 Phishing Email Alerts
Phishing Email Alerts
Catch of the Day: IONOS Support Phish
Chef’s Special: IRS Notification Phish
Also serving: OneNote Phish
Examples of clever phish that made it past my spam filters and into my inbox. Some are sent by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
IRS Notification Phish
The IRS never uses email or telephone calls to contact taxpayers. Only postal mail.
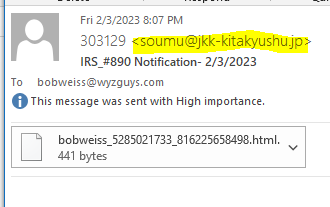
The sender of this email is using an email domain with a Japanese country code. 303129 <soumu@jkk-kitakyushu.jp> which is a clue this is fake.
The attachment is an HTML web page, also unusual.
Downloading…
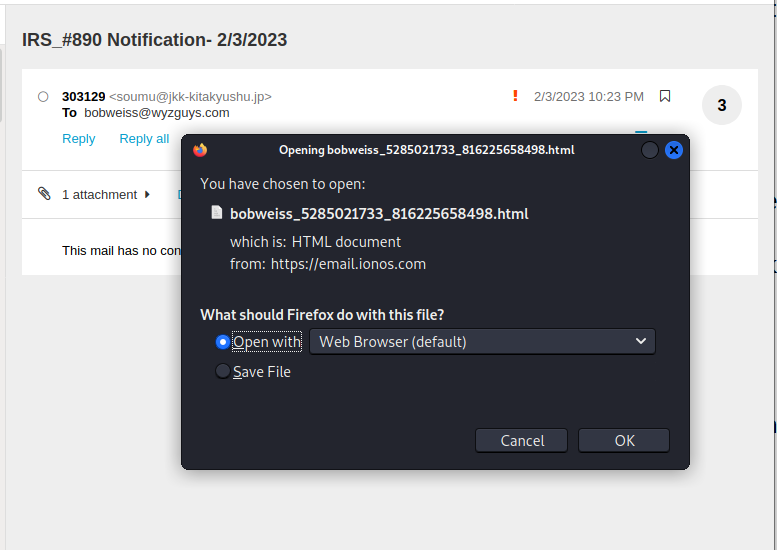
When I opened the attachment using my Kali Linux virtual machine, I got this CAPTCHA page
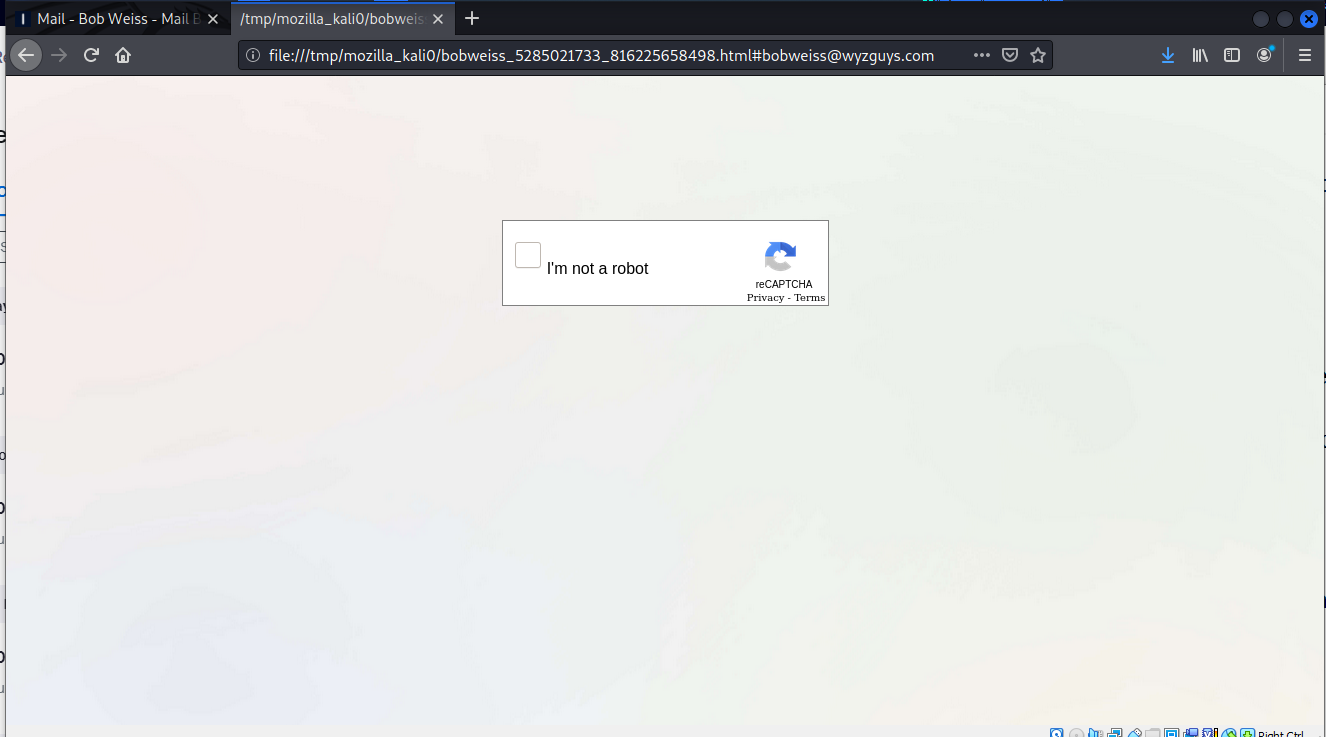
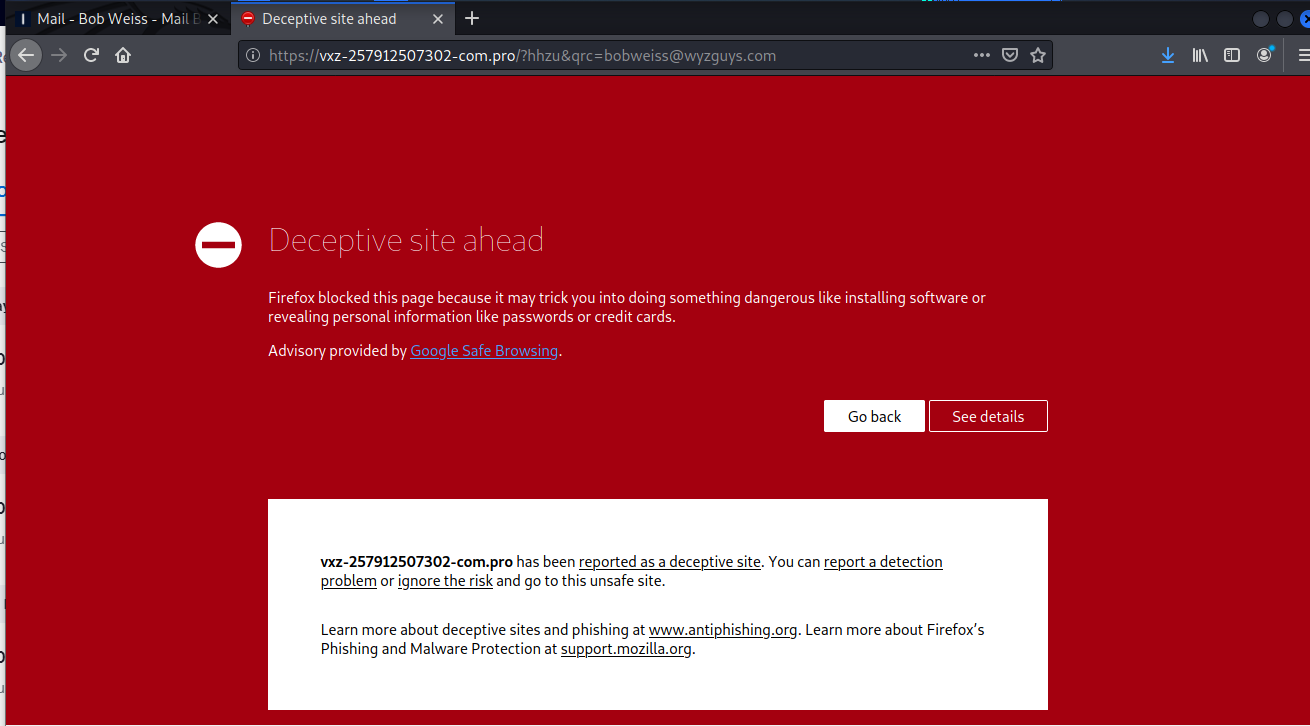
The Firefox browser left this warning. I tried clicking on ignore the risk but the link eventually timed out after a two minute delay. It looked like it was trying to install malware.
