 Happy SysAdmin Day!
Happy SysAdmin Day!
Today is the annual recognition event for all the sysadmins, technical support specialists, and cybersecurity professionals who keep your computers and networks operational and secure. Gifts are appreciated.
Phishing Email Alerts
Catch of the Day: Fake Domain Renewal Phish
Chef’s Special: Incomplete Document Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extended off the page, double-clicking on them will open them up in a photo viewer app.
Fake Domain Renewal Phish
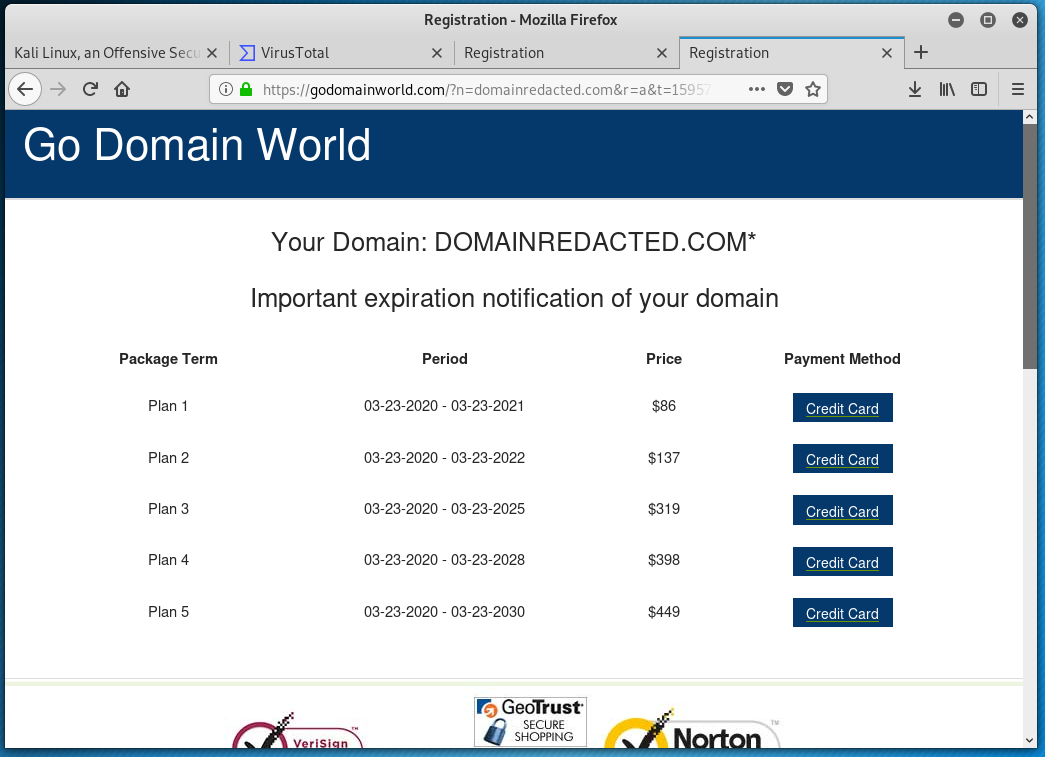
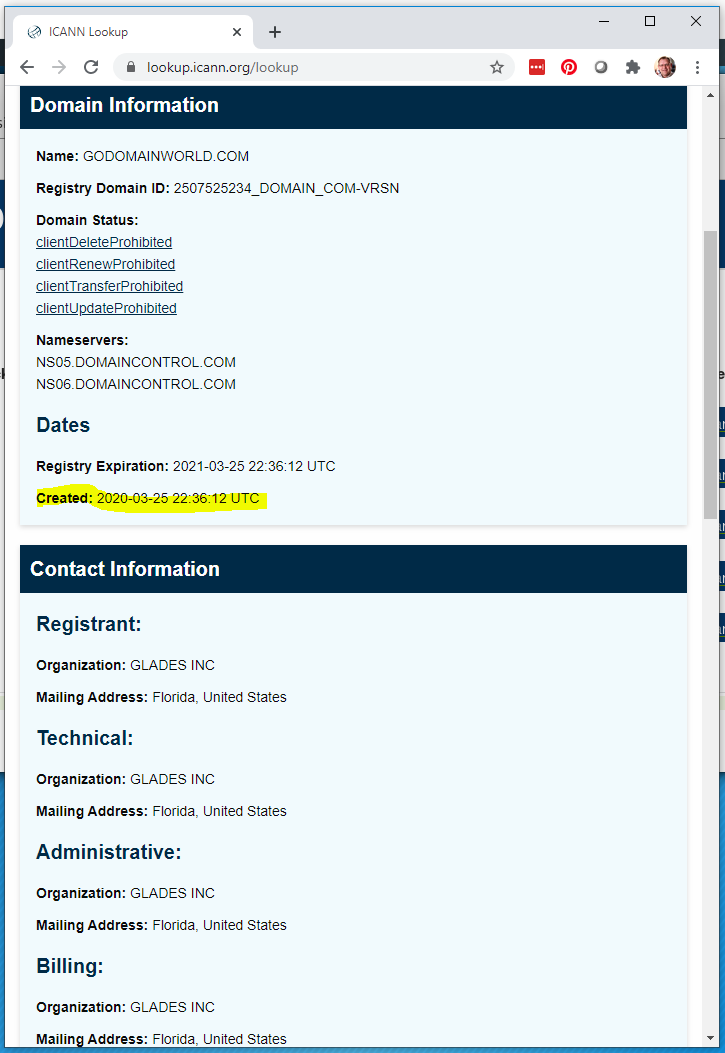
This example was sent to me by a long-time client who just wanted me to verify that this was a spam message. Over the years, he has learned to forward anything suspicious like this to me for review and an opinion. His name and his domain name has been redacted to protect his privacy. I don’t need to spell out the URL path, because they are explicit in the email, and resolve where they say they will, at a scammy domain registration company called Go Domain World. A quick lookup on the ICANN whois database showed the domain was recently registered on March 25 2020. Recent registrations can be a clue that this domain is being used in a scam. Here’s the email:
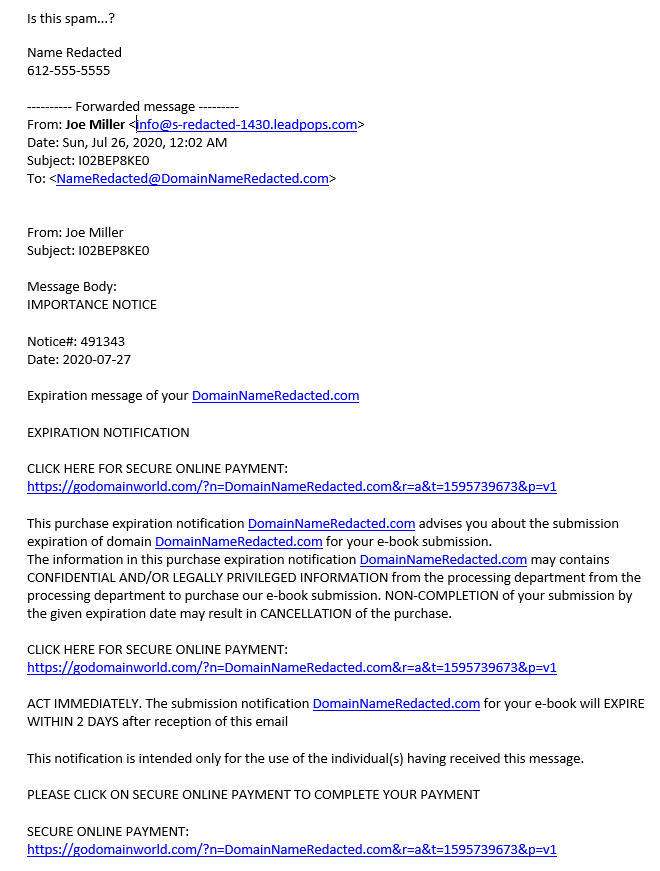
This is the landing page, but when I entered just the domain name to find the home page for Go Domain World, this is also the home page.
