Phishing Email Alerts
Catch of the Day: Web Form Phish
Chef’s Special: Voice Mail Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
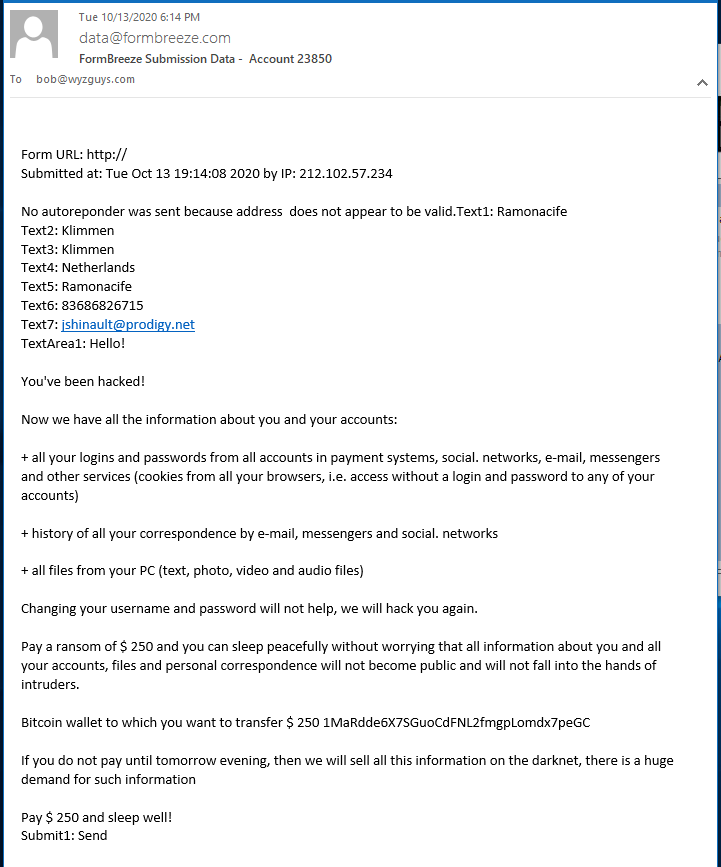
Web Form Phish
A popular way to phish is to send a web form to the owner of the website. This is an example, and is a simple extorsion threat that I am going to ignore. If you have a website with any sort of form, you can expect to get your share of these emails.
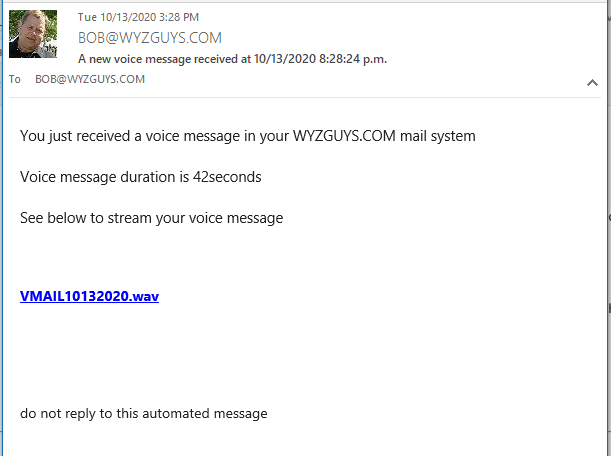
Voice Mail Phish
Here is a phish pretending to be a voice message. The WAV sound file is really a web link that resolves to https://nap.facesa.com.br/vendor/phpunit/php-file-integrator/scr/?ap_=bob@wyzguys.com. This is another one to ignore.
New Office 365 Phishing Attack Checks Your Stolen Credentials in Real-Time
Nothing says the bad guys are intent on stealing credentials like testing them while you participate in their phishing attack so they can verify the validity before letting you off the hook.
There are tons of stories where a fake log on to Office 365 is the punchline. But seldom do we see an attacker go the length to develop code that passes the compromised credentials over to Office 365 to check them out mid-attack.
NFL and NBA Player Account Takeovers Started with Phishing
They gained access to the social media accounts of some of the biggest names in sports. This included account takeovers of both NFL and NBA players. Now the U.S. Department of Justice (DOJ) is revealing the attacker identities, detailing their attack methods, and charging them with federal crimes. The accused hackers in this case both live in the U.S., and only one of them is old enough to order a beer… Read more
USPS and FedEx Phishing Attack Texts Flood Mobile Phones
Taking a page from traditional phishing scams that seek to use broadly-accepted messages and send them to everyone, last month officially brought SMiShing to the cybersecurity forefront.
The bad guys have figured out that, beyond ransomware, cyberattacks are a long-tailed game. Whether the endgame is fraud, data theft, or espionage, the initial play is almost always stealing credentials, infecting with trojan malware, or gaining access to a network.
Traditionally the target is an endpoint device running Windows or Mac OS. But last month’s widespread SMS-based phishing attack using a fake delivery message only proved that the bad guys can use any device to start an attack.
Pretending to be USPS, FedEx, or an unnamed shipper, U.S. residents began receiving multiple delivery notification texts offering a URL for more information.
Most of these attacks attempted to steal Google account credentials, while some pointed to fake casino games. Back in February, the Federal Trade Commission issued an alert on such scams, but it wasn’t until last month that these types of texts went mainstream.
With more legitimate companies using texts as a means to stay in contact with customers having an overloaded email Inbox, this kind of attack is only going to see more attention from cyberattacks.
And because it’s just as easy to create a business-related text (“An Office 365 email has been quarantined. CLICK HERE” is all it takes!) to steal credentials, it’s imperative that users be educated to understand why and how these scams are used to trick them, and the repercussions to your organization should the user fall for them.
Share
OCT





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com