. Just ignore these offers.
Credentials for WHO, CDC, NIH, Gates Foundation Dumped on Dark Web
Note from Bob: This breach means that email account hijacking can be easily done, and bad actors can take over legitimate email accounts. Emails arriving from valid WHO, CDC, and similar organization’s accounts may be spoofed or malicious. Suspect any emails from these groups. The World Health Organization is in the middle of responding to a global pandemic. It is COVID-19 chaos. Lives are at stake. Suddenly, out of nowhere, hackers publish more than 2,000 usernames and passwords for those who are part of the WHO, giving anyone with these credentials access to WHO servers and employee email inboxes. And then comes a plot twist you didn’t see coming: white supremacist and extremist groups are sharing the login credentials with glee, encouraging their members to use them to uncover “the truth” about the coronavirus. This plot is reality according to SITE Intelligence Group, an NGO that tracks online activity… Read more
Its Not All Email – Beware Phone Calls Too (Vishing)
When in Doubt: Hang Up, Look Up, & Call Back
Many security-conscious people probably think they’d never fall for a phone-based phishing scam. But if your response to such a scam involves anything other than hanging up and calling back the entity that claims to be calling, you may be in for a rude awakening. Here’s how one security and tech-savvy reader got taken for more than $10,000 in an elaborate, weeks-long ruse. Today’s lesson in how not to get scammed comes from “Mitch,” the pseudonym I picked for a reader in California who shared his harrowing tale on condition of anonymity. Mitch is a veteran of the tech industry — having worked in security for several years at a fairly major cloud-based service — so he’s understandably embarrassed that he got taken in by this confidence scheme. Read more…
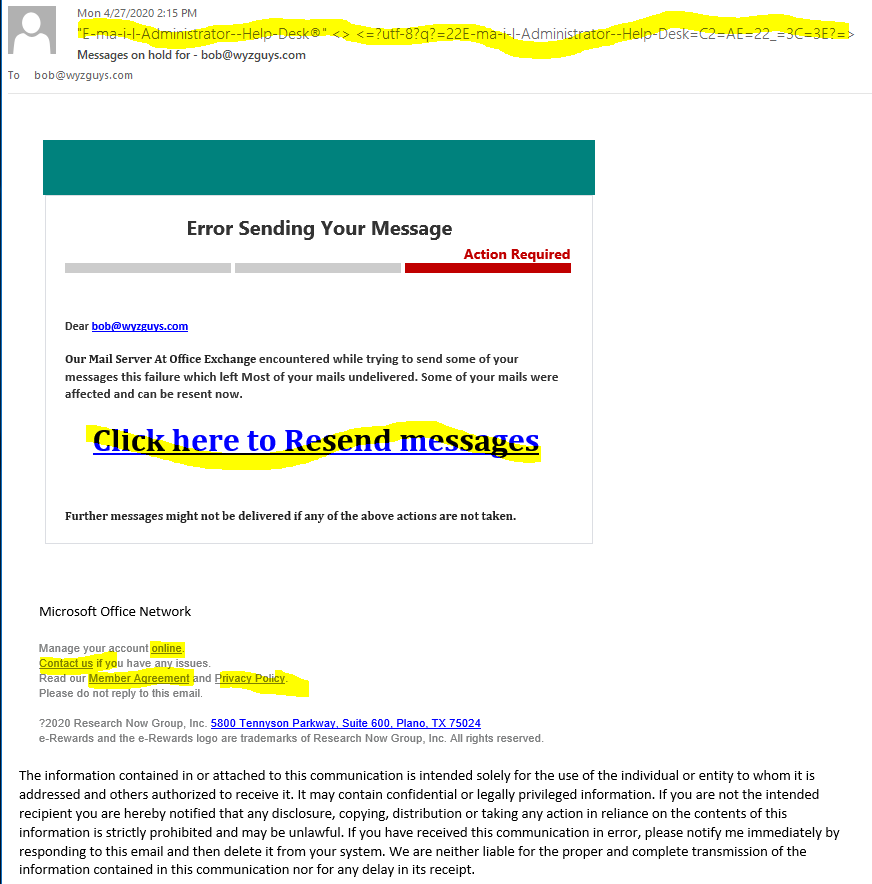
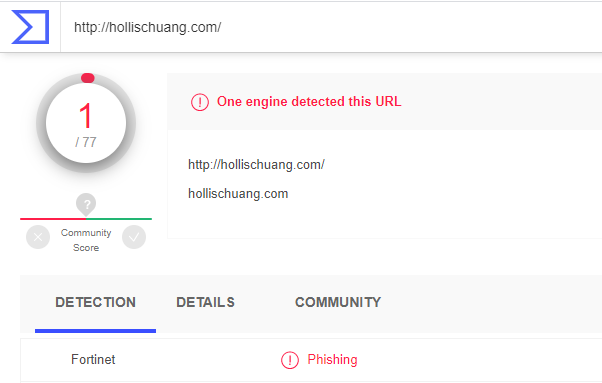
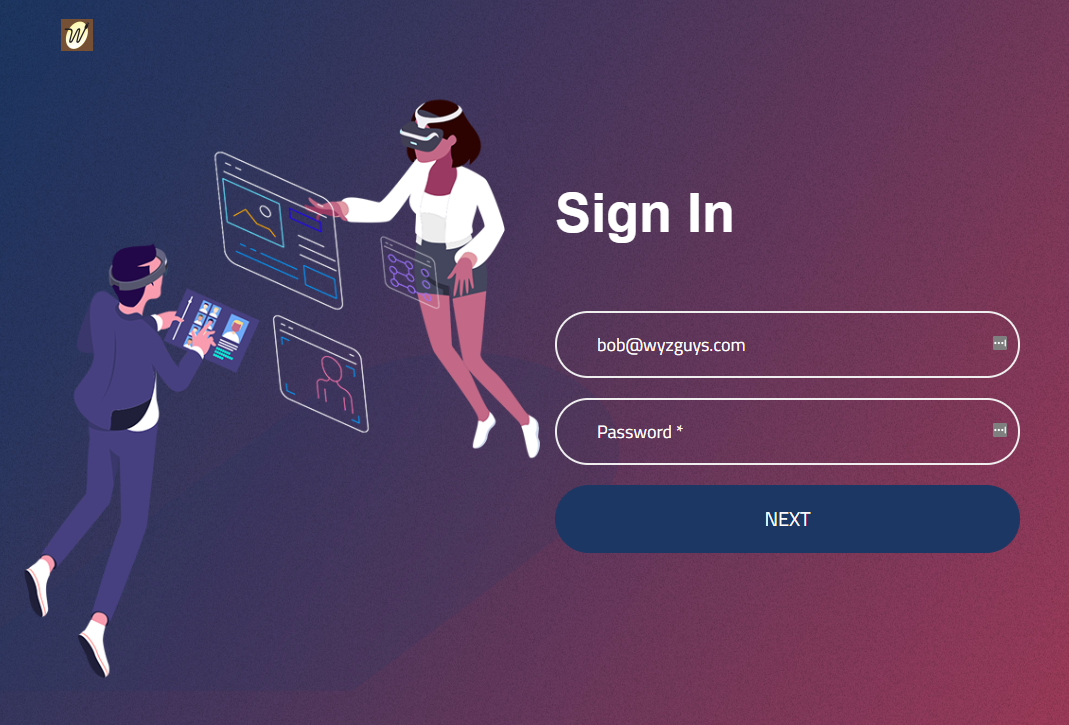
Email Error Scam – Click Here to Resend
Things to notice about this phish: 1) Strange email address of the sender. 2) the link Click here to resend messages resolves to https://www.hollischuang.com/wp-directing/?email=bob@wyzguys.com, which is listed as a phishing link on VirusTotal. the domain hollischuang.com did not have a website associated with it. 3) The links below Microsoft Office Network resolve to http://www.e-rewards.com. 4) Clicking through the Resend link brought me to https://cadenasmuscularesgds.com/wp-content/themes/bravio/languages/image a sign-in page where I was asked to give up my password. See the email and the landing page below. Nice touch – my logo appears in the upper left-hand corner. The third image is the actual home page of the website that has been hijacked in order to host the landing page.This is a scam.