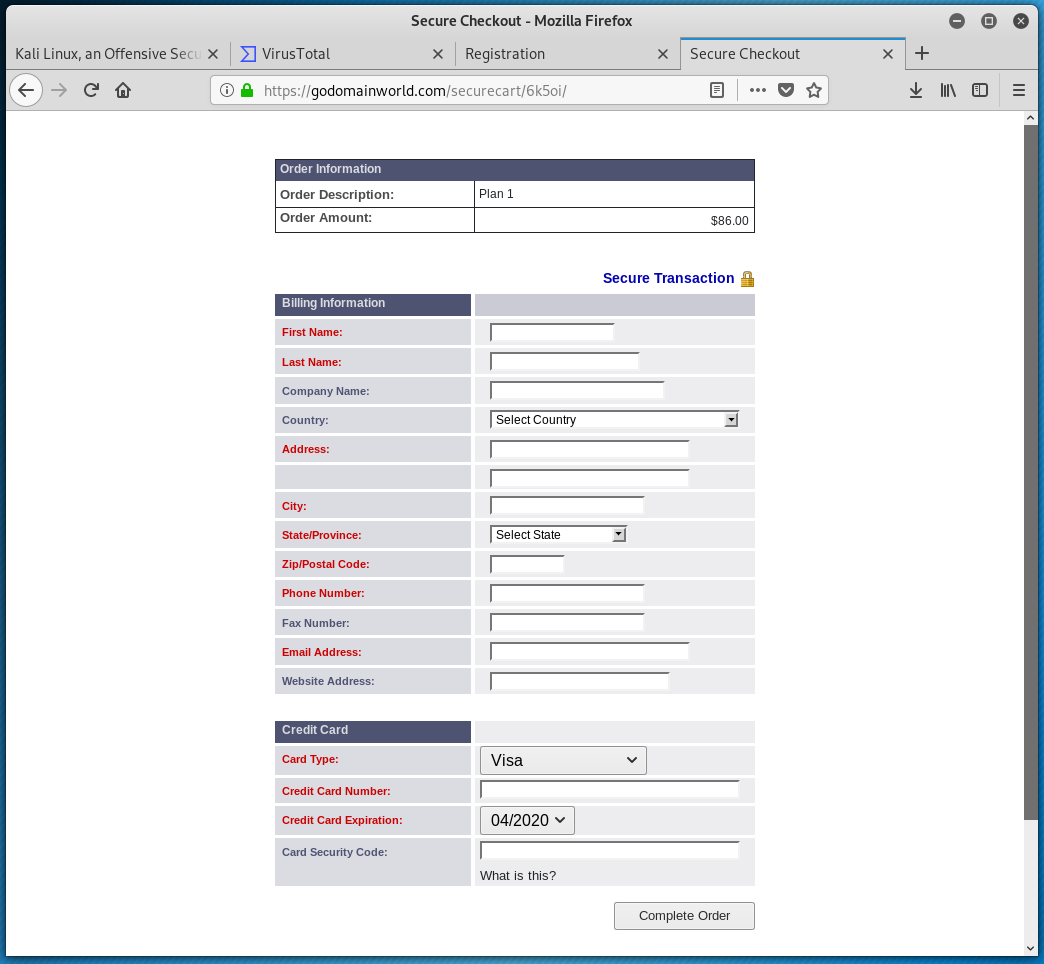
Clicking on one of the package term button lead to this page. So far they have NOT asked for an AUTH CODE, so this may be a straight out scam – I got your money and all your personal information. Or that step may come on the next page, in such case your domain name will be transferred to a new registrar, and your web site will stop working until it is resolved. Either way you gave a lot of info to a bunch of scammers.
Here is the ICANN whois lookup
And here is the VirusTotal report on the godomainworld.com links
After I finished up collecting information on this email, I returned to reading my email, and another one just like it showed up in my email inbox!!
Comparison of Genuine Credit Score Email to Spam/Phishing Email
Well Readers, I really did it. In playing through the landing pages on the credit score phish I autopsied last week, I managed to register my actual email address with the attackers, and the spam is coming daily. I can tell its them because most of the emails feature that Mumbai address in the footer.
Today I got an email from Experian, and another from my new pals in India. I am going to do a side by side comparison to help show you the differences between real and fake emails. First the Experian email. 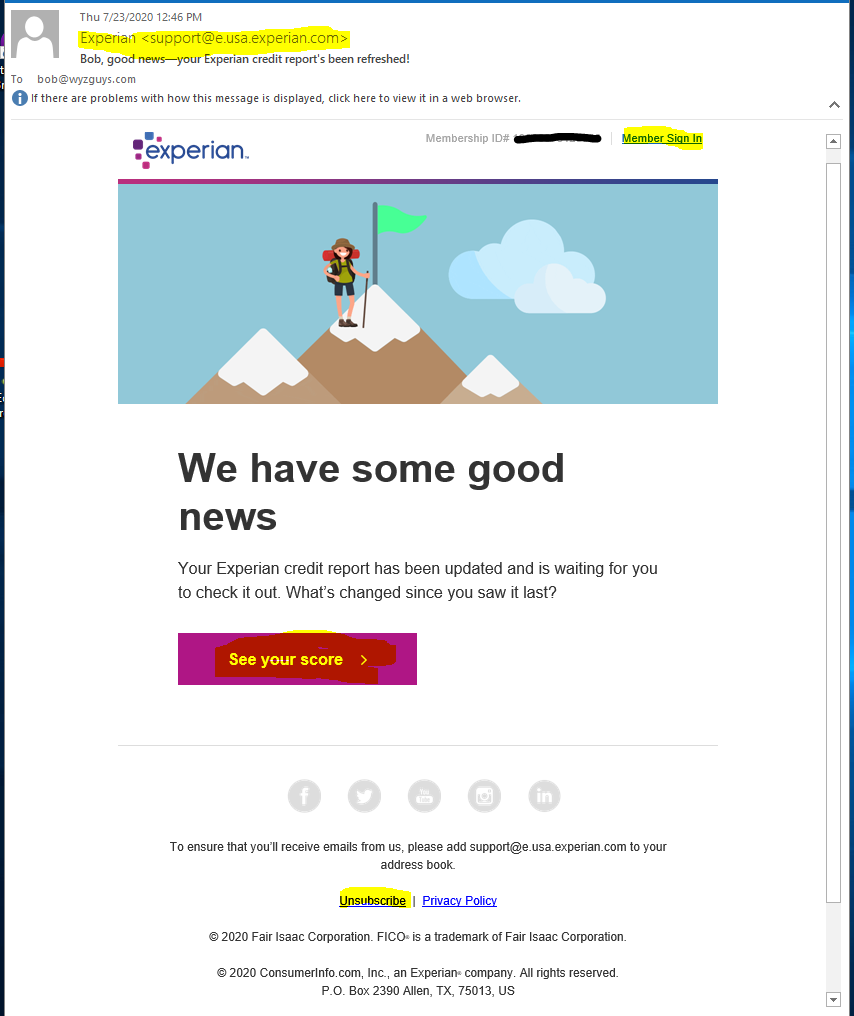
The sender email address, and all the links in this email all got to the experian.com domain
Member Sign In link https://click.e.usa.experian.com/?qs=d3d5487…(truncated)
See your score button https://click.e.usa.experian.com/?qs=d9e5a7…(truncated)
Unsubscribe link https://click.e.usa.experian.com/?qs=d3d5487…(truncated)
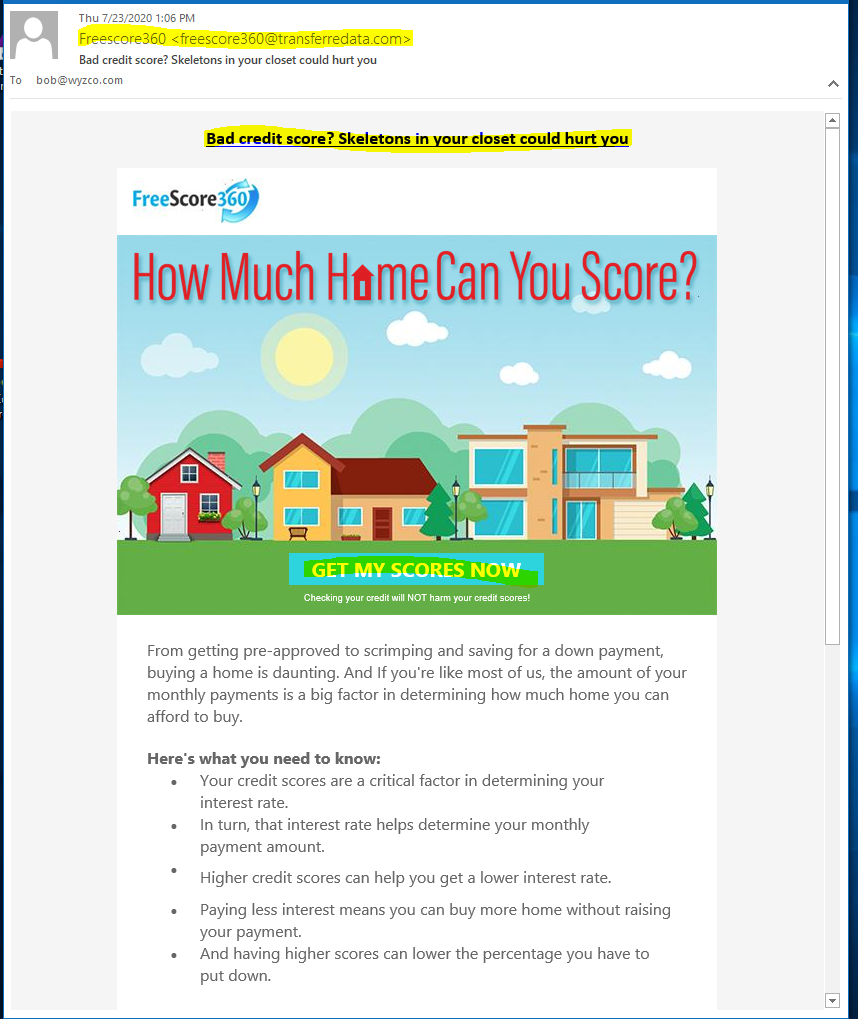
Now let’s look at the spam email.
The email domain and links at least use the same domain, so I would categorize this as more of a marketing spam email than a malicious, credential stealing phishing email. Here is where the links resolve.
