 Phishing Email Alerts
Phishing Email Alerts
Catch of the Day: Thryv Phish
Chef’s Special: LastPass Spear Phish
Examples of clever phish that made it past my spam filters and into my inbox. Some are sent by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
Thryv Phish
I have not heard of Thryv, but this is a legitimate online business services website. According to their site, “Thryv’s small business management platform gives you tools to revolutionize your business. Our platform helps you build your brand, keep organized and get paid faster from anywhere. 24/7 Support. Connect With Customers. Grow Your Business Online.
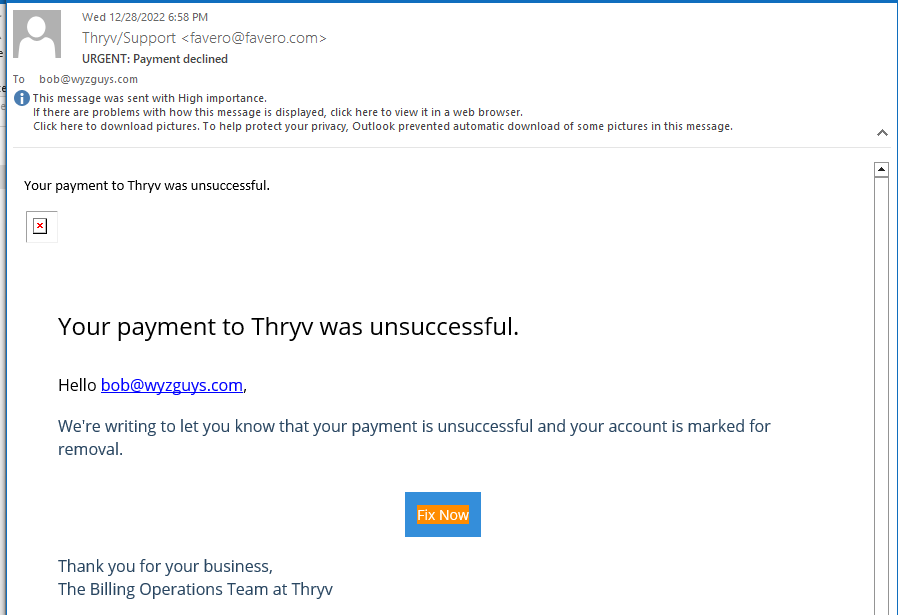
I received the following phishing email which appears to be from Thryv. The FIX NOW button resolved to a Send Grid address that is encoded n what looks like Base64 – https://u2309082.ct.sendgrid.net/ls/click?upn=HpGJr97iNoWH4wFKCT0hr1kffLmZNjVSNRrtfFhfLuarCFjuCUHUN4ofE7PplE24S-2BlcjrzjMOzKRYguF94H7g-3D-3DxTeL_SFbx6topEOS-2BGS6SqugjBqwgYiCeGFwwEr8h28hAAOgBP2fGQcs0CQreCZ4cXHiK4XFxRnqyf2bgCNQ-2Bsjn0sBCw37NPANG786LKjjhC7dq0urC1XfMDJxIhB8K7U5n0BDQ8Q3ovDcCHU4ArHrVSKx9TnB6qRnknvR8O8ctonvyBscro4-2BBqGpQYXFcaMXNRCorqlIwocqLKoQvUhwJjJA-3D-3D which was redirected to the Azure page at https://thryv.azurefd.net/#bob@wyzguys.com
Here’s the email
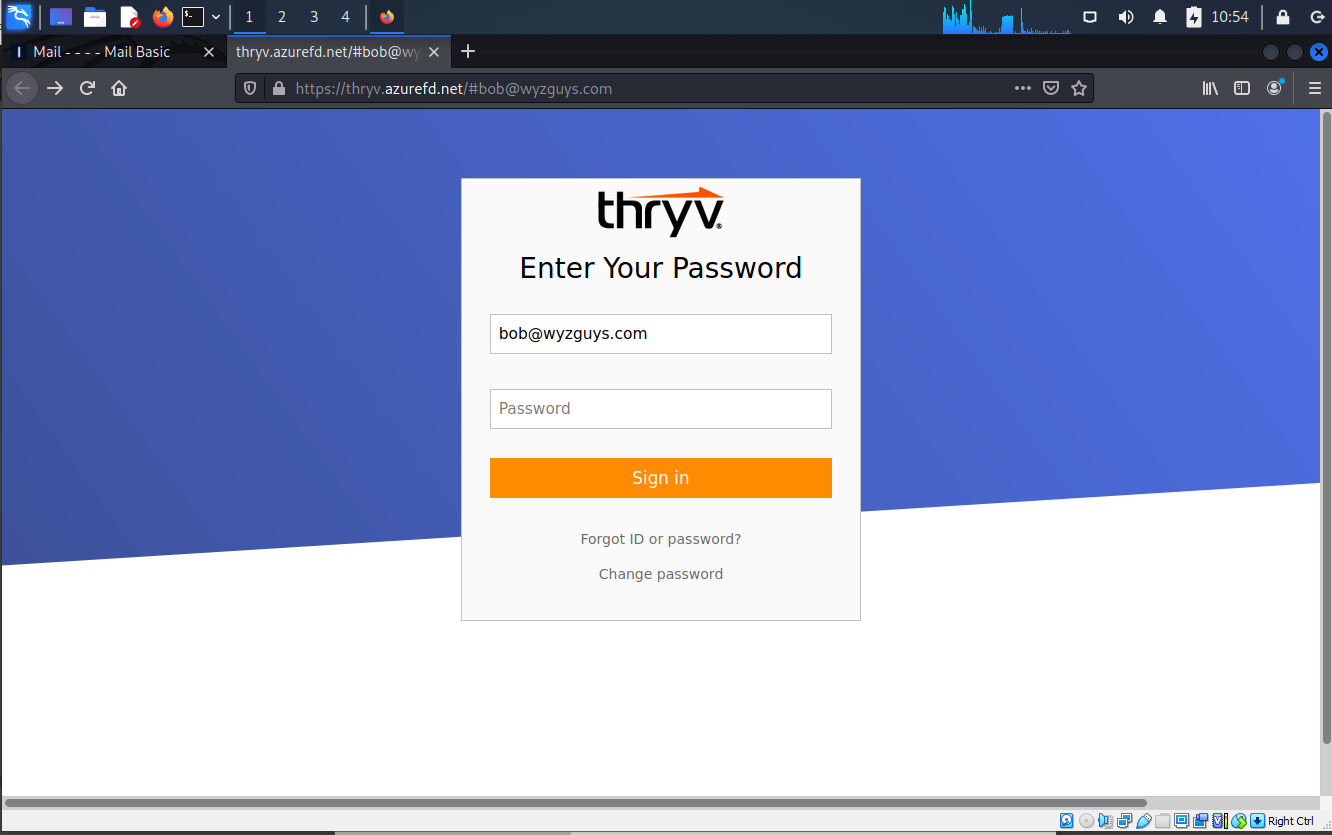
This was the landing page on Azure. Many attacks like this one use familiar public cloud services, because they are recognized and trusted brand.
I entered a password and was bounced to the real Thryv web site. Presumably my user ID and the password I anteed were sent to the attacker in a credential harvesting exploit.
Giant LastPass Breach Can Supercharge Spear Phishing Attacks
KnowBe4 recommends that everyone use a password manager to create and use strong passwords as a part of their password policy:
https://info.knowbe4.com/wp-password-policy-should-be
LastPass, one of the world’s most popular password managers, recently had a bad data breach as revealed here:
https://blog.lastpass.com/2022/12/notice-of-recent-security-incident/
LastPass divulged that although user’s plaintext passwords were not accessed, what the hackers did get included the following information:
- website URLs for the user’s stored passwords
- end-user names
- billing addresses
- email addresses
- telephone numbers
- company names
- IP addresses from which customers were accessing the LastPass service
The hackers also got LastPass user’s encrypted passwords for each stored logon. The encryption protection is strong AS LONG AS the master password users used for LastPass was strong. If you’re interested in a more detailed discussion, go here:
https://www.linkedin.com/pulse/just-how-bad-recent-lastpass-compromise-roger-grimes
In summary, if your LastPass password was at least 12-characters long (the current LastPass default), contained some complexity, wasn’t an easy-to-guess password, and was not used on any other site or service, then you’re probably OK. If not, you need to immediately change all your passwords, both the LastPass master password and all the passwords you stored in LastPass. More…
Share
JAN





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com