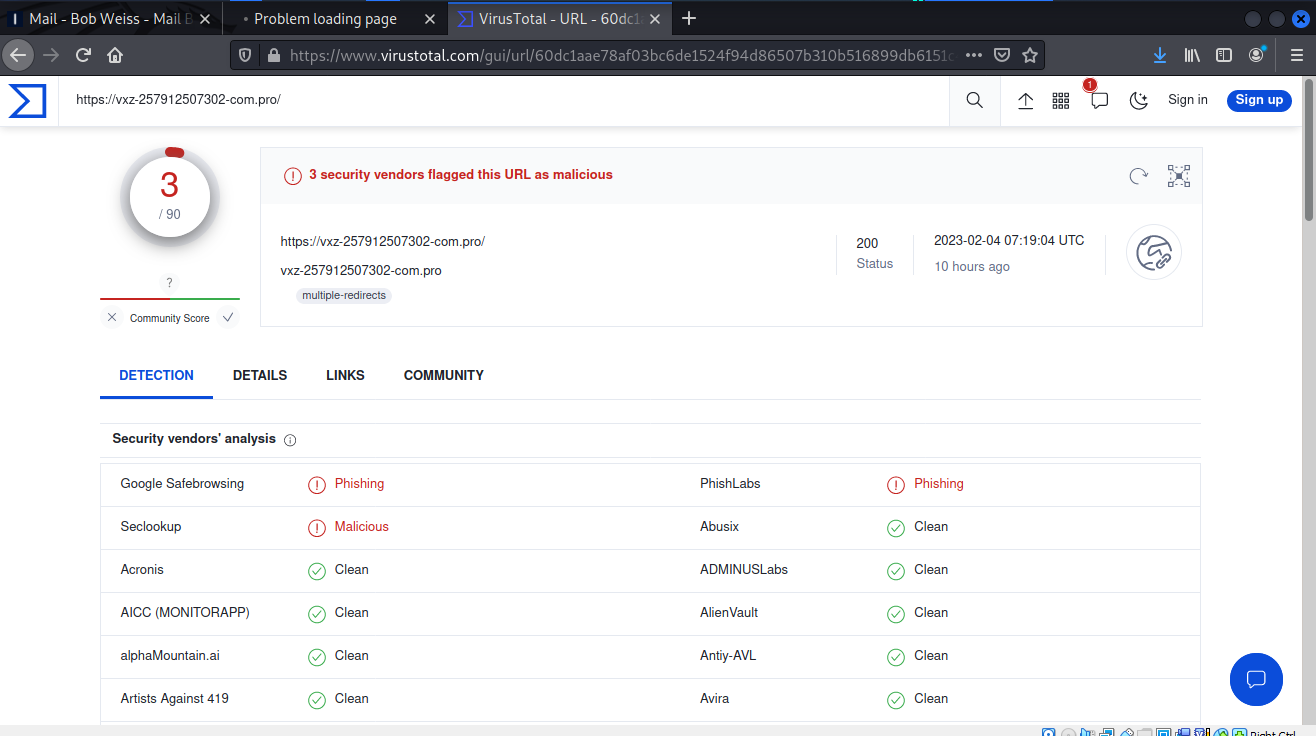
I checked out the link on VirusTotal, and confirmed this is a malicious phishing scam. I also tested the attachment, which came up a s non-malicious. The HTML file opened the CAPTCHA, which then redirected me to the vxz-257912507302-com.pro page, the one that did not load.
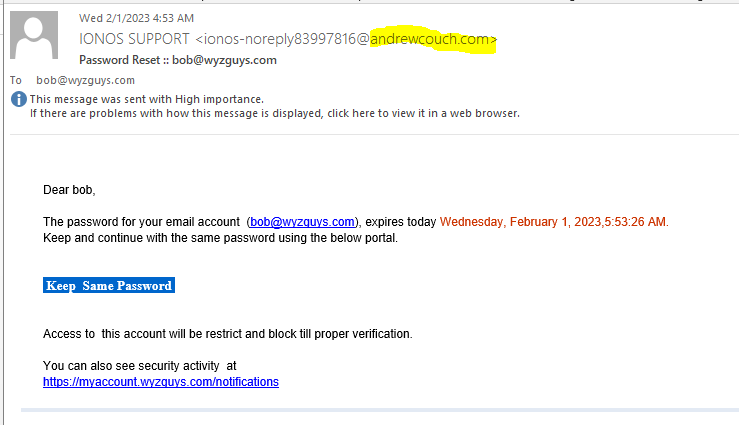
IONOS Support Phish
Here is another credential stealing exploit. The senders address looks pretty realistic if you miss the email domain for andrewcouch.com.