Bad credit score? link http://www.transferredata.com/a076UVS2395…(truncated)
Get My Scores Now button http://www.transferredata.com/a076UVS2395…(truncated)
The main problem is that I am going to have to train my spam filtering tools to move these messages to spam. In the future, I will be more careful when I decide to explore the landing pages and forms.
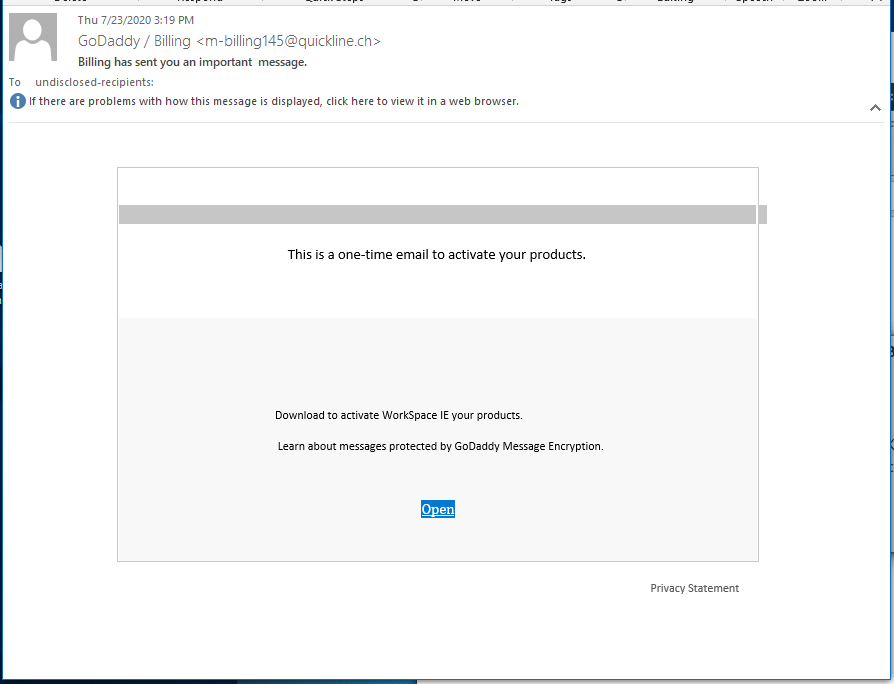
Fake GoDaddy Billing Phish
I got this phish from “GoDaddy.” There is so much wrong with this one it is hard to be seriously, but the attacker on this exploit used an HTML download, which was a new wrinkle.
First the email domain and link where on different domains, the email is from Switzerland and the link is from Australia.
GoDaddy / Billing <m-billing145@quickline.ch>
Open link http://ie.sunspec.com.au/ This link came up clean in VirusTotal. But the file it lead to did not.
Download Link https://fs01n5.sendspace.com
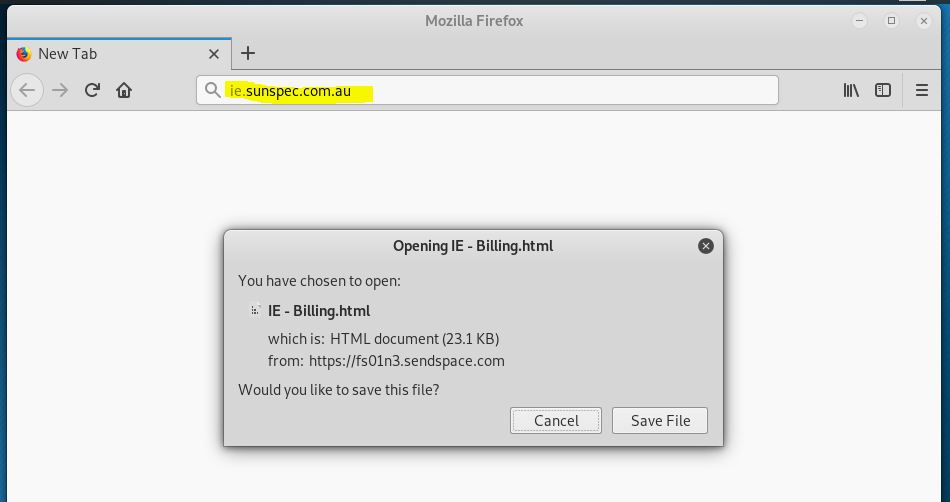
The link took me to a sendspace.com site where I was encouraged to download an HTML file.
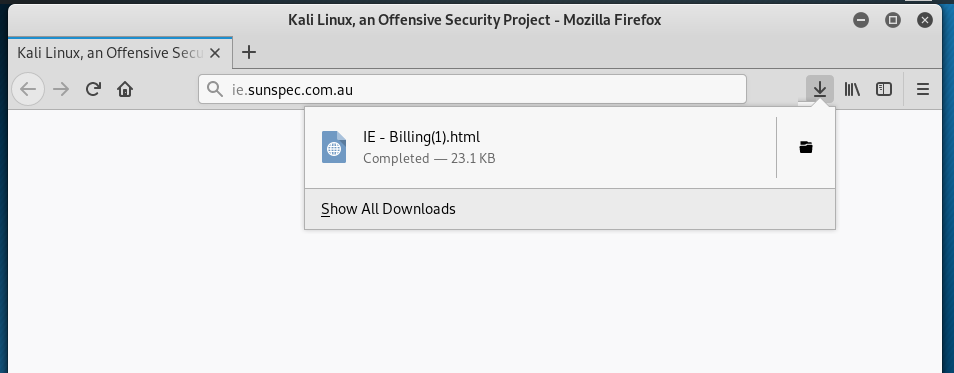
When I clicked on Save File the site downloaded an HTML file, a web page.
When I opened the file download, I was shown this HTML page. Not sure what an Earthlink login screen has to do with a GoDaddy invoice, so another mark against the attacker for poor design. It looks like this exploit was cobbled together from a bunch of mismatched parts.
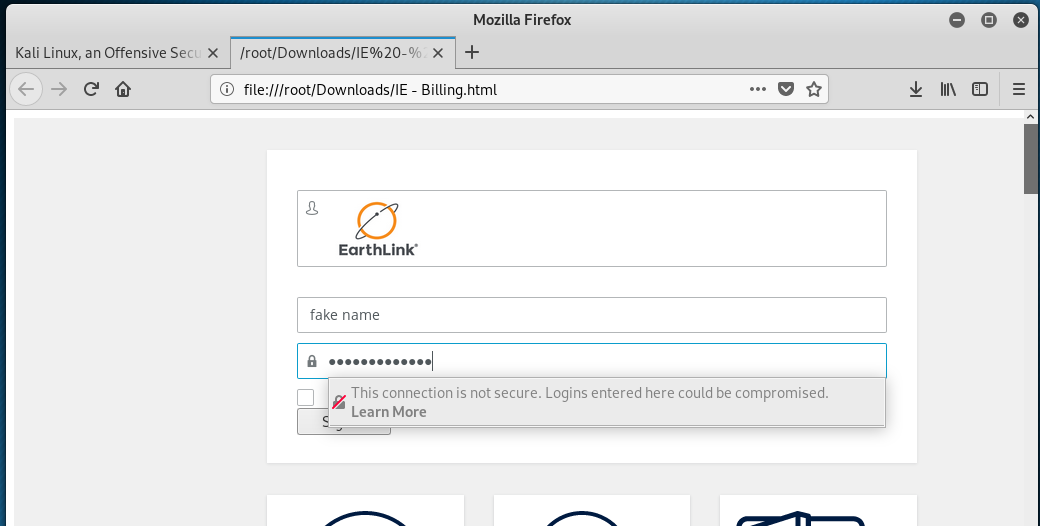
I entered a fake user ID and password, and Firefox threw up a warning. Not sure what happened when I click on Sign In, might be credential stealing or it might be that the HTML file was also carrying malware. Basically I am hoping that the malware does not run in Linux.