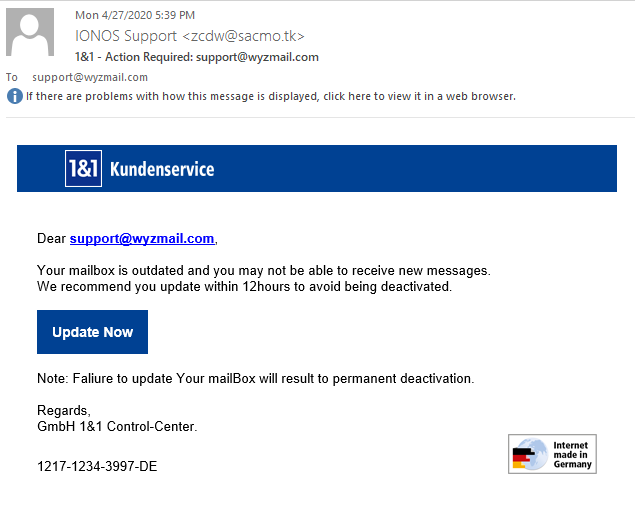
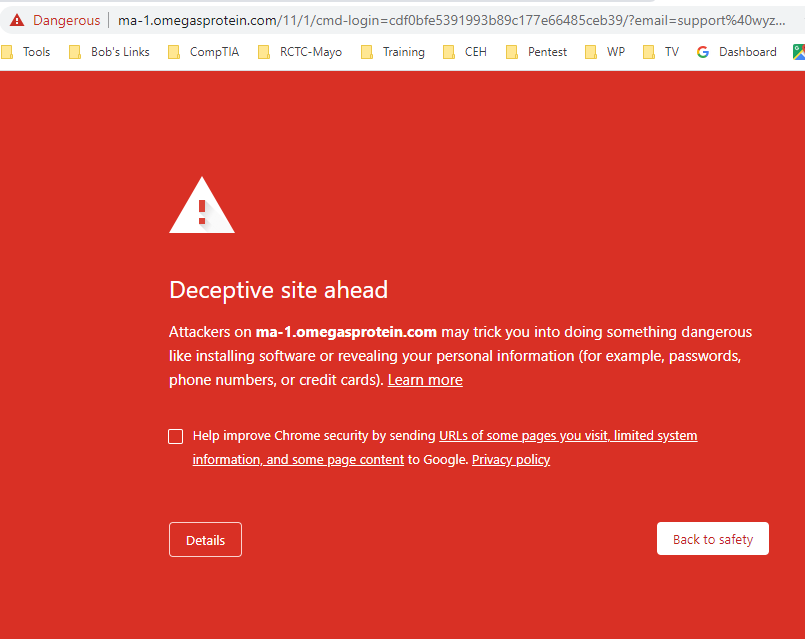
1&1 IONOS email account phish
I received this email that appears to be from 1&1, the hosting company I use for my websites and email services. Lets look for the indications of fraud in this email. The sender address is IONOS Supportzcdw@sacmo.tk, and this is a Turkish email domain. The email should be from support@ionos.com or something like that. The Update Now button resolves to https://ma-1.gerberliesure.com/.mg/.kg/register. Trying the link redirected me to ma-1.omegaprotein.com, and the following Google Chrome alert page. This is clearly a phishing email.