Another clue is the improper use of tense in the verbs in the sentence Access to this account will be restrict and block till proper verification
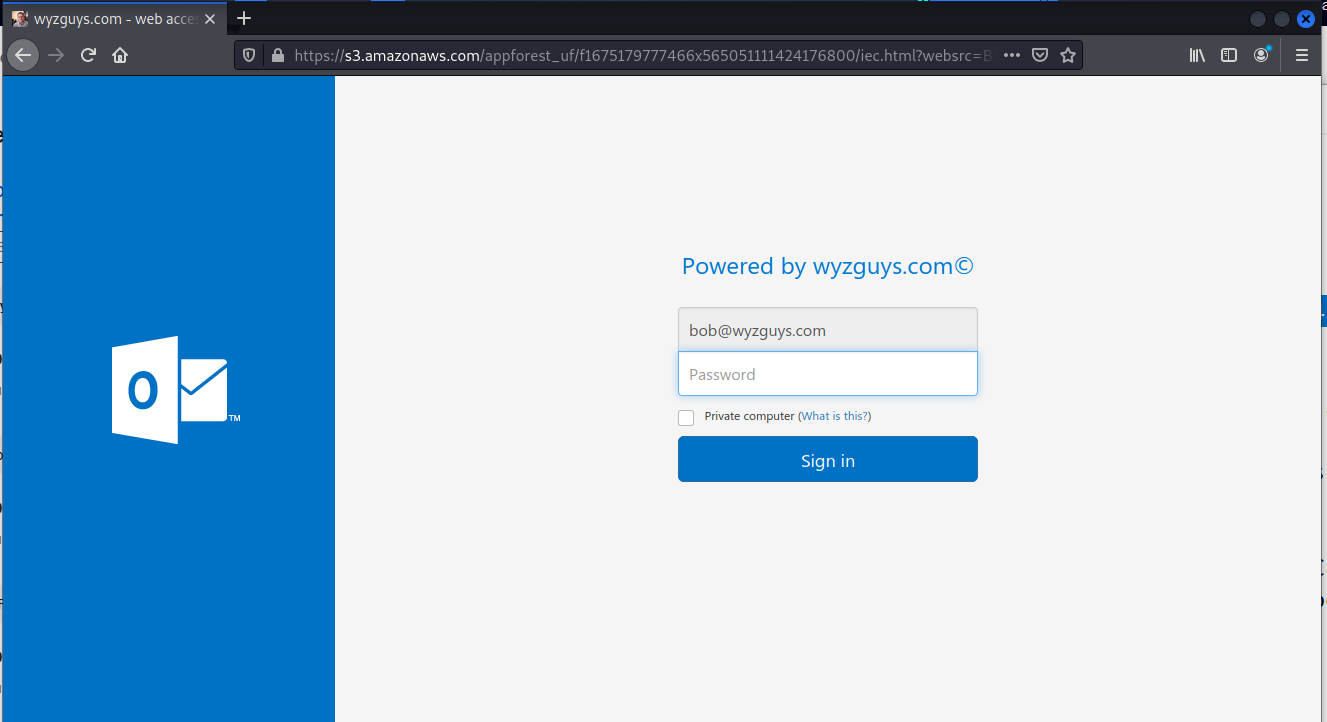
Clicking the Keep Same Password link resolved to an Amazon Web Services account that was created by the attackers. This is still up two days after I received the original email. These attackers have done a nice job updating the Microsoft Outlook 365 trade dress.
When I entered my fake password I received an error message.
If you were to sign in using your real Outlook email credentials, they would be sent to the attackers. This exploit could quickly evolve into a BEC or email account hijacking, and once they were logged into your email account, could impersonate you to family, friends, and coworkers. If this was a business email address, this acount could be used to spread the exploit further inside your company, and eventually used for invoice or wire-transfer fraud.
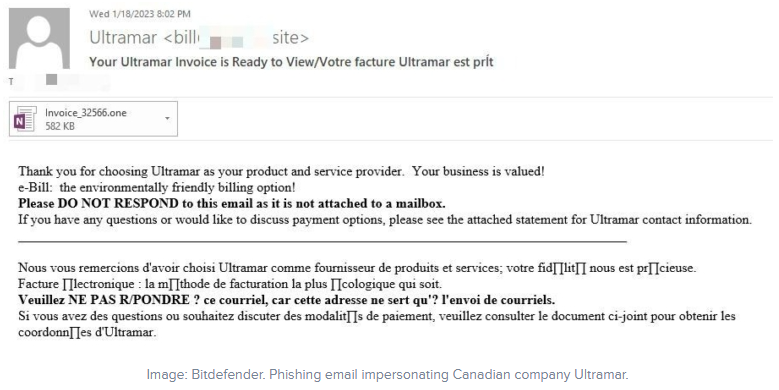
OneNote documents spread malware in several countries
A new phishing campaign abuses OneNote documents to infect computers with the infamous AsyncRAT malware, targeting users in the U.K., Canada and the U.S.
As Microsoft decided to change the default of its Office products to block macros on files downloaded from the internet, cybercriminals saw one of their favorite infection methods vanish.
Some cybercriminals have already found a workaround to keep using some Microsoft Office products, like abusing the XLL files from Excel. Some other cybercriminals have found a different way to keep abusing Microsoft products for infecting computers with malware: infected OneNote documents. More…
Share
FEB





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com