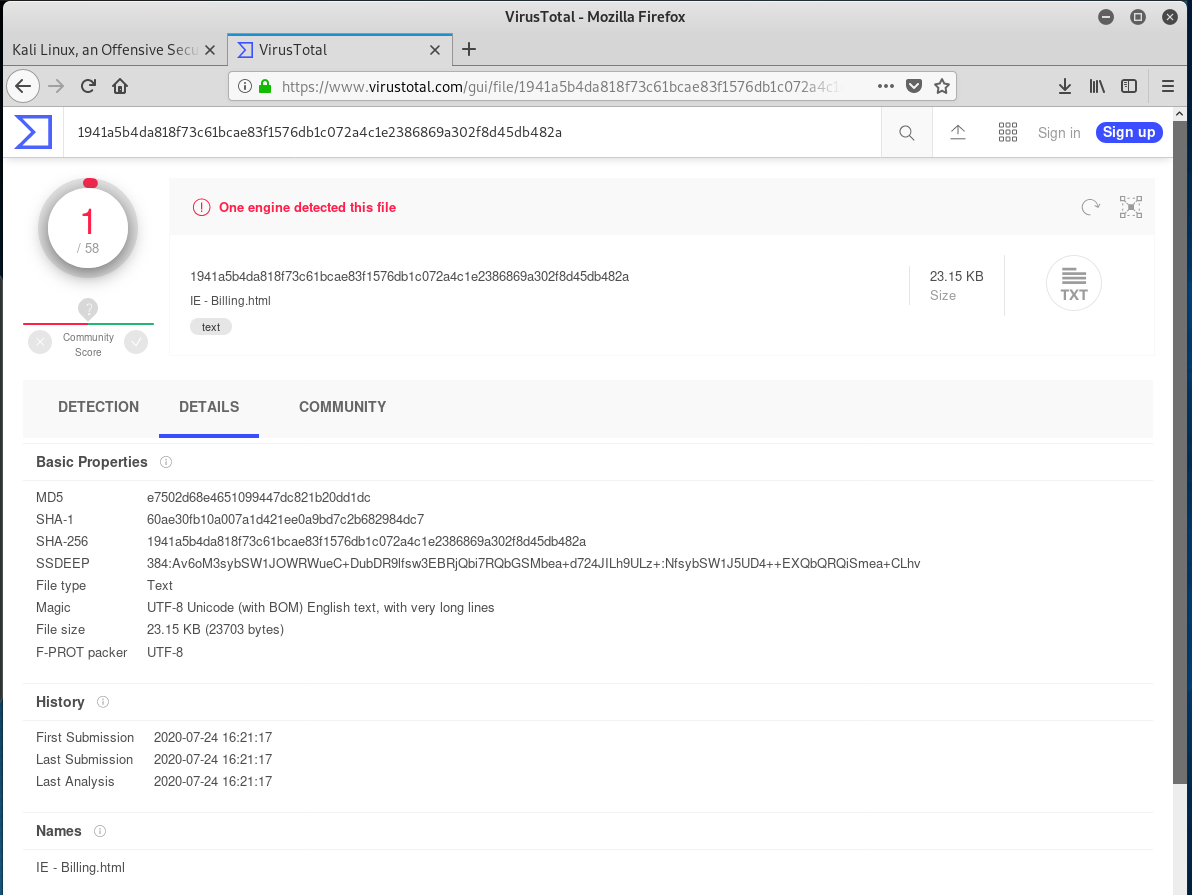
For good measure I uploaded the HMTL file to VirusTotal for analysis. ESET identified it as a phishing exploit.
I have not reported on a phishing exploit that used a download in this column yet, so this was interesting from that standpoint.
Incomplete Document Phish
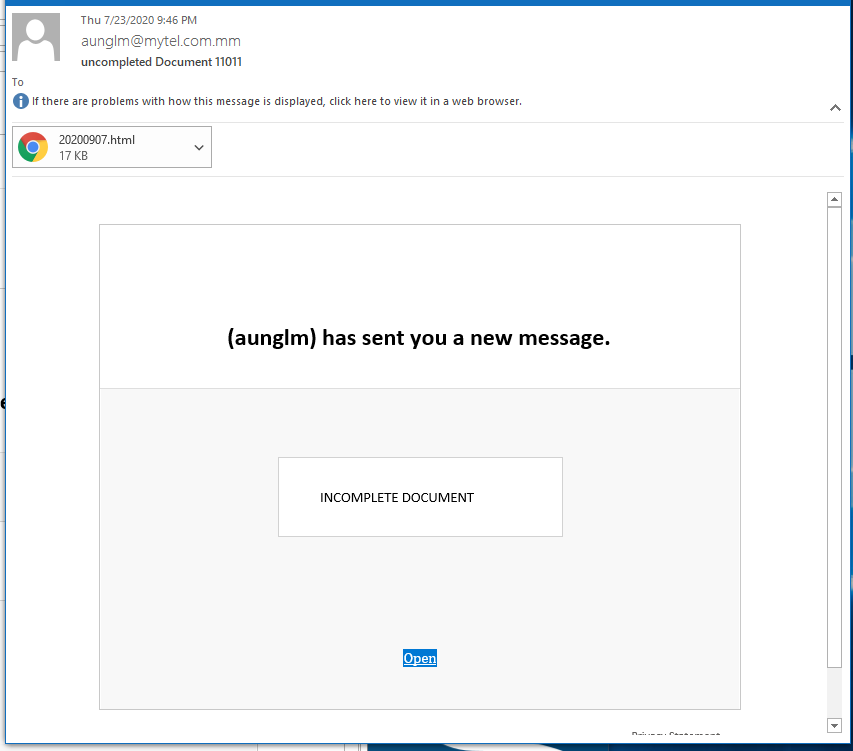
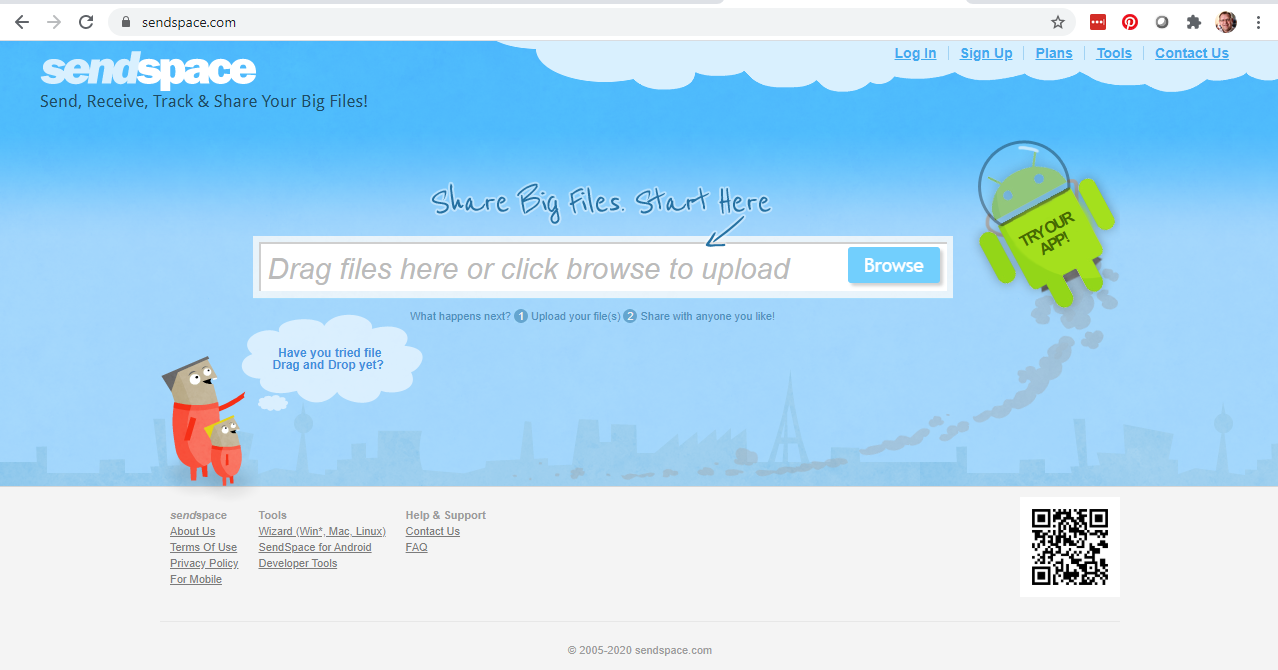
Not sure what’s happening, but this phishing exploit is very similar to the last one (GoDaddy). The phishing email is nearly identical, and both this exploit and the GoDaddy one use a sendspace.com document download. I investigated this phishing email a little differently, though so stick with me.
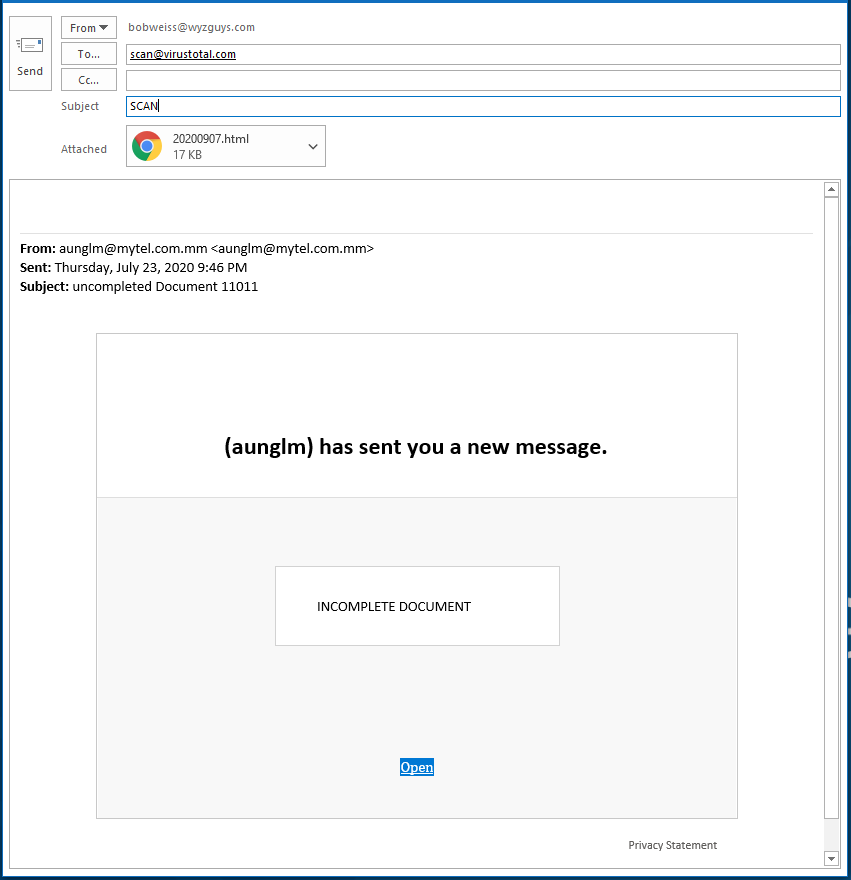
The email was sent using an email domain on the Myanmar top-level country domain space (.mm).