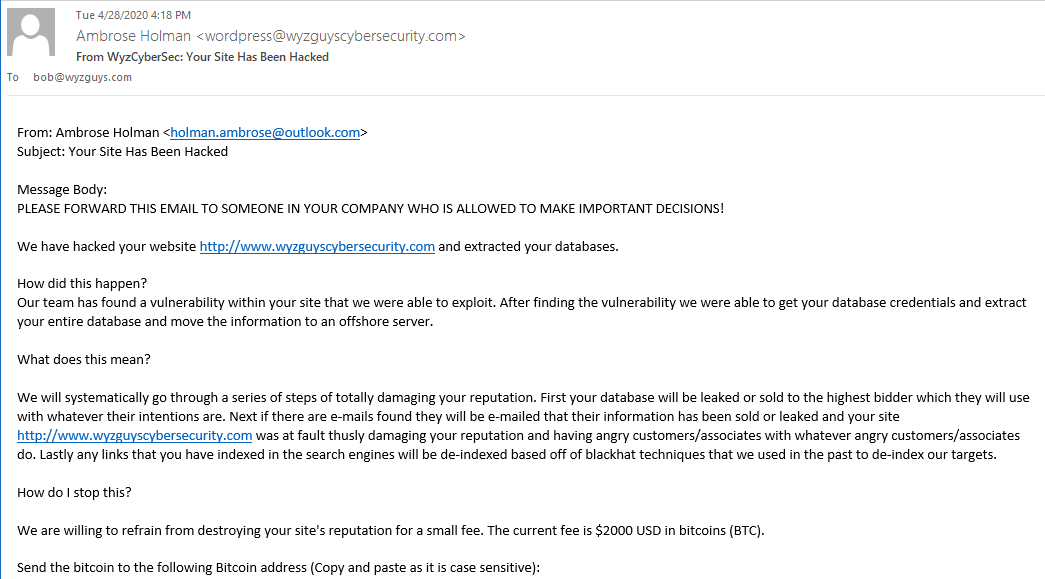
Supposedly, Ambrose Hacked My Website and is Holding It for Ransom
I got the following email. Pretty sure this is bogus, and I guess we will find out soon enough. This message was sent to me from my own contact form on my website. Then entire text of the email follows the image. I removed many unnecessary line breaks, but otherwise the message is unchanged.
This one bears looking after, and I will be checking his claims, but my website has pretty good security, so I doubt it. Anyway, how can you destroy my reputation by publishing the contents of my database? I have no user account information collected, and the articles in this blog represent the contents of my database.
If you get a message like this one, you might want to have your web designer, web hosting company, or IT professional take a look at the site for evidence of a breach. But these sorts of messages are usually a bluff, they have nothing, and are hoping to scare you into paying the extortion fee.
I got another identical email from a different sender this morning (4-29), so I am now certain this is a scam.
From: Ambrose Holman <holman.ambrose@outlook.com>
Subject: Your Site Has Been Hacked
Message Body:
PLEASE FORWARD THIS EMAIL TO SOMEONE IN YOUR COMPANY WHO IS ALLOWED TO MAKE IMPORTANT DECISIONS! We have hacked your website http://www.wyzguyscybersecurity.com and extracted your databases.
How did this happen? Our team has found a vulnerability within your site that we were able to exploit. After finding the vulnerability we were able to get your database credentials and extract your entire database and move the information to an offshore server.
What does this mean? We will systematically go through a series of steps of totally damaging your reputation. First your database will be leaked or sold to the highest bidder which they will use with whatever their intentions are. Next if there are e-mails found they will be e-mailed that their information has been sold or leaked and your site http://www.wyzguyscybersecurity.com was at fault thusly damaging your reputation and having angry customers/associates with whatever angry customers/associates do. Lastly any links that you have indexed in the search engines will be de-indexed based off of blackhat techniques that we used in the past to de-index our targets.
How do I stop this?
We are willing to refrain from destroying your site’s reputation for a small fee. The current fee is $2000 USD in bitcoins (BTC). Send the bitcoin to the following Bitcoin address (Copy and paste as it is case sensitive): 1Md6imvB2neTF3s1kFiMG473k1XrBhxQhF
Once you have paid we will automatically get informed that it was your payment. Please note that you have to make payment within 5 days after receiving this notice or the database leak, e-mails dispatched, and de-index of your site WILL start!
How do I get Bitcoins? You can easily buy bitcoins via several websites or even offline from a Bitcoin-ATM. We suggest you to start with http://coinmama.com for buying bitcoins with credit/debit cards or http://localbitcoins.com for other type of payments.
What if I don’t pay? If you decide not to pay, we will start the attack at the indicated date and uphold it until you do, there’s no counter measure to this, you will only end up wasting more money trying to find a solution. We will completely destroy your reputation amongst google and your customers. This is not a hoax, do not reply to this email, don’t try to reason or negotiate, we will not read any replies. Once you have paid we will stop what we were doing and you will never hear from us again! Please note that Bitcoin is anonymous and no one will find out that you have complied. —
This e-mail was sent from a contact form on WyzGuys Cybersecurity (http://wyzguyscybersecurity.com)
Share
MAY





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com