Here’s the email: It has an HMTL attachment, and an OPEN button
I decided to start the investigation by forwarding this email to VirusTotal, using the method I have recommended before. Click on the forward button, and send it to scan@virustotal.com, be sure to change the subject line to SCAN. I have demonstrated in the next image.
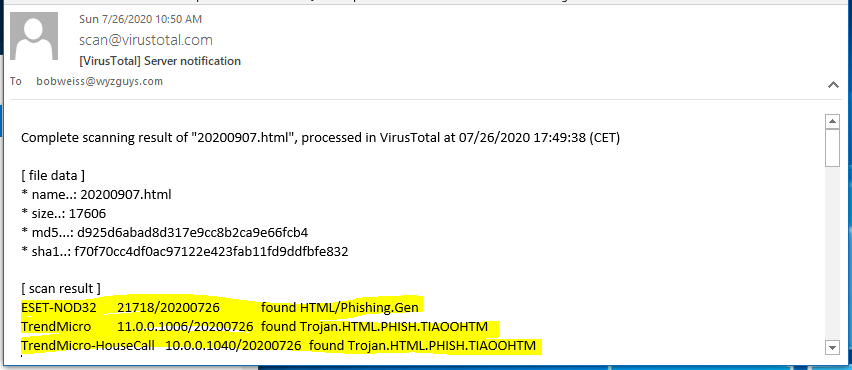
VirusTotal replied by email in a few minutes, and the HTML attachment was identified as malicious by three scanners – ESET, and to from TrendMicro.
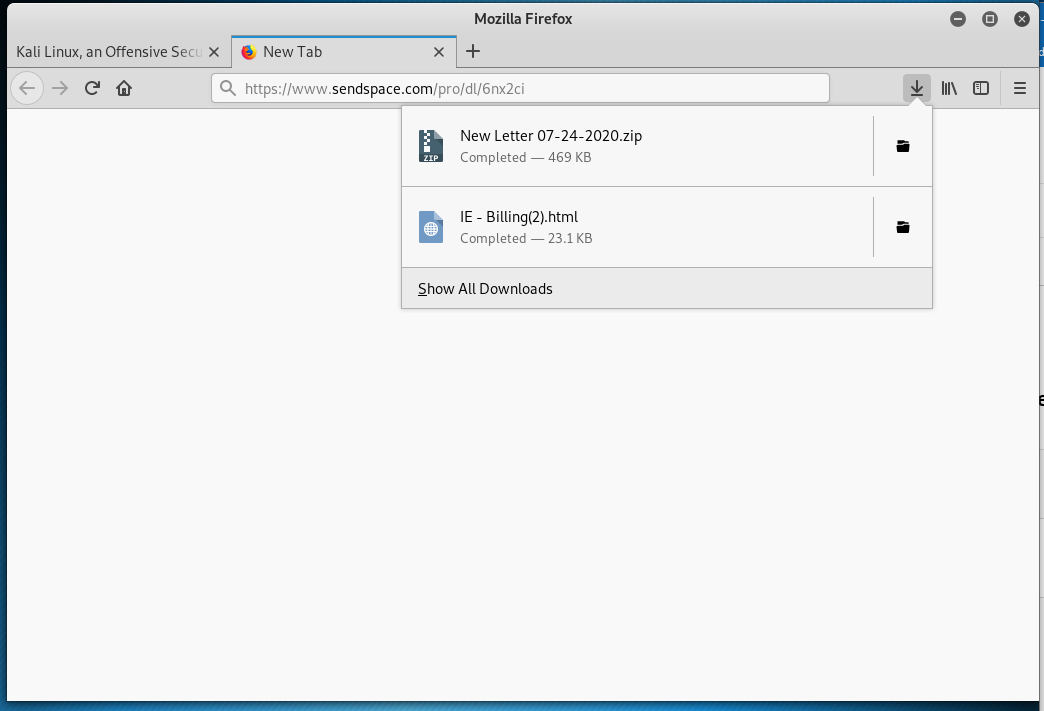
Next I clicked on the Open link, using the safety of my Kali Linux virtual machinie. This took me to a URL at https://www.sendspace.com/pro/dl/6nx2ci. The page opened a download box, too much to resist, so I clicked on the Save File button. This is the second time this week I am downloading something from sendspace.com.
The download contained a ZIP file archive named New Letter 07-24-2020.zip.
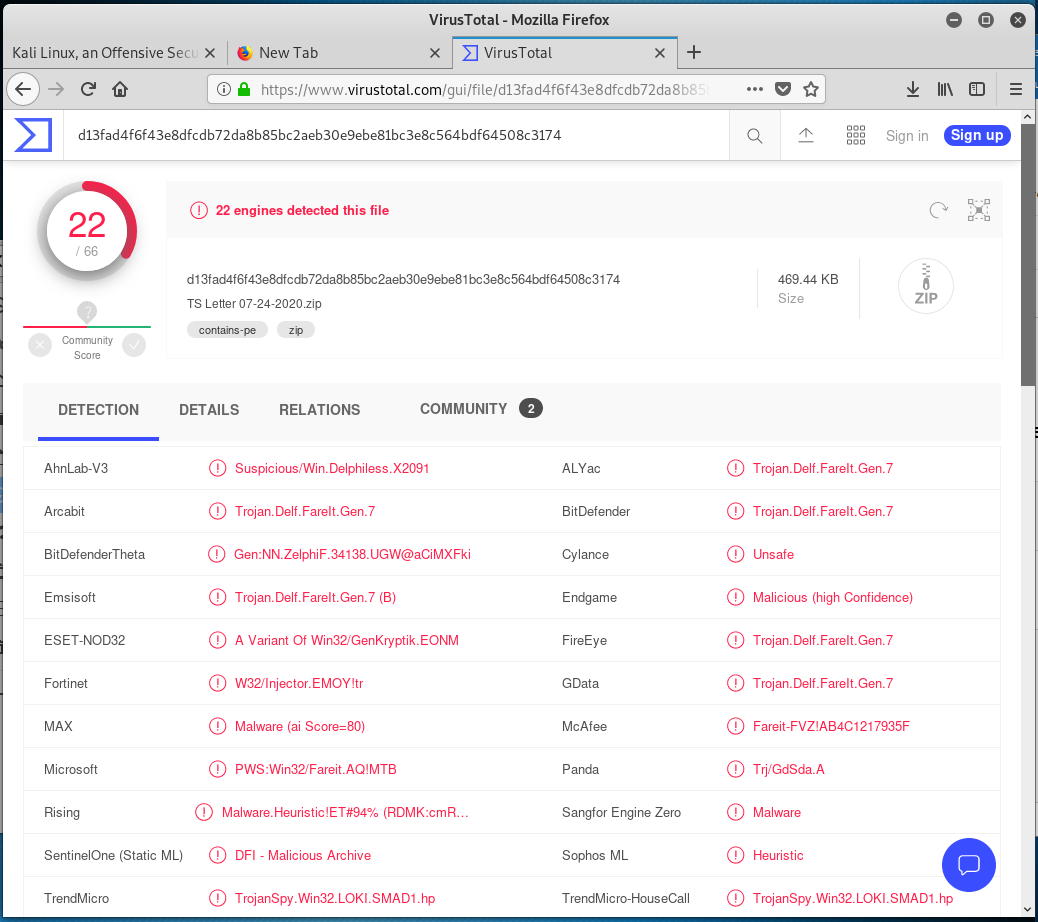
You never know what is in a ZIP archive, and I didn’t want to open it, even in the Kali VM. My next move was to upload the ZIP file to Virustotal.
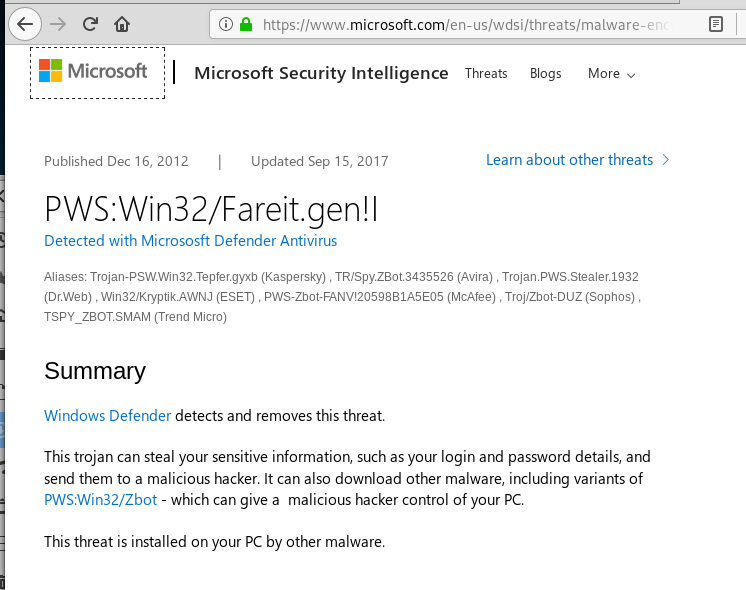
My my, what a nasty little file we have. Many of the scanners reported Trojan.Delf.Fareit.Gen.7, so I looked it up in Google and found a description on Microsoft’s website. Here’s what they described. Of course, Microsoft uses a different nomenclature, but this is the same bit of malware.
And what about Sendspace? I went to sendspace.com and discovered that it is a semi-legitimate file sharing service on par with Onedrive or Dropbox.
A quick Google search for “Sendspace reviews” found this article on the first page, plus additional pages describing hoe to remove SendSpace advertising plugins.
Glad I didn’t open this one. Not sure if this is two guys using the same exploit kit with different modifications, or if this is the same guy trying to accomplish the same thing using variations in methodology. Either way, you now know what to look for in your own mailbox.
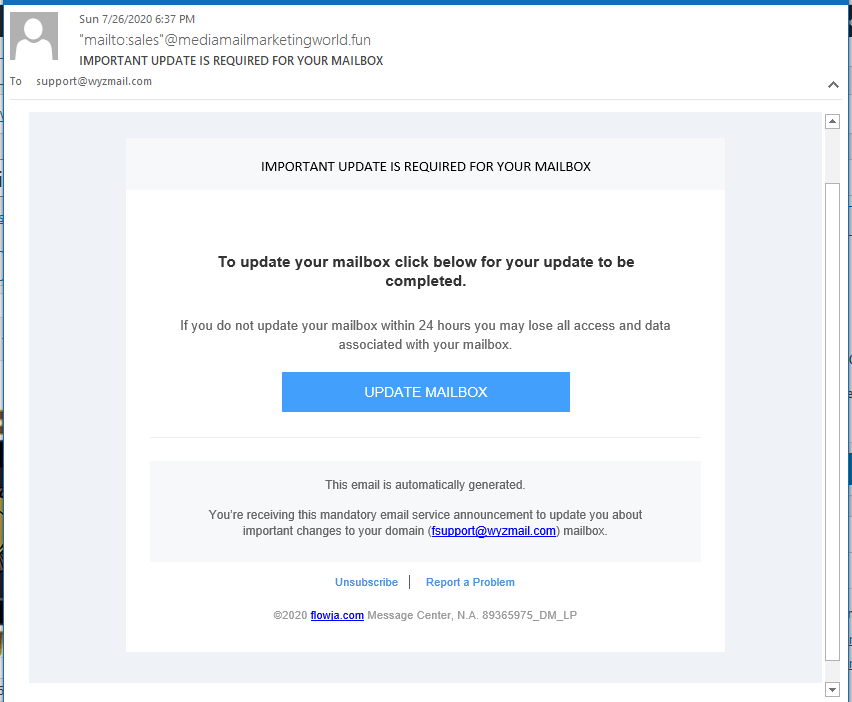
Update Mailbox Phish
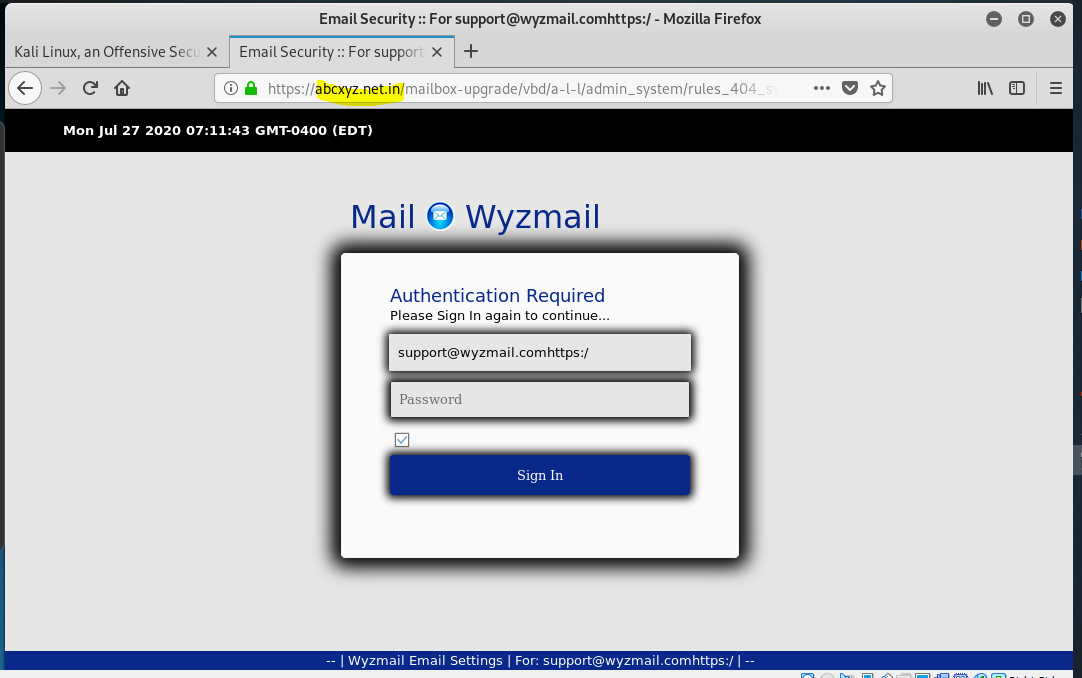
Here’s a cyber-criminal with a sense of humor. Email domain ends in the TLD “fun”. Then the URL link for the Update Mailbox button contains some “funny” encoding, now_g-a-m-e_starts. https://abcxyz.net.in/mailbox-upgrade/vbd/a-l-l/admin_system/rules_404_sys/2o19_nile_moves/ok_excute_2-2-1/now_g-a-m-e_starts/all-28-05-19/index.php?email=support@wyzmail.com.
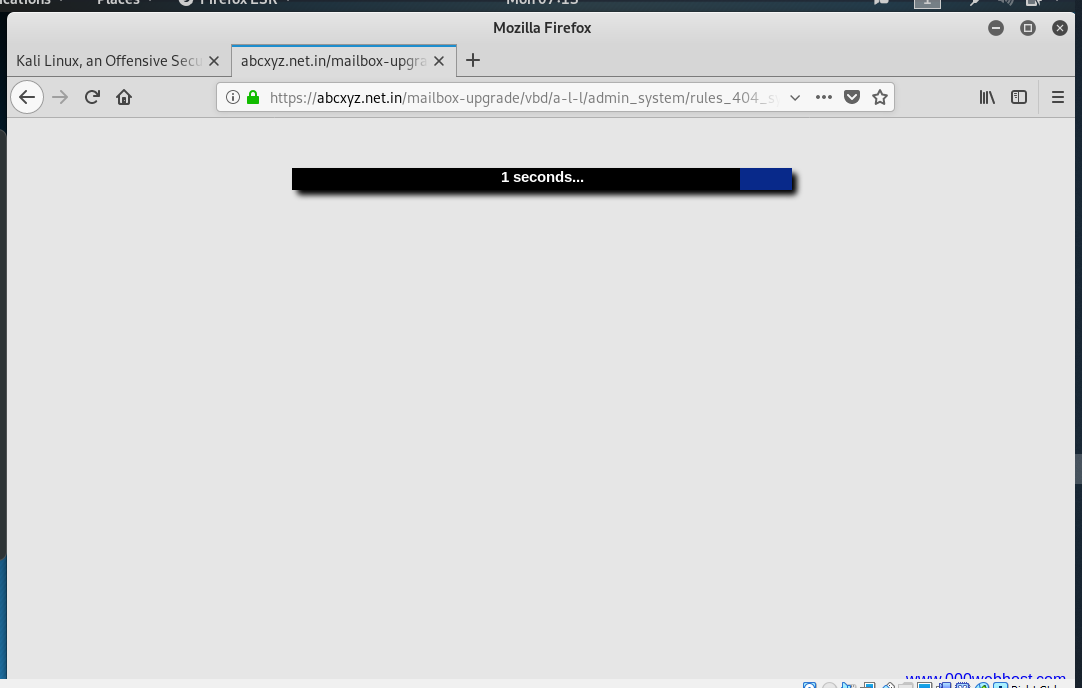
Clicking on the button took me to this landing page, where I selected a language. That took me to a second landing page with a login form. Entering a password, took me to a Progress bar page, but eventually it spawned an error and took me back to the fake login for another try. The landing pages were hosted on a website in India.
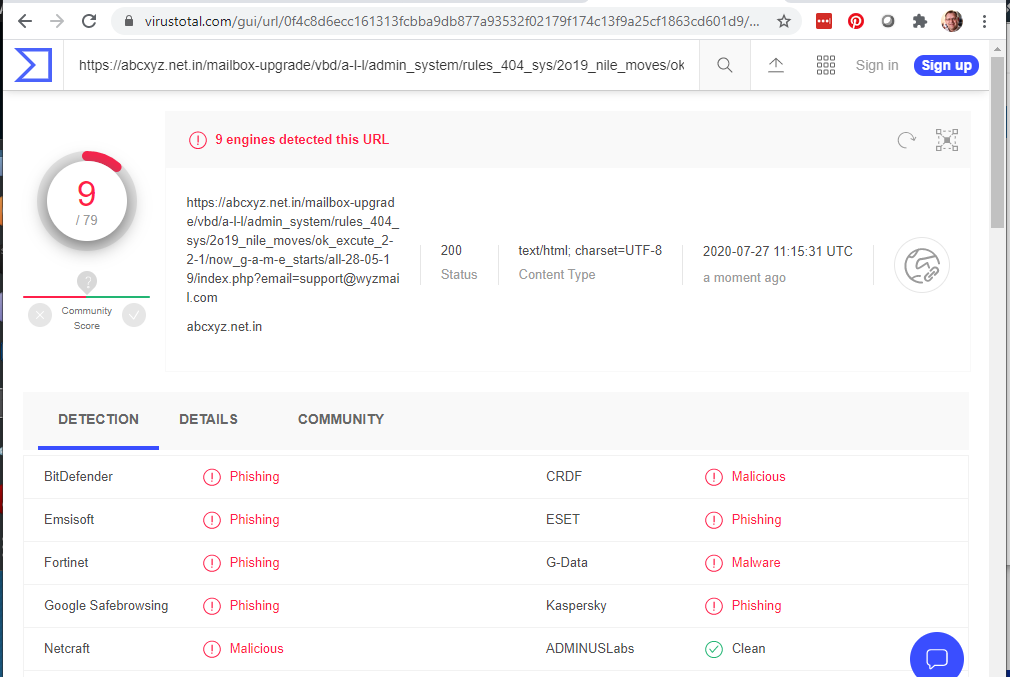
Running a quick VirusTotal scan on the button URL came back positive for a phishing site.
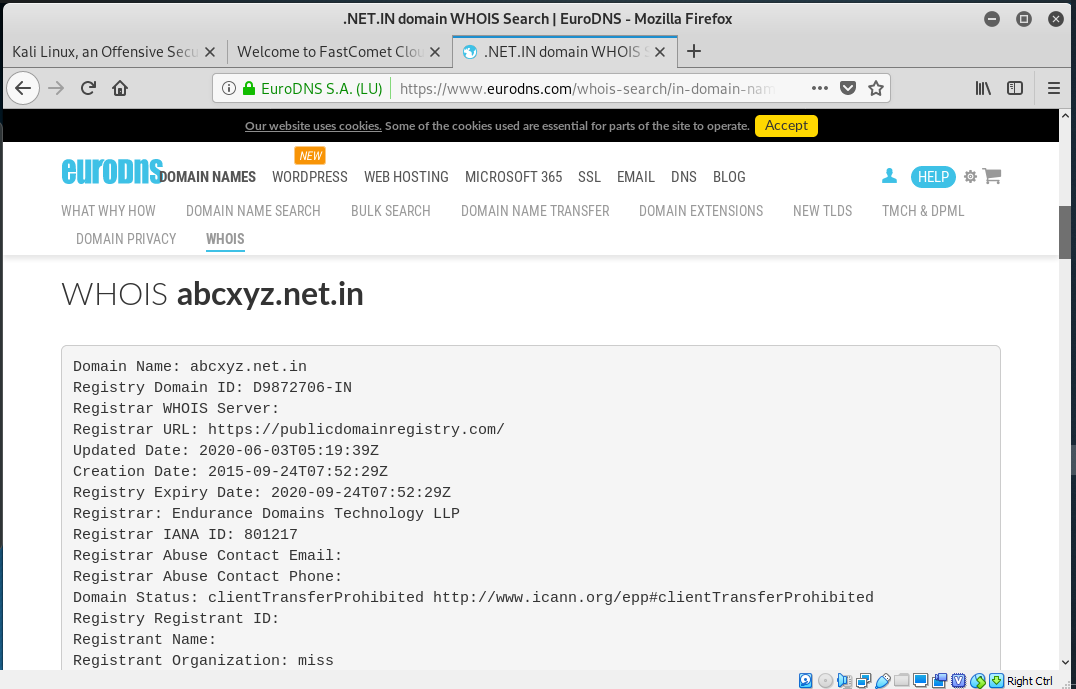
Then I looked up the domain in whois. It was registered in 2015, so this could indicate that the domain and website have been hijacked. Domain records were updated on June 3 2020, which is when this hijacking probably took place.
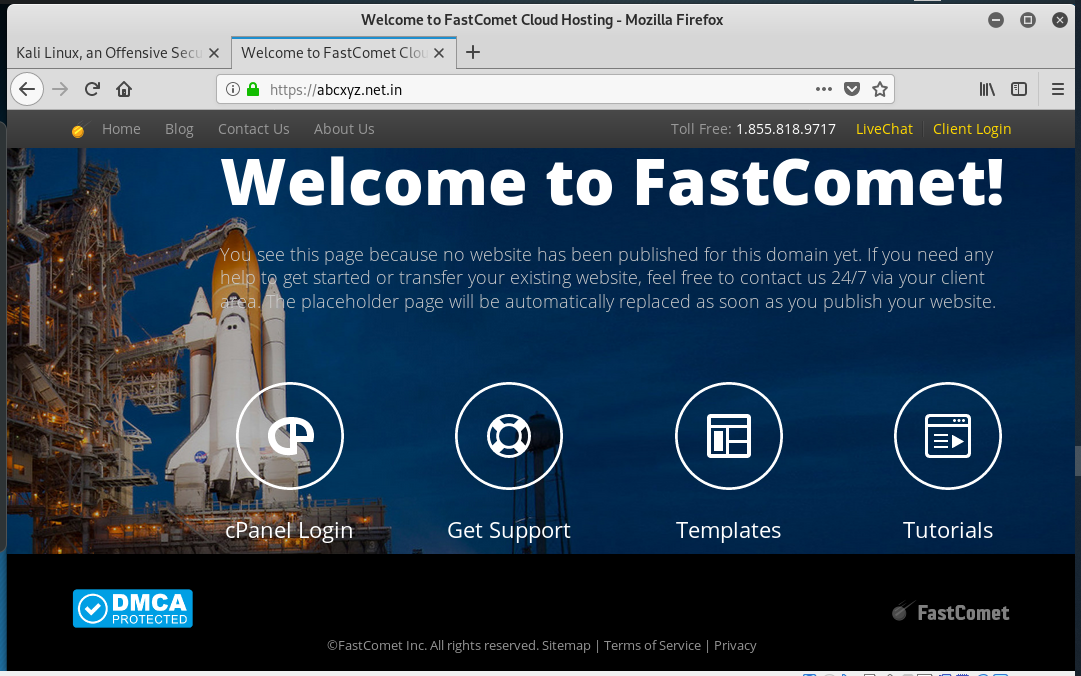
And here is the home page of the hijacked website.
This is a “placeholder” site, a site someone was going to start some day but abandoned. We’ve all done it, opened a social network account or started a website but abandoned them. Cyber-criminals are looking for abandoned accounts and sites to set up operations, and run their exploits. This is web littering. Please don’t litter, when you are done with an account, please close it responsibly.
Anthem Blue Cross EFT Phish
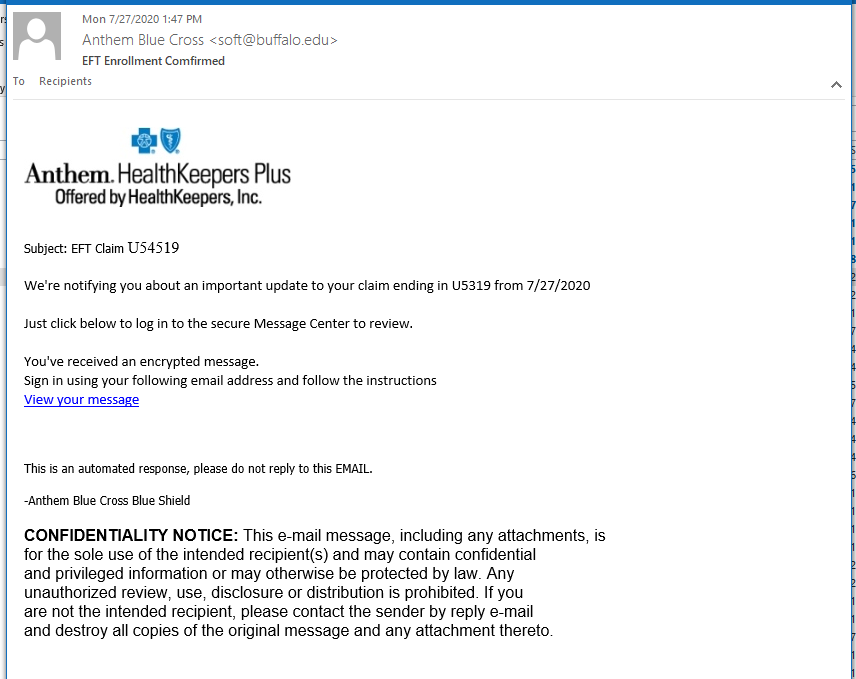
I got a couple of nearly identical phish that both seemed to come from Anthem Blue Cross. But the sender email was different on each of the, although both were from school with a .edu TLD.
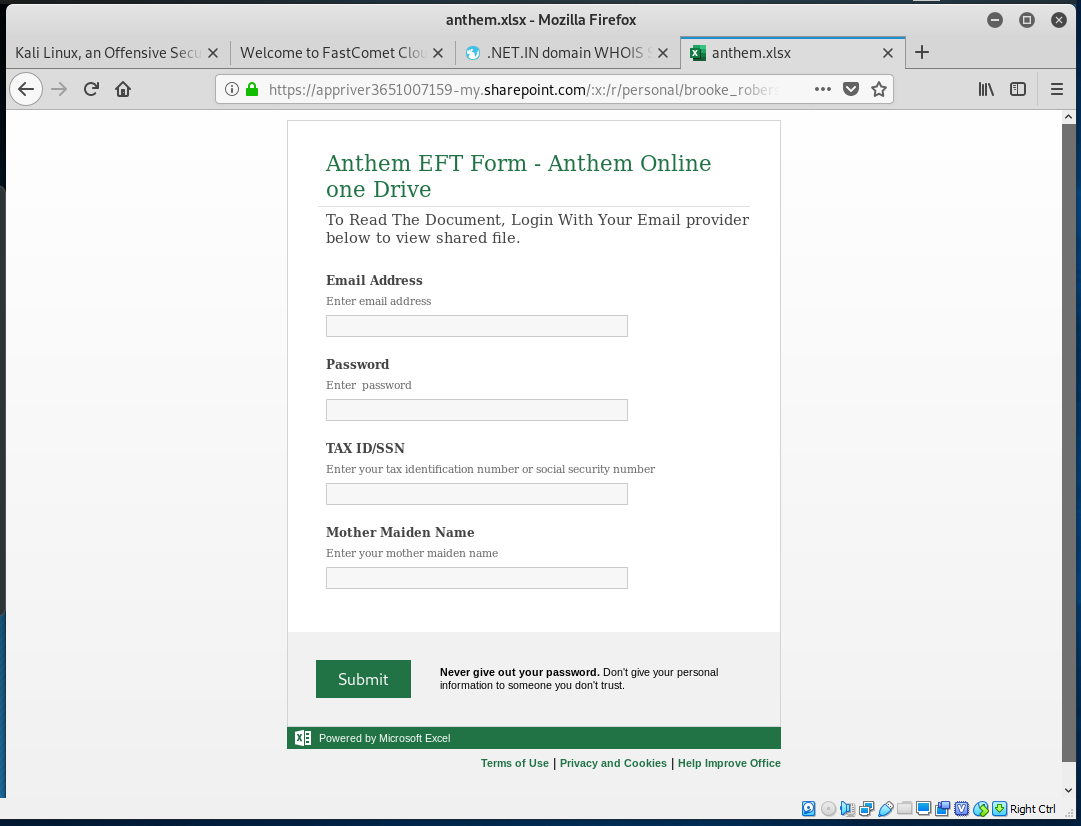
The View your message links bothe started with http://u3699884.ct.sendgrid.net/ls/click?upn=C78eXqp1n…(truncated) and redirected to https://appriver3651007159-my.sharepoint.com/:x:/r/personal/brooke_roberson_sfellc_org/_layouts/15/WopiFrame.aspx?guestaccesstoken=uClV49D%2b%2ftPQ%2bei8ANdBadzzjMnqNVJ2%2f5E%2b22GtYVs%3d&docid=1_1e706d17f46bf44a5a028be0dea8222f0&wdFormId=%7BE94F7FB5-A96E-45E3-BB0D-A6DC24042DB3%7D&action=formsubmit&cid=075088b3-7e35-43dd-a6d2-673847407565
At VirusTotal, Fortinet and GDATA found the first URL to be a phishing link, but the redirect came up clean.
Here are Thing 1 and Thing 2:
The landing page was just another personal information stealing form. It is designed to look like a Microsoft SharePoint form, and appears to open using MS Excel. I especially appreciated the advice next to the SUBMIT button: “Never give out your password. Don’t give your personal information to someone you don’t trust.”
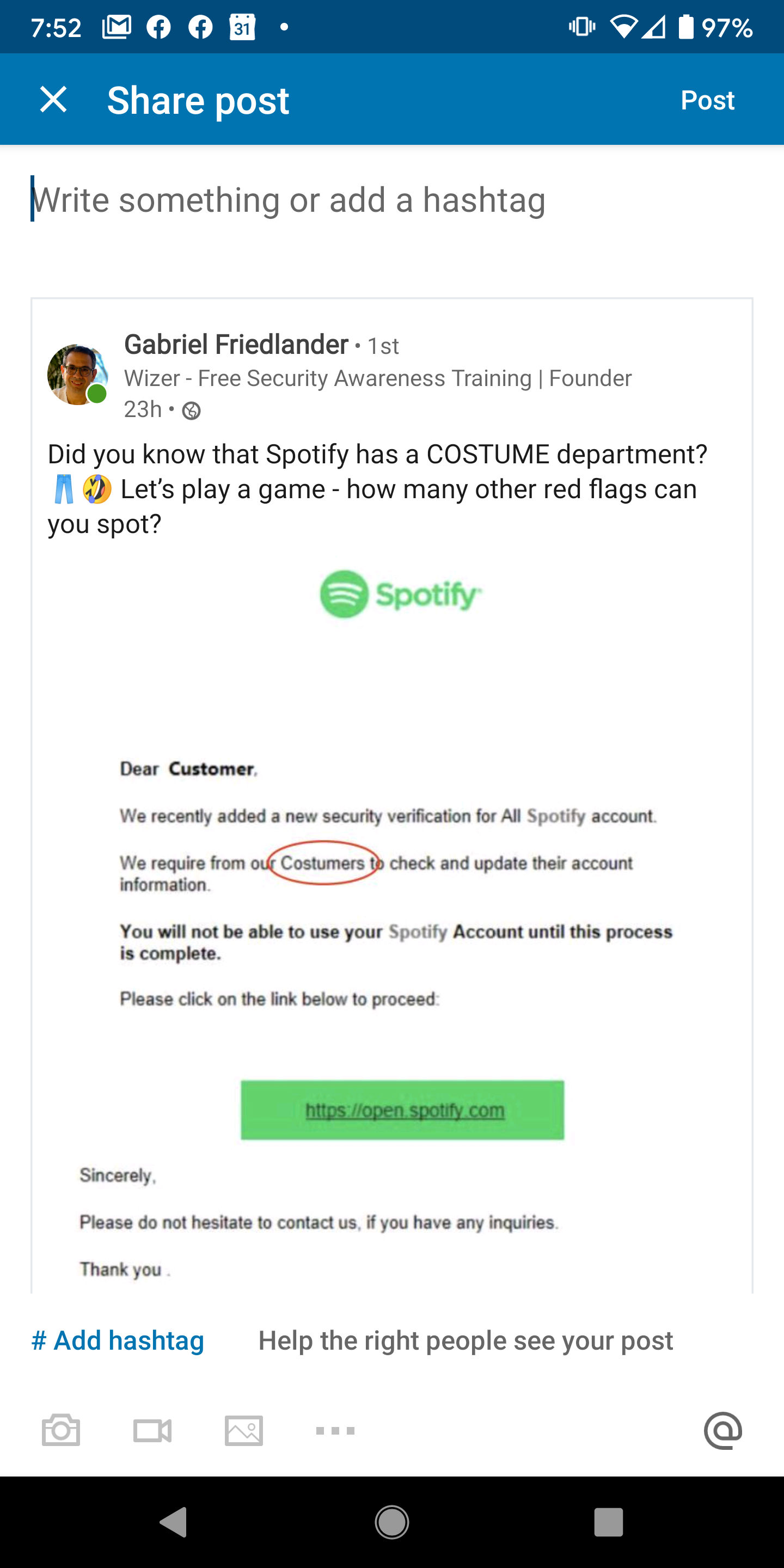
A Spotify Phish
This is from Gabriel Friedlander on Facebook. An email to their “Costumers?” Sometimes a misspelling can get you a new career. Spelling and grammatical errors are always a early warning sign of a phish
Phishing Filtering At Work
Here’s an advice notice from my email hosting company. I have email filtering activated with this account, and this is an example of the filtering working as it should.
Malicious Spam in Your Inbox? Blame Emotet’s Return
Noticing more spam than usual in your email inbox lately? It’s not just you. A five-month hiatus sounds like a long time. But considering who took the vacation, you’ll wish it was even longer. The world’s most costly and destructive botnet, Emotet, reemerged last week, bringing with it a rain of emails that install ransomware, bank fraud trojans, and other nasty malware strains. This lengthy hiatus is fairly… Read more
How to Forensically Examine Phishing Emails to Better Protect Your Org
[Web Conference] Wednesday, August 12 — 1:00 p.m. EDT / 10:00 a.m. PDT
Staying a step ahead of cybercriminals may involve becoming your own cybercrime investigator, forensically examining actual phishing emails to determine the who, the where, and the how. In this web conference, Roger Grimes, KnowBe4’s Data-Driven Defense Evangelist, will show you how to become a digital private investigator! Register here
Share
JUL











About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com